Palo Alto DLP Alternatives
Palo Alto DLP Alternatives in 2026. Compare Palo Alto vs Strac and other DLP solutions for SaaS, cloud, AI, and endpoint protection.
If you're evaluating Palo Alto DLP alternatives, you're likely asking a practical question: Does Palo Alto DLP actually protect sensitive data across SaaS apps, cloud storage, endpoints, and AI tools; without adding operational friction?
Palo Alto DLP extends from its firewall and Prisma ecosystem. That architecture works well for network-centric environments. But in 2026, most data risk doesn’t sit at the perimeter. It lives inside Slack threads, Salesforce records, Google Drive files, Zendesk tickets, and AI prompts.
So the real evaluation isn’t whether Palo Alto DLP works. It’s whether it’s built for where data actually moves today. Let’s break it down.
When evaluating Palo Alto DLP, you’ll see these core capabilities:
Delivered through Prisma Access, NGFW, and Prisma SaaS. Policies are centrally managed and enforced through Palo Alto’s infrastructure.
Covers web traffic, SaaS apps (via CASB/API), email (M365/Gmail), and limited endpoint exfiltration vectors like USB and printing.

Combines regex, pattern detection, fingerprinting, and some ML-based classification for identifying PII, PCI, PHI, and custom data types.
DLP violations surface in Panorama or Strata Cloud Manager for investigation and response.
Prebuilt detection profiles for GDPR, HIPAA, PCI-DSS, and other regulatory standards.
For organizations already running Palo Alto firewalls and Prisma Access, this feels like a natural add-on.
But SaaS protection in 2026 requires more than traffic inspection.
Here’s where the reality check begins.
Palo Alto DLP works best when traffic flows through Palo Alto infrastructure. If SaaS usage happens outside that path; unmanaged devices, remote users, shadow tools; visibility drops.
Modern SaaS environments are API-driven and distributed. Firewall-first enforcement has limits.
Despite marketing that suggests “turn it on,” real deployments often require:
For mid-sized SaaS teams, this isn’t lightweight.
Pattern-based detection requires constant refinement. Broad regex rules often trigger alert fatigue. Security teams end up spending weeks tuning policies to reduce noise.
In SaaS workflows where messages move fast, excessive blocking breaks productivity.
Detection is strong. But real-time redaction inside SaaS apps; Slack messages, Zendesk tickets, Salesforce case comments; isn’t always native or immediate.
Alerting without remediation leaves risk exposed.
Blocking traffic to ChatGPT domains is one thing. Inspecting prompts and responses contextually, across AI integrations and APIs, is another.
AI-driven environments require deeper prompt-level inspection, not just domain filtering.
Security leaders using Palo Alto DLP in SaaS-heavy environments typically report:
The tool works. But it was designed from the firewall outward, not from SaaS inward.
That distinction matters in 2026.
If you're evaluating Palo Alto DLP for SaaS environments, you're likely doing so because something feels heavy, complex, or misaligned with how your teams actually work.
Below are the top alternatives security leaders consider in 2026; starting with the most SaaS-aligned option.
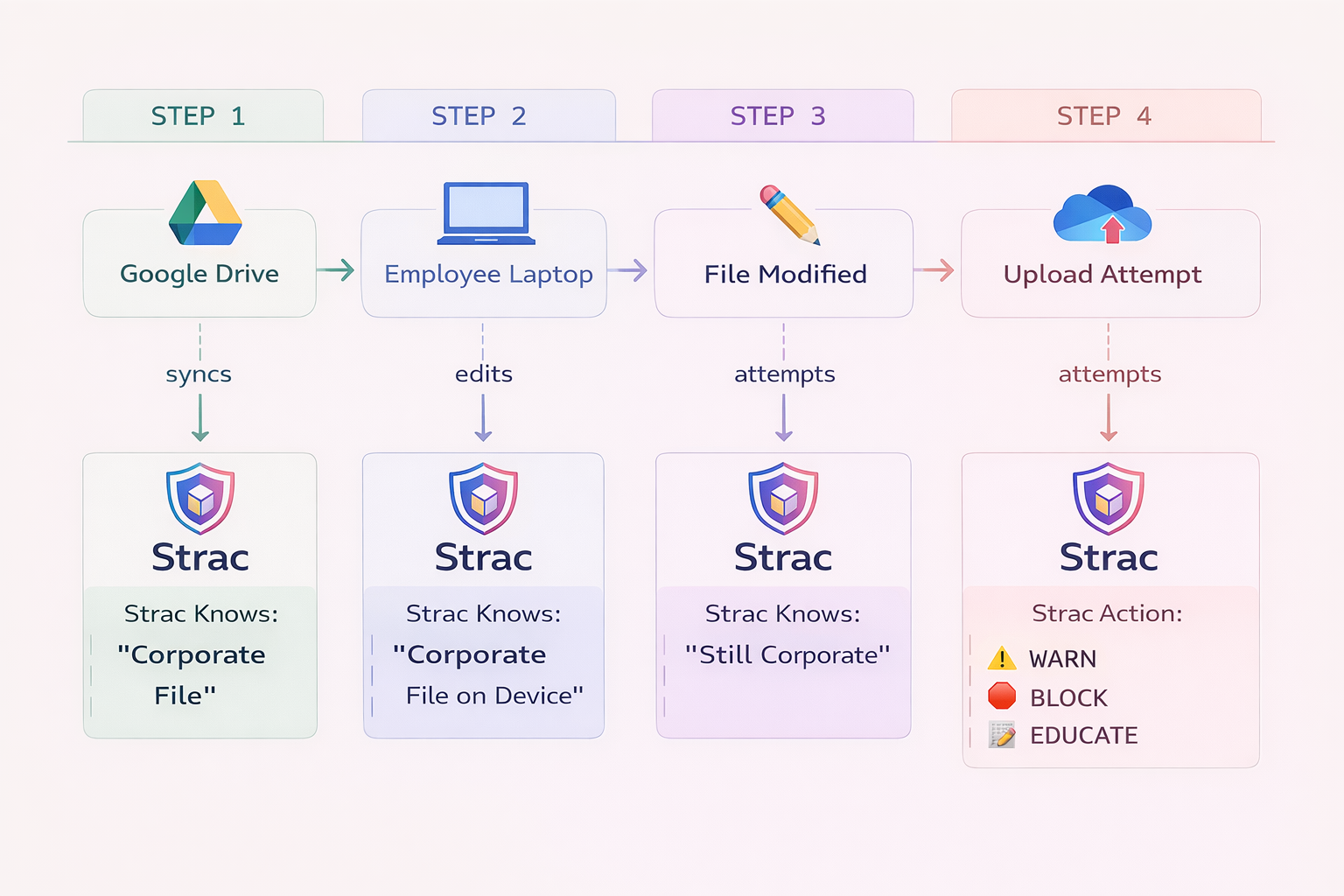
Strac is built specifically for modern SaaS, cloud, and AI workflows; not legacy firewall perimeters.
Instead of routing traffic through network enforcement points, Strac integrates directly into SaaS applications and APIs. That architectural difference matters in distributed, app-first environments.

Unified SaaS + Cloud + Endpoint + AI DLP
Strac integrates directly with Slack, Zendesk, Gmail, Google Drive, Microsoft 365 (Email + OneDrive), Salesforce, Intercom, Notion, and more — plus AWS (S3, RDS, CloudWatch), Azure, GCP, and macOS / Windows / Linux endpoints.
One control plane across apps, cloud storage, AI tools, and devices.
GenAI Protection
Blocks or redacts sensitive data in ChatGPT, Gemini, Copilot, Claude, and other LLM APIs. Protection happens at the prompt and response level.
Accurate Detection & Redaction
Contextual ML + OCR detect PII, PHI, PCI, secrets, and custom data elements across chat messages and all file formats; including PDFs, images, screenshots, Word docs, and spreadsheets.
Automated Remediation
Inline redaction, masking, access revocation, quarantine, and alerts; without manual review loops.
Compliance-Ready
Supports PCI, SOC 2, HIPAA, ISO-27001, CCPA, GDPR, and NIST frameworks.
Fully Customizable
Granular control over policies, detectors, access rules, and remediation workflows.

Fast deployment
Integrates in minutes. Live scanning and inline redaction start immediately across SaaS apps.
High detection accuracy
Contextual ML + OCR reduce false positives while detecting PII, PHI, PCI, secrets, and custom sensitive data.

Deep SaaS + Cloud coverage
Broad integrations across Slack, Zendesk, Gmail, Google Drive, Microsoft 365, Salesforce, Intercom, AWS, Azure, GCP, and more.
All document formats supported
Scans and redacts PDFs, images, screenshots, Word docs, spreadsheets, and attachments natively.
Inline redaction
Masks or blurs sensitive content directly inside messages and files; not just alerts.
AI-native protection
Protects LLM APIs and AI websites like ChatGPT, Gemini, Copilot, and others at the prompt level.
Endpoint DLP included
Works across macOS, Windows, and Linux alongside SaaS and Cloud protection.
Built-in + custom detectors
Prebuilt compliance templates for PCI, HIPAA, GDPR, SOC 2; plus fully customizable data elements.
API support
Developer APIs for detection and redaction workflows.
Strong customer support
Hands-on guidance from deployment through production.
Ideal for: SaaS-first companies, fintech, healthtech, and distributed teams that need real-time protection inside applications; not just at the network edge.
Zscaler provides strong SASE and CASB capabilities with cloud-delivered enforcement.
It’s architecturally closer to Palo Alto, focusing on:
Strong at network-layer enforcement. Less application-native compared to SaaS-first platforms.
Ideal for:
Enterprises already invested in SASE and Zero Trust network transformation.

Enterprise-grade DLP with strong endpoint and network enforcement. Mature and comprehensive but resource-heavy and complex.
Better suited for traditional enterprise environments.
Ideal for: Large enterprises with established on-prem infrastructure and insider threat programs that require deep endpoint controls.
Long-standing enterprise DLP suite with endpoint, network, and at-rest scanning.
Very comprehensive; also very heavy. Often requires significant infrastructure and tuning.
Ideal for:
Highly regulated enterprises that require deep data-at-rest discovery across file shares, legacy systems, and complex compliance mandates.
Endpoint-focused DLP tied into broader XDR strategy. Useful if you're already invested in the Trellix ecosystem.
Less SaaS-native.
Ideal for: Security teams prioritizing endpoint telemetry integration with XDR rather than SaaS-native, API-level coverage.
When evaluating Palo Alto DLP alternatives, focus on architecture first.
Ask:
If your environment is firewall-centric, Palo Alto may remain viable.
If your environment is SaaS-heavy and AI-driven, SaaS-native DLP platforms typically align better.
Palo Alto DLP extends strong network security into data protection. For firewall-centric enterprises, that integration makes sense.
But in 2026, most data exposure risk lives:
Modern SaaS teams need:
If your security model starts at the firewall, you’re protecting the edge.
If your risk lives inside applications, you need protection that starts there.
Not originally. It evolved from network and firewall-based architecture. SaaS support exists via Prisma SaaS and integrations, but enforcement often depends on traffic routing.
It can block or alert based on integration setup. However, inline redaction directly inside SaaS messages and files is not always native or immediate.
It can inspect traffic to AI domains when routed through enforcement points. But true AI protection requires contextual prompt and response inspection inside applications and APIs.
Detection relies heavily on pattern-based rules and thresholds. Broad policies create noise. Narrow policies create blind spots. Ongoing refinement is required.
Architecture. If enforcement assumes control at the network layer, but your risk lives inside SaaS applications and AI workflows, protection becomes reactive instead of inline.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

