TL;DR: In Short: Strac Helps Ensure Notion's HIPAA Compliance
- Notion is a productivity app that needs to be protected due to regulatory compliance and insider threats.
- Strac Notion App is a Data Leak Prevention (DLP) software that discovers and redacts sensitive messages and files from Notion pages, blocks, and comments.
- Strac's redaction experience blocks sensitive PII or PHI data.
- A business can configure a list of sensitive data elements to redact and compliance, risk, and security officers will get audit reports of who accessed what messages.
- Visit Strac's compilation of sensitive data items that are autonomously spotted and masked by Strac.
- Checkout our video demo below to learn about how Strac Notion DLP and redaction works
The Challenge of Meeting HIPAA Compliance for Notion
Notion is a productivity app that enables users to write, plan, collaborate, and organize. It offers features like notes, databases, kanban boards, wikis, calendars, and reminders. Users can connect these components to create their own systems for knowledge management, note taking, data management, and project management.
In a platform like Notion where data can be easily shared, collaborated and exported, it is more important than necessary that Notion account needs to be protected:
- Regulatory Compliance: Many industries are subject to regulations requiring certain data protection standards, such as GDPR for personal data in the European Union, or HIPAA for health information in the U.S. A DLP strategy can help ensure compliance with these regulations.
- Insider Threats: Verizon's 2021 Breach Investigation Report state that the Healthcare and Finance industries experience the most incidents involving employees misusing their access privileges and also suffer the most from lost or stolen assets. Even trusted employees can sometimes unintentionally or intentionally cause data leaks. Notion is used by teams for collaboration, and DLP can help ensure that this collaboration can take place securely, without risking data leaks. In a platform like Notion where data can be easily shared and exported, DLP provides a way to maintain control over the data, ensuring that it doesn't end up in the wrong hands.
Why Notion Alone Is Not Compliant for PHI, PCI & PII
Notion is an exceptional collaboration and knowledge-management platform; however, it is not designed as a compliant environment for regulated data such as PHI, PCI, and high-risk PII. Organizations in healthcare, finance, HR, insurance, and public sector environments need strict controls that enforce data minimization, real-time monitoring, and automated remediation; Notion does not natively provide these enforcement layers. As a result, teams storing sensitive data in pages, databases, comments, or file uploads unknowingly introduce compliance gaps that increase exposure, audit risk, and potential data leakage.
The main compliance gaps in Notion for PHI, PCI, and PII include:
- No native DLP controls; Notion cannot block, redact, or mask sensitive data such as SSNs, credit cards, medical information, or passport IDs.
- Limited auditability; Notion does not offer granular logs that trace sensitive data movement or prove compliance posture.
- No automated classification or scanning; sensitive fields in tables, notes, attachments, and embedded content remain undiscovered and unprotected.
- Insufficient support for regulatory frameworks; Notion is not certified for HIPAA by default and does not include PCI DSS–aligned controls.
- High exposure through sharing; pages and databases can be shared broadly, increasing risks of accidental duplication, screenshot sharing, or external access.
These gaps mean regulated teams cannot rely on Notion alone for compliant operations; they need a Notion DLP solution that can continuously discover sensitive data, enforce redaction and blocking, minimize oversharing, and maintain an auditable record of every high-risk event.
How Strac Can Help Notion Achieve HIPAA Compliance
Strac Notion App is a Data Leak Prevention (DLP) software which is highly alert driven:
- It discovers (aka detects) sensitive messages & files from Notion pages, blocks, databases, comments. You can turn on Strac Notion App to just get findings of sensitive messages shared.
- It masks (aka redacts or removes) sensitive messages and files from Notion pages, blocks, and comments while allowing authorized users to view those messages/files in Strac UI Vault. With Strac's redaction experience sensitive PII or PHI data is blocked.
- A business can configure a list of sensitive data elements (SSN, DoB, DL, Passport, CC#, Debit Card, API Keys, etc.) to redact. Compliance, Risk and Security officers will get audit reports of who accessed what messages.
Visit Strac's compilation of sensitive data items that are autonomously spotted and masked by Strac. More details can be found at this link: https://www.strac.io/blog/strac-catalog-of-sensitive-data-elements.
Notion DLP Use Cases for Regulated Teams
Notion DLP is essential for organizations that rely on Notion for collaboration but operate with PHI, PCI, or PII under strict regulatory requirements. Modern teams need real-time visibility into sensitive data flowing through databases, documents, templates, and shared pages; without automated controls, a single mis-entered medical record, credit card number, or employee profile can create a major compliance incident. With Strac Notion DLP, regulated teams can transform Notion into a safer, policy-enforced workspace without disrupting how employees collaborate.
Key Notion DLP use cases include:
- Healthcare & Healthtech; detect and redact PHI that appears in care notes, patient tickets, intake forms, screenshots, or product documentation to support HIPAA alignment.
- Fintech & Financial Services; block PCI data such as credit card numbers, bank account details, or loan files from appearing in shared team workspaces.
- HR & People Ops; protect PII like SSNs, national IDs, payroll data, and performance documents stored inside Notion databases and archives.
- Customer Support & Success Operations; prevent sensitive customer data from entering shared Notion spaces when agents paste logs, chat transcripts, or email excerpts.
- Engineering & Product Teams; remove secrets, tokens, API keys, and debugging logs before they are saved in documentation pages or project hubs.
- Legal, Compliance & Vendor-Management Teams; ensure regulated documents uploaded to Notion are automatically scanned, labeled, and remediated to maintain audit readiness.
Strac enables all of these use cases with real-time detection, pattern-agnostic ML/OCR scanning, auto-redaction, blocking, labeling, and full visibility across every Notion workspace; turning a collaboration tool into a secure, compliant knowledge environment without changing a team’s workflow.
Strac Notion DLP
Original Notion Page with Sensitive Data

Original Notion Page with Redaction

Spicy FAQs on Notion DLP
Does Notion support HIPAA compliance by default?
No; Notion does not support HIPAA compliance by default. Out of the box, Notion is a powerful collaboration tool but it is not designed as a HIPAA-compliant electronic health record or clinical system. For most organizations, this means you should not treat Notion as a primary system of record for storing PHI such as diagnoses, treatment notes, lab results, or detailed patient histories. Regulated healthcare and healthtech teams typically use Notion only for non-PHI collaboration and rely on a DLP platform like Strac to prevent accidental PHI from leaking into workspaces.
How can I prevent employees from storing PHI or PII in Notion?
Preventing employees from storing PHI or PII in Notion requires a combination of policy, user training, and automated enforcement. Written policies and security awareness help, but they are not enough when people copy-paste tickets, emails, or screenshots under time pressure; this is where Notion DLP becomes critical. With Strac, you can define policies that automatically detect and remediate sensitive data anywhere it appears in pages, blocks, databases, or file uploads so that risky content never persists.
Practical ways to prevent PHI/PII in Notion include:
- Create a clear Notion usage policy; explicitly state that PHI, PCI, or highly sensitive PII must not be stored in Notion and point people to approved systems of record.
- Deploy Strac Notion DLP; automatically scan workspaces for PHI/PII and redact or block violations so you are not relying only on manual policing.
- Use alerts and workflows; notify security or compliance teams when risky content is detected so they can coach specific teams or adjust policies.
- Limit external sharing; tighten workspace, page, and database sharing to reduce the blast radius if someone accidentally copies sensitive data into Notion.
By combining process, training, and automated DLP controls, you make it significantly harder for regulated data to live inside Notion at all.
Can Strac automatically redact sensitive data from Notion pages?
Yes; Strac can automatically redact sensitive data from Notion pages, databases, and files based on your policies. Instead of just alerting, Strac applies inline remediation so high-risk content is removed or masked directly at the source. This helps prevent compliance issues and reduces the need for manual cleanup after the fact.
With Strac Notion DLP, you can:
- Automatically redact PHI, PCI, and PII from text blocks, comments, and database fields.
- Mask or delete sensitive values inside structured tables without breaking the rest of the record.
- Apply different remediation actions per policy; for example, redact patient identifiers but block full credit card numbers entirely.
This type of automated redaction turns Notion from a blind spot into a controlled, monitored space that aligns with your data governance rules.
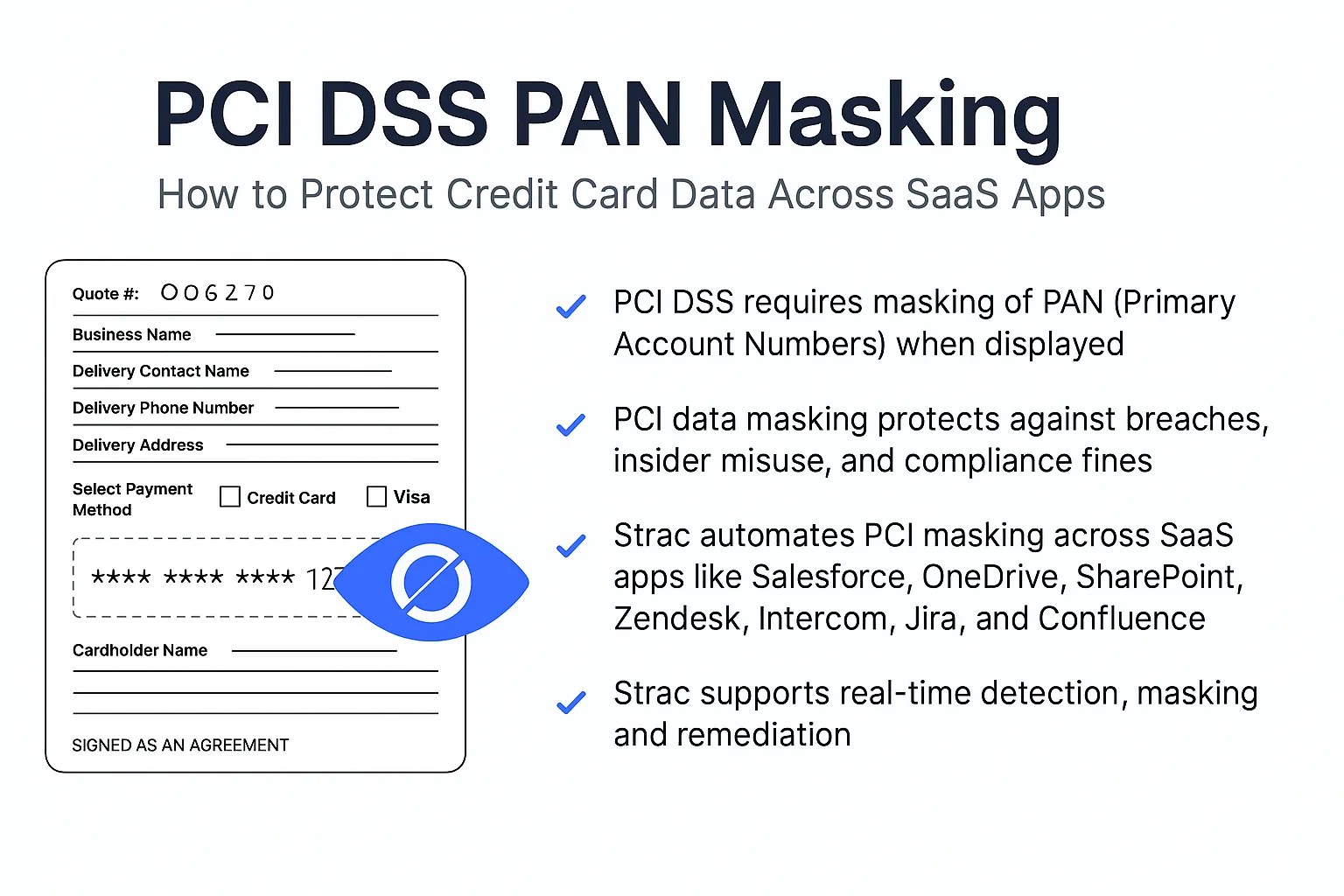
Does Notion allow PCI-compliant storage of cardholder data?
No; Notion is not a PCI DSS–scoped system and should not be used to store cardholder data such as full PANs, CVV/CVC codes, or unmasked expiration details. PCI compliance requires very strict technical and process controls around how cardholder data is collected, transmitted, stored, and accessed; Notion is not designed to meet those controls as a cardholder data environment. Even pasting a single full card number into a shared Notion page or database can introduce unnecessary PCI scope and audit risk.
The safer approach is:
- Never use Notion to store full payment card information.
- Use Strac Notion DLP to detect and redact any accidental card numbers that employees paste into notes, requests, or troubleshooting documents.
- Keep all cardholder data in PCI-approved systems and treat Notion as a collaboration layer for non-sensitive operational context only.
This keeps your PCI footprint small and avoids pulling Notion into your audit boundary.
How does Strac detect PHI inside Notion databases and pages?
Strac detects PHI inside Notion databases and pages using content-aware scanning that goes beyond simple regex matching. It connects to your Notion workspace; continuously scans text blocks, properties, comments, and file metadata; and uses ML/OCR to identify patterns consistent with PHI and other sensitive data. This allows Strac to find health information even when it appears in free-form notes, screenshots, or mixed with non-sensitive text.
In practice, Strac Notion DLP can:
- Scan structured data in databases; such as patient identifiers, insurance IDs, or clinical details that land in custom fields.
- Analyze unstructured notes in pages; comments and checklists where people often paste context from EHRs, emails, or chat tools.
- Run document and image analysis on attachments; using OCR to detect PHI inside PDFs, exported reports, and screenshots.
- Apply policy-driven remediation; redacting, masking, or deleting fields and values that match your PHI rules, while logging each event for auditing.
This combination of deep content analysis and automated enforcement ensures PHI does not quietly accumulate in Notion; instead it is detected quickly and remediated in line with your compliance posture.











.webp)














.webp)








.avif)


