CrowdStrike DLP Review (2026): Limitations & Alternatives
Explore CrowdStrike DLP capabilities, limitations, and why modern DLP solutions go beyond endpoints with SaaS, AI, and real-time data protection.
CrowdStrike DLP is an extension of the CrowdStrike Falcon platform focused on monitoring and controlling sensitive data at the endpoint level. It is built on top of strong endpoint detection and response (EDR) capabilities, which makes it effective for device-centric security.
In practice, CrowdStrike DLP is used to:
This makes it a solid solution for organizations that prioritize endpoint visibility and control. However, the architecture reflects an older assumption: that data primarily lives on devices.
CrowdStrike DLP limitations become more visible when you look at how data actually flows in modern organizations. Data no longer stays on endpoints; it moves across SaaS tools, APIs, cloud storage, and AI platforms in real time.
CrowdStrike DLP does not natively provide deep coverage across tools like Slack, Google Drive, Salesforce, Jira, or Zendesk. Sensitive data often lives in conversations, tickets, attachments, and shared links; areas that endpoint-based DLP cannot fully control.
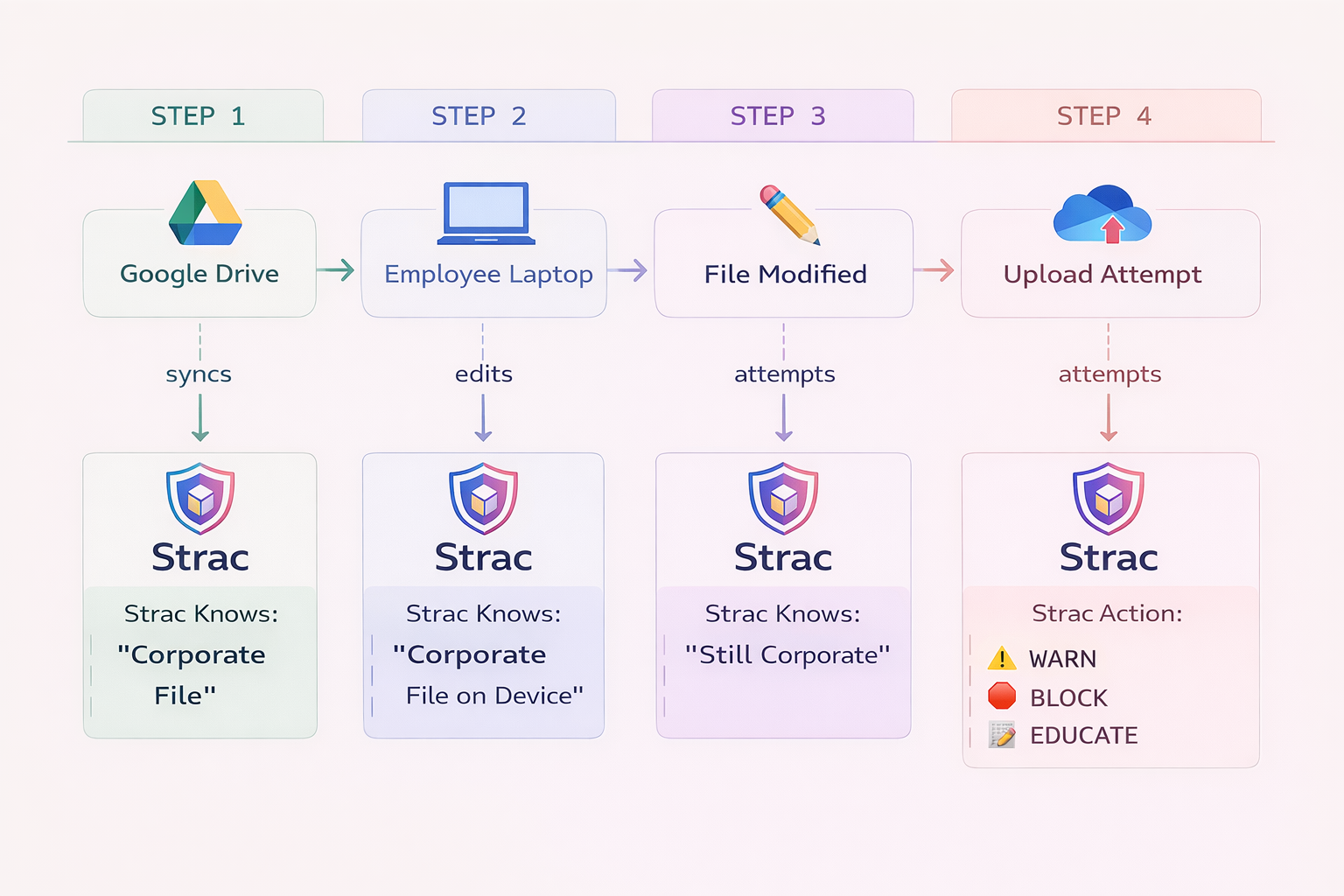
Modern security teams need to understand how data moves; not just where it exists. CrowdStrike DLP lacks persistent tracking of files across rename, copy, edit, and movement between systems, which makes investigations harder and incomplete.
CrowdStrike DLP was not built for AI workflows. It does not monitor or control:
This is now one of the fastest-growing data leakage vectors.
CrowdStrike DLP primarily focuses on detection and alerting. While blocking is possible, it lacks inline remediation capabilities like automatic redaction or masking in real time.
Detection without action increases operational overhead and delays response.
Because it is endpoint-centric, CrowdStrike DLP does not provide a unified view across:
This creates blind spots in environments where data is highly distributed.
CrowdStrike DLP is best understood as part of an older generation of data protection tools. Modern DLP has evolved to match how data moves across systems, users, and workflows.
A modern DLP approach includes:
Instead of focusing only on endpoints, modern DLP protects data itself; wherever it lives and however it moves.
One of the platforms emerging in this new category is Strac, which approaches data security differently from traditional endpoint-based tools.
Strac is built as a unified DSPM + DLP platform that:
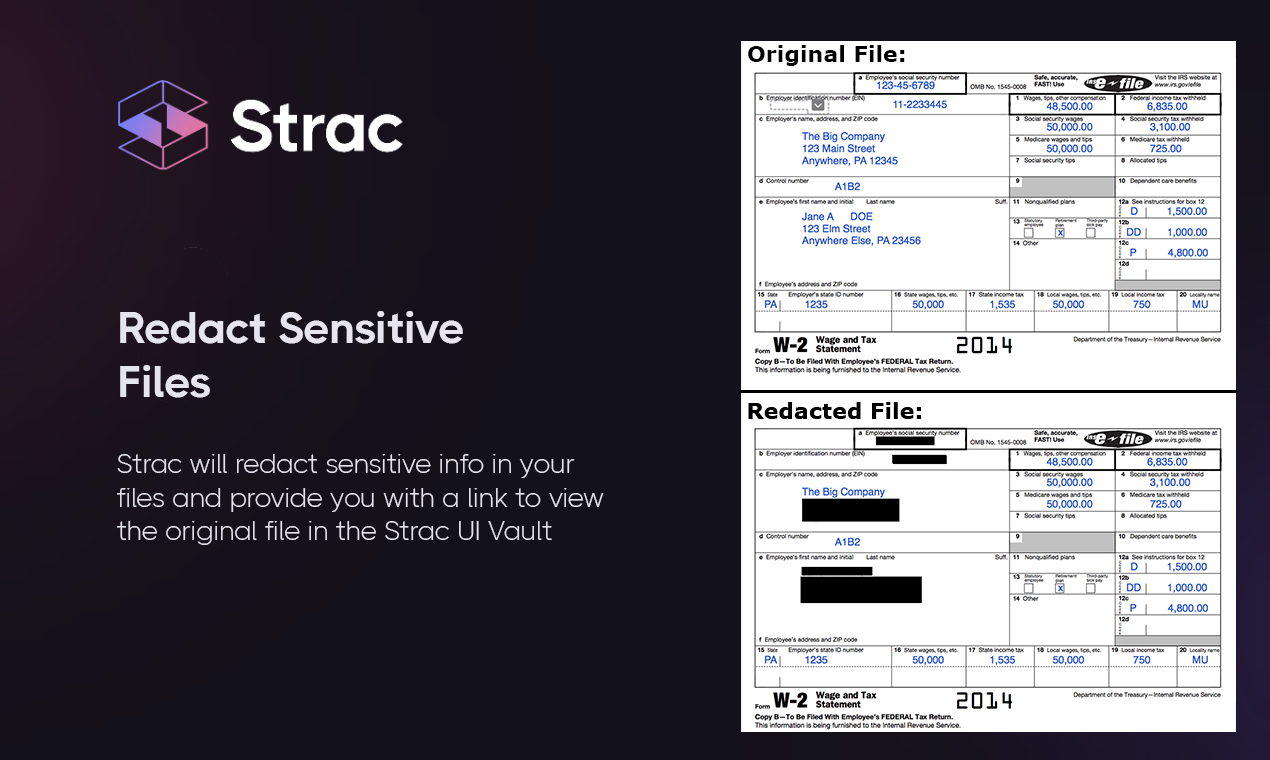

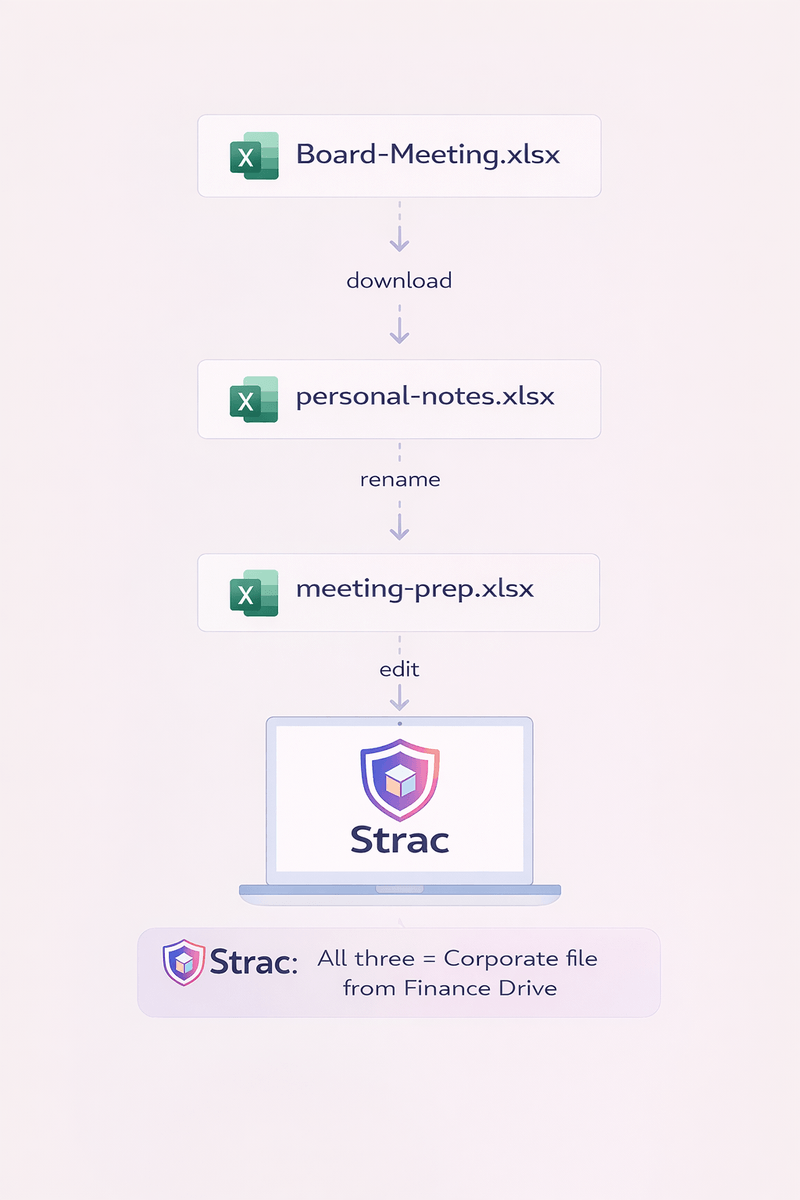
Unlike legacy tools, Strac focuses on inline protection and full data lifecycle coverage, rather than just monitoring endpoints. This includes protecting data inside conversations, tickets, attachments, and AI interactions.
These capabilities reflect a broader shift in the market toward real-time, context-aware data protection rather than static policy enforcement .
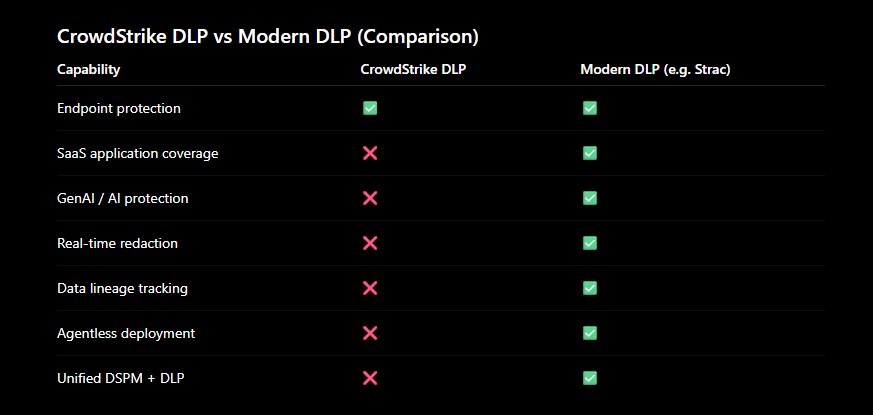
This comparison highlights the shift from device-centric security to data-centric security.
CrowdStrike DLP still has a place in certain environments, particularly where endpoint control is the primary concern. However, most organizations today operate across far more complex data environments.
CrowdStrike DLP is not a weak solution; it is simply incomplete for how data moves today. As organizations adopt SaaS, cloud, and AI tools, data protection needs to evolve beyond endpoints.
Modern DLP is no longer about watching files on devices. It is about protecting data across its entire lifecycle; in motion, at rest, and inside real-time workflows.

CrowdStrike DLP provides strong endpoint-level controls, but it is not a full DLP solution for modern environments. It lacks deep SaaS, cloud, and AI coverage, which are critical for complete data protection today.
CrowdStrike DLP has limited native visibility into SaaS applications. Most sensitive data in modern organizations exists in SaaS tools, which requires dedicated SaaS-native DLP solutions.
No, CrowdStrike DLP is not designed to monitor or control data flowing into AI tools like ChatGPT, Copilot, or Gemini. This is a major gap in modern data protection strategies.
The biggest limitation is its endpoint-centric architecture. It does not provide unified visibility or control across SaaS, cloud, and AI environments where most data now resides.
Look for solutions that offer real-time remediation, SaaS and AI coverage, data lineage tracking, and unified DSPM + DLP capabilities. These features reflect how modern data protection works in 2026.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

