What the Conduent Breach Actually Reveals About Modern Data Security
The Conduent breach exposed over 25 million records after 83 days of undetected data exfiltration. Learn what it reveals about modern data security and why legacy DLP fails.
The Conduent breach highlights a real gap in modern data security. For 83 days, attackers moved through the company’s systems and quietly exfiltrated about 8 terabytes of sensitive data, including Social Security numbers and healthcare records affecting millions of people.
What stands out is how long the activity went unnoticed. By the time the breach was discovered, the data had already left the environment. Lets dive in!
Conduent, a contractor that processes healthcare and benefits data, was breached in October 2024. Attackers remained inside the environment for nearly three months, quietly exfiltrating about 8 TB of sensitive data, including Social Security numbers, addresses, and medical records.
By the time the breach was discovered in January 2025, more than 25 million people had been affected.
Attackers used legitimate credentials and normal workflows, which made the activity look like regular system use.
Without visibility into the actual sensitive data moving through systems, large-scale data exfiltration can easily go unnoticed.

The Conduent breach also highlights a growing challenge in modern environments; sensitive data is everywhere, and much of it is poorly tracked.
Today, organizations store sensitive information across many different systems, including:
Over time, this creates massive amounts of scattered data. Some files are archived, some duplicated, some shared externally, and much of it ends up unclassified or forgotten.
That creates a large attack surface.
Attackers don’t need to compromise the entire environment. They just need to locate a valuable data repository and slowly move the data out without attracting attention.
The Conduent breach shows why many legacy DLP programs struggle to stop real-world data exfiltration. Most traditional tools rely on:
These approaches work in limited situations but break down in modern environments.
Modern data exfiltration often happens through normal workflows, which means security teams need visibility into the content and movement of sensitive data, not just network traffic.
The Conduent breach makes one thing clear: organizations need continuous visibility into how sensitive data moves across their environment.
Strong data security programs rely on a few core capabilities:
Automatically identify sensitive data across SaaS apps, cloud storage, and collaboration tools.

Continuously categorize data based on sensitivity.
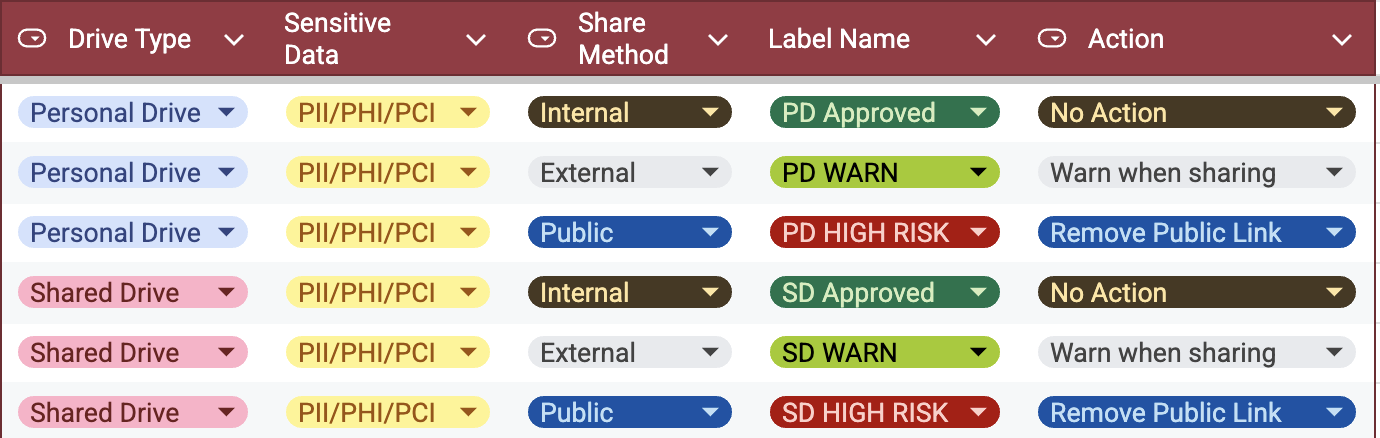
Understand where sensitive data originates and where it moves.
Block transfers, revoke sharing permissions, redact sensitive data, or alert security teams when risky activity occurs.
Together, these capabilities help organizations move from detecting breaches after the fact to preventing data exfiltration in real time.
Breaches like the Conduent incident happen when organizations lack visibility into how sensitive data moves across systems. Attackers often use legitimate credentials and normal workflows, which means traditional network alerts rarely trigger. The only reliable signal becomes the data itself and where it is going.
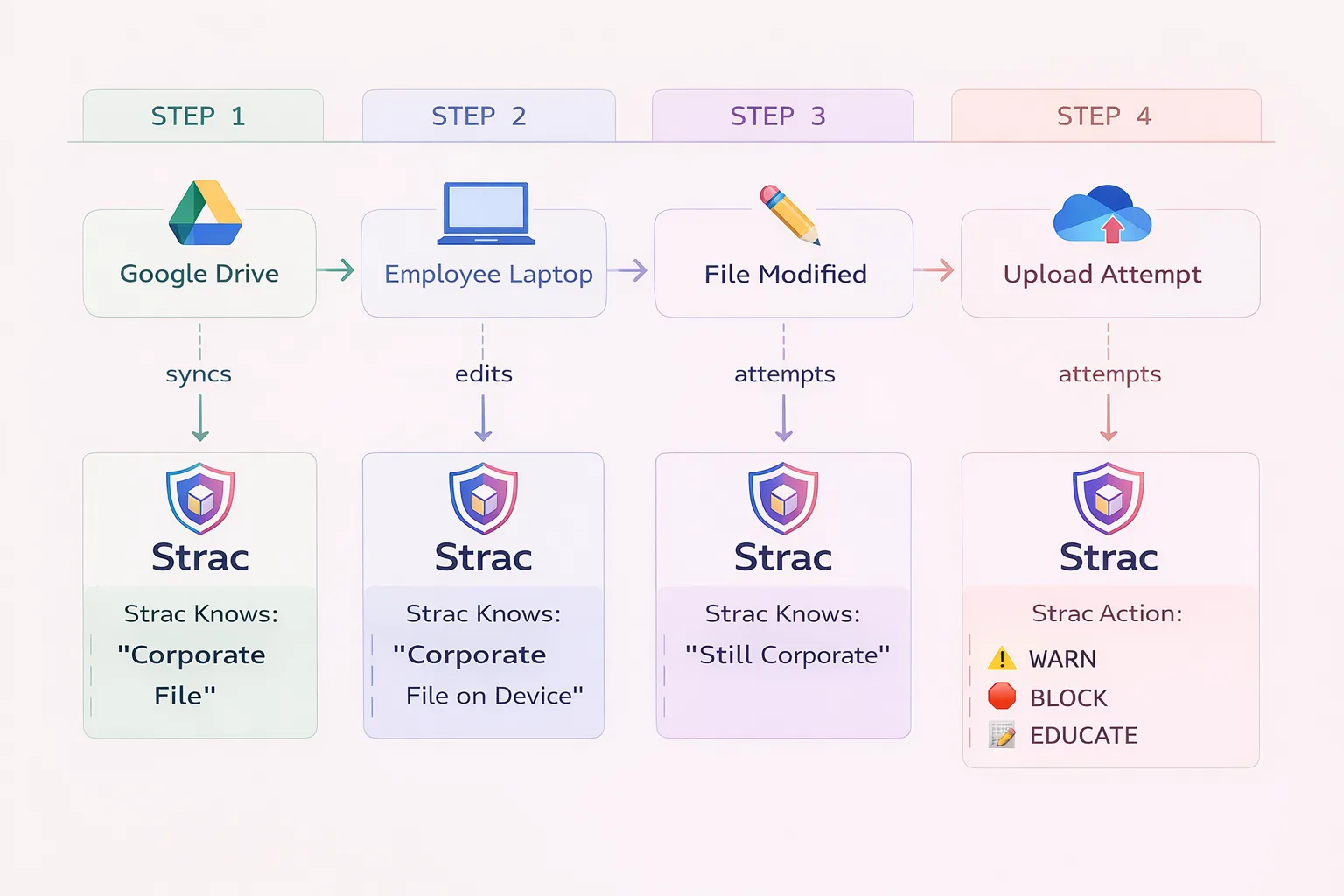
Modern DLP platforms focus on monitoring the content and movement of sensitive data across SaaS apps, cloud environments, endpoints, and AI tools.
Platforms like Strac address this attack pattern in several key ways:
By combining discovery, classification, data movement tracking, and automated response, modern DLP platforms help detect and stop the type of slow, quiet data exfiltration that allowed attackers to operate undetected in the Conduent breach.
Another important takeaway from the Conduent breach is how much the modern data perimeter has expanded.
Sensitive information now moves across a growing set of tools and platforms, including:
Every new platform introduces additional data flows that can potentially be abused by attackers.
Sensitive information may move through:
If these data flows are not monitored at the content level, organizations may unintentionally expose sensitive data through completely legitimate workflows.
The Conduent breach shows how modern attacks work; attackers gain access, stay quiet, and move sensitive data through normal systems until it leaves the environment.
Three lessons stand out:
Platforms like Strac address this by discovering sensitive data, tracking how it moves across SaaS, cloud, endpoints, and AI tools, and automatically remediating exposure before it turns into a breach.
👉 See how Strac detects and stops data exfiltration before it becomes a security incident. Scheduale your demo today!

The Conduent breach was a visibility failure in modern data security architecture.
Attackers succeeded because the movement of sensitive data went unnoticed for nearly three months.
As organizations continue expanding their SaaS, cloud, and AI ecosystems, the ability to discover, classify, monitor, and remediate sensitive data flows in real time will become one of the most important pillars of cybersecurity.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

