What the Nike Data Breach Reveals About Modern Data Security and Where Traditional DLP Failed
The Nike breach shows why legacy DLP fails. Modern data protection tracks data movement, lineage, and sensitive data across SaaS, cloud, and AI.
When news broke that over a terabyte of Nike’s internal data had allegedly been stolen, most headlines focused on the size of the leak.
But the size isn’t the most interesting part.
The type of data is.
Reports suggest the breach included internal documents like product designs, manufacturing workflows, factory audits, and R&D material accumulated over several years.
That isn’t customer data.
It’s operational intelligence.
And incidents like this highlight a growing shift in cybersecurity: attackers increasingly want the information that runs the business, not just the information about customers.
Many security strategies still think about data protection in terms of files leaving the network.
But that’s not how modern organizations work anymore.
Data moves constantly between tools.
An engineer might create a design document. Someone else opens it in a collaboration tool. Another team shares part of it with a vendor. A contractor downloads a copy for analysis.
Each step creates new versions and new exposure points.
By the time a document actually leaves the organization, it may already exist in multiple systems and multiple formats.
This is where traditional security approaches struggle.
They were built around the idea that data has a clear location and clear boundaries.
In reality, data now behaves more like a network of relationships across systems.
For years, attackers focused primarily on personal data.
Credit cards.
Healthcare records.
Login credentials.
Those datasets are valuable, but they’re also heavily regulated. Organizations have spent years building protections around them.
Operational data is different.
Documents like:
often fall outside traditional compliance frameworks.
Yet in many cases, these assets represent the core intellectual property of the company.
Stealing them doesn’t just expose individuals.
It can impact entire industries and markets.
That’s why attackers are increasingly shifting toward this type of information.
Traditional DLP tools were designed for a very specific type of risk: accidental data leakage.
For example:
In those cases, pattern detection works well.
But operational data rarely follows predictable patterns.
A design document might contain no obvious identifiers.
A manufacturing report might look harmless on its own.
The risk only becomes visible when multiple pieces of data are combined together.
This is why protecting modern data environments requires a different mindset.
Instead of focusing only on patterns inside files, organizations need to understand how data connects across systems and workflows.
One of the biggest challenges security teams face today is simple:
They don’t always know where sensitive data actually lives.
Modern companies operate across dozens of platforms:
Data flows between them constantly.
Without continuous discovery and monitoring, it becomes difficult to answer basic questions:
Where are sensitive documents stored?
Who has access to them?
How often are they downloaded or shared?
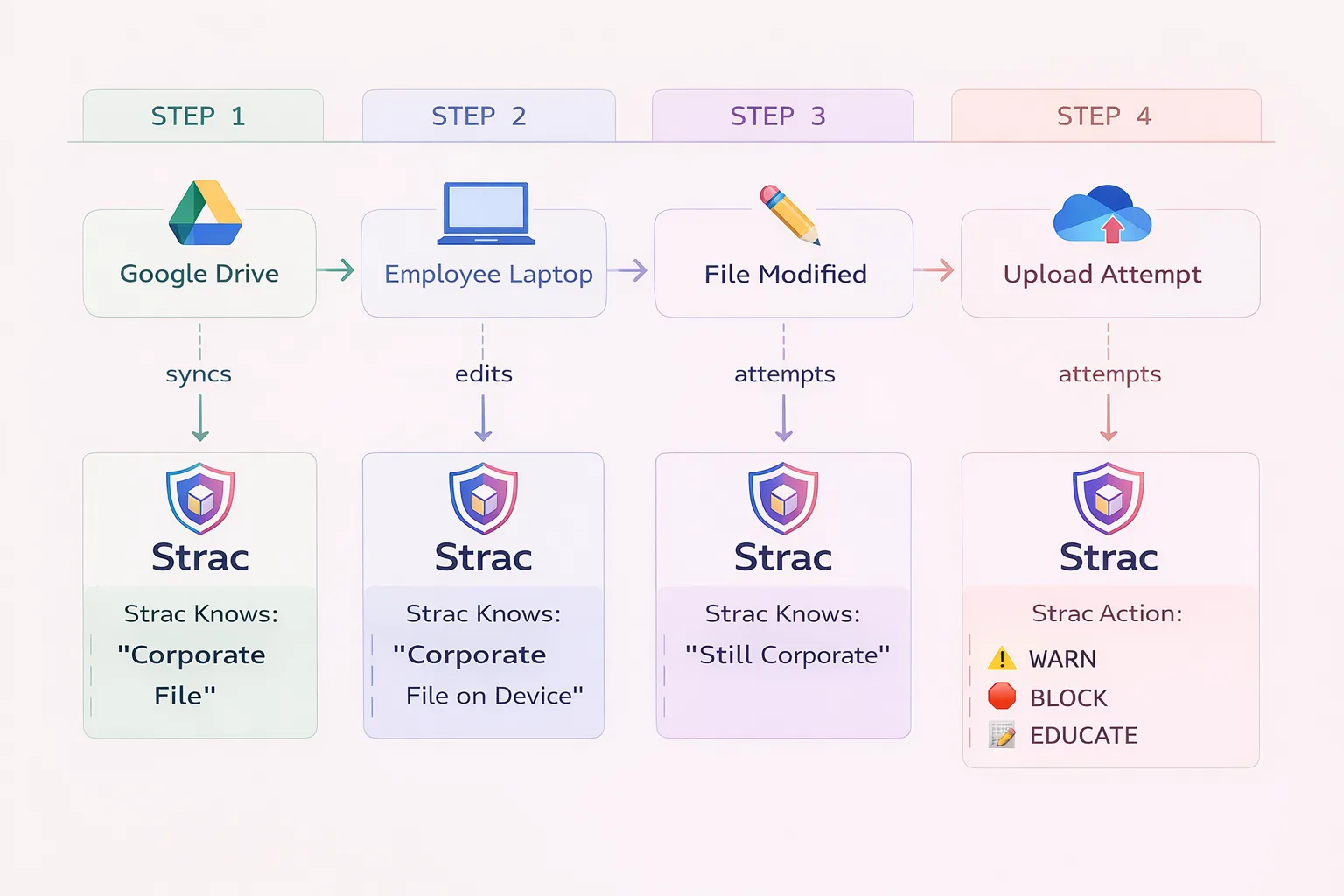
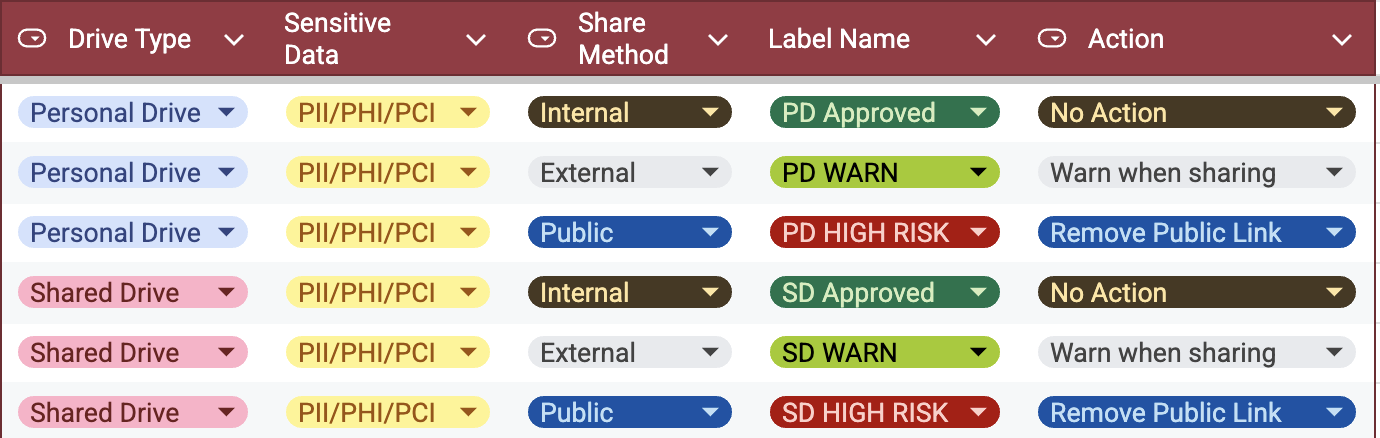
Modern data security platforms address this by continuously scanning and classifying information across SaaS applications, cloud systems, endpoints, and AI environments to build a complete picture of the organization’s data landscape.
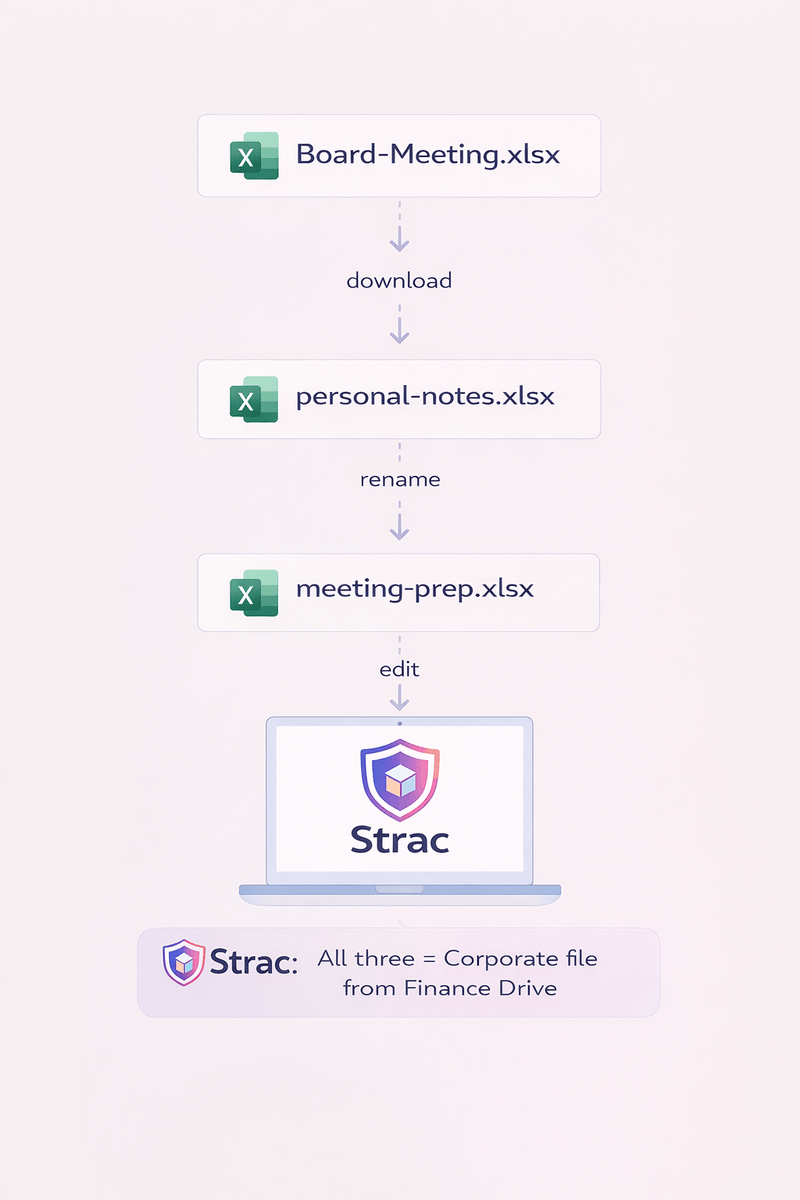
Looking at individual files rarely tells the full story.
What matters is context.
For example:
A single factory audit report may be routine.
But if someone downloads hundreds of audits, along with supplier lists and manufacturing documentation, that pattern looks very different.
Modern data security systems analyze these broader patterns:
This type of contextual analysis helps security teams understand how data is being used, not just what it contains.
Protecting modern data environments requires moving beyond static policies.
Organizations increasingly focus on three capabilities:
Continuous data discovery
Sensitive information must be identified automatically across all systems where it exists.

Context-aware monitoring
Security tools need to analyze how data moves and how users interact with it.
Automated remediation
When sensitive information appears in the wrong place, systems should be able to take action such as redaction, masking, or access restriction.
These capabilities allow organizations to protect data throughout its lifecycle, not just when it leaves the network.
Breaches like the Nike incident reveal an important truth.
The most valuable data inside organizations often isn’t the data we traditionally focus on protecting.
It’s the operational knowledge that powers the business.
Protecting that information requires visibility into where data exists, how it moves, and how different pieces of information relate to one another.
Because in modern environments, the biggest risk isn’t just that data leaks.
It’s that organizations lose track of it entirely.
Breaches like the Nike incident show something important.
The problem isn’t just attackers getting smarter.
It’s that data environments have fundamentally changed.
Today, sensitive information moves constantly between tools:
Traditional DLP systems were built for a world where most data lived inside corporate networks. That world doesn’t exist anymore.
Security teams need a way to see where sensitive data actually lives, understand how it moves, and respond quickly when risks appear.
That’s where modern platforms like Strac come in.
Instead of relying only on static rules, Strac continuously discovers, classifies, and protects sensitive data across SaaS apps, cloud storage, endpoints, and AI environments.

The Nike breach is another reminder that the data security landscape is changing.
Sensitive information now spreads across SaaS tools, cloud platforms, developer environments, and AI systems. Traditional approaches built around static rules and network boundaries struggle to keep up with that complexity.
Modern data protection focuses on visibility, context, and continuous monitoring so organizations can understand and secure their data wherever it lives.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

