OneDrive DLP & DSPM (Data Loss Prevention)
OneDrive quietly becomes the default dumping ground for sensitive files inside Microsoft 365:
- HR exports
- customer contracts
- invoices and payouts
- IDs for KYC
- PHI/benefits documents
- board decks
- screenshots and PDFs
And the risk isn’t just “someone uploads something sensitive.”
It’s the stuff that’s already there — shared months ago, inherited permissions, copied across folders, synced to laptops, and later exposed through one “Anyone with the link” mistake.
Uncomfortable truth: You can’t stop OneDrive data leaks if you don’t know what’s in OneDrive and who can access it.
TL;DR — OneDrive DLP
- OneDrive DLP stops sensitive data leaks by detecting risky sharing + exfiltration in real time.
- OneDrive DSPM (Data Discovery) scans your existing OneDrive content to find where sensitive data already lives.
- OneDrive DLP + OneDrive DSPM together tell you: what data exists, where it lives, who has access, and what’s publicly/external exposed — plus remediation.
✨ OneDrive DLP: Discover and Classify Sensitive Data in OneDrive

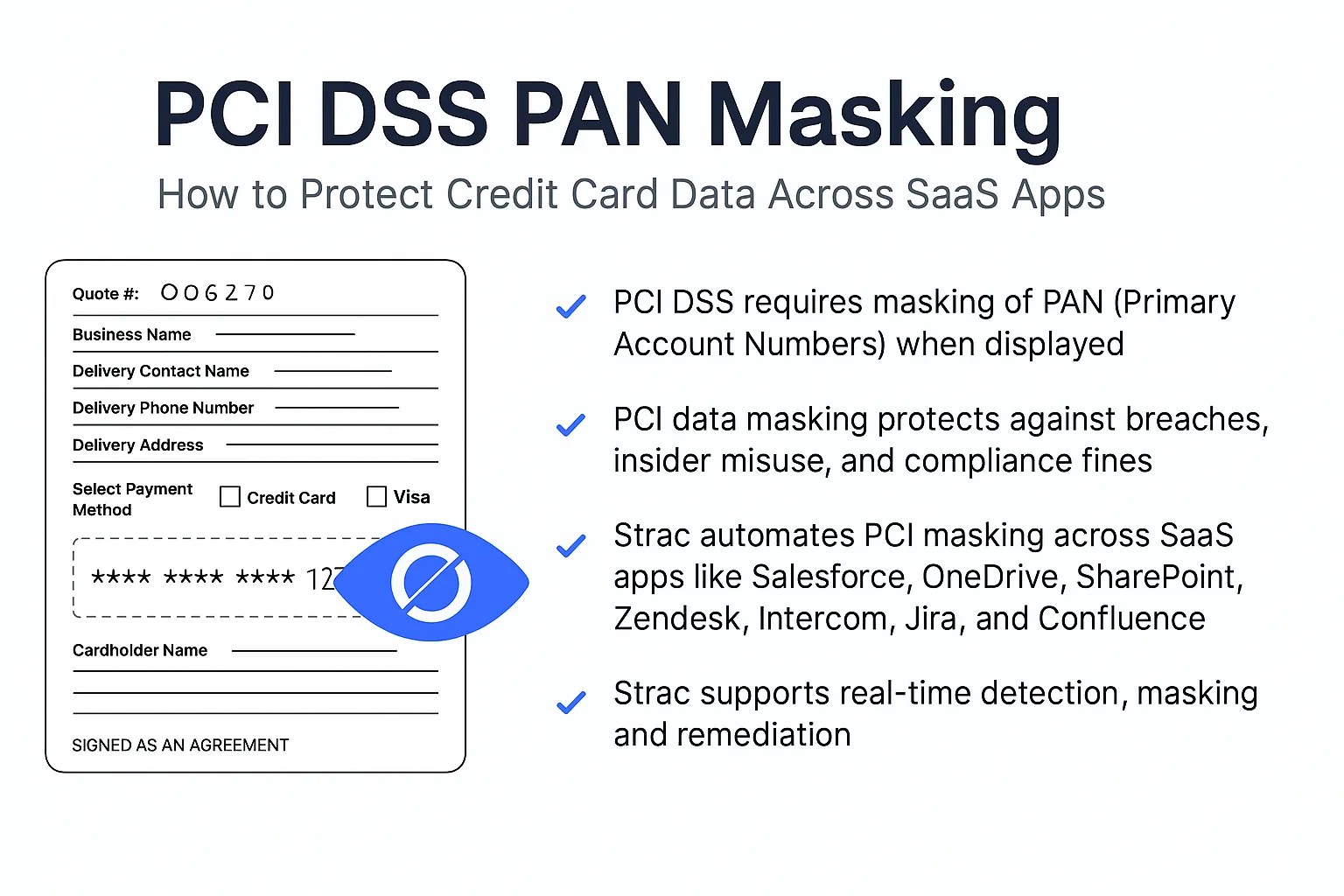
OneDrive DLP starts with one core capability: accurate sensitive data discovery + classification across files already stored in OneDrive.
Strac scans and classifies common regulated + high-risk data, including:
- PII (SSNs, driver’s licenses, addresses, DOB)
- PHI (patient IDs, medical docs, claims)
- PCI (card numbers, statements)
- Financial (bank accounts, payouts, invoices)
- IP (roadmaps, source code snippets, internal docs)
Output: a searchable inventory of sensitive files + metadata for security and compliance teams: file, owner, location, label, exposure risk.
OneDrive DLP: Why OneDrive Becomes a “Silent Leak” Channel
OneDrive exposure usually happens in boring ways:
- External sharing slowly expands (vendors, contractors, agencies, auditors)
- Links get forwarded into email/Teams/tickets
- Permission inheritance quietly overexposes folders
- Old folders never get cleaned up
- People sync locally and re-upload versions elsewhere
If you’re only relying on “user training” or manual reviews, you’ll miss most of it.
✨ OneDrive DLP: Find Public Links and External Sharing Exposure

OneDrive DLP should answer, instantly:
- Which sensitive files are shared externally?
- Which files have “anyone with link” style exposure?
- Which folders are accessible by broad groups that shouldn’t exist?
- Which sensitive files are owned by ex-employees (orphaned ownership risk)?
Strac continuously maps sensitive data + access so you can prioritize what actually matters.
✨ OneDrive DLP: Remediate Risky Sharing Automatically (Not With Tickets)

Most teams fail OneDrive governance because remediation becomes a ticket queue:
- “Hey, can you remove this external share?”
- “Can you lock this folder down?”
- “Can you revoke this link?”
Strac turns OneDrive DLP findings into bulk remediation actions, for example:
- Remove “public/anyone link” access
- Remove external users from sensitive folders
- Restrict sharing on specific sensitivity labels
- Enforce least-privilege access patterns
This is how you shrink exposure fast — without burning your IT team.
OneDrive DLP: Real-Time Alerts When Sensitive Data is Shared
OneDrive DLP isn’t just “scan and report.”
Strac can alert when sensitive files are:
- shared externally
- moved into risky folders
- accessed unusually (spikes, rare users, suspicious patterns)
- repeatedly reshared / link churn
Alerts can go to Slack/Teams/email/SIEM so security teams respond in minutes, not quarters.
OneDrive DLP: Policies Security Teams Actually Use
Instead of generic “DLP rules,” OneDrive DLP policies should map to real risk:
- Sensitive file shared externally → alert + auto-remediate
- Sensitive folder broadly accessible → restrict + notify owner
- Public link created → revoke link + label file
- Old sensitive file with external access → remove external users in bulk
- Pre-AI rollout readiness (Copilot/Gemini-style risk) → reduce exposed sensitive corpus first
OneDrive DLP: Compliance Evidence Without Spreadsheet Theater
Auditors don’t want vibes — they want evidence.
Strac OneDrive DLP helps produce:
- inventory of sensitive data locations
- “who has access” records
- remediation logs (what changed, when, by who)
- reports aligned to SOC 2 / HIPAA / PCI expectations
OneDrive DLP: Practical Scenario (Healthcare)
A healthcare ops team stores patient intake PDFs in OneDrive. A folder gets shared with a vendor for a short-term project — but access is never revoked. Months later, the vendor account is compromised.
With OneDrive DLP, Strac would detect PHI in that folder, flag external access, and allow bulk remediation (remove external users / restrict links).
OneDrive DLP: Practical Scenario (Finance / PCI)
A finance team keeps statements and chargeback documents in OneDrive. A new analyst shares a folder link externally to a processor “just to move fast.”
With OneDrive DLP, Strac detects PCI-like content and triggers alerting + automated remediation.
OneDrive DLP FAQs: Is Microsoft Purview enough for OneDrive DLP?
Purview helps, but most teams still struggle with:
- visibility into existing sensitive files already spread across OneDrive
- mapping who has access across nested folders and inheritance
- fast, consistent remediation at scale (without manual work)
That’s why Strac pairs OneDrive DLP with OneDrive DSPM (Data Discovery).
OneDrive DLP FAQs: What’s the difference between OneDrive DLP and OneDrive DSPM?
- OneDrive DLP = real-time controls (stop/alert on risky sharing and movement).
- OneDrive DSPM = historical scanning + posture (what exists today, who has access, where exposure lives).
You need both — because most risk comes from what’s already sitting in OneDrive.
OneDrive DLP FAQs: Can OneDrive DLP automatically revoke public links or external access?
Yes — Strac supports bulk and automated remediation, including removing public access and external collaborators based on policy and sensitivity.
OneDrive DLP FAQs: How fast can we deploy OneDrive DLP?
Most teams connect Strac quickly because it’s API-based and doesn’t require endpoint agents just to get OneDrive visibility (agents are optional for endpoint controls depending on your rollout).
Get Started with OneDrive DLP
If you want OneDrive to stay collaborative without becoming a leak channel, you need:
- OneDrive DSPM (Data Discovery) to see what exists + who has access
- OneDrive DLP to prevent new leaks and remediate exposure continuously
Book a demo to see OneDrive DLP running end-to-end: discovery → exposure → remediation → alerting.











.webp)














.webp)








.avif)


