TL;DR
- Data security safeguards sensitive data across its lifecycle with controls, governance, and monitoring so only the right people access the right data for the right reasons while keeping it confidential, accurate, and available.
- It matters because breaches, compliance obligations, and a growing SaaS, cloud, and GenAI attack surface demand visibility, least privilege, encryption, DLP, DSPM, backups, and continuous auditability.
- Core controls include authentication and authorization, classification and discovery, encryption and key management, DLP with automated remediation, DSPM, masking/tokenization, retention and erasure, UEBA, and evidence-rich monitoring.
- Biggest risks to prioritize now include public links and oversharing in SaaS, stale or overprivileged access, sensitive data in chats and tickets, secrets in code and CI logs, misconfigurations, shadow IT, and GenAI prompt/output leakage.
- Strac unifies discovery, classification, DLP, and DSPM across SaaS, cloud, browser, endpoints, and GenAI to detect PII/PHI/PCI and code with ML and OCR, then auto redacts, deletes, unshares, or revokes access in place, delivering faster time to fix, fewer open exposures, and smoother audits.
Every company runs on data. Customer profiles, payment records, product roadmaps, source code, clinical notes, and chat transcripts all move through dozens of systems daily. As cloud and SaaS usage grows, so does the attack surface. Data security gives you the guardrails to protect sensitive data wherever it lives and travels, meet compliance obligations, and keep the business resilient. This guide explains what data security is, why it is critical, which controls matter most, and how Strac’s data security platform strengthens protection with real time detection and automated remediation.
What is Data Security?
Data security is the discipline of safeguarding information throughout its lifecycle. It combines technical controls, process controls, and governance to ensure only the right people, devices, and services can access the right data for the right reasons, and that all access is monitored and enforced.
In simple terms: keep sensitive data confidential, accurate, and available, while preventing exposure, misuse, or loss.
Data Security vs Data Privacy vs Data Protection
While the terms data security, data privacy, and data protection are often used interchangeably, they represent distinct — yet interconnected — pillars of a comprehensive information governance strategy. Understanding their differences is essential for building a resilient and compliant data program.
Data Security
Data security focuses on safeguarding data from unauthorized access, breaches, or misuse. It involves the technical and procedural measures used to defend data against cyberattacks, insider threats, and accidental exposure.
Key components include:
- Encryption and access control: Ensuring only authorized users can view or modify data.
- Monitoring and alerting: Detecting abnormal or risky activity in real time.
- Data Loss Prevention (DLP): Blocking or redacting sensitive data shared outside approved channels.
In short, data security is about protecting data from threats — whether malicious or accidental.
Data Privacy
Data privacy deals with how data is collected, processed, and shared. It defines what organizations are allowed to do with personal information and whether individuals have control over their own data.
Key focus areas include:
- Compliance with regulations: Such as GDPR, CCPA, or HIPAA.
- Consent management: Ensuring users agree to data collection and usage.
- Purpose limitation: Using data only for legitimate and disclosed reasons.
Data privacy is about respecting individuals’ rights and ensuring transparency in how their information is handled.
Data Protection
Data protection is the umbrella concept that merges both privacy and security principles. It ensures data remains both secure (protected from breaches) and private (handled lawfully and ethically).
Core aspects include:
- Data retention and deletion policies: Keeping data only as long as necessary.
- Backup and recovery: Safeguarding against data loss due to system failures.
- Governance and compliance: Implementing organization-wide controls to ensure secure and compliant data handling.
Think of it this way:
- Data Security = defense mechanisms (locks and alarms)
- Data Privacy = rules and rights (who can enter and why)
- Data Protection = the entire house management system ensuring both are upheld
Key terms to know
- PII: Personally Identifiable Information such as names, emails, SSNs, addresses.
- PHI: Protected Health Information like patient records, diagnoses, lab results.
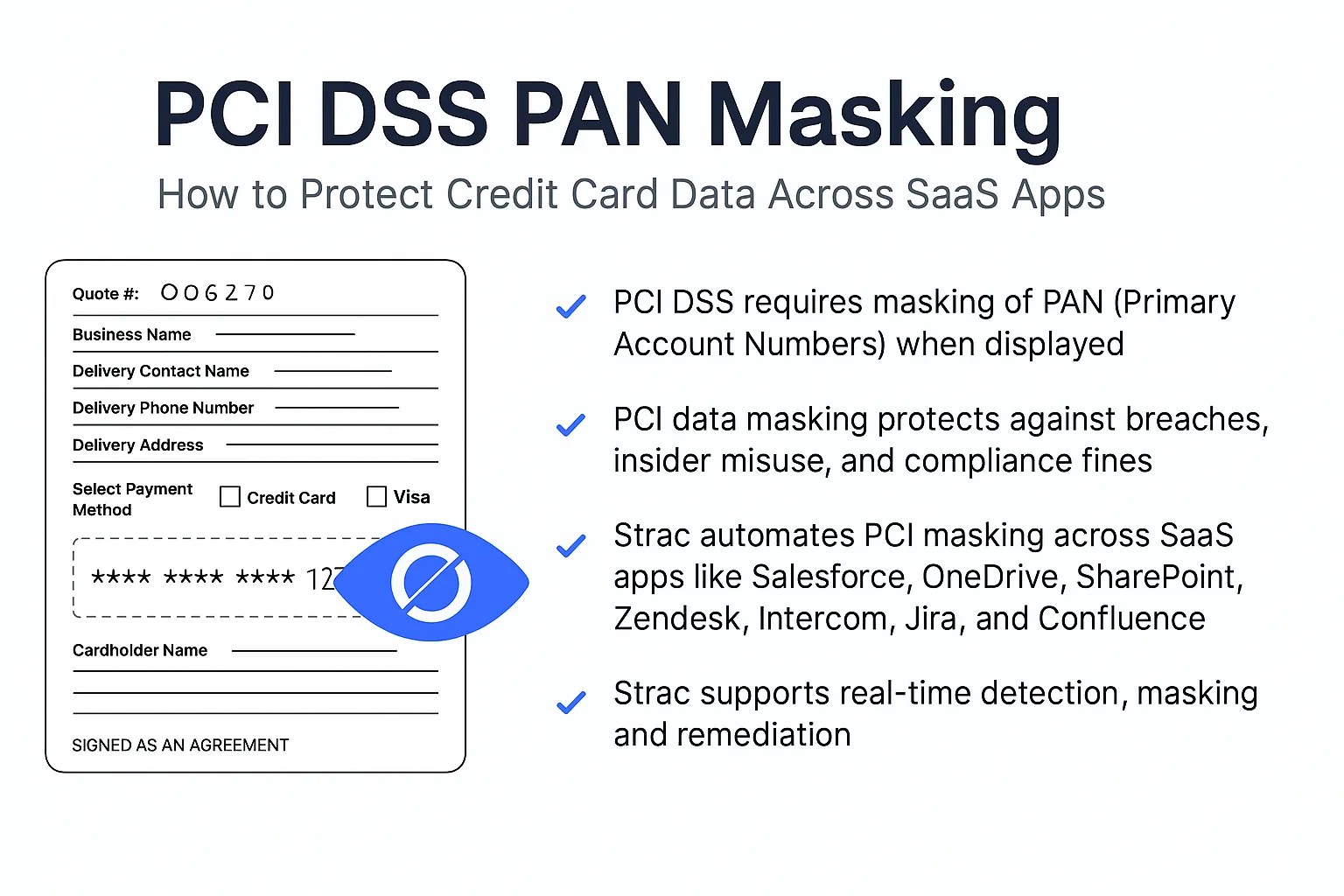
- PCI: Payment Card data such as PANs, cardholder names, and CVV.
- Encryption at rest/in transit: Protecting data stored on disk and data moving over networks.
- Shadow IT: Unapproved apps or services where data may be stored or shared outside governance.
- Data classification: Categorizing data by sensitivity to drive policy.
- Redaction vs Deletion: Redaction removes or masks sensitive elements within content, deletion removes the content entirely.

Why Data Security Matters
1) Breach risk and business impact
Breaches lead to immediate costs and long term consequences. Financial loss, operational downtime, regulatory penalties, and reputational damage compound quickly. Strong data security lowers the probability and impact of incidents by detecting and blocking risky events early.
2) Compliance requirements
Frameworks and regulations such as NIST, ISO 27001, HIPAA, PCI DSS, SOC 2, and GDPR require robust controls and proof of enforcement. Data security controls, auditing, and reporting are essential to pass assessments and avoid fines.
3) Expanding attack surface
Modern environments distribute data across cloud storage, SaaS apps, tickets, chats, code repos, wikis, analytics tools, and GenAI assistants. The more places data lives, the more ways it can leak. A modern posture must span endpoints, cloud, and SaaS with centralized visibility and automated remediation.
Core Components of Data Security
Data security is built on a multi-layered foundation of technologies, policies, and practices designed to protect sensitive information from unauthorized access, corruption, or loss. The following are the key components of a strong data security framework:
Core components of data security
Data security is a layered practice. Your mix should reflect where your data lives, who needs it, and which regulations apply. Use the components below as a checklist to design a balanced program.
Authentication
Verify the identity of users and services before granting access. Methods include passwords, MFA, hardware tokens, passkeys, and biometrics.
Authorization and least privilege
Grant only the permissions required to perform a task, and review them regularly. Role-based and attribute-based controls reduce blast radius from mistakes and misuse.
Data classification and tagging
Label data by sensitivity and context so the right controls follow it everywhere. Classifications typically include public, internal, confidential, and regulated categories.
How Strac helps: automated discovery and classification across SaaS, cloud, and endpoints, feeding policy and remediation.
Data discovery and inventory
Map where structured and unstructured data actually resides, including files, tickets, messages, and databases. This underpins every other control.
How Strac helps: agentless scanning across Slack, Google Workspace, Microsoft 365, Salesforce, AWS, and more.
Encryption at rest and in transit
Protect data using strong, well-managed cryptography. Cover disks, databases, object storage, and all network traffic. Pair with key rotation and HSM or managed KMS.
Key management
Securely generate, store, rotate, and retire keys. Restrict who can use which keys and audit every operation.
Data access governance (DAG)
Define how access is requested, approved, provisioned, and revoked. Continuously right-size permissions and remove public links or excessive sharing.
How Strac helps: revoke, quarantine, and delete actions to close exposure when risky sharing is detected.
Data loss prevention (DLP)
Detect and block sensitive data from being exposed through email, chat, uploads, and apps. The most effective programs pair detection with automatic remediation.
How Strac helps: real-time redact, mask, block, delete, and label across SaaS, browser, endpoints, and cloud.
Data security posture management (DSPM)
Continuously identify sensitive data, misconfigurations, and exposures across cloud and SaaS, then prioritize and remediate.
How Strac helps: unified DSPM plus DLP in one platform for discovery, posture assessment, and inline fixes.
Data masking and tokenization
Obscure or substitute sensitive values in non-production and analytics use cases so teams can work without handling real PII or PHI.
How Strac helps: built-in masking and redaction actions triggered by policy.
Backups and recovery
Create point-in-time copies, store them separately, test restores, and define RPO/RTO targets. Include immutable backups for ransomware resilience.
Data erasure and retention
Set policies to securely delete data when no longer needed and to meet legal holds when you must keep it.
How Strac helps: policy-based deletion and evidence to support audits.
Data resiliency and business continuity
Design for failures and disasters through redundancy, geo-replication, chaos testing, and clear runbooks so integrity and availability survive outages.
Data-centric threat detection and UEBA
Monitor data movements and user behavior for anomalies like mass downloads, unusual sharing, or sensitive content appearing in the wrong tools.
How Strac helps: ML and OCR to detect sensitive content in text, images, PDFs, code, and screenshots, reducing noise vs regex-only rules.
Monitoring, auditability, and evidence
Log access, changes, and policy actions. Produce reports that satisfy internal stakeholders and external auditors.
How Strac helps: centralized dashboard with policy actions and audit-ready trails mapped to SOC 2, HIPAA, PCI, GDPR, and ISO 27001 requirements.
Privacy by design and compliance
Bake privacy into product and process. Align with frameworks such as GDPR, CCPA, HIPAA, PCI DSS, and ISO 27001, and prove controls with documentation and tests.
How Strac helps: compliance-oriented templates and automated controls to reduce manual effort.
Coverage across modern surfaces
Ensure controls work where people actually work: SaaS suites, support tools, data warehouses, browsers, endpoints, and GenAI workflows.
How Strac helps: broad, agentless coverage with quick time to value across SaaS, cloud, endpoints, and GenAI tools.

Common Threats to Data Security
- Insider risks: Accidental oversharing, data exfiltration, or privilege misuse.
- Ransomware and malware: Encrypt or steal data for extortion and double extortion.
- Unsecured APIs and integrations: Weak authentication, overbroad scopes, or missing rate limits.
- Cloud and SaaS misconfigurations: Public links, permissive roles, open buckets, and weak default settings.
- Shadow IT and unsanctioned tools: Data lands in places without governance or visibility.
- GenAI data leakage: Sensitive prompts, outputs, or training data exposure through AI tools.
Strac’s Role in Data Security
Strac is a next generation data security platform for enterprises that need real time visibility and fast remediation across SaaS, cloud, and GenAI. It unifies data discovery, classification, DLP, and automated remediation so security teams can protect sensitive data without slowing the business.

Sensitive Data Detection
- Broad coverage: Scans apps like Gmail, Slack, Zendesk, Salesforce, Google Drive, Confluence, Jira, Notion, and cloud stores for PII, PHI, PCI, secrets, keys, and source code.
- Accurate classification: Pattern, dictionary, and ML models identify sensitive data with high precision.
- Data maps: Always up to date maps show where sensitive data lives and who can access it.
Automated Remediation
- In place fixes: Redact, delete, unshare, revoke public links, or adjust permissions directly in the source system.
- Playbooks: Define actions by severity and context to drive consistent outcomes.
- Time to fix: Reduce dwell time by turning findings into automated remediation within minutes.
Real Time Alerts and Dashboards
- Prioritized alerts: Route critical exposures with full context to the right responders.
- Dashboards: Track exposure trends, top risky apps, and recurring misconfigurations.
- Compliance reporting: Exportable evidence for audits and board updates.
Compliance Driven Controls
- Standards alignment: Supports HIPAA, PCI DSS, SOC 2, and GDPR by enforcing classification, access control, logging, and policy based remediation.
- Policy templates: Start with prebuilt rulesets and adapt them to your environment.
Bonus: Strac goes beyond text
- OCR for screenshots and PDFs: Detect PII, PHI, and PCI in images, dashboards, and scanned docs.
- GenAI visibility: Monitor and govern what users paste into tools like ChatGPT to prevent leaks and enforce redaction.
Outcome: Strac helps enterprises go from knowing about risks to fixing them quickly, turning data security from a backlog of alerts into measurable reductions in exposure.

Industries That Benefit from Strac
- Healthcare: Protect PHI, control ePHI in SaaS, and document safeguards for HIPAA.
- Fintech and Financial Services: Enforce PCI DSS for card data, support SOC 2 controls, and prevent data exfiltration from trading, lending, or payments systems.
- SaaS and Technology: Govern customer data across product, support, engineering, and GTM stacks.
- Retail and eCommerce: Secure customer PII and payment data across order systems, help desks, and marketing platforms.
- Professional Services: Control client data spread across collaboration suites and project tools.
- Education and Nonprofit: Safeguard student or donor data in shared drives and ticketing systems.
Data Security Controls: Practical Examples
- Encryption
- Enable server side encryption on object stores and databases.
- Enforce TLS 1.2+ between services and for user access.
- Identity and Access
- Use SSO with MFA for every SaaS.
- Adopt least privilege roles and time bound access for admins.
- Review and remove dormant accounts monthly.
- Data Classification
- Label PII, PHI, PCI, confidential, and public data.
- Map labels to policies that control sharing and export.
- DLP and Remediation
- Detect PANs, SSNs, keys, and secrets in chat, tickets, docs, and repos.
- Auto redact or block external sharing for high risk matches.
- Monitoring and Response
- Send high severity events to SIEM or ticketing.
- Track time to detect and time to remediate as primary KPIs.
- Secure Development and DevOps
- Scan repos and pipelines for secrets.
- Restrict access to production data and use masked datasets in non prod.
- Employee Training
- Teach safe sharing, classification, and phishing awareness.
- Reinforce with just in time prompts inside tools.
How Strac Helps With Compliance
- HIPAA: Discover and protect PHI across email, chat, and file shares. Enforce minimum necessary access and log all access events.
- PCI DSS: Find and remediate card data in SaaS, tickets, and logs. Mask or delete where needed. Prove continuous controls.
- SOC 2: Demonstrate logical access management, change management, and incident response with dashboards and audit trails.
- GDPR: Support data minimization, access governance, and right to erasure with precise search and remediation workflows.

Best Practices for Strong Data Security
- Classify sensitive data at the source
- Define categories, labels, and owners.
- Automate classification wherever possible.
- Use least privilege access
- Start with deny and grant minimal rights.
- Review access quarterly and automate revocation.
- Automate detection and remediation
- Pair continuous discovery with policies that fix issues immediately.
- Measure time to fix and exposure time, not just number of alerts.
- Train employees on secure data handling
- Provide role based training with clear, practical examples.
- Bake guidance into tools with inline prompts and templates.
- Audit and monitor continuously
- Centralize logs and alerts.
- Run routine posture reviews for SaaS, cloud, and data sharing.
- Secure GenAI usage
- Monitor prompts and outputs for sensitive content.
- Redact or block before data leaves your boundary.
How to Secure Sensitive Data: A Step by Step Approach
- Inventory and classify
- Build a real time data map across SaaS, cloud, and endpoints.
- Label PII, PHI, PCI, and confidential data with owners.
- Harden access
- Enforce SSO, MFA, and device posture checks.
- Adopt least privilege roles and session timeouts.
- Detect and govern sharing
- Set policies for external sharing, public links, and guest access.
- Use DLP to detect sensitive strings and context across apps.
- Automate remediation
- Redact or delete sensitive content in place.
- Revoke public links and adjust permissions automatically.
- Measure and improve
- Track exposure trends, top risky apps, and repeat offenders.
- Report on time to detection, time to remediation, and percent of issues auto remediated.
Where Strac fits: Strac accelerates this entire motion with agentless integrations, accurate detection, and one click or automated fixes that happen inside the source systems.

Data Security Frameworks to Guide Your Program
- NIST Cybersecurity Framework: Identify, Protect, Detect, Respond, Recover. Map controls and metrics to these functions.
- ISO 27001: Establish, implement, and improve an information security management system with risk based controls and continuous audits.
- CIS Controls: Pragmatic set of prioritized actions, including inventory, access control, and data protection basics.
Use frameworks to shape policy and evidence. Use platforms like Strac to operationalize and automate enforcement across your stack.
In Summary
Data security is not a single tool. It is a continuous practice that combines classification, access control, encryption, monitoring, and fast remediation. As data spreads across cloud, SaaS, and GenAI, the difference between a small incident and a headline often comes down to how quickly you can find and fix exposures. Strac helps you do exactly that by discovering sensitive data in real time, mapping where it lives, and remediating risk directly in the tools your teams use every day. Strong data security protects your customers, your brand, and your business momentum.
🌶️Spicy FAQs
1) What is data security in simple terms, and how do I explain it to my execs?
Data security means only the right people can access the right data for the right reason, and any misuse gets caught and fixed quickly. For the board, frame it as reducing financial, legal, and operational risk from data exposure while enabling the business to move faster.
Use this one-liner: “We protect sensitive data everywhere it lives and automate fixes when something slips.”
Back it with three numbers:
- Time to detect
- Time to remediate
- % of incidents auto-remediated
2) Which threats should I prioritize in 2025 and why?
Focus on the risks that happen daily, not just the headlines. Most real incidents start with simple oversharing or weak access, not elite zero-days.
Top five to prioritize:
- Public file links and guest sharing in SaaS
- Overprivileged accounts and stale access
- Sensitive data in tickets, chats, wikis, and logs
- Secrets and keys in code repos and CI logs
- GenAI prompt and output leakage
Win fast: kill public links at scale, enforce least privilege, and auto-redact sensitive strings in high-velocity systems like Slack, Gmail, Zendesk, and Jira.
3) What are practical examples of data security controls that actually move the needle?
Controls only matter if they shrink exposure time. Pair policy with automation.
- Encryption: at rest and in transit as table stakes, with centralized key management.
- Access control: SSO, MFA, least privilege, time-bound admin access.
- Classification + DLP: detect PII, PHI, PCI, secrets, and source code across SaaS.
- Automated remediation: unshare, revoke, redact, or delete directly in the source app.
- Monitoring: route high-severity alerts with full context and preserve audit trails.
Proof you are maturing: month over month reduction in public links, sensitive messages redacted, and dormant admin accounts removed.
4) Data protection vs data security: which do I invest in first?
Think sequence, not silos. You need both, but the order matters.
- Start with security to stop live leaks: access control, classification, DLP, remediation.
- Layer protection for resilience: backups, disaster recovery, legal holds, privacy workflows.
- Tie it together with governance: owners, labels, retention, and consistent policy across tools.
Decision check: if you cannot quickly find and fix a live exposure in Slack or Google Drive, increase security automation first. If you already can, invest next in backup and privacy operations.
5) How does Strac improve our data security and compliance without slowing teams down?
Strac discovers sensitive data in the tools your teams already use and fixes issues in place, so you reduce risk without changing how people work.
- Sensitive Data Detection: maps PII, PHI, PCI, secrets, and code across Gmail, Slack, Google Drive, Salesforce, Jira, Notion, and more.
- Automated Remediation: redacts, deletes, unshares, and revokes public links inside source systems.
- Real-Time Alerts: prioritizes incidents with context, not noise.
- Compliance Evidence: HIPAA, PCI DSS, SOC 2, and GDPR reporting with exportable proofs.
- Bonus: OCR finds leaks hidden in screenshots and PDFs from dashboards and code editors.
Outcome your execs care about: faster time to fix, fewer open exposures, smoother audits.
.avif)
.avif)
.avif)
.avif)
.avif)
Discover & Protect Data on SaaS, Cloud, Generative AI















.webp)














.webp)

.webp)






.gif)
