Salesforce DLP (Data Loss Prevention) is about finding and protecting sensitive data inside Salesforce; across records, tickets, and attachments. It ensures data like PII, payment details, and confidential info isn’t exposed or shared incorrectly. Strong Salesforce DLP doesn’t just detect risk; it fixes it in real time through redaction, masking, or access control.
TL;DR: Strac's Solution for Salesforce DLP & DSPM (Data Security Posture Management)
- Salesforce Service Cloud is the leading platform for organizations to handle customer service and support tickets are a major part of the product .
- Customer support tickets often contain sensitive information that must be protected to comply with privacy laws and regulations.
- Strac Salesforce DLP ( Data Loss Prevention) solution provides an automated way to detect and redact sensitive information in support tickets and attachments linked to them.
- There is no way to manually redact sensitive information a customer support ticket initiated through email . Strac provides an automated way to do this.
- See our video demo below to learn about how Strac Salesforce DLP and redaction works for email-to-case use-case
Salesforce is the lifeblood of many organizations’ sales, support, and customer success operations. It holds a treasure trove of sensitive information — from prospect contact details and account data to case notes and file attachments. With great data comes great responsibility: companies must prevent that data from leaking or falling into the wrong hands. Salesforce Data Loss Prevention (DLP) is all about safeguarding the confidential data in your CRM against unauthorized exposure or loss. But achieving effective DLP in Salesforce can be challenging. In this comprehensive guide, we’ll explore the key aspects of Salesforce DLP, including the challenges and risks involved, why manual efforts often fall short, and how automated solutions can fill the gaps. We’ll also compare the limitations of native Salesforce security controls to a more robust approach, and explain why Strac offers the best solution for Salesforce DLP. By the end, you’ll have both the technical insights and strategic perspective to implement effective DLP measures in Salesforce. Let’s dive in!
✨Understanding Salesforce Data Loss Prevention (DLP) and Why It Matters
What “Salesforce DLP” Means: Data Loss Prevention in Salesforce refers to strategies and tools designed to ensure that sensitive or confidential information in your Salesforce org is not lost, misused, or accessed by unauthorized users. This includes preventing both accidental leaks (e.g. an employee emailing out a report with client PII) and malicious exfiltration (e.g. someone exporting your entire customer list without permission). In practice, Salesforce DLP involves identifying sensitive data within the CRM, monitoring how that data is used or shared, and blocking or mitigating any risky activities (like downloads, emails, or posts that contain sensitive data outside approved channels).
Why DLP Is Critical for Salesforce: Salesforce often houses personally identifiable information (PII), financial records, health information (if you’re in healthcare using Salesforce Health Cloud or Service Cloud for patient info), intellectual property, and other confidential data. A leak of this information can lead to severe consequences: regulatory fines, legal liabilities, loss of customer trust, and damage to your brand reputation. Remember, under regulations like GDPR or CCPA, companies are obligated to protect personal data — a failure to do so can result in fines up to 4% of global revenue in severe cases. Even beyond fines, the business impact of a data breach is enormous. According to IBM’s 2024 research, the global average cost of a data breach reached $4.88 million. These costs include investigation, remediation, notification, and often long-term loss of business due to reputational damage. In fact, roughly 66% of consumers say they would not trust a company that suffered a data breach, and 75% are ready to sever ties with a brand after a major cybersecurity incident. In other words, failing to protect your Salesforce data could literally cost your company millions and erode your hard-earned customer loyalty overnight.
Salesforce’s Shared Responsibility: It’s important to note that while Salesforce provides a secure infrastructure (uptime, physical security, etc.), you as the Salesforce customer are largely responsible for safeguarding the data you put into the platform. Salesforce follows a shared responsibility model for security, meaning Salesforce ensures the platform is reliable and secure at the system level, but each organization must configure and use Salesforce in a secure way to protect against data loss or exposure. As one guide bluntly puts it, Salesforce’s default security settings may not automatically meet all your specific compliance needs. You need to take additional steps to prevent sensitive data from slipping through the cracks.
Compliance and Industry Demands: Different industries have different data protection requirements, but most have one thing in common: Salesforce data often falls under regulatory oversight. For example: if you store health data or medical case information in Salesforce, you’re subject to HIPAA requirements. Handling European customers’ personal data? GDPR mandates strict protection and breach disclosure. Dealing with credit card info (perhaps entered in a Case or Opportunity)? PCI DSS applies. A robust Salesforce DLP strategy helps ensure you meet these obligations. It’s not just about avoiding penalties – it’s about demonstrating to clients and auditors that you take data governance seriously.
In short, “Salesforce DLP” isn’t just a tech buzzword – it’s a critical component of business risk management. To truly understand how to implement DLP, we first need to recognize the unique challenges and risks that come with safeguarding data in Salesforce.
Salesforce Data Loss Prevention Challenges and Risks
Implementing data loss prevention in Salesforce comes with its own set of challenges. Salesforce is a highly customizable and collaborative platform by design – which is great for productivity, but can create security blind spots. Let’s break down some key challenges and risks businesses face regarding Salesforce data loss:
- Identifying Where Sensitive Data Lives: One of the fundamental challenges is simply knowing what sensitive data you have in Salesforce and where it resides. Customer data doesn’t only live in obvious places like Contact or Account fields. It can lurk in free-text fields (account descriptions, case comments), attachments (documents uploaded to records or cases), Chatter posts, or even custom objects. Many organizations lack a thorough data classification – in fact, very few Salesforce users have classified their data or know all the locations of sensitive information in their org. This unawareness leads to “shadow data” – sensitive info that isn’t on anyone’s radar – which is dangerous. A recent study found that shadow data was involved in 1 out of 3 data breaches, because it’s hard to track and secure what you don’t even know about.
- Data Everywhere (Attachments, Emails, and More): Salesforce’s strength is that it centralizes customer information, but ironically that means sensitive data can crop up in many places within Salesforce. For instance, support emails converted to cases, files attached to opportunities, or integrations feeding data into Salesforce from other systems. Emails, attachments, and Chatter messages all expand the surface where sensitive data might appear. This variety makes DLP harder – you need to monitor more than just standard field values. A support rep might copy-paste a client’s credit card number into a case comment or attach a spreadsheet of customer SSNs to a record. Without DLP in place, those could quietly live in your CRM, exposing you to compliance violations if accessed improperly.
- Excessive Access (Internal Threats): Not all data loss is from hackers – a lot is internal. Salesforce is often widely used across departments, meaning many users have access to data. If too many people can see sensitive records, the risk of an insider leak (intentional or accidental) rises. An employee might innocently run a report of all customers including personal data and save it locally, or maliciously export data before leaving for a new job. Misuse can happen if access controls aren’t tight. Every additional user with access to sensitive data is an added risk factor. Insider threats and human error remain leading causes of data exposure.
- Human Error and Manual Processes: Humans make mistakes – it’s inevitable. A common risk is someone entering sensitive data in the wrong place. For example, a rep should input a Social Security Number into a secure field that’s encrypted or masked, but instead puts it in an open “Notes” field where it’s visible to all. Or, an admin might accidentally change a sharing rule and open up records to users who shouldn’t see them. Relying purely on manual procedures or user diligence to prevent these mistakes is risky. With no safety net, it’s just a matter of time before something slips through.
- Sandbox and Test Environments: Many businesses copy production data into sandbox orgs for testing or development. Those sandboxes often have weaker controls (or less oversight) than production. If you’re not masking or scrubbing sensitive data in these copies, you could be doubling your risk surface. It’s easy to forget that a developer sandbox has full customer data — and if that sandbox gets breached or a user outside the core team accesses it, that’s a data leak. However, manually scrubbing or anonymizing data in sandboxes is cumbersome and often neglected, leading to unintended exposure.
- External Threats: While internal mishaps are common, we can’t ignore external attacks. If a cyber attacker compromises a Salesforce user account (via phishing, credential stuffing, etc.), they could exfiltrate a lot of data quickly. Or, an insecure integration or third-party app with access to Salesforce could become a backdoor. Ensuring only the right data leaves Salesforce in an authorized manner is difficult without specialized monitoring. Standard Salesforce logging might tell you after the fact what was accessed, but by then the damage is done.
- Compliance Violations and Consequences: All the above risks feed into the grand concern: a data breach or compliance violation. The consequences of failing to protect Salesforce data are dire. Consider privacy laws: under GDPR, if you expose EU customer data, your company could face fines up to €20 million or 4% of annual turnover, whichever is higher. Beyond regulatory fines, think of the business fallout: as noted, a breach can cost millions in clean-up and harm your reputation such that customers flee. The impact on trust is huge – surveys show a majority of consumers lose trust in a company after a data breach. This is why Salesforce DLP isn’t just an IT problem; it’s a business continuity and customer trust issue.
- Statistics Underscore the Risk: To paint a clearer picture, one report by SilverlineCRM found 86% of sensitive fields in Salesforce are not adequately protected in many orgs. That means the vast majority of fields containing things like personal data, financial info, etc., lack proper shielding (encryption, masking, or access control). This highlights how common it is to have gaps in Salesforce data protection. It’s not due to negligence; it’s often due to how easy it is for data to proliferate without admins realizing. The same report emphasizes that Salesforce often holds data like SSNs, credit card numbers, driver’s licenses – exactly the kind of info you must prevent from leaking.
In summary, the challenges of Salesforce DLP boil down to: knowing where your sensitive data is (visibility), controlling who can access it (governance), and preventing it from escaping Salesforce (monitoring and enforcement) – all while supporting business productivity. It’s a delicate balance. Now, let’s talk about approaches to tackle these challenges – specifically, the difference between trying to do it manually versus using an automated DLP solution.(
Manual vs. Automated Salesforce DLP: Why Automation Wins
When confronting Salesforce DLP, companies often start with manual efforts. Policies, training, and basic Salesforce configuration can get you part of the way. But as your data and user base grows, manual methods struggle to keep up. Let’s compare manual vs automated approaches to Salesforce DLP:
Manual DLP Approach: A manual approach relies on people and basic platform tools to prevent data loss. This might include:
- Establishing internal policies (e.g. “Don’t put credit card numbers in case comments” or “Never export data without approval”).
- Training employees on proper data handling and hoping they comply.
- Manually configuring Salesforce settings like profiles, field permissions, and validation rules to try and limit access to sensitive fields.
- Periodically auditing records to spot sensitive info where it doesn’t belong (maybe running a report to see if any SSN-like patterns show up in text fields).
- Relying on admins to reactively clean or remove sensitive data when someone reports it present in a record where it shouldn’t be.
While these steps are important (and we’ll cover some in the “actionable steps” section), they have serious limitations. Manual monitoring is labor-intensive and error-prone. It’s practically impossible to manually review every field, every attachment, every day for potential issues. Humans get tired and overlook things. Also, manual processes often catch problems late, if at all. By the time an admin discovers that an attachment contains a thousand customer emails with PII, that document might have been accessible for weeks.Furthermore, enforcement is inconsistent with manual methods. One employee might be diligent about following data policies, while another might be careless – all it takes is one mistake to leak data. Manual DLP is like having security cameras that someone occasionally checks; if no one is watching at the critical moment, you miss the incident.To maintain a strong posture purely manually, organizations would need to invest an extreme amount of time and resources. For a highly customizable environment like Salesforce, keeping up with best practices manually is difficult and costly – it can require an “excessive time or resource commitment”just to enforce policies and catch issues. In fact, experts recommend that the only sustainable way to enforce consistent data protection in Salesforce is to leverage automation
Automated DLP Approach: An automated Salesforce DLP solution means using technology tools to continuously identify and protect sensitive data with minimal human intervention. Key aspects of an automated approach include:
- Automatic Detection of sensitive data in Salesforce records, fields, messages, and files. This uses predefined patterns (like regex for credit card numbers) and possibly machine learning to find things like PII or secrets as soon as they appear.
- Real-time or Ongoing Monitoring of user actions (e.g., downloading a report, editing a record, attaching a file) and data flows. The system watches for any activity that violates data security policies.
- Automated Enforcement, such as instantly masking or redacting sensitive data when found, blocking a transfer (like preventing an attachment from being shared externally), or alerting admins immediately to suspicious behavior.
- Policy Consistency across the board. Once you set the rules (e.g., “block any SSN from being visible to non-HR profiles” or “alert if more than 500 records are exported at once with emails”), the DLP tool applies them uniformly, every time, without relying on individual discretion.
- Logging and Reporting of all these events so you have an audit trail and can demonstrate compliance or investigate incidents quickly.
Automated DLP effectively adds an extra “layer” of security on top of Salesforce that is always on duty. Unlike a human who might check things occasionally, an automated system can scan thousands of records and activities in seconds and do it 24/7. It doesn’t get tired or forget. And when something happens, it can respond in milliseconds – far faster than a manual response.Let’s illustrate the difference through a quick scenario: Imagine a customer support email comes in containing a credit card number (something that should be avoided). In a manual scenario, that email becomes a Case in Salesforce. It’s now sitting in a case comment or attachment. Maybe your support agent notices and manually deletes it or flags it… or maybe they don’t. Perhaps an admin runs a weekly report to find credit card patterns in case comments – best case, the number sits exposed for a few days before being cleaned up; worst case, it’s missed entirely. In an automated DLP scenario, as soon as that case is created, the DLP system detects the 16-digit card number pattern. It immediately flags and redacts it – perhaps replacing it with a masked version (e.g., “XXXX-XXXX-XXXX-1234”) or moving the content to a secure vault. The support agent and others never see the full card number in Salesforce, eliminating the risk of further exposure. The system also logs this event and could notify the security team, but all of this happens within seconds and without anyone having to take manual action. That’s the power of automation.
It’s clear that while manual measures (like good policies and Salesforce security settings) are necessary, they are not sufficient on their own for robust DLP. As one expert guide noted, without automated DLP, maintaining data security in a large Salesforce org would demand unsustainable time and resources In contrast, automated DLP solutions provide a feasible way to enforce data protection continuously and reliably. Next, we’ll examine how far you can get with Salesforce’s native security tools and where they fall short, necessitating third-party solutions.
Best practices for protecting sensitive data in Salesforce
Make Salesforce DLP a strategic priority.
Protecting sensitive data in Salesforce starts with leadership alignment and shared accountability. Salesforce DLP should not live only within IT—it must be a company-wide initiative that connects security, compliance, and operations. By defining ownership and embedding Salesforce DLP into everyday processes, organizations can prevent data exposure before it occurs. When data protection becomes cultural rather than reactive, every team member becomes a guardian of customer trust.
- Unite Salesforce admins, security, and compliance teams around one mission: protecting customer data.
- Define clear ownership for data handling across cases, comments, and attachments.
- Build Salesforce DLP into your broader security and compliance policies so data protection becomes part of company culture, not just a technical task.
Strengthen Salesforce security foundations.
A strong Salesforce DLP strategy begins with the right configurations and access controls. Securing your Salesforce environment means more than turning on encryption—it’s about ensuring users only see what they need and nothing more. Every unnecessary permission, shared report, or API token is a potential leak point. By tightening identity and access settings, you reduce both insider risk and external exposure, creating a resilient foundation for DLP to succeed.
- Enforce multi-factor authentication and least privilege access to minimize exposure.
- Encrypt sensitive fields and review permissions regularly to catch overexposure early.
- Train employees to identify and handle sensitive data properly so prevention happens before incidents occur.
Automate data discovery and protection.
Manual efforts can’t keep pace with the volume and velocity of Salesforce data. Automated Salesforce DLP ensures continuous visibility and control, identifying sensitive data the moment it enters your system. With Strac, organizations can instantly detect, redact, and quarantine PII or PHI in cases, attachments, and email-to-case threads. Automation not only strengthens compliance—it builds efficiency, accuracy, and trust across every customer interaction.
- Use an automated DLP and DSPM platform like Strac to continuously scan for sensitive data.
- Automatically detect and redact PII or PHI in real time across Salesforce records, files, and email-to-case threads.
- Apply consistent protection and compliance controls across Salesforce and every connected SaaS app.
- Gain instant visibility, faster compliance readiness, and complete control of your CRM data without slowing down your teams.
Limitations of Native Salesforce Security Controls for DLP
Salesforce comes with a variety of built-in security features – you might wonder, can’t those prevent data loss? Salesforce does offer robust access controls and some add-on tools, but when it comes to content-level DLP, the native capabilities have significant gaps. Let’s go through what Salesforce provides natively and why that may not be enough:
- Profiles, Roles, and Field-Level Security: Salesforce’s core security model lets you control which users can see or edit certain records (via role hierarchy and sharing settings) and even hide particular fields from certain profiles. For example, you might restrict a standard user from viewing the “SSN” field on a contact. This is useful, but role-based access control isn’t content-aware. If a user has access to a record, Salesforce doesn’t natively filter what’s inside a text field or attachment based on content. So, if you hide the dedicated SSN field but a well-meaning sales rep puts an SSN into the “Description” note, any user who can see the Description can see that SSN. Profiles and roles can’t prevent that scenario. They also can’t stop a user with legitimate access from exporting or sharing data they can see.
- Validation Rules and Data Entry Controls: Salesforce admins can set up validation rules or triggers to enforce some data policies (for instance, rejecting a case submission if it contains a pattern like a credit card number). This is a form of manual DLP some teams try. It can work for very specific cases but doesn’t scale well. You’d have to predict every sensitive pattern users might enter and maintain those rules. It might block some obvious things, but determined users or unexpected cases will slip past. Additionally, validation rules only work at the moment of data entry; they don’t help if the data comes in via integrations or if it was already in the system from before the rule.
- Salesforce Shield (Encryption & Event Monitoring): Salesforce offers Shield as a premium add-on which includes Platform Encryption, Event Monitoring, and Field Audit Trail. Shield’s Platform Encryption can encrypt data at rest at the field level (including in files/attachments, though that is an all-or-nothing switch). Encryption is great for security, but it’s not a panacea for DLP:
- Encrypted fields are still visible (in decrypted form) to users with permission, so an authorized user could still leak that data – encryption mainly protects against outsiders or Salesforce itself accessing the raw data. It “does not obfuscate the data; data is still mostly transparent to your end users in the UI”. See: https://www.salesforceben.com/salesforce-shield/#:~:text=,users%20from%20the%20Salesforce%20UI
- There are also trade-offs and limitations when using Shield Encryption: certain fields can’t be encrypted, you lose some functionality on encrypted fields (like being unable to use them in filter criteria or sorts), and implementing encryption needs careful planning (Salesforce’s implementation guide for Shield is 96 pages long, highlighting the complexity!). It’s a powerful tool for compliance but doesn’t actively stop data loss through user actions; it mainly protects data if someone gains direct access to the database or backups.
- Shield’s Event Monitoring logs a lot of user activity (logins, exports, etc.), which is useful for forensic analysis and spotting trends. However, out-of-the-box it’s more of an auditing tool than a prevention tool. It can tell you that “User X exported report Y” or “Data was downloaded” – but unless you or another tool is actively watching those events in real-time, you might find out after the fact. You would have to build a custom system or use a partner app to alert on those events for it to function like DLP. Salesforce does now allow event monitoring via API in near real-time, so a third-party DLP can hook in (as we’ll see with Strac), but by itself, Event Monitoring is like a security camera with no guard – the recording is there, but it won’t stop the intruder.
- Data Mask (for Sandboxes): Salesforce has a feature (or separate product) called Data Mask that helps anonymize or mask data when you copy it to a sandbox. This is great for reducing risk in test environments. But again, it’s an optional add-on and applies only during sandbox seeding. In production orgs, Salesforce doesn’t automatically mask any data – it’s up to you.
- Native Data Classification & Einstein Data Detect: Salesforce provides a way to tag fields with data sensitivity labels (e.g., marking a field as “PersonalData” or “Confidential”) as part of its data classification scheme. This is useful for documentation and for things like Shield (to decide what to encrypt), but it doesn’t enforce anything by itself (it’s metadata for your reference). In Spring 2021, Salesforce introduced Einstein Data Detect (now just “Data Detect” under Shield) which can scan your org for certain types of sensitive data. Data Detect is essentially Salesforce’s basic DLP discovery tool: it automatically scans your database and identifies some sensitive data patterns, specifically five types – credit card numbers, email addresses, social security numbers, URLs, and IP addresses. This is a nice feature, but it has limitations:
- It only searches for those five predefined patterns (as of now). What if you need to detect drivers license numbers, bank account numbers, or API keys? Data Detect won’t catch those unless they coincidentally look like one of the five patterns.
- It’s an assessment tool, not a real-time protector. Data Detect will tell you “Hey, we found 200 cases where a credit card number is in a field that’s not encrypted”, which is helpful to know, but it doesn’t automatically mask or remove it. It’s then on you to take action (like enable encryption on that field, or manually clean those records). In other words, it informs your policy; it doesn’t enforce it live.
- Data Detect is part of the Shield suite (requires a Shield subscription), so if you haven’t paid for Shield, Salesforce isn’t searching your data for PII at all.
- No Out-of-the-Box DLP Enforcement: Perhaps the biggest limitation to emphasize: Salesforce has no native, built-in DLP that will actively block or redact sensitive data in real-time. There is no “DLP” checkbox you can turn on in Salesforce that will do what a dedicated DLP tool does. As one guide noted in plain terms, Salesforce relies on third-party apps to provide DLP functionality. This means if you want to, say, automatically remove or hide credit card numbers that appear in case comments, Salesforce alone won’t do that for you – you need a third-party solution or some custom code.
- Example – Editing Email-to-Case: To illustrate a native limitation: When a customer emails your support address and it becomes a Case (Email-to-Case), the email content is stored in the case’s thread or as an attachment. Salesforce does not allow you to edit the content of an email-to-case easily (to preserve the fidelity of email records). That means if a customer included sensitive info in their email, your support reps cannot simply edit it out within Salesforce. There is literally “no way to manually redact sensitive information” from a support ticket that came via email. This is a design limitation – Salesforce treats inbound emails as immutable. Without a specialized tool, you’re stuck: the sensitive info stays unless you delete the whole email from the case, which might not be feasible. This is a prime example where a Salesforce-specific DLP tool is needed to clean or mask data that users cannot.
- Reporting and Exports: Natively, Salesforce lets you restrict the ability to export reports (via profile permissions). Some orgs go as far as disabling “Export Report” for most users or even turning off API access to prevent mass exports. However, this can cripple legitimate business processes because people do need to export data for analysis or integrations. If you don’t fully disable it, then any user with the permission can export large datasets. Salesforce will log that an export happened (if you have event monitoring), but it won’t stop it. You also can’t easily differentiate between a legitimate export and a risky one (like someone exporting all contacts right before resignation) without additional logic. It’s a coarse control: either allow exports or don’t. There’s no native concept of “alert me if an unusual export occurs” or “block exports to personal devices”.
-
In summary, Salesforce’s native security controls are indispensable for setting the groundwork (you should absolutely use things like field-level security, sharing rules, and Shield encryption appropriately). However, for true data loss prevention – especially content-based detection and automatic remediation – you need more. The native toolkit wasn’t designed to sniff out a social security number hiding in a case comment and black it out, or to alert you the moment someone downloads 10,000 records. Those are the capabilities of a dedicated DLP solution.The good news is, the Salesforce platform is extensible, and there are solutions that fill these gaps seamlessly. Next, we’ll look at how Strac’s automated DLP solution builds on Salesforce’s foundation and addresses these limitations head-on, providing a superior safeguard for your CRM data.
🎥 The Superior Salesforce DLP Solution: How Strac Stands Out
When it comes to protecting sensitive data in Salesforce, third-party solutions are the go-to answer. But not all DLP tools are created equal. Strac is a platform that has emerged as a best-in-class solution for Salesforce Data Loss Prevention, offering a comprehensive and automated approach tailored to the needs of Salesforce users. In this section, we’ll explore how Strac works and why it provides a superior solution compared to both native controls and other approaches.

Strac’s Salesforce DLP solution is designed to seamlessly integrate with Salesforce and actively protect your data without disrupting your business workflows. Here’s what makes Strac stand out:
- Automated Sensitive Data Detection (Powered by AI): Strac automatically discovers sensitive data across your Salesforce objects, fields, and files. It uses a combination of pattern matching and high-accuracy machine learning models to identify PII, PHI, financial information, secrets (like API keys), and more. This goes far beyond the handful of patterns Salesforce’s Data Detect covers. You’re not limited to pre-canned patterns either – Strac comes with a large catalog of sensitive data types out of the box (think Social Security numbers, dates of birth, driver’s license numbers, passport numbers, credit card #s, bank routing/account #s, API keys, etc.), and you can configure which ones are relevant to your business. If needed, Strac even allows custom patterns or tuning the detection to suit your data, ensuring nothing important slips by. The moment a new piece of data enters Salesforce (say, a new case is created or a field is updated), Strac can scan it in near real-time. This proactive discovery means you gain full visibility into where sensitive data is in your org.
- Instant Redaction and Masking: Detection is only half the battle – what truly differentiates Strac is its ability to take action automatically to prevent data exposure. When Strac finds sensitive information in a Salesforce record or attachment that shouldn’t be openly visible, it will redact or mask that information in Salesforce. For example, if a customer’s message contains a credit card number, Strac can replace it with a masked version or a placeholder in the Salesforce record. The original sensitive content is removed from Salesforce, effectively “neutralizing” the risk of exposure within the CRM. But Strac doesn’t just delete it outright (after all, your business might still need that info to do its job) – instead, it stores the full sensitive data in a secure vault outside of Salesforce (within Strac’s system). Authorized personnel can still access the real data through Strac’s interface (with proper authentication), but regular Salesforce users will only see the sanitized version. This approach is ideal because it balances security with business continuity: your team can continue using Salesforce normally, without stumbling over or spreading around sensitive info, yet the data is not lost – it’s just quarantined in a safe place. Strac essentially gives Salesforce the ability to “edit out” sensitive bits that Salesforce itself didn’t allow editing (like that email-to-case scenario). In scenarios where Salesforce provides no native way to remove the data (recall the email-to-case limitation), Strac’s automated masking is a lifesaver.
- Exfiltration Monitoring and Threat Detection: A unique aspect of Strac’s solution is that it not only looks at data at rest in Salesforce, but also keeps an eye on data in motion. Strac includes exfiltration detection features that monitor when large amounts of data are accessed or exported from Salesforce. For example, Strac can watch for report exports or data downloads, and crucially, it distinguishes between normal business actions and potentially risky ones. If someone downloads a report to an untrusted device (say, a personal laptop or an unknown IP), Strac will flag it. Downloads to your managed corporate devices might be left alone (since those are usually policy-compliant), but that same data going to an external location triggers an alert. This level of context-aware monitoring is something native Salesforce logs can’t do on their own. It’s like having a smart guard who not only notes that “data left the building,” but also checks who is taking it and to where, and sounds the alarm if it looks suspicious. Strac can thus catch insider threats or account compromise early – if at 2 AM, a user begins exporting lots of customer records to a strange IP, Strac’s going to raise a red flag immediately.
- Real-Time Alerts and Notifications: When Strac detects a policy violation or a sensitive data event, it doesn’t sit quietly. It will send alerts to the appropriate channels so your team can take action if needed. You can configure Strac to send alert notifications via email or tools like Slack, integrating with your existing incident response workflow. For example, your security officer might get a Slack message within seconds if someone attempts to share a file containing confidential data. This real-time awareness is crucial for mitigating incidents – you’re not finding out days later; you know now and can respond promptly.
- Comprehensive Audit Trail and Reporting: Every action Strac takes – every detection, redaction, user access to the vault, etc. – is logged. Strac provides detailed reports that show what sensitive data was found where, what was done (e.g., “Field X on Case 1001 was masked because it contained an SSN”), and who viewed any of the original data in the secure vault. These audit logs are gold for compliance and for internal oversight. If an auditor asks “how do you ensure no one’s viewing credit card numbers in Salesforce?”, you can pull out Strac’s report showing that any credit card that appeared was automatically masked and only viewable by, say, your Finance manager (with a record of when they viewed it). This level of detail helps demonstrate compliance with regulations like HIPAA, GDPR, or PCI DSS. Strac essentially makes it easier to prove you have control over your sensitive Salesforce data.
- Fine-Grained Access Controls & Secure Vault: The Strac Vault is a secure web interface where the redacted data is held. Only authorized users (which you can set up with single sign-on, integrating your identity provider) can access this vault. Within it, you can have fine-grained access rules. For instance, perhaps your compliance officer and a senior manager are the only ones allowed to view full Social Security numbers. They would log into the Strac vault to retrieve that info when absolutely needed. Meanwhile, your frontline staff never need to see or handle that sensitive data – they just see [REDACTED] or a masked version in Salesforce. This separation of duties greatly reduces the chance of accidental exposure. It’s like having a high-security safe for the crown jewels of data; only the key holders can open it, and you get an audit log every time it’s opened.
- Anonymization for Lower Environments: Remember the sandbox problem? Strac can help there too. You can use Strac’s data masking features to anonymize or tokenize data before it proliferates to less secure environments. For example, you might configure Strac so that any PII copied to a sandbox is automatically masked, or ensure that test data doesn’t include real customer identifiers. This means developers and testers can work with realistic data sans the actual sensitive values. Strac’s platform supports these use cases as part of an overall DLP strategy (as noted in their features like anonymization and masking for sandbox data).
- Easy Integration and Low Overhead: One of the big advantages of Strac is its ease of deployment. It integrates with Salesforce via API and event monitoring, which means no heavy agents or code installations on your Salesforce org. You typically connect Strac to Salesforce using an OAuth 2.0 connection with an admin or integration user account. Once connected, Strac starts monitoring and scanning within minutes. The solution is designed to be up and running quickly – some organizations have it integrated in under 10 minutes. This is a stark contrast to something like Salesforce Shield which, as mentioned, can be a large project to implement fully. Strac’s approach is more “plug-and-play” for DLP. Additionally, because it’s API-based and running externally, it doesn’t significantly impact the performance of your Salesforce instance. All the heavy processing (scanning for PII, etc.) is done on Strac’s side, offloading from Salesforce.
- Broad Coverage and Consistency Across Apps: Many companies use more than just Salesforce – you might also use Slack, Google Drive, Zendesk, or other SaaS apps that handle sensitive data. Strac is not limited to Salesforce; it’s a unified DLP platform that can integrate with a wide range of applications (SaaS, cloud storage, even endpoints). This means you can have one consistent data protection policy across all your tools. For instance, you could set a rule in Strac that “credit card numbers should be redacted from all customer support channels,” and Strac would enforce that in Salesforce Cases, in Zendesk tickets, in Slack messages, etc., if you use those. This is a competitive edge – instead of piecemeal solutions for each app, Strac gives you a centralized way to manage DLP. So if your business is concerned about data loss not just in Salesforce but everywhere, Strac’s extensibility is a big plus. (Even though our focus here is Salesforce, it’s nice to know the solution can scale with your ecosystem.)
- Competitive Insights (Without Naming Names): How does Strac compare to other DLP solutions generally? Many traditional DLP solutions (especially older, “legacy” enterprise DLP) were focused on endpoints or networks and weren’t built with cloud apps like Salesforce in mind. They might require installing software agents on devices or have limited visibility into cloud application data. Newer cloud DLP tools exist, but some only provide alerting and leave the remediation to you, or they might not integrate as deeply (for example, some might scan files but not be able to redact inline text within a Salesforce record). Strac distinguishes itself by offering in-line remediation (redaction) and deep integration into Salesforce objects (including support tickets, standard and custom objects, etc.), not just surface-level scanning. Also, some solutions might generate a lot of “noise” (false positives or too many alerts) which can overwhelm security teams. Strac, by leveraging ML and providing an “AI Agent” as they call it, aims to reduce false positives and intelligently classify data, so you get high fidelity alerts. Essentially, Strac’s focus on accuracy and action (not just detection) makes it a best-of-breed for Salesforce DLP.
What “Salesforce DLP” Means: Data Loss Prevention in Salesforce refers to strategies and tools designed to ensure that sensitive or confidential information in your Salesforce org is not lost, misused, or accessed by unauthorized users. This includes preventing both accidental leaks (e.g. an employee emailing out a report with client PII) and malicious exfiltration (e.g. someone exporting your entire customer list without permission). In practice, Salesforce DLP involves identifying sensitive data within the CRM, monitoring how that data is used or shared, and blocking or mitigating any risky activities (like downloads, emails, or posts that contain sensitive data outside approved channels).
Why DLP Is Critical for Salesforce: Salesforce often houses personally identifiable information (PII), financial records, health information (if you’re in healthcare using Salesforce Health Cloud or Service Cloud for patient info), intellectual property, and other confidential data. A leak of this information can lead to severe consequences: regulatory fines, legal liabilities, loss of customer trust, and damage to your brand reputation. Remember, under regulations like GDPR or CCPA, companies are obligated to protect personal data — a failure to do so can result in fines up to 4% of global revenue in severe cases. Even beyond fines, the business impact of a data breach is enormous. According to IBM’s 2024 research, the global average cost of a data breach reached $4.88 million. These costs include investigation, remediation, notification, and often long-term loss of business due to reputational damage. In fact, roughly 66% of consumers say they would not trust a company that suffered a data breach, and 75% are ready to sever ties with a brand after a major cybersecurity incident. In other words, failing to protect your Salesforce data could literally cost your company millions and erode your hard-earned customer loyalty overnight.
Salesforce’s Shared Responsibility: It’s important to note that while Salesforce provides a secure infrastructure (uptime, physical security, etc.), you as the Salesforce customer are largely responsible for safeguarding the data you put into the platform. Salesforce follows a shared responsibility model for security, meaning Salesforce ensures the platform is reliable and secure at the system level, but each organization must configure and use Salesforce in a secure way to protect against data loss or exposure. As one guide bluntly puts it, Salesforce’s default security settings may not automatically meet all your specific compliance needs. You need to take additional steps to prevent sensitive data from slipping through the cracks.
Compliance and Industry Demands: Different industries have different data protection requirements, but most have one thing in common: Salesforce data often falls under regulatory oversight. For example: if you store health data or medical case information in Salesforce, you’re subject to HIPAA requirements. Handling European customers’ personal data? GDPR mandates strict protection and breach disclosure. Dealing with credit card info (perhaps entered in a Case or Opportunity)? PCI DSS applies. A robust Salesforce DLP strategy helps ensure you meet these obligations. It’s not just about avoiding penalties – it’s about demonstrating to clients and auditors that you take data governance seriously.
In short, “Salesforce DLP” isn’t just a tech buzzword – it’s a critical component of business risk management. To truly understand how to implement DLP, we first need to recognize the unique challenges and risks that come with safeguarding data in Salesforce.
Salesforce Data Loss Prevention Challenges and Risks
Implementing data loss prevention in Salesforce comes with its own set of challenges. Salesforce is a highly customizable and collaborative platform by design – which is great for productivity, but can create security blind spots. Let’s break down some key challenges and risks businesses face regarding Salesforce data loss:
- Identifying Where Sensitive Data Lives: One of the fundamental challenges is simply knowing what sensitive data you have in Salesforce and where it resides. Customer data doesn’t only live in obvious places like Contact or Account fields. It can lurk in free-text fields (account descriptions, case comments), attachments (documents uploaded to records or cases), Chatter posts, or even custom objects. Many organizations lack a thorough data classification – in fact, very few Salesforce users have classified their data or know all the locations of sensitive information in their org. This unawareness leads to “shadow data” – sensitive info that isn’t on anyone’s radar – which is dangerous. A recent study found that shadow data was involved in 1 out of 3 data breaches, because it’s hard to track and secure what you don’t even know about.
- Data Everywhere (Attachments, Emails, and More): Salesforce’s strength is that it centralizes customer information, but ironically that means sensitive data can crop up in many places within Salesforce. For instance, support emails converted to cases, files attached to opportunities, or integrations feeding data into Salesforce from other systems. Emails, attachments, and Chatter messages all expand the surface where sensitive data might appear. This variety makes DLP harder – you need to monitor more than just standard field values. A support rep might copy-paste a client’s credit card number into a case comment or attach a spreadsheet of customer SSNs to a record. Without DLP in place, those could quietly live in your CRM, exposing you to compliance violations if accessed improperly.
- Excessive Access (Internal Threats): Not all data loss is from hackers – a lot is internal. Salesforce is often widely used across departments, meaning many users have access to data. If too many people can see sensitive records, the risk of an insider leak (intentional or accidental) rises. An employee might innocently run a report of all customers including personal data and save it locally, or maliciously export data before leaving for a new job. Misuse can happen if access controls aren’t tight. Every additional user with access to sensitive data is an added risk factor. Insider threats and human error remain leading causes of data exposure.
- Human Error and Manual Processes: Humans make mistakes – it’s inevitable. A common risk is someone entering sensitive data in the wrong place. For example, a rep should input a Social Security Number into a secure field that’s encrypted or masked, but instead puts it in an open “Notes” field where it’s visible to all. Or, an admin might accidentally change a sharing rule and open up records to users who shouldn’t see them. Relying purely on manual procedures or user diligence to prevent these mistakes is risky. With no safety net, it’s just a matter of time before something slips through.
- Sandbox and Test Environments: Many businesses copy production data into sandbox orgs for testing or development. Those sandboxes often have weaker controls (or less oversight) than production. If you’re not masking or scrubbing sensitive data in these copies, you could be doubling your risk surface. It’s easy to forget that a developer sandbox has full customer data — and if that sandbox gets breached or a user outside the core team accesses it, that’s a data leak. However, manually scrubbing or anonymizing data in sandboxes is cumbersome and often neglected, leading to unintended exposure.
- External Threats: While internal mishaps are common, we can’t ignore external attacks. If a cyber attacker compromises a Salesforce user account (via phishing, credential stuffing, etc.), they could exfiltrate a lot of data quickly. Or, an insecure integration or third-party app with access to Salesforce could become a backdoor. Ensuring only the right data leaves Salesforce in an authorized manner is difficult without specialized monitoring. Standard Salesforce logging might tell you after the fact what was accessed, but by then the damage is done.
- Compliance Violations and Consequences: All the above risks feed into the grand concern: a data breach or compliance violation. The consequences of failing to protect Salesforce data are dire. Consider privacy laws: under GDPR, if you expose EU customer data, your company could face fines up to €20 million or 4% of annual turnover, whichever is higher. Beyond regulatory fines, think of the business fallout: as noted, a breach can cost millions in clean-up and harm your reputation such that customers flee. The impact on trust is huge – surveys show a majority of consumers lose trust in a company after a data breach. This is why Salesforce DLP isn’t just an IT problem; it’s a business continuity and customer trust issue.
- Statistics Underscore the Risk: To paint a clearer picture, one report by SilverlineCRM found 86% of sensitive fields in Salesforce are not adequately protected in many orgs. That means the vast majority of fields containing things like personal data, financial info, etc., lack proper shielding (encryption, masking, or access control). This highlights how common it is to have gaps in Salesforce data protection. It’s not due to negligence; it’s often due to how easy it is for data to proliferate without admins realizing. The same report emphasizes that Salesforce often holds data like SSNs, credit card numbers, driver’s licenses – exactly the kind of info you must prevent from leaking.
In summary, the challenges of Salesforce DLP boil down to: knowing where your sensitive data is (visibility), controlling who can access it (governance), and preventing it from escaping Salesforce (monitoring and enforcement) – all while supporting business productivity. It’s a delicate balance. Now, let’s talk about approaches to tackle these challenges – specifically, the difference between trying to do it manually versus using an automated DLP solution.(
Manual vs. Automated Salesforce DLP: Why Automation Wins
When confronting Salesforce DLP, companies often start with manual efforts. Policies, training, and basic Salesforce configuration can get you part of the way. But as your data and user base grows, manual methods struggle to keep up. Let’s compare manual vs automated approaches to Salesforce DLP:
Manual DLP Approach: A manual approach relies on people and basic platform tools to prevent data loss. This might include:
- Establishing internal policies (e.g. “Don’t put credit card numbers in case comments” or “Never export data without approval”).
- Training employees on proper data handling and hoping they comply.
- Manually configuring Salesforce settings like profiles, field permissions, and validation rules to try and limit access to sensitive fields.
- Periodically auditing records to spot sensitive info where it doesn’t belong (maybe running a report to see if any SSN-like patterns show up in text fields).
- Relying on admins to reactively clean or remove sensitive data when someone reports it present in a record where it shouldn’t be.
While these steps are important (and we’ll cover some in the “actionable steps” section), they have serious limitations. Manual monitoring is labor-intensive and error-prone. It’s practically impossible to manually review every field, every attachment, every day for potential issues. Humans get tired and overlook things. Also, manual processes often catch problems late, if at all. By the time an admin discovers that an attachment contains a thousand customer emails with PII, that document might have been accessible for weeks.Furthermore, enforcement is inconsistent with manual methods. One employee might be diligent about following data policies, while another might be careless – all it takes is one mistake to leak data. Manual DLP is like having security cameras that someone occasionally checks; if no one is watching at the critical moment, you miss the incident.To maintain a strong posture purely manually, organizations would need to invest an extreme amount of time and resources. For a highly customizable environment like Salesforce, keeping up with best practices manually is difficult and costly – it can require an “excessive time or resource commitment”just to enforce policies and catch issues. In fact, experts recommend that the only sustainable way to enforce consistent data protection in Salesforce is to leverage automation
Automated DLP Approach: An automated Salesforce DLP solution means using technology tools to continuously identify and protect sensitive data with minimal human intervention. Key aspects of an automated approach include:
- Automatic Detection of sensitive data in Salesforce records, fields, messages, and files. This uses predefined patterns (like regex for credit card numbers) and possibly machine learning to find things like PII or secrets as soon as they appear.
- Real-time or Ongoing Monitoring of user actions (e.g., downloading a report, editing a record, attaching a file) and data flows. The system watches for any activity that violates data security policies.
- Automated Enforcement, such as instantly masking or redacting sensitive data when found, blocking a transfer (like preventing an attachment from being shared externally), or alerting admins immediately to suspicious behavior.
- Policy Consistency across the board. Once you set the rules (e.g., “block any SSN from being visible to non-HR profiles” or “alert if more than 500 records are exported at once with emails”), the DLP tool applies them uniformly, every time, without relying on individual discretion.
- Logging and Reporting of all these events so you have an audit trail and can demonstrate compliance or investigate incidents quickly.
Automated DLP effectively adds an extra “layer” of security on top of Salesforce that is always on duty. Unlike a human who might check things occasionally, an automated system can scan thousands of records and activities in seconds and do it 24/7. It doesn’t get tired or forget. And when something happens, it can respond in milliseconds – far faster than a manual response.Let’s illustrate the difference through a quick scenario: Imagine a customer support email comes in containing a credit card number (something that should be avoided). In a manual scenario, that email becomes a Case in Salesforce. It’s now sitting in a case comment or attachment. Maybe your support agent notices and manually deletes it or flags it… or maybe they don’t. Perhaps an admin runs a weekly report to find credit card patterns in case comments – best case, the number sits exposed for a few days before being cleaned up; worst case, it’s missed entirely. In an automated DLP scenario, as soon as that case is created, the DLP system detects the 16-digit card number pattern. It immediately flags and redacts it – perhaps replacing it with a masked version (e.g., “XXXX-XXXX-XXXX-1234”) or moving the content to a secure vault. The support agent and others never see the full card number in Salesforce, eliminating the risk of further exposure. The system also logs this event and could notify the security team, but all of this happens within seconds and without anyone having to take manual action. That’s the power of automation.
It’s clear that while manual measures (like good policies and Salesforce security settings) are necessary, they are not sufficient on their own for robust DLP. As one expert guide noted, without automated DLP, maintaining data security in a large Salesforce org would demand unsustainable time and resources In contrast, automated DLP solutions provide a feasible way to enforce data protection continuously and reliably. Next, we’ll examine how far you can get with Salesforce’s native security tools and where they fall short, necessitating third-party solutions.
Limitations of Native Salesforce Security Controls for DLP
Salesforce comes with a variety of built-in security features – you might wonder, can’t those prevent data loss? Salesforce does offer robust access controls and some add-on tools, but when it comes to content-level DLP, the native capabilities have significant gaps. Let’s go through what Salesforce provides natively and why that may not be enough:
- Profiles, Roles, and Field-Level Security: Salesforce’s core security model lets you control which users can see or edit certain records (via role hierarchy and sharing settings) and even hide particular fields from certain profiles. For example, you might restrict a standard user from viewing the “SSN” field on a contact. This is useful, but role-based access control isn’t content-aware. If a user has access to a record, Salesforce doesn’t natively filter what’s inside a text field or attachment based on content. So, if you hide the dedicated SSN field but a well-meaning sales rep puts an SSN into the “Description” note, any user who can see the Description can see that SSN. Profiles and roles can’t prevent that scenario. They also can’t stop a user with legitimate access from exporting or sharing data they can see.
- Validation Rules and Data Entry Controls: Salesforce admins can set up validation rules or triggers to enforce some data policies (for instance, rejecting a case submission if it contains a pattern like a credit card number). This is a form of manual DLP some teams try. It can work for very specific cases but doesn’t scale well. You’d have to predict every sensitive pattern users might enter and maintain those rules. It might block some obvious things, but determined users or unexpected cases will slip past. Additionally, validation rules only work at the moment of data entry; they don’t help if the data comes in via integrations or if it was already in the system from before the rule.
- Salesforce Shield (Encryption & Event Monitoring): Salesforce offers Shield as a premium add-on which includes Platform Encryption, Event Monitoring, and Field Audit Trail. Shield’s Platform Encryption can encrypt data at rest at the field level (including in files/attachments, though that is an all-or-nothing switch). Encryption is great for security, but it’s not a panacea for DLP:
- Encrypted fields are still visible (in decrypted form) to users with permission, so an authorized user could still leak that data – encryption mainly protects against outsiders or Salesforce itself accessing the raw data. It “does not obfuscate the data; data is still mostly transparent to your end users in the UI”. See: https://www.salesforceben.com/salesforce-shield/#:~:text=,users%20from%20the%20Salesforce%20UI
- There are also trade-offs and limitations when using Shield Encryption: certain fields can’t be encrypted, you lose some functionality on encrypted fields (like being unable to use them in filter criteria or sorts), and implementing encryption needs careful planning (Salesforce’s implementation guide for Shield is 96 pages long, highlighting the complexity!). It’s a powerful tool for compliance but doesn’t actively stop data loss through user actions; it mainly protects data if someone gains direct access to the database or backups.
- Shield’s Event Monitoring logs a lot of user activity (logins, exports, etc.), which is useful for forensic analysis and spotting trends. However, out-of-the-box it’s more of an auditing tool than a prevention tool. It can tell you that “User X exported report Y” or “Data was downloaded” – but unless you or another tool is actively watching those events in real-time, you might find out after the fact. You would have to build a custom system or use a partner app to alert on those events for it to function like DLP. Salesforce does now allow event monitoring via API in near real-time, so a third-party DLP can hook in (as we’ll see with Strac), but by itself, Event Monitoring is like a security camera with no guard – the recording is there, but it won’t stop the intruder.
- Data Mask (for Sandboxes): Salesforce has a feature (or separate product) called Data Mask that helps anonymize or mask data when you copy it to a sandbox. This is great for reducing risk in test environments. But again, it’s an optional add-on and applies only during sandbox seeding. In production orgs, Salesforce doesn’t automatically mask any data – it’s up to you.
- Native Data Classification & Einstein Data Detect: Salesforce provides a way to tag fields with data sensitivity labels (e.g., marking a field as “PersonalData” or “Confidential”) as part of its data classification scheme. This is useful for documentation and for things like Shield (to decide what to encrypt), but it doesn’t enforce anything by itself (it’s metadata for your reference). In Spring 2021, Salesforce introduced Einstein Data Detect (now just “Data Detect” under Shield) which can scan your org for certain types of sensitive data. Data Detect is essentially Salesforce’s basic DLP discovery tool: it automatically scans your database and identifies some sensitive data patterns, specifically five types – credit card numbers, email addresses, social security numbers, URLs, and IP addresses. This is a nice feature, but it has limitations:
- It only searches for those five predefined patterns (as of now). What if you need to detect drivers license numbers, bank account numbers, or API keys? Data Detect won’t catch those unless they coincidentally look like one of the five patterns.
- It’s an assessment tool, not a real-time protector. Data Detect will tell you “Hey, we found 200 cases where a credit card number is in a field that’s not encrypted”, which is helpful to know, but it doesn’t automatically mask or remove it. It’s then on you to take action (like enable encryption on that field, or manually clean those records). In other words, it informs your policy; it doesn’t enforce it live.
- Data Detect is part of the Shield suite (requires a Shield subscription), so if you haven’t paid for Shield, Salesforce isn’t searching your data for PII at all.
- No Out-of-the-Box DLP Enforcement: Perhaps the biggest limitation to emphasize: Salesforce has no native, built-in DLP that will actively block or redact sensitive data in real-time. There is no “DLP” checkbox you can turn on in Salesforce that will do what a dedicated DLP tool does. As one guide noted in plain terms, Salesforce relies on third-party apps to provide DLP functionality. This means if you want to, say, automatically remove or hide credit card numbers that appear in case comments, Salesforce alone won’t do that for you – you need a third-party solution or some custom code.
- Example – Editing Email-to-Case: To illustrate a native limitation: When a customer emails your support address and it becomes a Case (Email-to-Case), the email content is stored in the case’s thread or as an attachment. Salesforce does not allow you to edit the content of an email-to-case easily (to preserve the fidelity of email records). That means if a customer included sensitive info in their email, your support reps cannot simply edit it out within Salesforce. There is literally “no way to manually redact sensitive information” from a support ticket that came via email. This is a design limitation – Salesforce treats inbound emails as immutable. Without a specialized tool, you’re stuck: the sensitive info stays unless you delete the whole email from the case, which might not be feasible. This is a prime example where a Salesforce-specific DLP tool is needed to clean or mask data that users cannot.
- Reporting and Exports: Natively, Salesforce lets you restrict the ability to export reports (via profile permissions). Some orgs go as far as disabling “Export Report” for most users or even turning off API access to prevent mass exports. However, this can cripple legitimate business processes because people do need to export data for analysis or integrations. If you don’t fully disable it, then any user with the permission can export large datasets. Salesforce will log that an export happened (if you have event monitoring), but it won’t stop it. You also can’t easily differentiate between a legitimate export and a risky one (like someone exporting all contacts right before resignation) without additional logic. It’s a coarse control: either allow exports or don’t. There’s no native concept of “alert me if an unusual export occurs” or “block exports to personal devices”.
In summary, Salesforce’s native security controls are indispensable for setting the groundwork (you should absolutely use things like field-level security, sharing rules, and Shield encryption appropriately). However, for true data loss prevention – especially content-based detection and automatic remediation – you need more. The native toolkit wasn’t designed to sniff out a social security number hiding in a case comment and black it out, or to alert you the moment someone downloads 10,000 records. Those are the capabilities of a dedicated DLP solution.The good news is, the Salesforce platform is extensible, and there are solutions that fill these gaps seamlessly. Next, we’ll look at how Strac’s automated DLP solution builds on Salesforce’s foundation and addresses these limitations head-on, providing a superior safeguard for your CRM data.
🎥 The Superior Salesforce DLP Solution: How Strac Stands Out
When it comes to protecting sensitive data in Salesforce, third-party solutions are the go-to answer. But not all DLP tools are created equal. Strac is a platform that has emerged as a best-in-class solution for Salesforce Data Loss Prevention, offering a comprehensive and automated approach tailored to the needs of Salesforce users. In this section, we’ll explore how Strac works and why it provides a superior solution compared to both native controls and other approaches.
Strac’s Salesforce DLP solution is designed to seamlessly integrate with Salesforce and actively protect your data without disrupting your business workflows. Here’s what makes Strac stand out:
- Automated Sensitive Data Detection (Powered by AI): Strac automatically discovers sensitive data across your Salesforce objects, fields, and files. It uses a combination of pattern matching and high-accuracy machine learning models to identify PII, PHI, financial information, secrets (like API keys), and more. This goes far beyond the handful of patterns Salesforce’s Data Detect covers. You’re not limited to pre-canned patterns either – Strac comes with a large catalog of sensitive data types out of the box (think Social Security numbers, dates of birth, driver’s license numbers, passport numbers, credit card #s, bank routing/account #s, API keys, etc.), and you can configure which ones are relevant to your business. If needed, Strac even allows custom patterns or tuning the detection to suit your data, ensuring nothing important slips by. The moment a new piece of data enters Salesforce (say, a new case is created or a field is updated), Strac can scan it in near real-time. This proactive discovery means you gain full visibility into where sensitive data is in your org.
- Instant Redaction and Masking: Detection is only half the battle – what truly differentiates Strac is its ability to take action automatically to prevent data exposure. When Strac finds sensitive information in a Salesforce record or attachment that shouldn’t be openly visible, it will redact or mask that information in Salesforce. For example, if a customer’s message contains a credit card number, Strac can replace it with a masked version or a placeholder in the Salesforce record. The original sensitive content is removed from Salesforce, effectively “neutralizing” the risk of exposure within the CRM. But Strac doesn’t just delete it outright (after all, your business might still need that info to do its job) – instead, it stores the full sensitive data in a secure vault outside of Salesforce (within Strac’s system). Authorized personnel can still access the real data through Strac’s interface (with proper authentication), but regular Salesforce users will only see the sanitized version. This approach is ideal because it balances security with business continuity: your team can continue using Salesforce normally, without stumbling over or spreading around sensitive info, yet the data is not lost – it’s just quarantined in a safe place. Strac essentially gives Salesforce the ability to “edit out” sensitive bits that Salesforce itself didn’t allow editing (like that email-to-case scenario). In scenarios where Salesforce provides no native way to remove the data (recall the email-to-case limitation), Strac’s automated masking is a lifesaver.
- Exfiltration Monitoring and Threat Detection: A unique aspect of Strac’s solution is that it not only looks at data at rest in Salesforce, but also keeps an eye on data in motion. Strac includes exfiltration detection features that monitor when large amounts of data are accessed or exported from Salesforce. For example, Strac can watch for report exports or data downloads, and crucially, it distinguishes between normal business actions and potentially risky ones. If someone downloads a report to an untrusted device (say, a personal laptop or an unknown IP), Strac will flag it. Downloads to your managed corporate devices might be left alone (since those are usually policy-compliant), but that same data going to an external location triggers an alert. This level of context-aware monitoring is something native Salesforce logs can’t do on their own. It’s like having a smart guard who not only notes that “data left the building,” but also checks who is taking it and to where, and sounds the alarm if it looks suspicious. Strac can thus catch insider threats or account compromise early – if at 2 AM, a user begins exporting lots of customer records to a strange IP, Strac’s going to raise a red flag immediately.
- Real-Time Alerts and Notifications: When Strac detects a policy violation or a sensitive data event, it doesn’t sit quietly. It will send alerts to the appropriate channels so your team can take action if needed. You can configure Strac to send alert notifications via email or tools like Slack, integrating with your existing incident response workflow. For example, your security officer might get a Slack message within seconds if someone attempts to share a file containing confidential data. This real-time awareness is crucial for mitigating incidents – you’re not finding out days later; you know now and can respond promptly.
- Comprehensive Audit Trail and Reporting: Every action Strac takes – every detection, redaction, user access to the vault, etc. – is logged. Strac provides detailed reports that show what sensitive data was found where, what was done (e.g., “Field X on Case 1001 was masked because it contained an SSN”), and who viewed any of the original data in the secure vault. These audit logs are gold for compliance and for internal oversight. If an auditor asks “how do you ensure no one’s viewing credit card numbers in Salesforce?”, you can pull out Strac’s report showing that any credit card that appeared was automatically masked and only viewable by, say, your Finance manager (with a record of when they viewed it). This level of detail helps demonstrate compliance with regulations like HIPAA, GDPR, or PCI DSS. Strac essentially makes it easier to prove you have control over your sensitive Salesforce data.
- Fine-Grained Access Controls & Secure Vault: The Strac Vault is a secure web interface where the redacted data is held. Only authorized users (which you can set up with single sign-on, integrating your identity provider) can access this vault. Within it, you can have fine-grained access rules. For instance, perhaps your compliance officer and a senior manager are the only ones allowed to view full Social Security numbers. They would log into the Strac vault to retrieve that info when absolutely needed. Meanwhile, your frontline staff never need to see or handle that sensitive data – they just see [REDACTED] or a masked version in Salesforce. This separation of duties greatly reduces the chance of accidental exposure. It’s like having a high-security safe for the crown jewels of data; only the key holders can open it, and you get an audit log every time it’s opened.
- Anonymization for Lower Environments: Remember the sandbox problem? Strac can help there too. You can use Strac’s data masking features to anonymize or tokenize data before it proliferates to less secure environments. For example, you might configure Strac so that any PII copied to a sandbox is automatically masked, or ensure that test data doesn’t include real customer identifiers. This means developers and testers can work with realistic data sans the actual sensitive values. Strac’s platform supports these use cases as part of an overall DLP strategy (as noted in their features like anonymization and masking for sandbox data).
- Easy Integration and Low Overhead: One of the big advantages of Strac is its ease of deployment. It integrates with Salesforce via API and event monitoring, which means no heavy agents or code installations on your Salesforce org. You typically connect Strac to Salesforce using an OAuth 2.0 connection with an admin or integration user account. Once connected, Strac starts monitoring and scanning within minutes. The solution is designed to be up and running quickly – some organizations have it integrated in under 10 minutes. This is a stark contrast to something like Salesforce Shield which, as mentioned, can be a large project to implement fully. Strac’s approach is more “plug-and-play” for DLP. Additionally, because it’s API-based and running externally, it doesn’t significantly impact the performance of your Salesforce instance. All the heavy processing (scanning for PII, etc.) is done on Strac’s side, offloading from Salesforce.
- Broad Coverage and Consistency Across Apps: Many companies use more than just Salesforce – you might also use Slack, Google Drive, Zendesk, or other SaaS apps that handle sensitive data. Strac is not limited to Salesforce; it’s a unified DLP platform that can integrate with a wide range of applications (SaaS, cloud storage, even endpoints). This means you can have one consistent data protection policy across all your tools. For instance, you could set a rule in Strac that “credit card numbers should be redacted from all customer support channels,” and Strac would enforce that in Salesforce Cases, in Zendesk tickets, in Slack messages, etc., if you use those. This is a competitive edge – instead of piecemeal solutions for each app, Strac gives you a centralized way to manage DLP. So if your business is concerned about data loss not just in Salesforce but everywhere, Strac’s extensibility is a big plus. (Even though our focus here is Salesforce, it’s nice to know the solution can scale with your ecosystem.)
- Competitive Insights (Without Naming Names): How does Strac compare to other DLP solutions generally? Many traditional DLP solutions (especially older, “legacy” enterprise DLP) were focused on endpoints or networks and weren’t built with cloud apps like Salesforce in mind. They might require installing software agents on devices or have limited visibility into cloud application data. Newer cloud DLP tools exist, but some only provide alerting and leave the remediation to you, or they might not integrate as deeply (for example, some might scan files but not be able to redact inline text within a Salesforce record). Strac distinguishes itself by offering in-line remediation (redaction) and deep integration into Salesforce objects (including support tickets, standard and custom objects, etc.), not just surface-level scanning. Also, some solutions might generate a lot of “noise” (false positives or too many alerts) which can overwhelm security teams. Strac, by leveraging ML and providing an “AI Agent” as they call it, aims to reduce false positives and intelligently classify data, so you get high fidelity alerts. Essentially, Strac’s focus on accuracy and action (not just detection) makes it a best-of-breed for Salesforce DLP.
🌶️Spicy FAQs on Salesforce DLP
What is Salesforce Data Loss Prevention (DLP) and why does it matter?
Salesforce Data Loss Prevention (DLP) refers to the set of tools, policies, and technologies that prevent sensitive or confidential data in Salesforce from being leaked, misused, or accessed by unauthorized users. Salesforce holds massive volumes of PII, PHI, and financial data, making it a prime target for breaches and compliance violations. A Salesforce DLP strategy ensures that critical business data is protected at every touchpoint—whether it’s entered manually, shared in a case comment, or synced from another app. Implementing Salesforce DLP is not just about compliance; it’s about preserving trust, reducing financial risk, and maintaining control over the customer data that powers your business.
What are the main challenges and risks of implementing DLP in Salesforce?
Protecting sensitive data in Salesforce can be complex because of how dynamic and customizable the platform is. Sensitive data often hides in unexpected places such as case notes, attachments, and Chatter posts, creating blind spots for admins.
Key challenges include:
- Data visibility gaps: Sensitive data can exist in free-text fields, comments, or files that aren’t easily searchable.
- Overexposed access: Too many users often have unnecessary data visibility.
- Human error: Employees may enter or share sensitive data in unsecured areas.
- Sandbox risks: Production data copied into unprotected test environments.
- Limited native detection: Salesforce’s built-in tools only identify a few data types and don’t remediate them.
- Without comprehensive Salesforce DLP controls, these risks compound over time—making breaches, compliance fines, and trust erosion almost inevitable.
Why is automated DLP better than manual DLP approaches for Salesforce?
Manual DLP relies on human diligence, training, and static validation rules that can’t keep pace with today’s data volume. It’s time-consuming, reactive, and prone to human error. Automated Salesforce DLP solutions like Strac continuously monitor your org, scanning records, attachments, and integrations for sensitive data in real time.
Automation delivers clear advantages:
- Speed: Detect and redact sensitive data instantly as it enters Salesforce.
- Coverage: Scan across all fields, comments, and files continuously.
- Consistency: Apply policies 24/7 without relying on user behavior.
- Accuracy: Reduce false positives using ML and content-aware detection.
- Auditability: Maintain a full, automated trail for compliance reports.
- With automation, Salesforce DLP evolves from a manual clean-up task into a continuous protection layer that prevents issues before they spread.
What are the limitations of native Salesforce security controls for DLP?
Salesforce provides strong access and encryption controls, but its native features were not built for content-level data protection.
Key limitations include:
- No real-time redaction: Salesforce cannot automatically mask or redact sensitive data in email-to-case threads, comments, or attachments.
- Limited pattern detection: Einstein Data Detect identifies only a few data types (like credit card or SSN) and doesn’t remediate them.
- Reactive monitoring: Event Monitoring tracks user activity but doesn’t block risky actions as they occur.
- Sandbox exposure: Salesforce Data Mask only applies to lower environments, leaving production data unmanaged.
- Coarse access controls: Role and field-level security can’t prevent data leaks if sensitive content is entered into open fields.
- In short, Salesforce’s security tools help define “who can access what,” but not “what should never be visible.” That’s where modern Salesforce DLP steps in.
How does Strac's DLP solution address the gaps in Salesforce's native security?
Strac delivers automated, real-time data protection purpose-built for Salesforce. It fills the gaps that native tools can’t cover by combining data discovery, classification, redaction, and compliance reporting in one platform.
Here’s how Strac enhances Salesforce DLP:
- Instant redaction and masking: Automatically removes PII or PHI from case comments, attachments, and email-to-case messages.
- Secure vault storage: Sensitive data is quarantined in Strac’s secure vault, accessible only to authorized users.
- Exfiltration detection: Monitors report exports and API usage, flagging suspicious downloads or unusual data flows.
- Cross-app protection: Applies consistent DLP policies across Salesforce and other SaaS tools like Slack, Google Drive, and Zendesk.
- Agentless integration: Connects via API and starts protecting data in minutes without impacting performance.
- By combining Salesforce DLP with broader DSPM capabilities, Strac gives organizations full visibility and control over where sensitive data lives, how it moves, and how it’s protected.











.webp)














.webp)
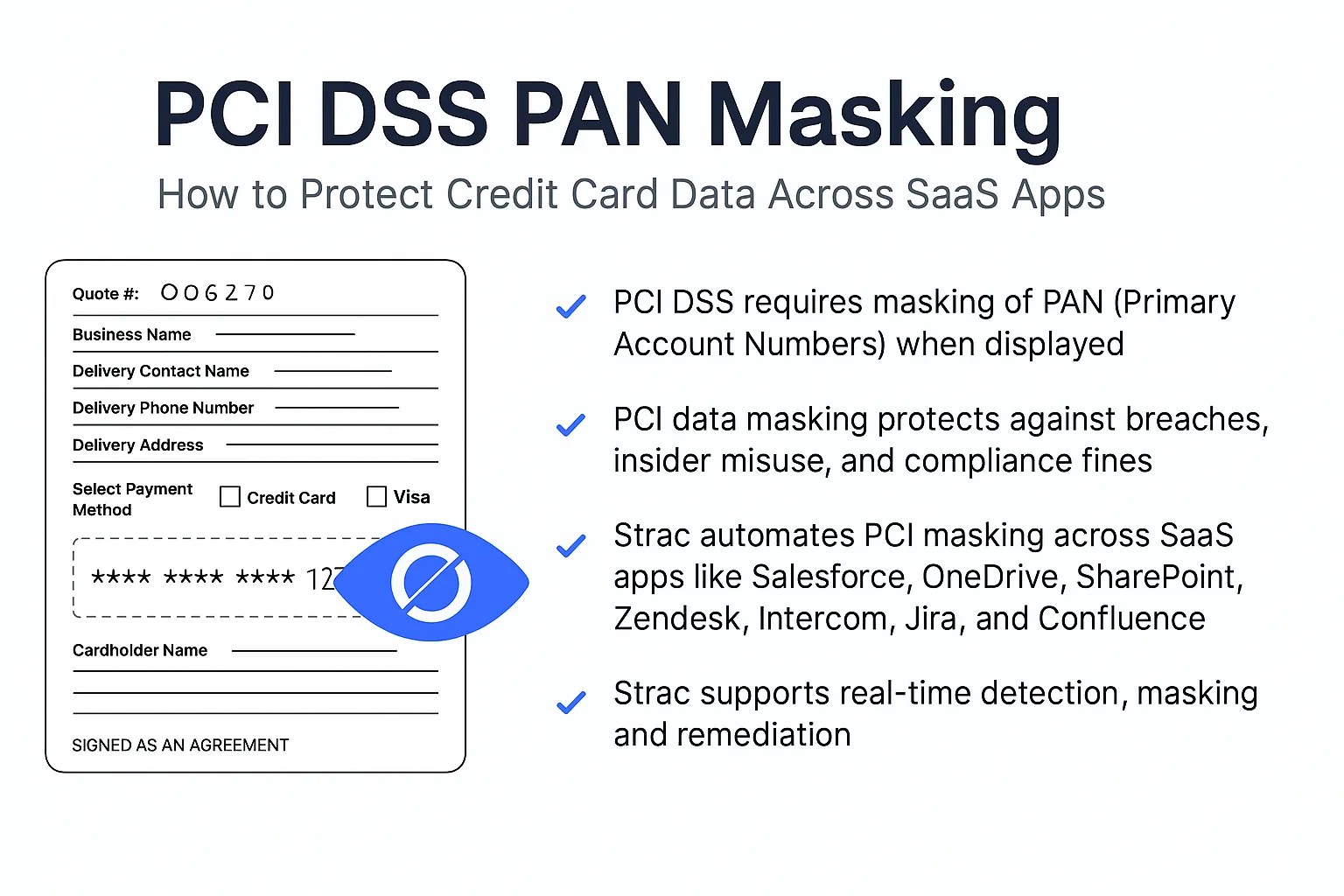







.avif)


