How to Secure Sensitive Data in AWS S3
Explore AWS S3 security concerns & best practices. Learn how to protect your data in the cloud, enhance compliance & respond to potential breaches effectively.
Amazon S3's widespread adoption as a cloud storage solution makes it a prime target for data breaches. High-profile incidents like the Capital One breach highlight the inherent vulnerabilities of improperly secured S3 buckets. In this case, a simple misconfiguration exposed 100 million credit card applications and resulted in an $80 million penalty. Organizations must carefully explore various security measures and implement recommended protocols to protect their data in Amazon S3.

Amazon Web Services (AWS) Simple Storage Service (S3) is a cloud-based storage service that provides a simple and scalable way to store, retrieve, and manage data. It is a popular choice for storing a wide variety of data, including websites, images, videos, and backups.
However, like any cloud-based service, AWS S3 is not without its security concerns. Here are some of the most common ones:
If the permissions on your AWS S3 buckets are not configured correctly, it could allow unauthorized users to access or modify your data.
Two significant incidents involving misconfigured S3 buckets:
Inadequate encryption practices also pose a risk by leaving sensitive information vulnerable to interception and unauthorized access during storage or transmission.
Incorrectly configured access control rules might grant unwanted access to individuals or roles, potentially resulting in data breaches.
Failure to monitor API activity for irregular or unauthorized access might expose the bucket to security attacks.
Mismanagement of encryption keys can make data unavailable or, in the worst-case scenario, expose data.
Related: A Complete Guide to Credential Exposure: Causes & Prevention
Ensuring the security of your Amazon S3 buckets is crucial to safeguard sensitive data, maintain privacy, and meet regulatory requirements. Here are some recommended best practices for securing your AWS S3 buckets.

When using Amazon Web Services (AWS), you can apply Bucket and IAM Policies to control access to your resources. Bucket Policies are JSON-formatted documents attached directly to an S3 bucket, allowing you to specify which actions are permitted or denied by which users or groups.
IAM Policies, on the other hand, are attached to IAM users, groups, or roles and define permissions across all of your AWS resources. Both types of policies help ensure secure and controlled access to your data.
Properly defining and regularly reviewing bucket and IAM policies ensures only authorized entities have the appropriate access, minimizing the chances of data exposure or unauthorized entry.
The S3 bucket logging feature captures detailed information about every request made to your S3 bucket, including the requester, bucket name, request time, action taken, response status, and any error codes encountered. This valuable tool allows you to monitor access, track usage patterns, and identify suspicious activities.
By enabling AWS S3 server access logging, you can ensure comprehensive records of all requests made to your S3 bucket. Without access logs, it can be challenging to detect unauthorized access or other malicious activities, which could hinder your ability to respond to security incidents.
Access logs are essential for detecting and responding to unauthorized access or other malicious activities that could compromise the security of your system. Without them, you may not be aware of potential security incidents until it's too late.

The versioning feature in S3 ensures that multiple versions of an object are stored in a bucket, enabling you to safeguard, access, and recover each version. If versioning is not enabled, unintended overwrites or deletions may lead to data loss.
Versioning is an important feature that helps protect against accidental or malicious changes and deletions, ensuring the durability and recoverability of your data. It keeps multiple versions of an object in a bucket, allowing you to retrieve and restore previous versions if needed.
Even if you delete an object, S3 will retain all versions, giving you peace of mind knowing that you can always recover from unintended user actions or application failures.
Multi-factor authentication (MFA) is a security feature that adds an extra layer of protection by requiring multiple verification forms before allowing certain actions, such as deleting a versioned bucket. Without MFA, a hacker with stolen credentials could delete important S3 buckets without the ability to retrieve them.
Implementing MFA for crucial actions such as deleting buckets helps to prevent unauthorized access. It ensures that even if credentials are compromised, an extra layer of verification is required for high-risk actions.
Data encryption at rest and in transit are two important security measures for protecting data stored in S3. While the former safeguards data while it is stored, the latter protects it as it is transmitted. Without these measures, sensitive information could be easily accessed or intercepted by unauthorized parties.
Encryption at rest protects unauthorized access in case the storage is compromised. With SSE-S3, Amazon handles encryption, decryption, and key management.
Encryption in transit guarantees that your data remains secure as it travels between your client and S3. With HTTPS, you can effectively safeguard your data during transit.
Regular audits, such as utilizing AWS Trusted Advisor, are crucial in upholding a secure configuration, identifying potential vulnerabilities, and guaranteeing compliance with industry standards. These audits pinpoint misconfigurations and excessively permissive policies while ensuring adherence to best practices.
Neglecting regular audits could leave you oblivious to potential vulnerabilities or misconfigurations, thereby heightening the chances of unauthorized access or data exposure.
AWS Trusted Advisor is a valuable tool that offers real-time advice and guidance for provisioning AWS resources according to best practices. By regularly auditing S3 buckets, it helps identify potential issues such as misconfigurations and overly permissive policies, ensuring compliance with industry standards.
Preventing public access to your S3 data is a must. One way to do this is by using signed URLs, which provide temporary and secure access to private objects. Allowing public access can make sensitive data vulnerable to cyber attacks and breaches. Additionally, having overly permissive access controls can lead to unauthorized users gaining access to your data. It's important to carefully manage and restrict public access to protect your private information.
With AWS S3 Block Public Access, you can block public access to your S3 data. This means that only authorized entities will have access, reducing the risk of data breaches and unauthorized access. By not making your buckets public, you can prevent sensitive data from being exposed to the internet and potentially avoid a data breach.
Additionally, using pre-signed URLs allows you to provide temporary and secure access to private objects in your S3 storage. This adds an extra layer of control over who can access private objects.
AWS Macie is a comprehensive data security and privacy solution that leverages machine learning and pattern-matching technology to identify and safeguard sensitive data, such as Personally Identifiable Information (PII).
Macie is a useful tool for monitoring S3 buckets. It can automatically scan and identify sensitive data, giving detailed visibility into its access and movement. This helps with complying with data privacy regulations by alerting you to any potential risks or unauthorized access, as well as detecting data leaks.
S3 Object Lock is a feature that allows you to protect your objects in AWS S3 from being deleted or overwritten. This can be done for a specific period or indefinitely. To use this feature, you must enable Object Lock at the bucket level and apply retention policies to individual objects. Alternatively, you can set a default retention period for all objects in the bucket.
By implementing S3 Object Lock and retention policies, you ensure your data remains immutable and safe from accidental deletions or malicious alterations. This provides a write-once, read-many (WORM) protection for your objects.
Additionally, it offers numerous benefits, such as improved data integrity and security, protection against ransomware attacks and accidental data loss, and adherence to legal and regulatory data retention requirements.

AWS WAF is a powerful tool that shields your S3 buckets from common web vulnerabilities, ensuring the availability of your applications, maintaining security, and preventing resource overload.
AWS WAF offers comprehensive protection against DDoS attacks at both the infrastructure and application layers for your S3 buckets. To establish a secure content delivery network (CDN) for your S3 bucket, combine AWS WAF with Amazon Cloud Front. Furthermore, you can enable AWS Shield (Standard or Advanced) to safeguard all your AWS resources, including S3, from DDoS attacks based on your specific requirements.
Data Loss Prevention (DLP) is an essential aspect of protecting sensitive data stored in cloud environments such as AWS S3. This solution actively monitors data access and movement within the platform to prevent potential breaches or policy violations. It achieves this through the use of predefined or customized policies that can identify sensitive information and detect any abnormal or unauthorized activities. In case of any suspicious activity, the DLP solution will generate real-time alerts for immediate action to be taken.
With a real-time alert system, you can quickly identify potential data breaches to minimize their impact on your organization. This also helps ensure compliance with data protection regulations by continuously monitoring and protecting sensitive information.
Related: A Complete Guide to Cloud Data Loss Prevention
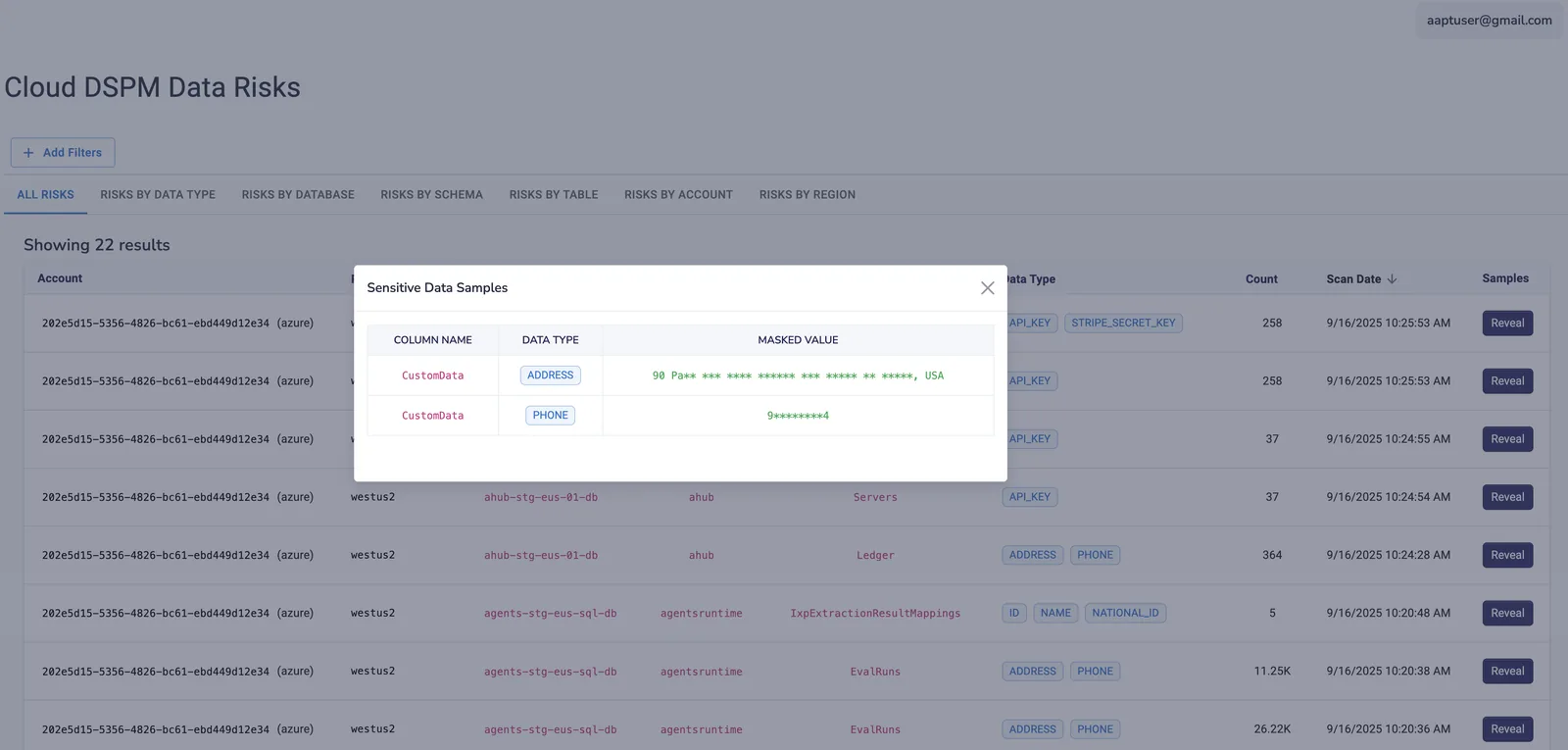
Strac protects AWS S3 by automatically discovering and classifying sensitive data across buckets; giving you full visibility into what data you have and where it lives. It continuously monitors access and usage; detecting risky behavior, misconfigurations, and potential leaks in real time. And when issues are found, Strac doesn’t just alert; it takes action with automated remediation like redaction, blocking, and encryption to stop exposure instantly.


.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

