What is CASB Security? Guide on Cloud Access Security Brokers in 2026
Discover what a Cloud Access Security Broker (CASB) is, its key features, and how it enhances cloud security, compliance, and data loss prevention.
Back in 2006, Amazon launched Amazon Web Service - a service that allowed Amazon to rent computing resources to clients globally. 20 years later, Amazon enjoys more than 1 million active customers across 190 countries - a massive feat hard to replicate.
However, in reality, not everything’s good in paradise. The company faces cyber threats every odd second, and despite implementing strong security protocols, a cyber-security firm identified over 6.5 terabytes of exposed information in May of 2022.
This raises eyebrows and makes us think, is our data really secure? More significantly, how safe are our businesses’ valuable digital assets?
The answers lie in Cloud Access Security Broker (CASB).
A Cloud Access Security Broker (CASB) is a security policy enforcement point positioned between cloud service consumers and providers. It enforces enterprise security policies and provides visibility, compliance, data security, and threat protection when accessing cloud services.
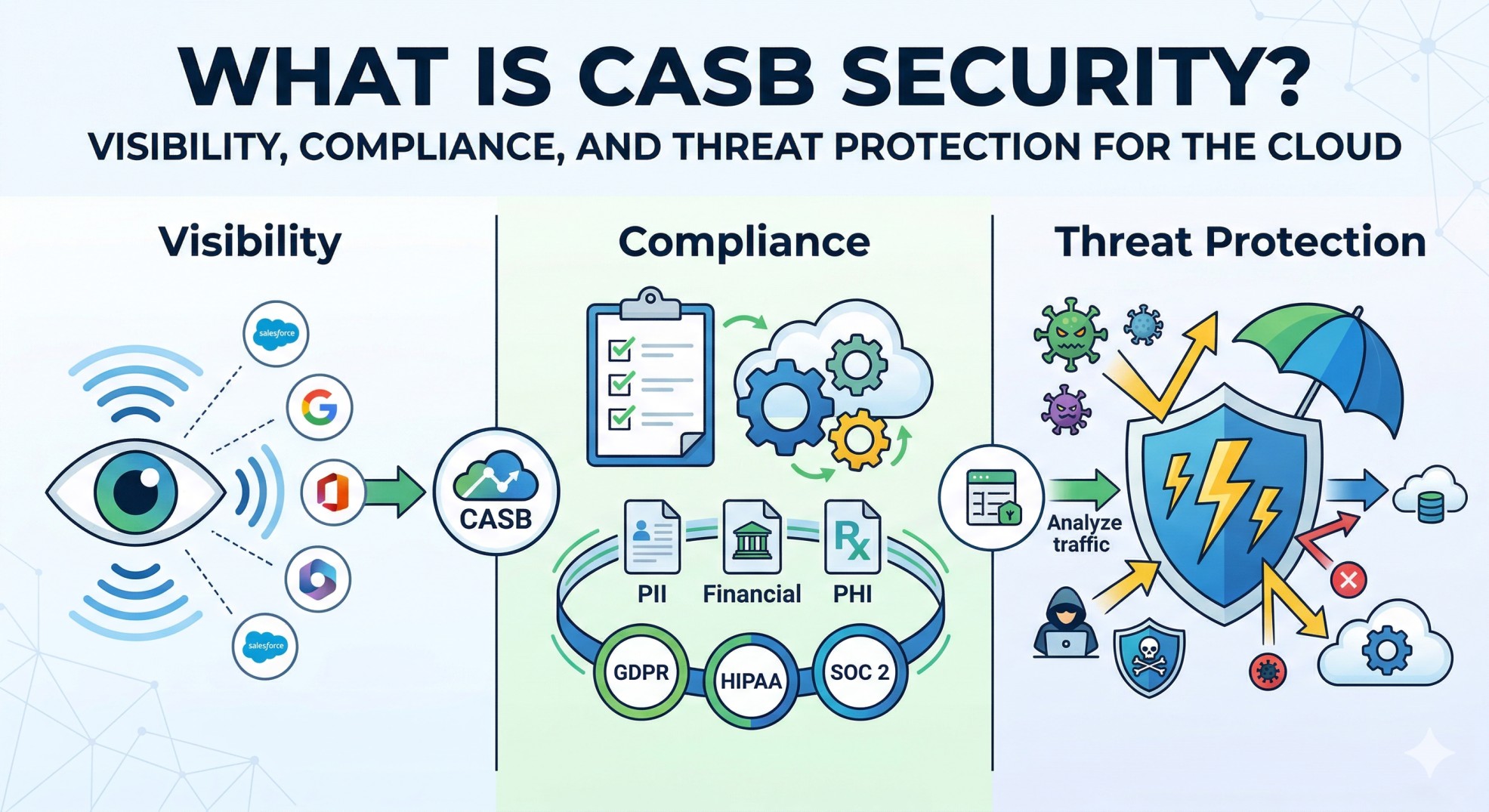
In simpler terms, a CASB serves as an intermediary between users and cloud services. It not only monitors all activity but also enforces your organization's security policies. Think of CASB as a gatekeeper, allowing safe and compliant cloud access while denying any potentially risky activities or transactions.
CASBs are crucial in the current era of increasing cloud adoption and growing cybersecurity threats. They address the unique security challenges that arise from the use of cloud services, including the risk of data leakage, unauthorized access, and non-compliance with regulations.
The below pillars represent the core components necessary for any CASB solution:
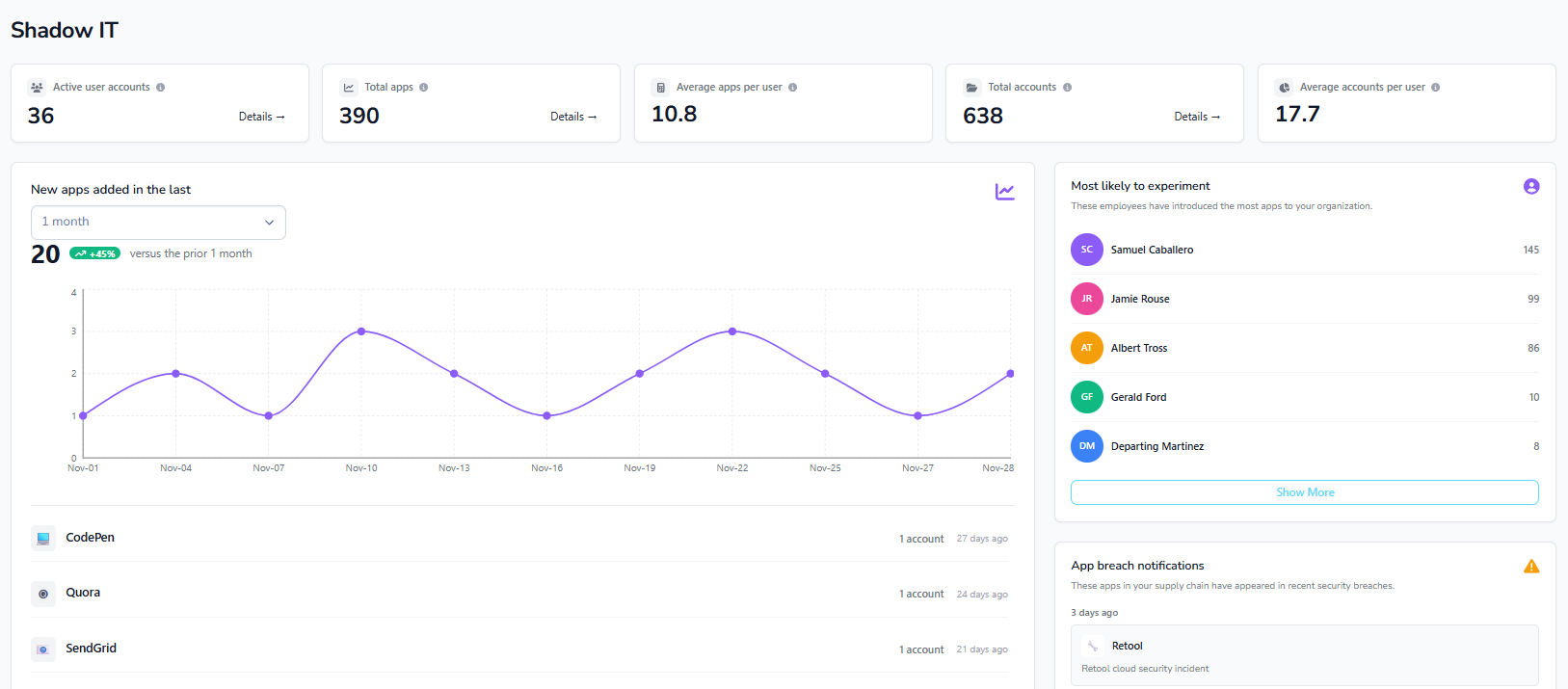
CASBs provide visibility and control over both managed and unmanaged cloud services. They help identify "shadow IT," which includes undocumented systems and cloud services that may pose security risks. CASBs enable IT to monitor and govern access to activities and data within cloud services while allowing useful ones. This includes discovering all cloud services in use, reporting on cloud expenditure, and identifying redundant functions and costs.
CASBs ensure adherence to industry-specific compliance standards such as SOC 2, HIPAA, and GDPR. They help organizations meet regulatory requirements by implementing robust security controls crucial for healthcare, retail, and financial services. CASBs maintain compliance with these regulations, protecting against data breaches and avoiding penalties and fines.
CASBs prevent confidential data from leaving company-controlled systems and ensure data integrity. This is particularly important with the rise of AI tools, where employees might upload sensitive data. Technologies like access control and data loss prevention (DLP) are essential for securing sensitive data and preventing unauthorized transfers.
CASBs provide real-time scanning and remediation of threats across internal and external networks. They block external threats and attacks, stop data leaks, and prevent unauthorized access. Key technologies include anti-malware detection, sandboxing, packet inspection, URL filtering, and browser isolation, all of which help block cyber attacks and ensure comprehensive threat protection.
A CASB helps manage various aspects of cloud security such as identifying unauthorized cloud services (also known as Shadow IT), flagging potential risks associated with various cloud applications, and tracking user behavior to detect anomalies. For instance, if an employee starts downloading excessive amounts of data from a cloud service, the CASB could detect this unusual behavior and alert the administrators.
CASB aids in identifying unsanctioned cloud applications used by employees (Shadow IT), allowing IT administrators to assess associated risks and manage cloud application usage appropriately.
One of the fundamental roles of a CASB is allowing administrators to enforce granular security policies across different cloud applications. This capability ensures that your organization's use of cloud services aligns with your internal security policies and regulatory requirements. For example, you can set policies to restrict access to sensitive data based on user roles, locations, or devices.
Cybersecurity threats are escalating, with more than 236.1 million attacks hitting servers globally each year. A CASB protects sensitive data from these threats in the organization's cloud environment, thereby helping to mitigate risks associated with data breaches and cyber-attacks. This protection includes features like encryption, tokenization, and data loss prevention (DLP).
By providing visibility into cloud application usage, enforcing security policies, and protecting sensitive data, a CASB plays an invaluable role in an organization's overall cybersecurity framework.
.webp)
A Cloud Access Security Broker (CASB) is integral to any cloud security strategy due to its extensive capabilities. It facilitates visibility, data protection, threat detection, and policy enforcement, enabling organizations to confidently embrace cloud services while maintaining control over their data and ensuring compliance with industry standards. Let's delve into some of these capabilities in detail:
A CASB grants organizations real-time visibility into cloud applications. It helps distinguish between sanctioned and unsanctioned (Shadow IT) cloud applications, giving IT administrators insights into cloud service usage and potential security risks.
CASB integrates with identity providers to enforce robust authentication methods, such as Multi-Factor Authentication (MFA) and Single Sign-On (SSO). This safeguard ensures that only authorized users can access cloud applications and data.
CASB deploys sophisticated threat detection mechanisms to identify and neutralize various cloud-based threats, including malware, ransomware, phishing attempts, and other suspicious user activities. It alerts in real-time and responds to potential security breaches. For instance, if a user logs into Salesforce from Russia five minutes after logging into Office 365 from California, the CASB will detect this anomaly through a combination of detailed activity logs and User and Entity Behavior Analytics (UEBA).
CASB incorporates encryption and tokenization capabilities to secure sensitive data at rest and in transit. Encryption ensures that intercepted data remains unreadable to unauthorized individuals. Tokenization replaces sensitive data with non-sensitive tokens, further enhancing data security. For example, Strac as a tokenization provider offers UI components that block the parent page from accessing sensitive data. Strac then tokenizes this data and returns the tokens to the UI app.
CASB supports organizations in meeting regulatory compliance requirements, ensuring that data stored and processed in the cloud aligns with industry-specific regulations such as GDPR, HIPAA, and CCPA. Many CASB solutions offer compliance reporting and auditing features, assisting organizations in adhering to these regulations.

By integrating these key capabilities, a CASB provides a holistic and flexible approach to cloud security, shielding organizations from emerging threats and mitigating risks associated with cloud-based services.
CASBs provide a range of security capabilities designed to protect cloud environments. The key security capabilities offered by CASBs include:
CASB solutions operates through two primary deployment models: API-based and Proxy-based. Here's how you can implement each model,
In the API-based model, the CASB integrates directly with the cloud service providers’ APIs, enabling it to monitor and control data and activities within the cloud applications. This model provides more visibility without rerouting traffic but requires cloud providers to expose their APIs for integration.
Here is how you can implement API-based CASB:
.webp)
The CASB discovers and inventories all cloud applications used across your organization. It differentiates between sanctioned and unsanctioned applications, providing administrators with a comprehensive view of all cloud services in use.
The CASB integrates with the cloud service providers’ APIs. This integration allows it to access metadata, user activity logs, and other relevant information from cloud applications. It also collects data on user actions, file activities, login attempts, and security events within the cloud environment.
The CASB continually monitors user activities and real-time data within the cloud applications. This provides IT administrators with visibility into who is accessing what data, from where, and on what device.
The CASB can enforce on sensitive data within cloud applications. It also enforces encryption, access controls, and other security practices based on predefined rules and compliance requirements.

CASB employs advanced threat detection mechanisms to identify and block cyber threats aimed at cloud applications. It can enforce encryption, access controls, and other security policies based on pre-defined rules and compliance requirements.
API-based CASB generates comprehensive reports on cloud application usage, security events, policy violations, and compliance status. These reports are essential for compliance audits and improving cloud security practices.
In the proxy-based CASB deployment model, CASB acts as an intermediary proxy between users and cloud services. All traffic passes through the CASB, enabling real-time inspection, data protection, and policy enforcement. The Proxy-based approach introduces some latency but provides robust security features. Here is how it works:
All user traffic to and from cloud applications is redirected through the CASB proxy. Users must authenticate with the CASB before accessing cloud resources, ensuring all cloud activities are routed through the security gateway.
CASB inspects all traffic passing through the proxy, scanning for potential threats and policy violations. It enforces security policies like data encryption, access controls, and DLP-based predefined rules.

Proxy-based CASBs employ real-time malware and threat detection mechanisms to identify and block malicious content before it reaches the cloud applications or the end users.
CASB can encrypt data before it leaves the organization’s network, ensuring that sensitive information remains protected throughout its journey to the cloud.
CASB enforces strong authentication mechanisms, such as multi-factor authentication (MFA) and single sign-on (SSO), to ensure that only authorized users can access cloud resources.
The CASB continuously monitors cloud activities, generating logs and reports on user behavior, policy compliance, security incidents, and threat intelligence.
CASB’s ability to provide comprehensive visibility, control, data protection, and threat detection makes it a crucial component of modern cloud security strategies.
Also read: How Strac protects sensitive data with tokenization
Choosing the right CASB can be confusing as most vendors promise one of a few features without differentiation. Here are some key points to identify the right CASB solution provider for your business.
Check out our list of Top 10 CASB Solutions
Legacy Cloud Access Security Brokers (CASBs) face several significant drawbacks that necessitate a new approach to cloud security:
1. Operational Complexity:
Legacy CASBs are often standalone solutions, detached from the core security architecture, leading to complexity in synchronizing data protection and security policies. This disjointed setup complicates management and can lead to inconsistent policy enforcement.
2. Limited Deployment Models:
Traditional CASB cyber security solutions use forward and reverse proxies, which are limited to web-based protocols and require extensive infrastructure like log collectors and PAC agents. These deployment models do not provide comprehensive visibility into all cloud applications, particularly unsanctioned ones, and complicate threat prevention.
3. Static Application Signatures:
Legacy CASBs rely on static application libraries and manual signature updates, which cannot keep up with the rapid growth of SaaS applications. This delays identifying and controlling new cloud apps, leaving security gaps.
4. Inadequate Data Protection Integration:
Legacy CASBs often function as standalone DLP tools, which can create inconsistencies in data protection across cloud and on-premises environments. This approach can reduce the effectiveness of data governance and compliance efforts.
5. Complex Deployment and Management:
Deploying legacy CASBs requires significant resources and infrastructure, such as log collectors and PAC configurations. This increases the total cost of ownership (TCO) and reduces operational efficiency.
A modern CASB approach with Strac addresses these issues and provides more effective and comprehensive security.
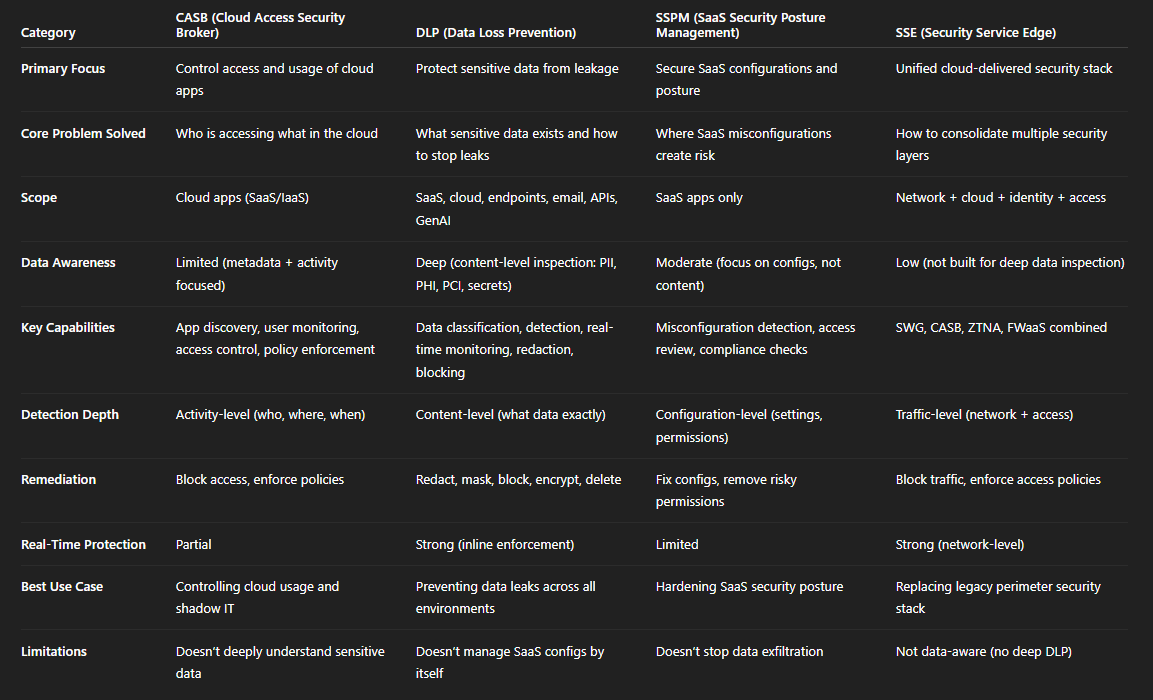
CASBs are cloud-centric and offer tools specifically designed for cloud security challenges, including data protection. DLP solutions provide broader data protection, focusing on preventing data loss across all environments, not just the cloud.
Key Features:
CASB:
DLP:
CASBs focus on securing cloud services and managing access, while SSPMs are dedicated to monitoring and improving the security posture of SaaS applications. SSPMs offer a more detailed view of SaaS security configurations, identifying and addressing potential vulnerabilities. Both tools are essential for comprehensive cloud security, with CASBs providing broad control over cloud usage and SSPMs ensuring detailed configuration security for SaaS applications.
Key Features
CASB:
SSPM:
CASBs specialize in securing cloud services and applications, providing visibility, data security, threat protection, and compliance. SSE offers a broader, integrated security solution that includes CASB functionalities, SWG, ZTNA, and FWaaS, providing comprehensive and unified security.
Despite CASBs’ capabilities and familiarity with approaches and techniques used to protect data in on-premise setups ring bell, CASBs, however, are a lot different.
CASBs are often misunderstood. For instance, when CASBs first appeared, it was considered a cloud surveillance solution. However, modern-day CASBs like Strac offer a wide range of capabilities across core compliance, data security, transparency, and threat protection.

So what else does Strac help us achieve?
Strac as a comprehensive data loss prevention (DLP) solution helps companies of all sizes:

In conclusion, the power of CASBs, particularly Strac, extends far beyond simple surveillance. Its proactive approach to data loss prevention, compliance, and threat detection make it an indispensable tool for robust cloud security strategies.
Understanding the prominent use cases, such as data loss prevention (DLP), threat protection, and compliance, will help you determine if the CASB aligns with your organization's security goals.
Instead of blocking entire services, ensure you can control specific activities (e.g., file sharing) across all cloud storage services.
Verify that the CASB can enforce data policies across sanctioned and unsanctioned services while minimizing false positives.
Ensure the CASB offers flexible deployment options, including on-premises and cloud-based models.
Ensure the CASB can detect anomalies like excessive downloads or suspicious activity across all cloud services.
Confirm that the CASB can monitor and report activities in regulated services to comply with regulations like Sarbanes-Oxley.
Inquire about the range of data protection policies the CASB can enforce, such as encryption, tokenization, and access controls, to ensure comprehensive data security.
Ensure the CASB can identify and protect against compromised user accounts.
Confirm the CASB's ability to identify and mitigate threats and malware in all cloud services.
Check if the CASB can integrate with existing on-premises security solutions like DLP, SIEM, and EDR.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

