Why Data Loss Prevention is essential for Mac OS ?
Explore the 2026 guide for Mac Data Loss Prevention with new challenges, best practices, and advanced strategies to secure MacOS in a hybrid work environment.
Despite macOS's robust security features, the rise in sophisticated malware like DazzleSpy and KeySteal has exposed significant vulnerabilities, particularly in handling sensitive data and system security.
Mac OS devices, once considered nearly impervious to cyber threats, are facing increased vulnerability in the era of remote work. Our valued Apple devices are frequently targeted by sophisticated malware attacks. DazzleSpy and KeySteal are not just silent predators; they actively swipe session cookies and valuable data. KeySteal takes advantage of the macOS keychain—a safe haven for passwords and credentials—to siphon off user information, putting user privacy and security at risk.
Researcher Thijs Alkemade exposes a major security flaw that could enable attackers to circumvent macOS's security protocols and gain access to all system files. Traditional Data Loss Prevention (DLP) solutions have failed to address the unique challenges for Mac devices, leading to a lack of adequate protection.
This new reality demands a robust data loss prevention (DLP) strategy customized to macOS to safeguard sensitive information.
Mac devices are now deeply integrated with SaaS applications, cloud storage, collaboration tools, and generative AI platforms; which means sensitive data frequently moves between endpoints and online services. Without a modern macOS Data Loss Prevention (DLP) strategy that monitors how data is accessed, downloaded, and shared, organizations risk exposing confidential information such as PII, PHI, financial records, and intellectual property. This is why implementing a purpose-built Mac Data Loss Prevention solution has become essential for securing today’s distributed work environments.
Mac devices have long been perceived as more secure than traditional endpoints. But in modern SaaS-driven organizations, macOS devices now interact with dozens of cloud apps, AI tools, and collaboration platforms, dramatically expanding the surface area for sensitive data exposure.
Security incidents are no longer limited to malware infections. Today, the most common risks come from how data moves across systems; from Google Drive to laptops, from browsers to SaaS apps, and from internal tools to generative AI platforms.
This is why Mac Data Loss Prevention (DLP) has become essential for organizations that rely on macOS devices. A modern macOS DLP strategy must provide visibility into how sensitive data moves across endpoints, browsers, SaaS platforms, and cloud environments.
Without this visibility, security teams cannot reliably detect or stop data leaks involving:
Modern DLP platforms like Strac address this challenge by combining endpoint visibility, SaaS monitoring, browser protection, and data lineage tracking into a unified security approach.

The growing adoption of macOS devices in enterprises has exposed gaps in traditional data protection models. Most legacy security tools were designed primarily for Windows environments and network-based monitoring, leaving macOS workflows insufficiently protected.
In modern organizations, sensitive data moves through many pathways that traditional tools struggle to monitor effectively.
Encryption protects data in transit, but it does not eliminate the risk of data exposure. Sensitive data can still be leaked through authorized channels like cloud uploads, email attachments, or browser interactions. Without content-aware inspection, encryption alone cannot stop data exfiltration.
Employees regularly move files between devices, personal storage, and cloud services. Without proper monitoring, confidential files can be transferred outside corporate systems without detection.
For example, a user could download sensitive documents from Google Drive and upload them to a personal cloud account from their Mac laptop.
Data stored locally on devices is especially dangerous in environments where there is a risk of device theft or unauthorized access. For instance, if a laptop is stolen, sensitive data can be compromised. With robust DLP software to encrypt the data at rest, the stolen information would have been protected from unauthorized access, ensuring compliance.
When Mac devices connect to unsecured networks, data may be exposed through network traffic interception or unauthorized access to shared resources.
Sensitive documents printed from Mac systems can easily become a source of accidental exposure if proper authentication and monitoring controls are not enforced.
One of the hardest threats to detect is slow, incremental data leaks. Employees or compromised accounts may transfer small pieces of sensitive information over time, making it difficult for traditional rule-based systems to detect anomalies.
Modern DLP systems address this by monitoring behavior patterns and content movement, allowing security teams to detect suspicious activity before large-scale breaches occur.
Many legacy DLP tools were not designed with macOS architecture in mind. As a result, organizations frequently encounter several challenges when trying to protect Mac environments.
First, support for macOS updates often lags behind Apple’s release cycle. When new versions of macOS are released, older security tools may become incompatible or unstable.
Second, many traditional DLP systems rely on heavy endpoint agents that consume significant system resources. This can degrade performance on Mac devices and negatively impact user productivity.
Third, poorly optimized security tools can trigger kernel panics and system instability, forcing frequent reboots and disrupting workflows.
Finally, legacy DLP systems often rely heavily on static rules and regex-based detection, which can generate excessive false positives and fail to detect complex data patterns in modern workflows.
These limitations highlight the need for modern macOS DLP solutions designed for SaaS-first environments.
Apple provides strong native security features such as FileVault encryption, Gatekeeper protections, and application sandboxing. However, these capabilities focus primarily on device security, not data movement visibility.
Third-party macOS DLP solutions extend Apple’s built-in protections by introducing capabilities such as:
Modern DLP platforms continuously monitor how data moves across systems, identifying suspicious activity such as unauthorized uploads or abnormal file access patterns.
Organizations must be able to automatically detect and classify different categories of sensitive information including:
Advanced DLP tools apply machine learning and content-aware detection to classify sensitive data automatically.

Not all organizations can rely on a one-size-fits-all approach to data security. Third-party DLP solutions provide tailored data handling and classification systems. Companies can set specific criteria for organizing data according to its sensitivity level (e.g., top secret, confidential, internal use only). For example, a financial services firm could implement various security measures using a DLP solution. Strict protocols such as content inspection and data loss prevention rules may be necessary for highly confidential client financial information. In contrast, less sensitive internal documents could allow for more flexible sharing options.
Relying only on macOS security features may create vulnerabilities in your overall security stance. Third-party DLP solutions integrate a range of security measures, such as:
In a financial setting, layered security could consist of starting with firewall protection, then moving on to encrypting important financial information, and using real-time anomaly detection to spot unusual transaction behavior that could be a sign of fraud.
Modern solutions evaluate contextual factors such as:
This allows organizations to apply adaptive security policies instead of static rules.
Security teams can enforce policies that block or restrict risky actions such as:
Contrary to the built-in macOS tools, third-party DLP solutions can seamlessly connect with various security tools and systems. This enables a cohesive and synchronized security approach across various platforms and settings. This combines the DLP system with current SIEM (Security Information and Event Management) systems to boost overall security monitoring and incident response capabilities.
One of the most important capabilities in modern endpoint security is data lineage visibility.
Data lineage tracks how a file moves across systems, applications, and devices over time. This allows security teams to understand not only where sensitive data exists, but also how it arrived there and where it may go next.
For example:
With lineage visibility, a DLP system can recognize that the file remains corporate data, even after being downloaded or modified.
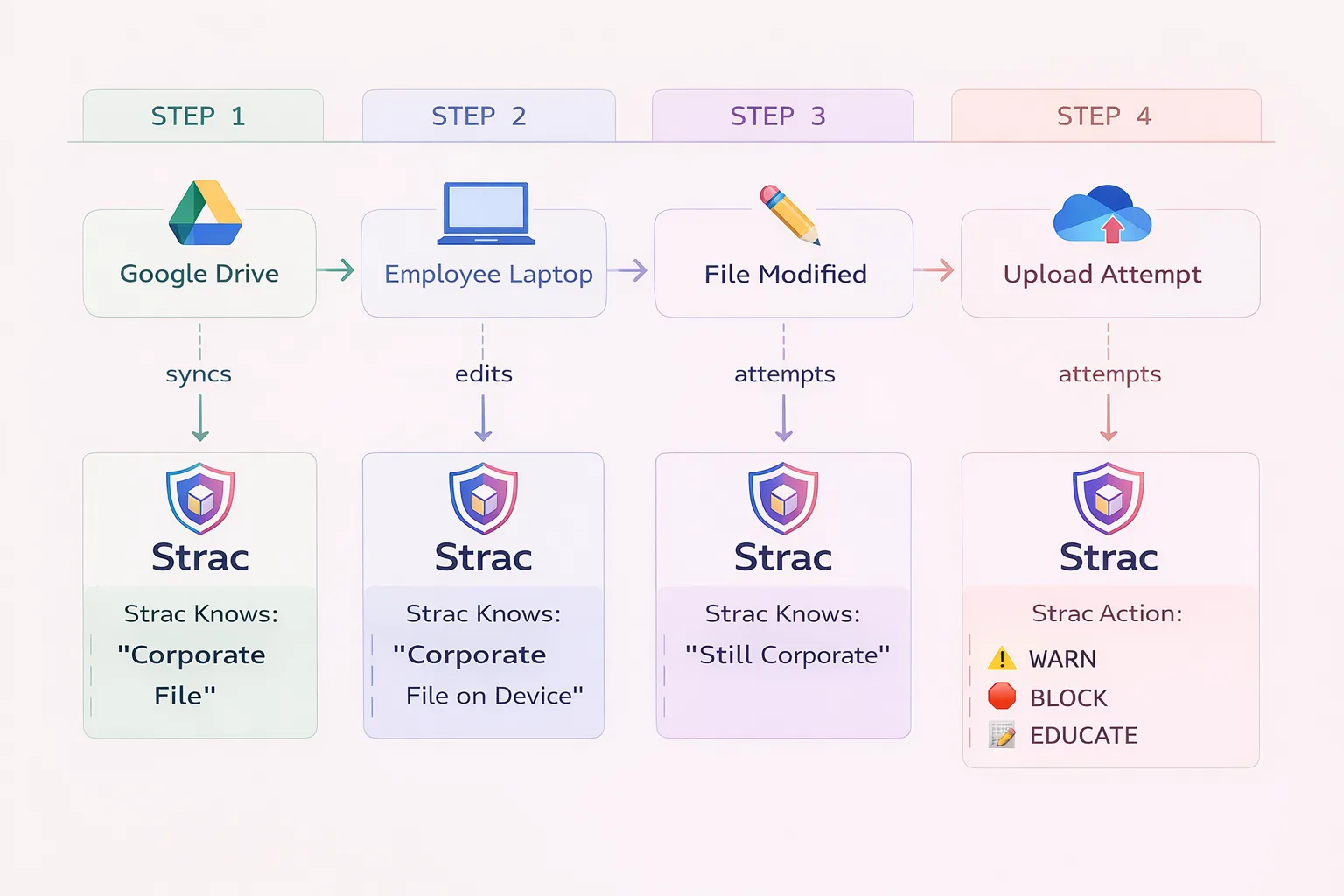
This type of tracking enables security tools like Strac to apply real-time remediation actions, including:
The lineage model ensures that security policies follow the data itself, not just the device or application.
Your uploaded architecture illustrates this concept clearly. It shows how Strac tracks a file from its origin in Google Drive through device edits and ultimately to a potential upload attempt, allowing the platform to intervene before data is exposed.
Organizations can significantly reduce their risk exposure by implementing several macOS security best practices.
First, organizations should enforce regular operating system updates across all Mac devices to ensure security patches are applied promptly.
Second, security teams should implement strict device configuration policies using tools like Apple Business Manager or MDM platforms to enforce encryption, firewall rules, and secure system settings.
Third, organizations should maintain strong application control policies to prevent unauthorized software installation and ensure all approved applications remain updated.
Fourth, remote workers should be required to use secure VPN connections, especially when accessing corporate resources over public networks.
Fifth, organizations should deploy centralized monitoring tools capable of tracking file activity, browser interactions, and SaaS usage across Mac devices.
Finally, companies should invest in security awareness training to educate employees about phishing attacks, credential theft, and accidental data sharing.
Strac thoroughly checks the storage systems on Mac devices and network-attached storage for any sensitive data at risk. This in-depth scan helps to strengthen your defenses against potential data breaches. It offers:


Modern macOS environments interact constantly with SaaS platforms, browsers, and cloud storage services, which means sensitive data often moves far beyond the local device. Strac extends Mac Data Loss Prevention beyond traditional endpoint monitoring by providing visibility across browser activity, SaaS applications, and cloud storage platforms. This allows security teams to detect when sensitive data downloaded to a Mac device is later uploaded to external services, shared through collaboration tools, or transferred through browser-based workflows; ensuring organizations maintain control over their data wherever it moves.
Keep your macOS safe with Strac!
This short demo shows how Strac monitors sensitive data across SaaS platforms, endpoints, and collaboration tools while automatically redacting or blocking risky activity.
macOS devices are now deeply integrated into modern SaaS workflows, making them a critical point of exposure for sensitive data.
Traditional endpoint security tools cannot keep up with the complexity of modern data movement across cloud applications, browsers, and AI platforms.
A modern Mac Data Loss Prevention strategy must provide:
Solutions like Strac enable organizations to monitor how sensitive data moves across systems and stop data leaks before they happen.
No, macOS does not include a full Data Loss Prevention system. Apple provides strong security features such as FileVault encryption, Gatekeeper, and application sandboxing, but these focus on protecting the device itself rather than monitoring how sensitive data moves across applications, cloud platforms, and external services.
To prevent data leaks, organizations typically deploy a third-party macOS DLP solution that can detect sensitive information, monitor file activity, and enforce policies when users attempt to move or share protected data.
Mac Data Loss Prevention is critical because sensitive data frequently moves between endpoints, browsers, SaaS applications, and cloud storage platforms. Without visibility into these workflows, organizations cannot detect when confidential information is downloaded, modified, or uploaded to unauthorized locations.
A modern macOS DLP solution allows security teams to monitor data activity, classify sensitive information such as PII, PHI, or PCI, and prevent accidental or malicious data leaks.
A macOS DLP system should be able to detect and protect multiple categories of sensitive information, including:
Protecting these data types helps organizations comply with regulations such as GDPR, HIPAA, and PCI DSS.
Modern DLP platforms use data lineage tracking to monitor how sensitive files move across systems. This means the system can follow a file from its original location in a SaaS platform or cloud storage system to a user’s Mac device and detect any attempts to upload, copy, or share it elsewhere.
By understanding the origin, movement, and destination of data, DLP tools can apply policies that warn users, block risky actions, or automatically redact sensitive information.
When evaluating a macOS Data Loss Prevention solution, organizations should look for capabilities such as:
Solutions that combine data discovery, classification, and remediation typically provide the most effective protection.
Strac provides modern Mac Data Loss Prevention by monitoring sensitive data across endpoints, browsers, SaaS applications, and cloud storage platforms. The platform automatically detects regulated data types and can take real-time actions such as warning users, blocking risky uploads, or redacting sensitive information.
Because Strac combines DSPM and DLP capabilities, organizations gain full visibility into where sensitive data exists and how it moves across their environment.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

