Understanding Data Detection and Response (DDR) for Modern Cybersecurity
Learn what Data Detection and Response (DDR) is and how Strac helps detect, classify, and remediate sensitive data across SaaS, cloud, endpoints, and GenAI in real time.
Data breaches and privacy violations are becoming alarmingly frequent, highlighting the urgent need for robust data protection strategies. Organizations must swiftly detect and respond to threats to safeguard sensitive information & maintain compliance with stringent regulations.
This raises an important question: What is Data Detection and Response (DDR)?
Strac addresses these challenges by offering comprehensive Data Detection and Response (DDR) solutions. With real-time monitoring, automated remediation, and seamless integration capabilities, Strac empowers organizations to protect their data effectively while ensuring compliance with standards like GDPR and HIPAA.
Data Detection and Response (DDR) refers to a suite of technologies and practices designed to identify, monitor, and respond to data security threats in real-time. DDR solutions focus on the detection of anomalies or unauthorized access to sensitive data, followed by an appropriate response to mitigate risks.
This proactive approach is essential in today's digital landscape, where data breaches & privacy violations are increasingly common.
DDR plays a crucial role in cybersecurity by providing organizations with the ability to:
By integrating DDR into their security frameworks, organizations can enhance their overall security posture & lower the risk of data loss.
Organizations need DDR for several reasons:

DDR is integral in preventing data privacy violations by:
Dynamic monitoring enhances Data Security Posture Management (DSPM) by providing real-time visibility into data access patterns and potential vulnerabilities. This allows organizations to:
Effective DDR solutions typically include four key components:
In the context of databases, DDR refers specifically to the practices and tools used to monitor database activity for unauthorized access or anomalies. This includes:
When selecting a DDR solution, consider the following features:
Key considerations when evaluating a DDR product include:

The future of DDR will likely involve:
In cloud environments, DDR integrates by providing:
Data Detection and Response (DDR) focuses on identifying and responding to data-specific threats, primarily concerning sensitive information. It is designed to monitor data access patterns, detect anomalies, and implement remediation actions when unauthorized access occurs.
Endpoint Detection and Response (EDR), on the other hand, is concentrated on endpoint devices such as laptops, desktops, and servers. EDR solutions track endpoint activities to identify potential threats, isolate affected devices, and respond to incidents at the endpoint level.
Extended Detection and Response (XDR) provides a broader approach by integrating data from multiple security layers—such as network, endpoint, server, and email security—into a unified platform. This allows for more complete threat detection and response across an organization’s entire security landscape.
Primary Focus:
DDR: Data-specific threats.
EDR: Endpoint-specific threats.
XDR: Cross-layered threat detection.
Scope:
DDR: Limited to data.
EDR: Focused on endpoints.
XDR: Comprehensive across multiple layers.
Response Mechanism:
DDR: Automated remediation actions for data breaches.
EDR: Endpoint isolation and threat containment.
XDR: Unified response across systems for a coordinated approach.
Data Detection and Response (DDR) & Data Security Posture Management (DSPM) are two distinct approaches to data security, each with its own focus and methodology.
DDR is a reactive strategy that emphasizes:
In essence, DDR focuses on actively identifying and responding to data threats as they occur.
DSPM takes a proactive approach by:
DSPM is about assessing and managing the overall security landscape to prevent incidents before they happen.
Together, DDR and DSPM create a comprehensive framework for protecting sensitive data against cyber threats.
Strac is a unified DLP + DSPM platform built to handle Data Detection and Response (DDR) across SaaS, Cloud, Endpoints, and GenAI environments; not just detect risk, but act on it in real time.
Strac provides a robust framework for enhancing Data Detection and Response (DDR) capabilities through several key features:
GenAI and Browser Protection: Strac extends DDR into GenAI workflows and browser activity. It can detect, block, or redact sensitive data in tools like ChatGPT, Gemini, and Copilot, ensuring employees don’t accidentally leak PII, PCI, or confidential data into AI systems.
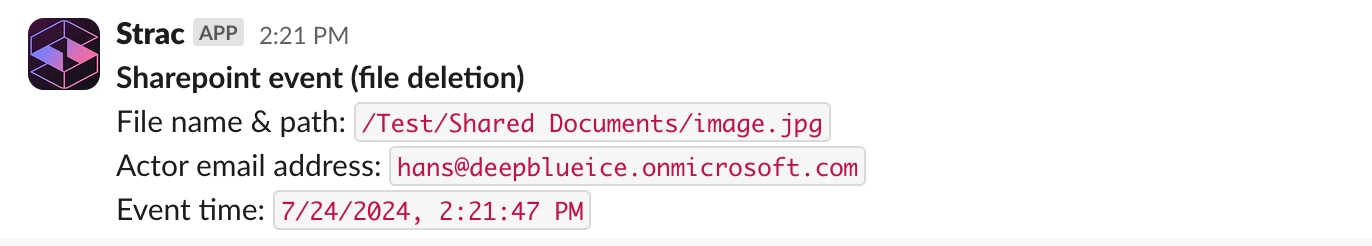
Automated Remediation (Not Just Alerts): When risk is detected, Strac takes action instantly. It can redact, mask, revoke access, delete, block, or alert based on policy. This inline remediation is critical; detection without action leaves gaps, while Strac closes them in real time.
Inline Redaction Across All Data Types: Strac can automatically redact sensitive data inside messages and files, including PDFs, images, screenshots, Word docs, and spreadsheets. This works across chat tools, support tickets, and attachments; not just plain text.

Sensitive Data Discovery and Classification: Strac automatically discovers and classifies sensitive data across SaaS apps (Slack, Gmail, Google Drive, Salesforce, Zendesk, Notion), cloud (AWS S3, Azure, databases), endpoints, and file systems. It works across structured and unstructured data, including files, chats, tickets, and attachments. Using contextual ML (not just regex), it delivers high accuracy with low false positives, so teams can prioritize real risks instead of noise.

Comprehensive Coverage Across Environments:
Strac unifies DDR across:

This eliminates blind spots and removes the need for multiple disconnected tools.
Custom Detection and AI Data Elements: Strac supports out-of-the-box detectors for PII, PHI, PCI, and compliance frameworks, plus custom data definitions. You can define organization-specific sensitive data and enforce policies globally.

Compliance-Ready by Default: Strac helps enforce compliance with GDPR, HIPAA, PCI DSS, SOC 2, ISO 27001, CCPA, and NIST through built-in templates, audit trails, and automated enforcement.
Fast, Agentless Deployment: Strac is agentless and deploys in minutes, with minimal friction for security and engineering teams. No heavy infrastructure, no long rollout cycles; immediate visibility and control.
API and Integration Flexibility: Strac provides APIs and deep integrations, allowing teams to programmatically detect and remediate sensitive data across custom workflows and applications.
Proven at Scale: Strac is already deployed in production at companies like UiPath and others, handling real-world sensitive data across high-volume environments.
In conclusion, understanding What is Data Detection and Response (DDR) is essential for modern organizations to safeguard sensitive information against evolving cyber threats. By focusing on real-time monitoring, automated responses, and regulatory compliance, DDR solutions help minimize risks and protect data integrity.
Strac stands out as a comprehensive DDR solution, offering features such as sensitive data discovery, real-time monitoring, automated remediation, and integration with existing security tools. By leveraging Strac, organizations can enhance their security posture, ensure compliance, & build trust with customers by effectively protecting their valuable data assets.
Most traditional DLP tools stop at detection and generate alerts; Data Detection and Response (DDR) goes further by automatically acting on threats in real time. With platforms like Strac, sensitive data is not just identified; it is instantly redacted, blocked, or remediated, closing the gap between detection and protection.
Yes; modern DDR solutions like Strac are built for SaaS and GenAI environments, where most data leaks happen today. They can detect and block or redact sensitive data in real time across chat, email, cloud storage, and AI tools, preventing exposure before it happens.
Many DDR tools rely heavily on regex and static rules, which leads to high false positives and missed risks. Strac solves this with contextual machine learning and OCR, enabling accurate detection across files, images, and unstructured data with far less noise.
DDR alone is not enough. DDR is reactive (detect + respond), while DSPM is proactive (discover + assess risk). Strac combines DDR + DSPM in one platform, so you can find, monitor, and fix sensitive data risks across your entire data estate without tool sprawl.
Unlike legacy tools that take months, Strac is agentless and deploys in minutes. Teams can start scanning, detecting, and remediating sensitive data almost immediately; without heavy infrastructure or complex setup.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

