What is a DLP Endpoint Agent?
Why endpoint agents are the frontline defenders in modern data loss prevention and how Strac sets the new standard.
In this guide, we’ll dive into what is aDLP endpoint agent, how it works, what problems it solves, and what a modern DLP agent should look like; and we’ll explore how Strac takes this to the next level with automated remediation and cloud-native protection.
A DLP endpoint agent is a lightweight software component installed on user devices (e.g., Windows, macOS, Linux machines) to monitor, detect, and control the movement of sensitive data. It enforces security policies directly at the device level; even when the device is offline or outside corporate networks.
Think of it as your on-device data guardian.
It monitors activities like:
Real-World Example 1:
An employee attempts to copy a file containing Social Security Numbers to a personal USB drive. The DLP endpoint agent detects the data pattern and blocks the action immediately.
Real-World Example 2:
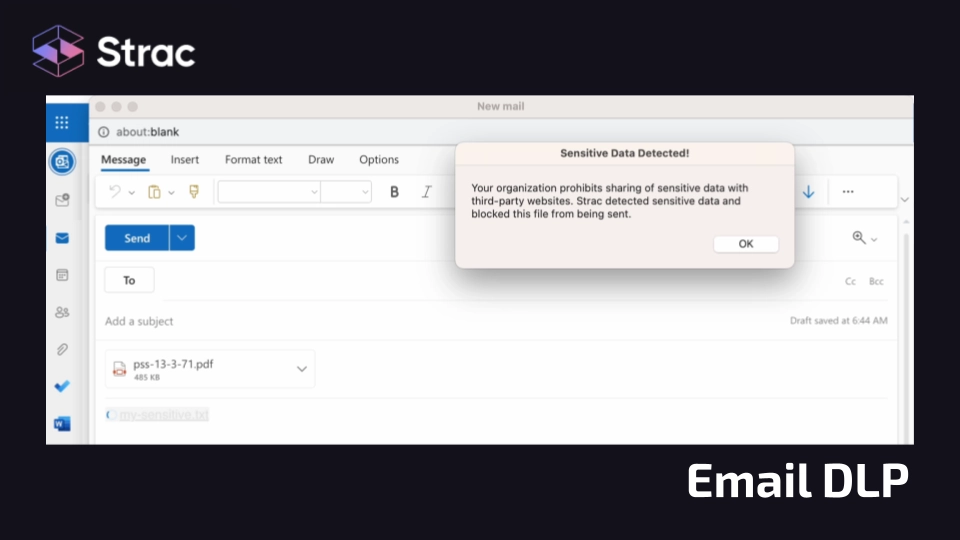
A contractor tries to email a spreadsheet with PHI (Protected Health Information) to an external recipient. The agent redacts the sensitive fields and sends an alert to the security team.
Real-World Example 3:
A developer screenshots source code and tries to upload it to ChatGPT. The endpoint DLP agent intercepts the screenshot before upload and prevents the leak.
For cross-platform coverage, check out how Strac enables endpoint protection for:
The endpoint is often the weakest link in your security chain; and it’s where sensitive data is most vulnerable. A DLP endpoint agent mitigates numerous data risks, including:
Example 1:
An intern tries uploading client financial data to Google Drive — the agent flags the activity, encrypts the file, and sends an alert to the admin.
Example 2:
A disgruntled employee prints payroll documents. The DLP agent detects the pattern and disables printing functionality for sensitive data.
Example 3:
A remote worker is using a browser-based AI tool to process confidential legal documents. The agent redacts sensitive fields before submission.

A good DLP endpoint agent doesn’t just scan and alert. It follows the data, understands context, and steps in when something risky actually happens. It should feel invisible to users; but very visible when there’s a real problem.
Here’s what that looks like:
If an endpoint agent can’t follow the data and enforce policy in the moment, it’s not really protecting anything.
We don’t work behind a perimeter anymore. Sensitive data lives on laptops, inside browsers, across SaaS apps, and now inside AI tools. The endpoint is where real data movement happens.
Here’s why that matters:
Remote and hybrid work is permanent.
Data moves through home networks, USB drives, personal browsers, and unsanctioned apps. If you don’t control the endpoint, you don’t control the risk.
GenAI created a new leakage vector.
Employees paste contracts, source code, PHI, and payroll data into ChatGPT and Copilot every day. Traditional DLP wasn’t built for prompt streams or browser-based AI. Modern endpoint DLP must inspect, redact, or block sensitive data before it reaches AI systems; not after exposure.
Strac GenAI DLP
Insider risk happens at the device level.
Most leaks aren’t dramatic. They’re copy-paste, uploads, prints, screenshots. Those actions happen on the endpoint; enforcement must happen there too.
Compliance now requires enforcement and traceability.
CCPA, HIPAA, PCI, and AI governance frameworks expect provable controls; not just written policies.
And this is where data lineage becomes critical.
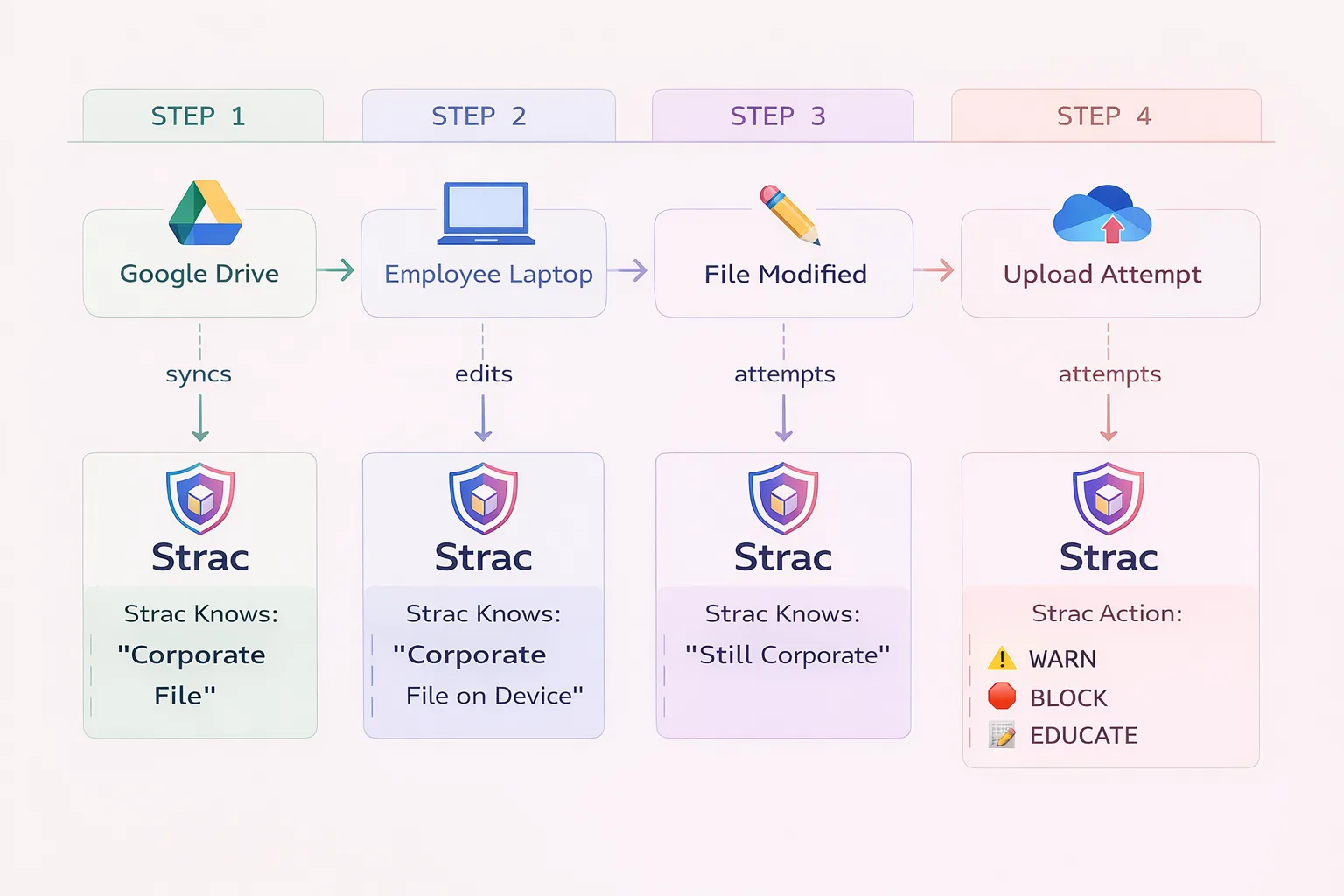
Blocking a file transfer isn’t enough. Security teams need to see where sensitive data originated, who accessed it, how it moved from endpoint to SaaS to AI, and whether an incident is isolated or part of a broader exposure chain.
Without endpoint enforcement and data lineage visibility; you’re not just exposed; you’re blind to how exposure spreads.
Strac reimagines the traditional endpoint DLP with a powerful, cloud-native solution that combines Data Discovery, DSPM, and advanced DLP; and full data lineage visibility across endpoints and SaaS applications; all from one pane of glass.
How Strac stands out:
See what our customers are saying on G2
Below is a quick comparison between Strac and Traditional Endpoint DLP Agents.
Yes! A good agent (like Strac’s) enforces policies locally, even when the device isn’t connected to the internet.
Strac’s agent is ultra-lightweight with minimal impact on CPU and memory.
Absolutely. Strac uses OCR and ML to detect sensitive info even in screenshots, scanned documents, or images.
Strac can scan and unpack formats like ZIP, DOCX, XLSX, and more — even nested documents.
Yes! Learn more about Strac Linux DLP
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

