The Coinbase Breach Proves Traditional DLP Is No Longer Enough
The Coinbase breach shows why traditional DLP fails against insider threats. Learn how modern data protection tracks sensitive data movement across SaaS and AI tools.
When Coinbase disclosed the breach affecting nearly 70,000 customer records, the story surprised many security teams.
The attackers didn’t break through a firewall.
They didn’t exploit a zero-day vulnerability.
Instead, customer service agents were bribed to access and share customer data.
Those agents already had permission to view sensitive information such as:
From a traditional security perspective, everything looked normal.
The agents logged in using legitimate credentials and accessed the systems they were supposed to use.
That’s what makes insider-driven breaches so difficult to detect.
The problem isn’t access.
The problem is what happens after the data is accessed.
Traditional DLP systems are built around a simple idea: detect sensitive patterns in files or messages.
If the system sees something like a credit card number or Social Security number, it raises an alert.
But that approach assumes the risky action is the transfer itself.
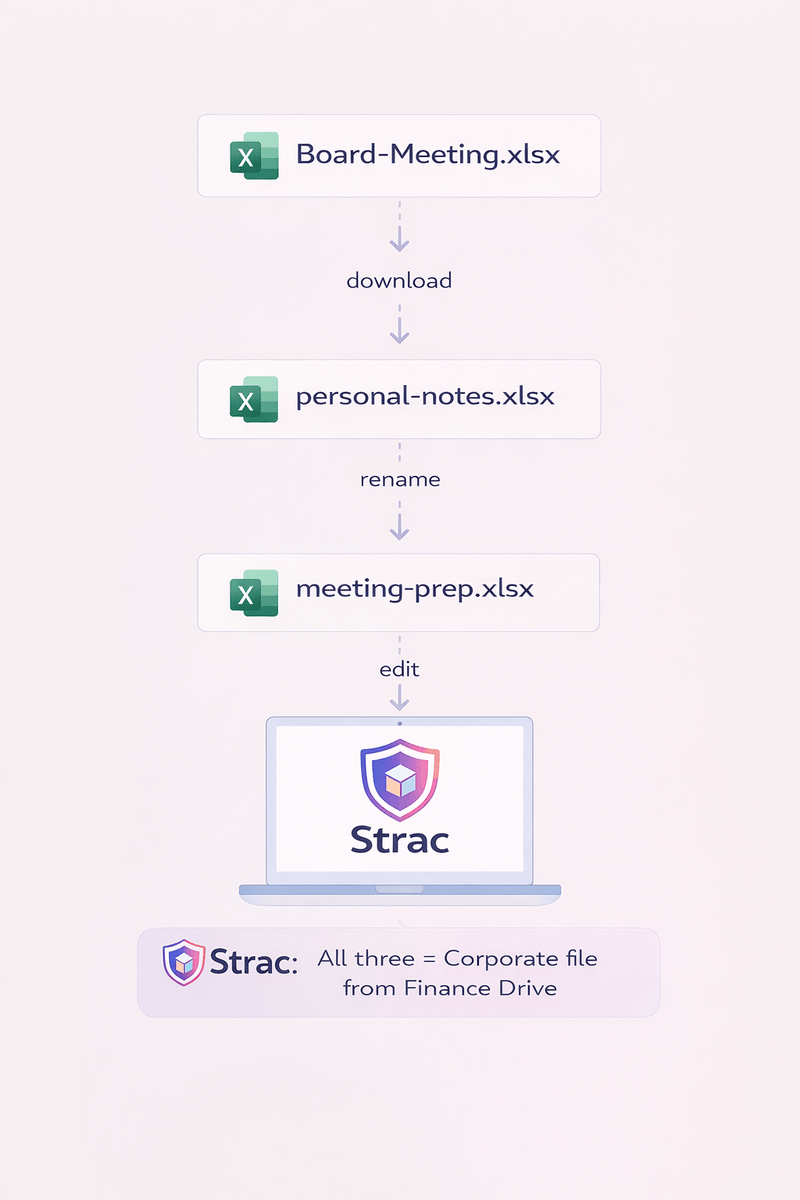
In insider-driven incidents, the transfer rarely happens in a single obvious step.
Instead, sensitive data moves gradually across everyday workflows.
For example:
Each step looks normal on its own.
But together, they form a clear path for data exposure.
In modern environments, data rarely leaves through a single file download.
Instead, it often exits through everyday tools employees use constantly.
Some of the most common exit paths include:
None of these actions necessarily trigger a traditional DLP alert.
To most systems, they simply look like normal employee activity.
But when sensitive data begins appearing across multiple tools outside its original system, that movement tells a different story.

Here’s what modern monitoring can reveal when you look at how sensitive data moves, not just the content itself.
A support agent accesses customer records during their shift; normal.
They paste part of that data into a Slack message to ask a teammate for help; still common.
Minutes later, the same information appears in a support ticket or an AI prompt.
Individually, none of these actions look suspicious.
But together they show something important: sensitive data is moving across multiple systems very quickly.
Traditional DLP tools usually treat these as isolated events. They may detect sensitive content, but they often miss the broader pattern of how that data spreads.
Modern platforms like Strac focus on that missing layer; tracking where sensitive data appears and how it moves across SaaS apps, cloud storage, and AI tools, so risky patterns become visible and can be stopped earlier.
Another challenge with traditional DLP is that most systems focus primarily on alerts.
Security teams receive notifications when sensitive data is detected somewhere unusual.
But by the time the alert appears, the data may already exist in several other places.
Security teams then have to investigate:
This reactive approach makes insider-driven incidents especially difficult to contain.
Modern data protection strategies focus on reducing risk immediately, not just reporting it.
When sensitive information appears in the wrong location, the system should be able to:
Stopping the exposure in real time is far more effective than responding after the fact.
Modern platforms like Strac are designed around a different assumption: sensitive data constantly moves across systems.
Instead of focusing only on file scanning, modern platforms combine:
This approach allows security teams to see how sensitive data spreads across environments such as:
Because Strac uses an agentless architecture, organizations can deploy protection across multiple SaaS platforms without introducing heavy infrastructure or slowing teams down.

This makes it possible to detect and reduce exposure earlier, before sensitive data spreads across multiple systems.
The Coinbase incident highlights an important shift in how data protection needs to work.
The biggest risk is no longer a single file leaving the organization.
Instead, it is sensitive data gradually spreading across the modern software stack.
When organizations rely only on pattern detection or isolated alerts, they miss the broader picture of how insider-driven data exposure actually unfolds.
Modern data protection must focus on three things:
The Coinbase breach is a reminder that insider threats rarely look like traditional attacks.
Employees often have legitimate access to sensitive information. The real risk begins when that information starts moving beyond its intended system.
Traditional DLP tools were designed to detect sensitive content.
Modern environments require something more: visibility into how sensitive data spreads across tools, users, and workflows.
Organizations that can see and control that movement will be far better positioned to prevent the next insider-driven breach.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

