What is Data Loss Prevention? DLP Best Practices,Use Cases & Benefits
Stay ahead of data breaches, protect sensitive information, and prevent data loss with our comprehensive guide to Data Loss Prevention in 2026 with these DLP best practices.
This article talks about Data Loss Prevention and its importance in protecting sensitive data, ensuring compliance, and preventing breaches.
DLP tools protect data by:
To maximize DLP investment, organizations must:
Choose the ideal DLP software for an organization based on:
Data loss can be a nightmare, costing businesses valuable time and money. Losing crucial data means losing countless hours of hard work, critical data, and ultimately client trust. Data breaches are an unfortunate reality of our digital world and are increasingly common.
According to Statista, the average cost of a data breach globally in 2022 was $4.35 million, a 2.6% increase from 2021. Protecting sensitive information has never been more crucial in today's interconnected society.
Because of these risks, organizations are looking for practical DLP use cases and proven data loss prevention best practices to protect sensitive data across SaaS apps, cloud platforms, endpoints, and AI tools. Common DLP use cases include preventing employees from sharing PII in tools like Slack or Google Drive or pasting sensitive data into AI prompts. Applying strong data loss prevention best practices helps security teams reduce risk, maintain compliance, and protect sensitive information wherever it moves.
Solutions, like Strac, provide unparalleled visibility and control into an organization's data while mitigating fraudulent activity.

DLP is the practice of detecting and preventing unauthorized access to sensitive data within and outside a network. DLP security solutions are more than just data storage and retention policies. They help organizations maintain regulatory compliance. DLP solutions promptly respond to breaches or security incidents with alerts, encryption, and data isolation capabilities. DLP software accelerate incident response by identifying threats and anomalous activity during routine monitoring.
Moreover, they ensure compliance with regulations like HIPAA and GDPR. A comprehensive DLP system provides complete insight into all network data, whether in use, motion, or rest.
Data loss prevention has become essential today because data moves faster, lives in more places, and is exposed to more risks than ever before. Organizations no longer operate from a single network perimeter; sensitive information travels through SaaS apps, cloud storage, AI tools, and employee devices. With this constant movement, companies need data loss prevention to maintain visibility; enforce policies; and prevent costly mistakes that can lead to breaches, fines, or reputational damage.
Traditional security tools cannot keep up with the velocity of data in modern work environments. Critical information like PII, PHI, PCI, financial data, and secrets travels through Slack messages, Google Drive files, Salesforce tickets, customer support chats, and GenAI prompts. Even one accidental upload, misconfigured file, or unauthorized access can create exposure that takes months to detect.
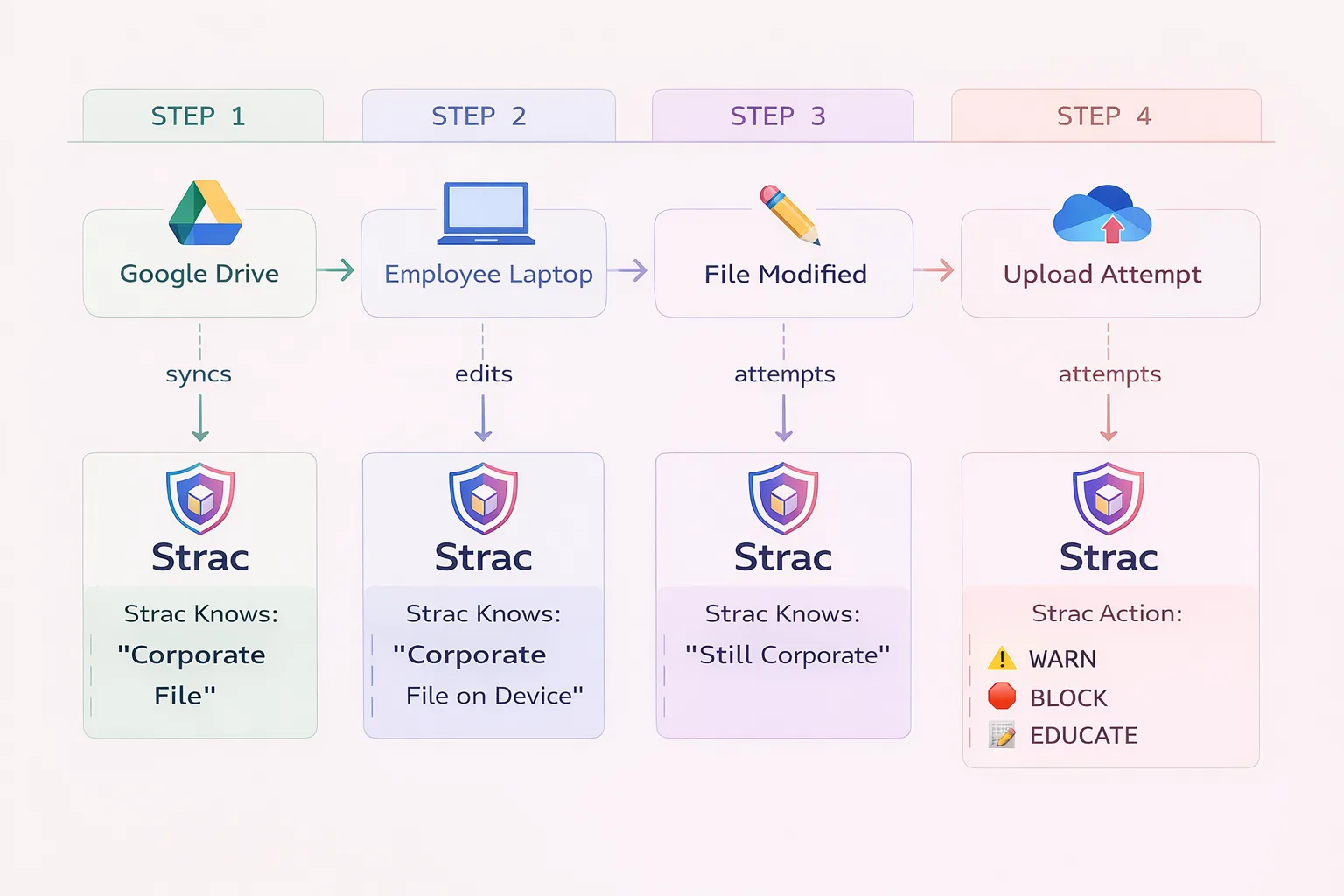
Strac solves this by providing real-time data loss prevention across the full data surface; SaaS, Cloud, GenAI, and Endpoints. Strac discovers sensitive data automatically, classifies it with ML and OCR, and applies instant remediation actions like redaction, masking, blocking, and quarantine.
Modern data loss prevention works by continuously inspecting data where it is created, stored, shared, or accessed, then applying policies that prevent unauthorized exposure or misuse. As companies adopt SaaS tools and AI systems at scale, data loss prevention must operate outside the traditional network perimeter and function in real time. Effective DLP today relies on content awareness, automation, and broad coverage to monitor data regardless of location or format.
Modern DLP systems identify sensitive data using ML and OCR; not just regex. They analyze text, attachments, images, PDFs, logs, and even AI prompts or responses. When sensitive elements are detected, the DLP engine enforces security policies like redaction, blocking, encryption, deletion, or alerting.
Strac enhances this with agentless, real-time inspection across tools like Slack, Zendesk, Google Workspace, Salesforce, AWS, and ChatGPT. Every piece of sensitive data triggers immediate remediation; organizations gain visibility, consistent control, and reduced risk across their entire digital ecosystem.
Data Loss Prevention operates through a sophisticated system of monitoring, detection, and enforcement mechanisms. The process begins with data discovery and classification, where the DLP solution scans and categorizes sensitive information across the organization’s network, devices, and cloud storage.
This includes scanning both structured and unstructured data, from databases to documents and emails.
The system employs advanced pattern recognition and machine learning algorithms to identify sensitive data types such as CC numbers, social security numbers, & proprietary information. Once identified, the DLP solution applies predefined policies and rules to control how this data can be used, shared, or transmitted.

Organizations face various types of data threats that can compromise sensitive information & lead to significant financial and reputational damage.
Understanding the primary causes of data leaks is crucial for implementing effective prevention strategies.
The most common cause of data leaks stems from employee mistakes, including:
Technical shortcomings that can lead to data leaks:
Organizational weaknesses that contribute to data leaks:
.jpeg)
Data loss can severely affect businesses, including hefty fines and potential criminal penalties. Moreover, it can significantly harm an organization's reputation and lead to its downfall. In fact, according to a survey conducted by Zogby Analytics in 2019, 10% of small businesses ceased operations after experiencing a data exfiltration, while 25% filed for bankruptcy and 37% suffered significant financial losses.
As companies increasingly adopt remote work and rely on cloud-based infrastructure, having a robust DLP (Data Loss Prevention) solution has become essential to their risk reduction strategy. A DLP software offers comprehensive protection for sensitive data by addressing both physical and digital security threats and preventing unauthorized access or information misuse.
Data loss prevention solutions come in multiple categories because sensitive data lives across different tools, devices, and infrastructures. Each category protects a different layer of the organization’s environment; however, most companies now require a combination of DLP types to achieve complete coverage. Understanding these types helps teams choose a solution that aligns with how they work today.
Protects data in collaboration, productivity, and support tools like Slack, Google Drive, Salesforce, Zendesk, and Notion.
SaaS DLP detects and remediates sensitive data inside messages, files, tickets, and shared content.
Strac delivers agentless SaaS DLP with real-time redaction, masking, and blocking across 40+ applications.

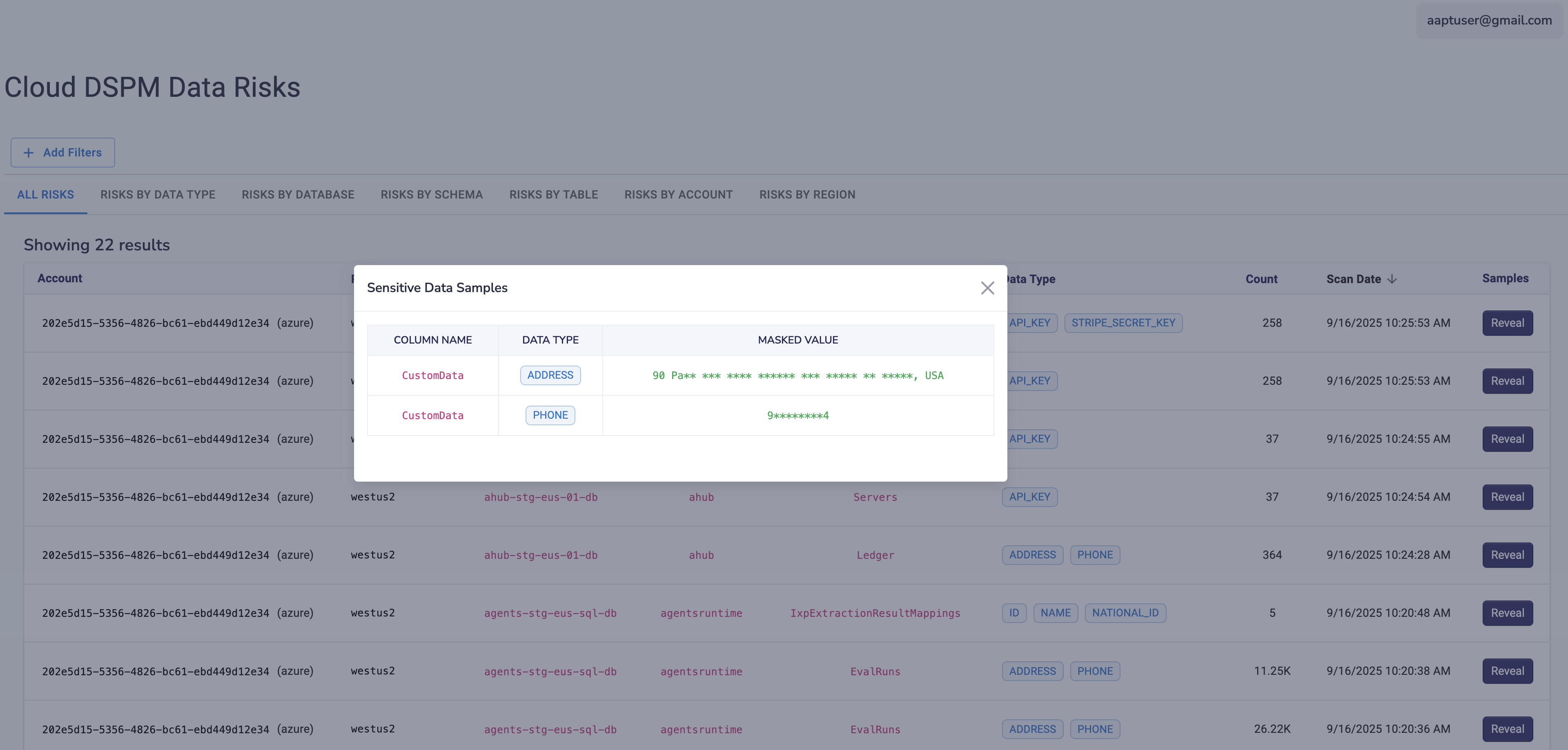
Monitors data stored in cloud platforms such as AWS, Azure, GCP, Snowflake, or S3.
Cloud DLP ensures sensitive data is discovered, labeled, and governed, especially in large data repositories.
Strac provides DSPM-grade visibility across cloud storage, misconfigurations, and high-risk exposures.
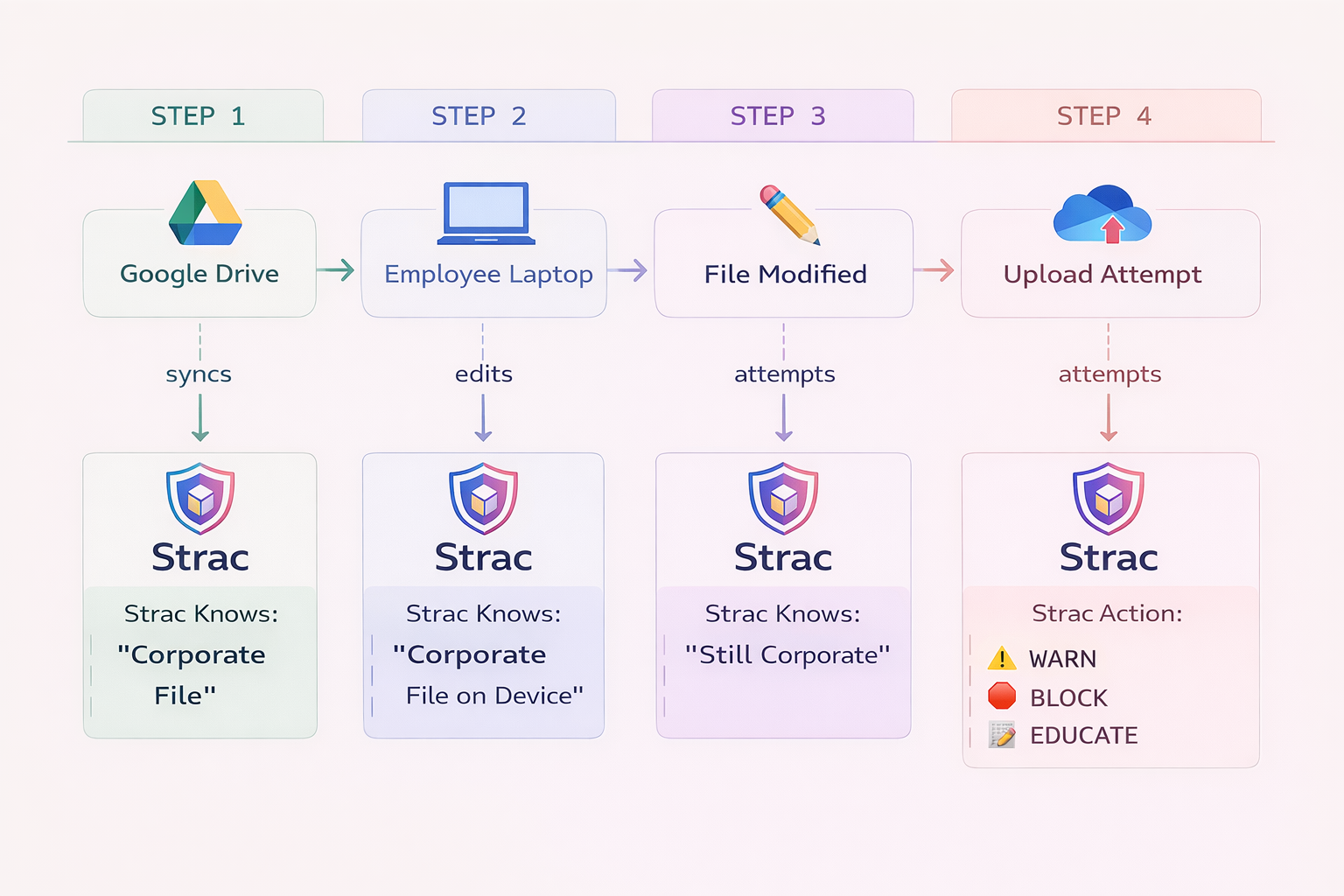
Runs on employee devices like laptops and desktops to prevent data exfiltration through USBs, downloads, screenshots, or local files.
Endpoint DLP helps block unauthorized transfers or suspicious behavior originating from user machines.
Strac extends protection to Windows, macOS, and Linux devices with lightweight endpoint coverage.
Monitors data moving across the organization’s internal network or outbound traffic to external destinations.
Network DLP is more effective for legacy on-premise environments or organizations with strict perimeter controls.
While powerful for certain use cases, modern teams often rely more on SaaS and Cloud DLP due to distributed work.
A newer category focused on AI tools and LLMs like ChatGPT, Google Gemini, and Microsoft Copilot.
GenAI DLP prevents employees or systems from accidentally sending sensitive data into AI prompts or receiving sensitive data in AI responses.
Strac leads this category with real-time redaction, policy enforcement, and discovery inside AI workflows.
Together, these data loss prevention types create a complete framework for protecting sensitive information wherever it moves. Strac unifies all of them into a single, low-friction platform that delivers continuous protection and immediate remediation.
DLP use cases have expanded as sensitive data moves across SaaS apps, cloud platforms, endpoints, and AI tools. Security teams now need to protect data where people actually work; in chats, tickets, files, prompts, and devices. The most common DLP use cases focus on stopping accidental exposure, insider risk, and compliance failures before they turn into incidents.
Common DLP use cases include:
A comprehensive DLP strategy requires a multi-layered approach combining technology, policies, and human factors.
Implement robust technical measures including:
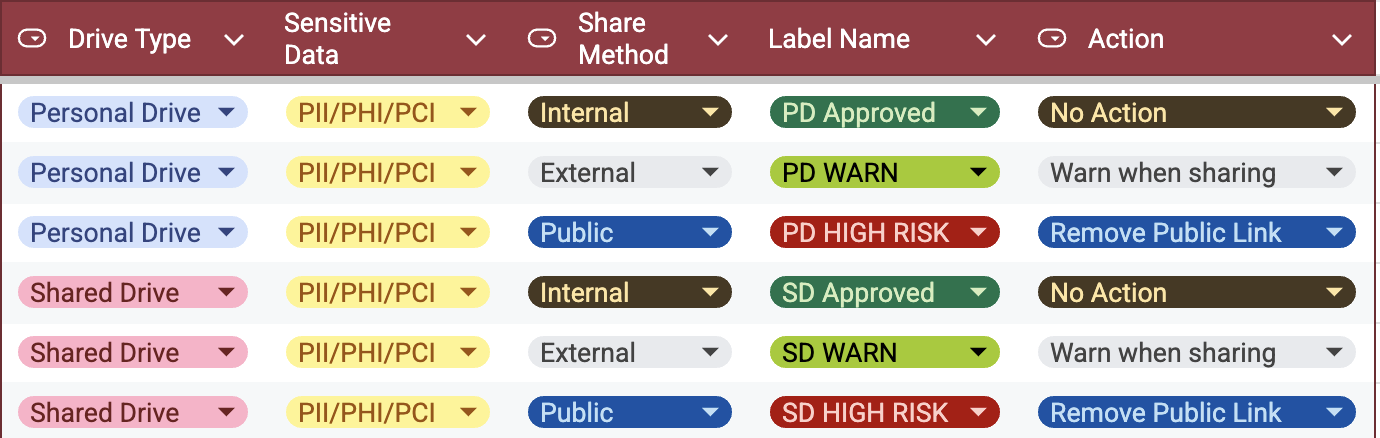
Develop and maintain clear policies addressing:
Create a security-aware culture through:
Establish continuous oversight through:
These strategies should be regularly reviewed & updated to address emerging threats and changing business needs. Organizations must ensure their DLP policies align with regulatory requirements while maintaining operational efficiency.
Data loss prevention best practices help organizations reduce exposure, improve compliance, and make DLP programs actually work in production. A good DLP program is not just about detection; it is about visibility, policy enforcement, and fast remediation across every place sensitive data lives. The strongest data loss prevention best practices are the ones teams can apply consistently without slowing the business down.
Key data loss prevention best practices include:
Following these data loss prevention best practices helps security teams protect sensitive data in real time and reduce risk across the full data environment.
Data loss prevention software is a security tool designed to monitor, detect, and prevent unauthorized access and transmission of sensitive data. It works by classifying and protecting critical information, thereby ensuring that data does not exit the network without proper authorization.
DLP software is essential for businesses to ensure the security of sensitive information and compliance with regulatory requirements. It helps protect a company's most valuable data from internal and external threats. Here are a few requirements that justify DLP:
Regulations mandate that industries such as healthcare, finance, and government contracting secure sensitive personal data effectively. Organizations must comply with regulations like:
DLP ensures compliance with these regulations regardless of whether data is stored on local endpoints or managed through SaaS platforms.
DLP software protects internal business secrets and intellectual property, such as project plans and proprietary code. It helps prevent data breaches coming from insider actions and intentional external attacks.
Implementing DLP is critical in environments with a risk of data exfiltration or accidental leaks. It provides tools to monitor and control data flows so that sensitive information only leaves the network under proper supervision.
Below are the benefits of implementing a DLP security solution:
Investing in DLP adoption is wise for companies looking to reduce the risk of data loss. Organizations gain complete visibility into the information being accessed, providing them with an added layer of protection. Thanks to DLP solutions, businesses can effectively protect themselves from ransomware attacks, prevent data theft, unauthorized sharing of documents, and combat phishing attempts.
Your company can readily detect breaches and protect sensitive data if it has a complete picture of the data movement throughout the cycle. You can establish a compliant data policy that guarantees the safety of critical information using DLP'S data categorization.
DLP systems can identify and prevent unauthorized activity on your network thanks to their sophisticated scanning abilities. DLP guarantees that sensitive information stays protected inside the bounds of your network, whether it is sent by email, copied to external devices, or any other means.
Automatic classification is a process that collects important details about a document, such as its creation date, storage location, and sharing methods. This information is used to enhance the accuracy and effectiveness of data classification within your organization. A DLP solution utilizes this information to effectively implement your DLP policy, thereby reducing the risk of unauthorized sharing of sensitive data.
Complying with data protection regulations such as HIPAA, the Sarbanes-Oxley Act (SOX), and the Federal Information Security Management Act (FISMA) is critical. Adopting a DLP solution gives you access to extensive reporting features that simplify compliance audits, reducing noncompliance risks and penalties.
DLP solutions are designed to monitor data access and usage to mitigate threats effectively. It ensures that only those with permission can access sensitive information and keeps track of their activities.
DLP mitigates the risks associated with insider breaches and fraudulent activities by effectively managing the digital identities of employees, vendors, and partners within the network. Role-based access control (RBAC) is one approach that guarantees only authorized users have access to sensitive information.
DLP solutions provide unparalleled visibility into your organization's critical data while identifying fraudulent activity. As organizations transition to cloud computing, maintaining visibility over sensitive information becomes challenging, demanding a cloud DLP solution.
Strac, a cloud DLP solution, automatically detects and redacts (masks) sensitive data (images, text, audio, video) from all Cloud and SaaS apps (email, slack, zendesk, intercom, AWS services, Google Drive, One Drive, ChatGPT, and more).
You get to choose the degree of confidentiality for each record and can also set up automatic responses for security incidents. You can further configure in-depth data and content analysis evaluating both present and future risks bolstering cybersecurity and DLP initiatives.
When it comes to protecting data within an organization, DLP security solutions shine due to their ability to classify and constantly monitor critical data. They dramatically boost your data security by identifying and blocking suspicious and illegal activity.

Various DLP strategies are employed to protect data at different stages and locations within an organization:
Given the complexity of the threat environment and the magnitude of business networks, implementing a Data Loss Prevention (DLP) strategy is no easy feat.
Below best practices can help you maximize your investment in DLP tools .
Prioritize the data you need to protect. Understand the different categories of data in your organization like PII (Personally identifiable information), PHI(Protected Health Information), PCI( Payment Card Industry )data and classify them based on their sensitivity levels. An accurate data inventory is the foundation for effective data loss prevention.
Develop clear DLP policies and procedures based on the type of data you have, its sensitivity, and applicable compliance regulations. This includes identifying who has access to what data, under what circumstances data can be transferred or shared, and what to do in case of a potential breach.
Restrict access to sensitive data and implement the principle of least privilege, granting employees access to only the information necessary for their role. This reduces the risk of data exposure from the inside.
Always encrypt sensitive data both in transit and at rest. In the event of a breach, encryption can render the data useless to unauthorized individuals.
Use your DLP solution to continuously monitor and log all data movements within your network. Regular audits of these logs can help identify potential threats before they cause damage.
Conduct regular DLP training and make sure all employees understand the importance of data security. Often, data breaches are the result of ignorance rather than malicious intent.
Regular testing and updating of your DLP system can help you keep up with evolving security threats. It also helps to ensure that your DLP system remains compatible with other systems in your IT infrastructure.
Have a well-defined incident response plan in place. In the event of a data breach, your team should know exactly what steps to take. This includes how to isolate affected systems, how to investigate the breach, how to communicate the breach to stakeholders and authorities, and how to prevent similar breaches in the future.
To help you choose among many DLP vendors for your organization, answer these questions first
DLP helps Software-as-a-Service (SaaS) platforms improve security by automatically identifying and protecting sensitive data. Key benefits include:
Endpoint DLP focuses on protecting data at the device level, including laptops, desktops, and mobile devices. Essential features include content inspection and contextual analysis to identify and control sensitive data effectively. Encryption, device control, and user behavior monitoring are critical to prevent data leaks through various transfer methods, such as USB drives.
DLP for Generative AI addresses the challenges posed by AI platforms, especially around data training and output. Its key functionalities include monitoring and controlling the input data used for training AI models and the output generated by these models. It ensures the integrity and confidentiality of training datasets and real-time monitoring of AI activities to prevent data theft.
Strac is a unified DLP + DSPM platform built for how data actually moves today; across SaaS apps, cloud storage, AI tools, browsers, and employee endpoints. Instead of stitching together multiple tools, Strac gives security teams one system to discover, classify, and remediate sensitive data in real time across the entire data surface.
Unlike traditional DLP tools that only monitor or alert, Strac is built for real-world execution; detection + immediate action.
Strac covers SaaS, Cloud, GenAI/Browser, and Endpoints in one platform:
Sensitive data is protected where it actually lives and moves; not just inside one system.
Strac GenAI DLP
Strac protects AI workflows in real time:
Built for how employees actually use AI today.

Strac covers both past and present risk:
Closes exposure, not just alerts on it.
Strac Slack DLP
Strac takes action the moment data is detected:
Response time drops from days to seconds.

Powered by contextual ML + OCR (not regex):
Usable in production, not just dashboards.
Strac provides full visibility into how sensitive data moves across endpoints, browsers, SaaS, and AI tools.
This gives security teams context, not just detection; understanding how data is used, not just where it exists.
Strac unifies multiple layers into one system:
Supports:
With full policy, data, and remediation customization.
Strac's DLP solutions are designed to provide comprehensive data protection across SaaS applications, endpoint devices, and generative AI platforms. By leveraging advanced AI and ML technologies, Strac offers:

This ensures that your organization remains compliant while keeping sensitive data secure. Strac's audit reports give 100% visibility and control over data, providing detailed insights into your data usage, allowing you to monitor and manage it effectively.
Read more on Data Loss Prevention in Cloud and SaaS
Data loss prevention is no longer optional; it is essential for any organization that stores, shares, or builds products with sensitive data. As information spreads across SaaS tools, cloud platforms, endpoints, and GenAI systems, companies need modern data loss prevention that provides visibility, real-time protection, and consistent enforcement. Strac delivers this with agentless deployment, ML and OCR-driven classification, and instant remediation across every critical data surface; helping security teams reduce risk, maintain compliance, and operate with confidence.
A Data Loss Prevention solution monitors, detects, and stops sensitive data from being exposed, misused, or leaving the organization without authorization. Because modern companies use dozens of SaaS apps and cloud systems, data constantly moves; DLP ensures visibility and control at every stage of that movement. A strong DLP also reduces compliance risk by preventing PII, PHI, PCI, secrets, and financial information from leaking into places they should not be.
A DLP solution typically performs three core functions; discover, classify, and protect. It inspects text, attachments, and files; applies sensitivity labels; and enforces real-time policies like blocking, redaction, masking, alerting, or quarantine. With Strac, these protections happen instantly across SaaS, Cloud, GenAI, and Endpoints, giving organizations continuous risk reduction.
The DLP process is a structured workflow that ensures data is identified, labeled, monitored, and protected everywhere it moves. Because companies handle thousands of files, messages, emails, and SaaS interactions daily, this process must be automated and continuous. Modern DLP relies on content-aware detection rather than static rules to keep up with real-world complexity.
The DLP process includes:
• Discovery; scanning data across SaaS apps, cloud storage, endpoints, and AI systems
• Classification; labeling sensitive data using ML, OCR, and policy templates
• Monitoring; tracking where data goes, who accesses it, and how it is used
• Protection; applying real-time remediation actions like redaction, masking, blocking, or quarantine
A complete DLP process ensures that sensitive data is always visible, properly labeled, and automatically protected at scale.
Organizations categorize DLP into three main types because each focuses on a different layer of technology and user behavior. Sensitive data does not live in one place, so effective protection requires coverage across storage, movement, and usage. These three types form the foundation of any complete DLP strategy.
The three core types of DLP are:
• Storage DLP; protects data at rest in databases, cloud storage, local devices, and repositories
• Network DLP; monitors data in motion across internal networks and outbound traffic
• Endpoint DLP; protects data in use on employee devices like laptops, desktops, and local apps
Strac expands this model with SaaS DLP, Cloud DLP, and GenAI DLP, giving companies full coverage across all modern data surfaces.
The best way to prevent data loss is to combine continuous discovery, intelligent classification, and real-time remediation across every platform where data lives. Because threats often come from accidental sharing, misconfiguration, or human error, prevention must be proactive and automated; not reactive. A modern DLP strategy should also integrate with SaaS apps, cloud storage, endpoints, and AI tools to eliminate blind spots.
Highly effective data loss prevention includes:
• Automated scanning across SaaS, Cloud, GenAI, and Endpoints
• ML and OCR-based classification that avoids false positives
• Real-time actions like redaction, masking, blocking, or quarantine
• Continuous monitoring for risky access, sharing, or downloads
• Unified visibility that ties every policy to consistent enforcement
Strac delivers all of these capabilities in one agentless platform; enabling organizations to prevent data loss without slowing down productivity.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

