Google Drive DLP: Protect Sensitive Data in Google Drive
Prevent Data Leaks, Get PII Alerts and Ensure your organization complies!
Google Drive has become an essential tool for organizations of all sizes, providing a secure and convenient way to store and collaborate on files in the cloud. However, as the use of Google Drive has become more widespread, so too has the risk of data breaches and security incidents. This is where Data Loss Prevention (DLP) on Google Drive comes into play, offering powerful tools and technologies to help organizations protect their sensitive data and prevent unauthorized access.
Implementing a Google Drive DLP strategy is not optional anymore. If your team uses Google Drive to collaborate, share files, or store customer data, then sensitive information is already moving through folders, shared links, comments, exports, and downloads. Without controls, PII, PHI, PCI, contracts, source code, and internal documents can be overshared in seconds. In this blog, we examine how to implement Data Loss Prevention (DLP) for Google Drive in a way that actually works in modern SaaS environments.
Google Drive DLP is the technology and policy framework that allows organizations to discover, monitor, and protect sensitive data stored and shared within Google Drive. It ensures that confidential information such as PII, PHI, PCI, credentials, or intellectual property cannot be exposed accidentally or intentionally.
Cloud collaboration is powerful but risky — files move fast across My Drive, Shared Drives, and external domains. Without DLP, visibility drops and sensitive data can slip outside your control.
A healthcare provider might accidentally share a Drive folder with patient lab results via a public link, instantly violating HIPAA. A financial firm could upload credit-card spreadsheets to Drive and share them externally, creating a PCI breach.
Strac’s Google Drive DLP solves these risks by:
With a smart DLP layer, Google Drive transforms from an open collaboration tool into a secure, compliant workspace that protects your most valuable data.
Google Data Loss Prevention (DLP) is part of the overall company's strategy to prevent, protect, and secure against leakage, loss, or misuse of the company’s confidential, sensitive data (API keys, Personally Identifiable Information, credit card numbers, and PHI). DLP control typically works by identifying, monitoring, and controlling the flow of sensitive data across various channels including emails, file sharing, instant messaging, cloud services, and web browsing. DLP is important to protect data wherever it resides, whether in storage, transit, or use.
In the context of Google Drive, DLP refers to a set of security features that help organizations protect their sensitive data stored on the cloud-based platform. Specifically, DLP on Google Drive can help prevent data breaches by detecting and blocking the unauthorized sharing of sensitive data with people who shouldn't have access to it. DLP gives you control over what users can share and prevent unintended exposure of sensitive data such as credit card numbers or identify numbers. Google Drive DLP control scans files for sensitive contents and prevents users from sharing such files.

There are several ways that DLP can be implemented on Google Drive, including:
One of the main benefits of DLP on Google Drive is that it can help organizations maintain compliance with data protection regulations. For example, the General Data Protection Regulation (GDPR) requires organizations to take measures to protect personal data, including implementing appropriate security measures and ensuring that sensitive data is not shared with unauthorized parties. By using DLP on Google Drive, organizations can help ensure that they are meeting these regulatory requirements and avoid expensive data breaches.
Another important benefit of DLP on Google Drive is that it can be customized to meet the specific needs of each organization. For example, an organization may choose to block the sharing of certain types of data, such as credit card numbers or social security numbers, to prevent accidental or intentional exposure.
Additionally, DLP on Google Drive can be configured to provide notifications and alerts to users when they attempt to share sensitive data, helping to educate them about the risks involved and encouraging them to use best practices for protecting their data. DLP on Google Drive can also help organizations protect against internal threats, such as employees' accidental or intentional exposure of sensitive data. By detecting and preventing the unauthorized sharing of sensitive data, DLP can help organizations reduce the risk of data breaches and protect their intellectual property and confidential information.

Google Drive has had several incidents of data breaches due to the lack of DLP. Here are a few of them:
Based on aggregated, anonymized data across Strac’s enterprise customers, we analyzed how sensitive data actually lives and leaks inside Google Drive environments.
| Files scanned | 10M+ files across Google Drive deployments |
| Sensitive data exposure | 34% contained at least one PII, PCI, or PHI element |
| External sharing risk | 12% of sensitive files were shared outside the organization |
| Public link exposure | 3.2% had “Anyone with the link” enabled |
| Most common data types | Credit cards (28%), SSNs (19%), API keys (17%), Emails (15%), Phone numbers (12%) |
| Time to detection | < 5 minutes with Strac vs. often undetected natively |
| Spreadsheets (.xlsx, .gsheet) | 47% contain sensitive data |
| Documents (.docx, .gdoc) | 31% contain sensitive data |
| PDFs | 29% contain sensitive data |
| Images (OCR scanned) | 14% contain sensitive data |
| Presentations | 9% contain sensitive data |
| Financial Services | 412 sensitive files per 1,000 |
| Healthcare | 387 sensitive files per 1,000 |
| Technology | 298 sensitive files per 1,000 |
| Professional Services | 276 sensitive files per 1,000 |
| Retail / E-commerce | 243 sensitive files per 1,000 |
Data aggregated and anonymized across Strac enterprise customers. Last updated: January 2026.
Google Workspace Business Starter, Business Standard and Business Plus do not have DLP support.
Google Workspace Enterprise has DLP support.
Although Google Workspace Business Plans do not have native Data Loss Prevention (DLP) features, there are several steps you can take to protect your account and sensitive information:

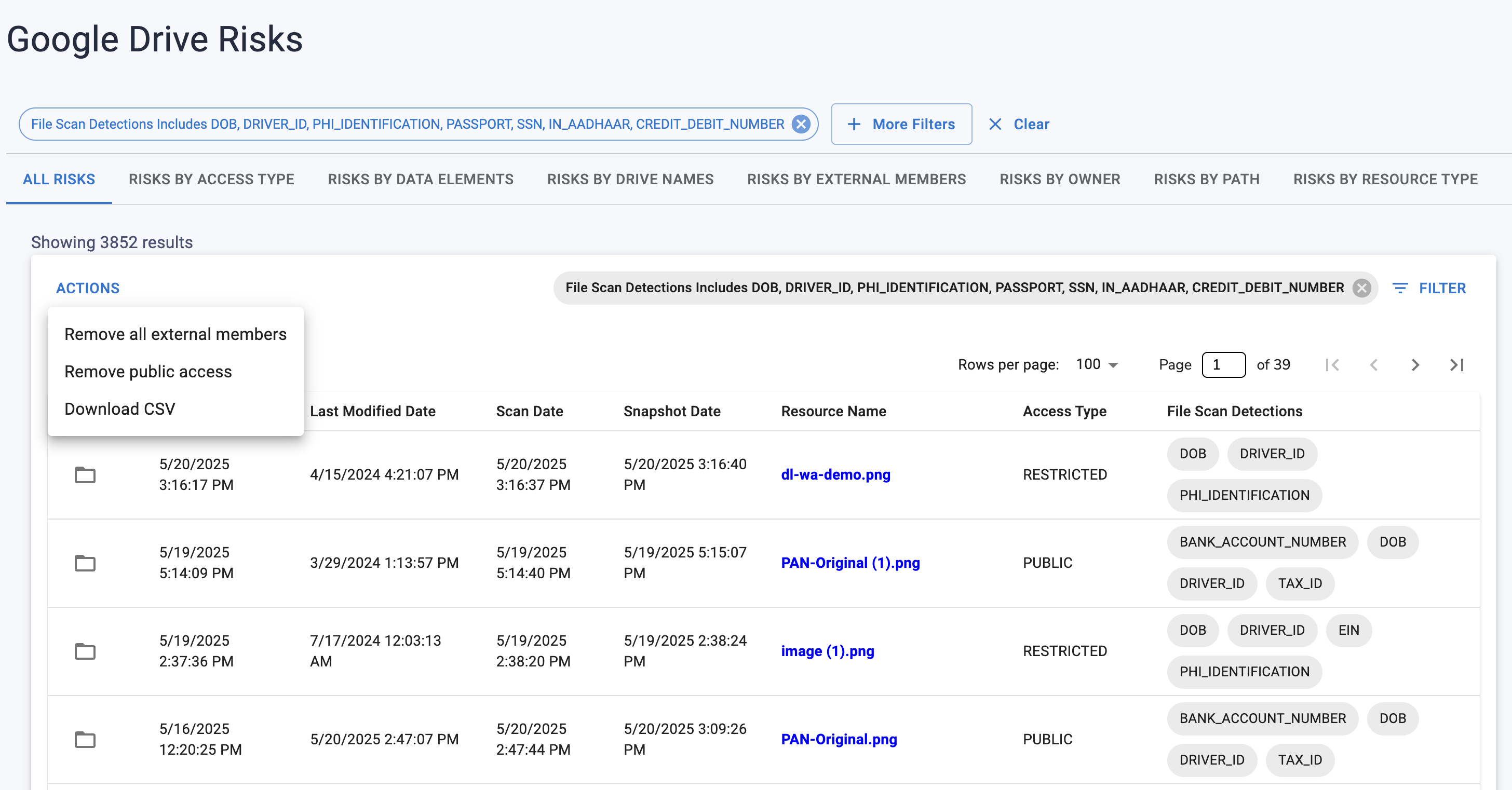
Google Drive is a hub for collaborative file sharing, but without proper security controls, sensitive data can easily be exposed. DLP detections in Google Drive help organizations identify policy violations in real-time, preventing leaks of Personally Identifiable Information (PII), Payment Card Industry (PCI) data, and Protected Health Information (PHI).
DLP solutions for Google Drive continuously scan files to detect sensitive data based on predefined policies, contextual keywords, and pattern matching (such as regex for credit card numbers or social security numbers). These detections typically involve:

Organizations implementing Google Drive DLP typically focus on detecting:
Google Drive’s collaboration power also makes it a potential data security risk if left unmonitored. Files are constantly created, copied, and shared — often beyond the organization’s intended boundaries.
Common risk points include:
A single misconfigured folder could expose confidential client data, violate GDPR, or leak IP to competitors.
Strac’s Google Drive DLP eliminates these weak spots through:
With Strac, organizations can keep collaboration frictionless while maintaining airtight security.
Data Loss Prevention (DLP) in Google Drive is important for organizations looking to protect sensitive information from unauthorized access or sharing. Here’s a step-by-step guide on how to set up DLP rules and create custom content detectors.
Custom content detectors allow you to tailor DLP rules to your organization's specific needs.
By following these steps, organizations can effectively implement Data Loss Prevention rules in Google Drive, enhancing their overall data security posture while ensuring compliance with relevant regulations.
By following these steps, organizations can effectively implement Data Loss Prevention rules in Google Drive, enhancing their overall data security posture while ensuring compliance with relevant regulations.
| Feature | Google Native DLP | Strac |
|---|---|---|
| Works with any Google Workspace plan | ❌ Enterprise-only | ✅ Any plan |
| Free trial | ❌ | ✅ |
| Feature | Google Native DLP | Strac |
|---|---|---|
| PII detection (SSN, email, phone, etc.) | ✅ | ✅ |
| PCI detection (Credit Card / PAN) | ✅ | ✅ |
| PHI / HIPAA detection | ⚠️ Limited | ✅ |
| Custom detectors (regex + context) | ✅ | ✅ Unlimited |
| Source code / API key detection | ❌ | ✅ |
| OCR for images & scanned PDFs | ❌ | ✅ |
| Platform | Google Native DLP | Strac |
|---|---|---|
| Google Drive | ✅ | ✅ |
| Gmail | ✅ | ✅ |
| Docs / Sheets / Slides | ✅ | ✅ |
| Customer Support (Salesforce, Zendesk, Intercom) | ❌ | ✅ |
| Atlassian (Jira, Confluence) | ❌ | ✅ |
| AWS | ❌ | ✅ |
| Azure | ❌ | ✅ |
| Slack | ❌ | ✅ |
| Microsoft 365 | ❌ | ✅ |
| ChatGPT & GenAI tools | ❌ | ✅ |
| Feature | Google Native DLP | Strac |
|---|---|---|
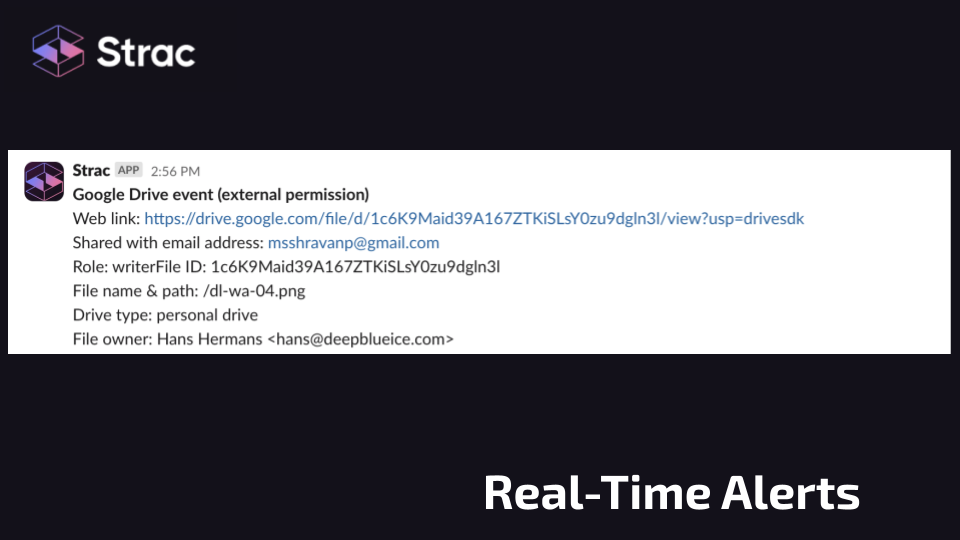
| Real-time alerts | ✅ | ✅ |
| Blocking (policy enforcement) | ✅ Drive/Gmail | ✅ |
| Auto-labeling (apply labels automatically) | ❌ | ✅ |
| Auto-redaction of sensitive data | ❌ | ✅ |
| Auto-delete sensitive files | ❌ | ✅ |
| Revoke external or public sharing | ❌ | ✅ |
| Feature | Google Native DLP | Strac |
|---|---|---|
| Real-time scanning | ✅ | ✅ |
| Historical file scanning DSPM | ❌ | ✅ |
| Scan files larger than 10MB | ❌ | ✅ |
| Framework | Google Native DLP | Strac |
|---|---|---|
| HIPAA | ⚠️ Basic | ✅ |
| PCI-DSS | ⚠️ Basic | ✅ |
| SOC 2 | ✅ | ✅ |
| ISO 27001 | ✅ | ✅ |
The major downsides of implementing the above section are:
Although Google Workspace Business Plans do not have DLP support, Enterprise plan does have the DLP Support.
Here are the most important limitations security leaders must understand:
Google Workspace DLP does not give you a real-time, unified view of:
It provides some one-off reports, but not a DSPM-style continuous inventory with risk scoring, access posture, or historical traceability.
Strac provides a single-pane, live view across Google Drive, SaaS apps, cloud stores, ChatGPT/GenAI, and endpoints.
Drive DLP cannot:
This means admins are forced to fix exposures manually — one file at a time — which is impossible at enterprise scale.
Strac performs one-click bulk remediation: remove external users, restrict public links, revoke access, and fix thousands of files instantly.
Google’s DLP does not provide a consolidated risk timeline:
Strac enriches every file with full audit trails, modifiers, timestamps, and access changes.
Google can show a basic warning when sharing externally, but cannot:
Strac does all of this — and reduces accidental data leaks dramatically.
Drive DLP scans:
It struggles with:
Strac scans 100% of the file, including large docs, images, OCR layers, PDFs, and more.
This is a critical gap:
Google Workspace Enterprise DLP does not redact, mask, or sanitize sensitive data inside Drive files.
This means:
Strac can automatically redact or mask sensitive data, allowing users to see the file without exposing private information — a huge win for compliance and least-privilege access.
Gmail’s built-in DLP:
But it cannot redact or mask:
This is a major limitation for regulated industries: once an email is sent, sensitive data is fully exposed to recipients.
Strac provides full inline redaction and masking, allowing emails to be delivered safely without leaking PII/PHI/PCI.
According to Google’s own Admin FAQ, Google Workspace Enterprise DLP does not scan audio or video files stored in Google Drive, including common formats such as:
Reference: Google Workspace Admin FAQ on supported file types.
This is a significant blind spot because sensitive data increasingly appears in:
Strac can scan transcripts, audio content, and video frames (via OCR/ML) to detect sensitive information hidden inside multimedia files.
Yes, Strac Google Drive DLP will give you visibility and alerts to Slack, Teams or your SIEM service if anyone downloads any file OR any sensitive file. Check out https://www.strac.io/blog/how-to-prevent-downloads-in-google-drive
Yes, Strac Google Drive DLP will give you visibility and even prevent excessive file downloads. Excessive file downloads could be any number of downloads in a given time frame. Also, you can configure alert on sensitive file downloads only. Sensitivity is any data elements that is configured from our Sensitive Data Catalog. Check out https://www.strac.io/blog/how-to-prevent-downloads-in-google-drive
Yes, Strac Google Drive DLP will give you visibility and even block external file sharing
Short answer: Yes. Strac monitors inbound Google Drive shares (“Shared with me” / “Incoming”), alerts your security team, and can automatically revoke your users’ access—at scale—without you having to disable all external sharing.
What Strac specifically does
vendor.com, lawfirm.com.Why this matters (real-world attack fit)
TL;DR for admins
A business using the Strac Google Drive DLP application can configure a list of sensitive data elements to mask or redact. Here are some sensitive data elements that can be redacted with our DLP application.

Strac is a data loss prevention software that detects and redacts sensitive data across all communication channels. It has no-code integrations with Google Drive, Gmail, Slack, Zendesk, Intercom, Office 365, etc.

A business using the Strac Google Drive DLP application can configure a list of sensitive data elements to mask or redact. The list below shows a list of sensitive data that can be redacted using the Strac Google Drive DLP application:
Now, let’s get down to how Strac protects your Google Drive workspace.
The following steps show how the Strac Google Drive DLP application protects your team's Google Drive workspace and saves your organization from data loss or leakage.
Strac Google Drive DLP application detects or discovers sensitive files. When integrated and turned on, the Strac Google Drive DLP application detects sensitive files shared.
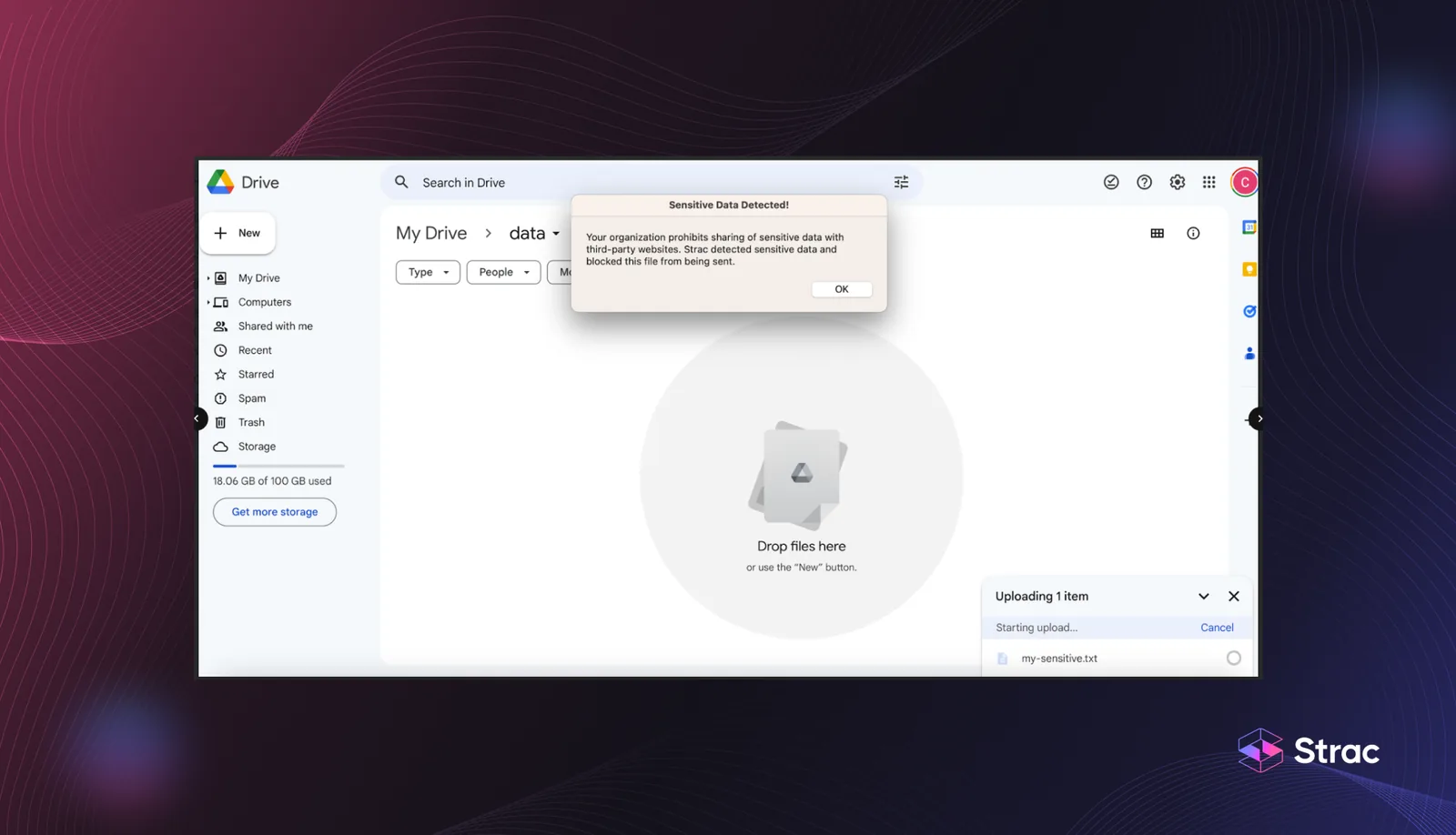
Strac prevents file sharing. Teams can build workflows around file sharing. E.g., send a file only if an owner approves it. If the owner rejects it, that file to an external party won't be sent.
Strac masks or redacts sensitive files or files containing sensitive data while giving authorized users access to those redacted contents in the Strac UI vault.


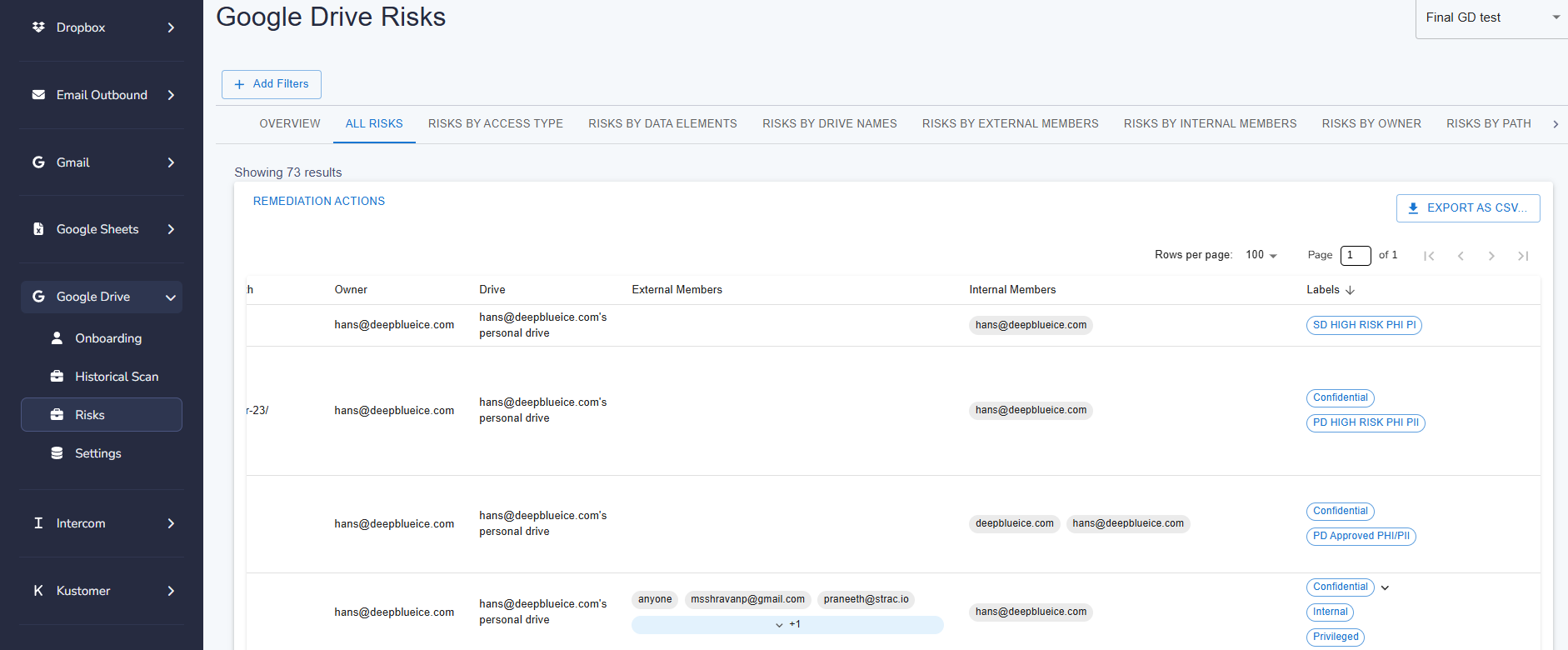
Strac makes Google Drive labels actionable by bringing them directly into the Strac Vault, where they can be evaluated alongside real exposure and access signals. Instead of treating labels as static metadata that lives only in Google Drive, Strac allows security and compliance teams to see how labeled data is actually stored, shared, and accessed across the organization, all in one place.
• Google Drive labels applied natively in Drive are automatically visible in Strac Vault
• Labels appear with full context, including sensitivity findings, sharing status, owners, paths, and access levels
• Label updates in Strac Vault stay aligned with Google Drive, keeping governance consistent
• Labeled files can be quickly assessed for risk by correlating classification with exposure signals like public links or external access
Click here to book a demo session and learn how to integrate Strac into your Google Drive workspace. Strac's unique redaction technology will improve your DLP techniques, and help you protect sensitive data while eliminating compliance risks. Read more here to learn how Strac integrates with other SaS apps. Additionally, Strac can send Google Drive PII alerts to configured users.

Learn more about:
How secure is Microsoft One Drive?
Implementing Google Drive DLP ensures your organization can collaborate safely while keeping sensitive data under control. It helps prevent leaks of PII, PCI, and PHI by continuously monitoring files and applying automated rules. With the right policies in place, Google Drive DLP strengthens compliance, governance, and operational efficiency across teams.
Key benefits include:
While both tools enhance security, Strac’s Google Drive DLP provides a far more comprehensive and intelligent layer of protection. It’s built to detect and act on threats in real time, integrating machine learning and OCR for deeper visibility into Drive files. Compared to Google Workspace Enterprise DLP, Strac adds automation, wider coverage, and faster response.
Here’s how Strac stands out:
Yes. Strac Google Drive DLP monitors every sharing event, link change, and download pattern to stop risky behavior before data exposure occurs. It detects both accidental and intentional sharing outside your domain and applies instant protective actions. This proactive approach helps organizations maintain compliance without slowing down productivity.
Strac automatically:
The Google Drive DLP feature within Strac detects a broad range of sensitive data types, ensuring total coverage across your documents, sheets, and shared drives. Its ML engine identifies structured and unstructured data across text, images, and compressed files. By mapping and classifying sensitive content, Google Drive DLP allows you to protect it through clear labeling and policy enforcement.
Detected data types include:
Setting up custom rules in Google Drive DLP gives your business fine-grained control over what’s protected and how violations are handled. These rules define what counts as sensitive data, where it can live, and what happens when it’s shared incorrectly. Using Strac’s automation, you can create intelligent workflows that scan, classify, and remediate sensitive data across your entire Drive environment.
To configure DLP rules effectively:
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

