Top 11 Forcepoint Alternatives & Competitors in 2026
Explore the best alternatives to Forcepoint in 2026 exceeding Forcepoint in features, efficiency, and user reviews.
Navigating the cybersecurity landscape can be challenging, especially when popular solutions like Forcepoint present challenges. Many enterprises are now seeking alternatives that better align with their unique needs.
Though Forcepoint is a popular tool in the DLP field, it has limitations such as a difficult UI, deployment and performance issues.
This article delves into the top Forcepoint alternatives for 2026, providing insights into solutions that offer enhanced flexibility and integration capabilities to better meet diverse organizational needs. Let's explore the leading competitors and their unique offerings in the cybersecurity arena.

Forcepoint DLP is one of the most established enterprise data protection platforms, known for its broad set of traditional DLP controls. Forcepoint combines endpoint agents, network monitoring, and policy-based detection to help organizations manage risk across on-premise and cloud environments. While powerful for large enterprises with legacy infrastructure, its architecture still relies heavily on agents and rule-based policies, which can make deployment slow and maintenance heavy.
Endpoint DLP Coverage: Forcepoint provides deep endpoint monitoring using heavy agents that track data movement across USB, network transfers, print operations, and local file activity.
Network DLP & CASB: It includes network inspection and CASB-like capabilities designed to monitor and control data traveling between corporate systems and cloud applications.
Policy-Based Detection: The platform uses predefined DLP policies, regex-based pattern matching, and rule-heavy configurations to identify sensitive data exposures.
Encryption & Device Control: Forcepoint supports full-disk encryption, email encryption, and device controls (USB, removable media).
Incident Management & Forensics: Includes dashboards for alert review, incident triage, and long-form forensic analysis used by large, security-mature enterprises.
Forcepoint’s feature set is built for large, traditional enterprises that have:
But today’s SaaS-first and AI-enabled companies often need faster deployment, lower friction, and broader coverage across SaaS, GenAI, and cloud stores; areas where agent-based legacy tools struggle.
Complex setup and usability
The UI is not intuitive, and deployment takes time. Teams often need significant effort to configure policies correctly, slowing time to value.
Limited visibility into user behavior
Strong on enforcement, but weak on monitoring. UEBA capabilities are basic, making it harder to detect insider threats or risky user activity.
High cost and integration friction
Advanced features often require add-ons, increasing total cost. Integrations can be complex and slow to implement in real environments.
No remote response control
Lacks remote desktop or deep response capabilities, which limits how teams investigate and respond to incidents.
Weak forensic depth
Basic logging and screenshots exist, but audit trails and forensic analysis are not comprehensive enough for complex investigations.
Bottom line
Forcepoint works for traditional DLP use cases, but falls short for modern environments that need fast deployment, deep visibility, and real-time action.
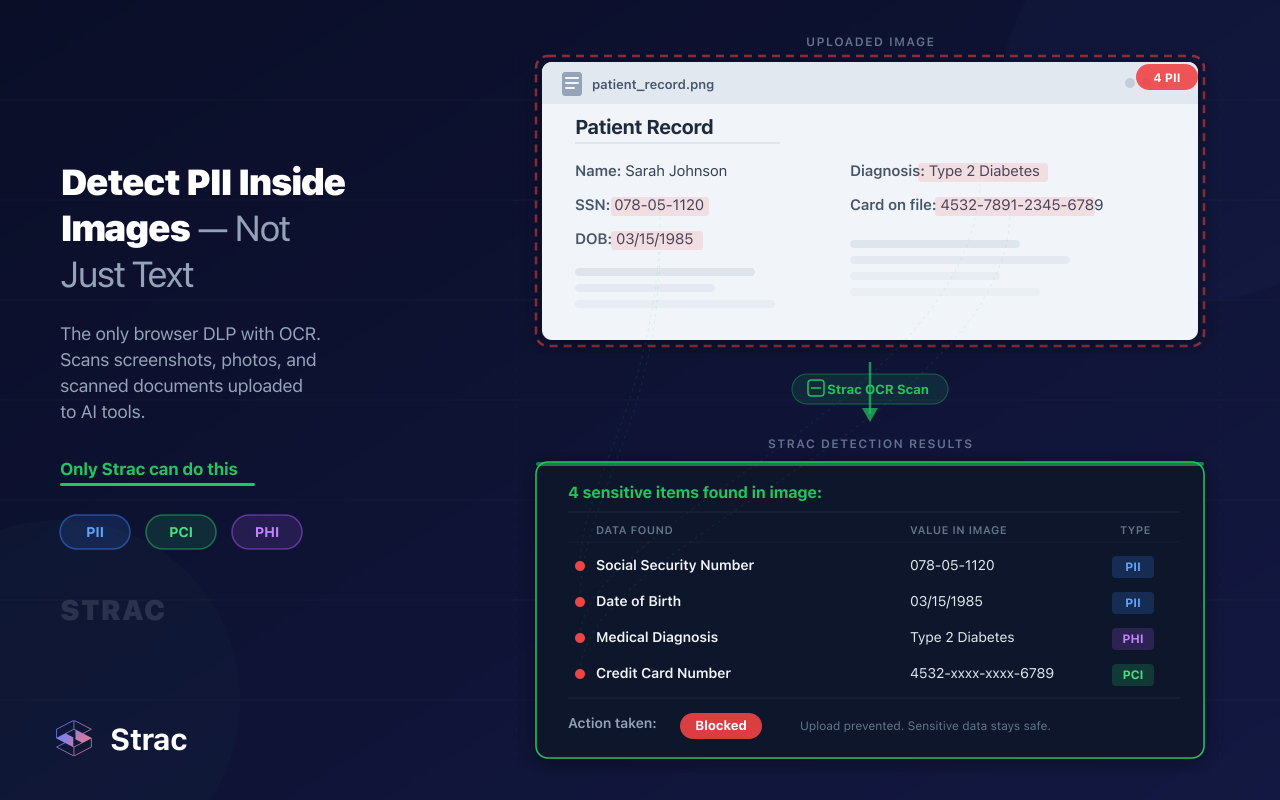
Strac delivers a fundamentally modern approach to DLP: fully agentless, real-time, ML-powered, and purpose-built for SaaS, cloud, Endpoints, and AI environments. Instead of depending on complex rule-writing or slow endpoint deployments, Strac protects data instantly across the tools companies actually use today.

Strac stands out because it is built for today’s world—SaaS-native, cloud-native, AI-native, and high-velocity, whereas legacy DLP tools were designed for a perimeter that no longer exists.
Forcepoint is a well-known player in the cybersecurity arena, offering a complete suite of solutions to protect businesses against digital attacks.
Unfortunately, Forcepoint has limitations such as,

For these reasons, many enterprises are now looking for alternative solutions that meet their unique requirements better.
Let’s look at the best possible alternatives to Forcepoint.
⭐Rated 5/5 on g2
Strac is an end-to-end data loss prevention & cloud access security broker software for all SaaS and Cloud apps that safeguards businesses from security and compliance risks with its robust features. It ensures that your confidential information remains secure throughout the entire process.



Check out how they are used to protect their AI or LLM apps and also to safeguard their sensitive data ➡️ Strac Developer Documentation.
.webp)
Check out Strac’s full catalog of sensitive data elements.
Invoicing was manual initially, but Strac has now made invoices available online.
Strac provides multiple pricing options for teams of all sizes. It also offers a free 30-day trial. Connect with the team for further information.


⭐Rated 4.4/ 5 on g2
Symantec Endpoint Protection (SEP) offers unrivaled protection against various malware attacks. This multi-layered approach incorporates essential and next-gen technologies, creating a powerful fusion that delivers superior protection. Managing SEP is easy due to its high performance, lightweight nature, and single client and management console, allowing users to oversee physical and virtual protection. SEP's orchestrated response to evolving threats is delivered at scale for maximum security.

Contact Symantec’s enterprise sales team for pricing information.

⭐Rated 4.8/5 on g2
Check Point Data Loss Prevention (DLP) is a platform designed to protect against the unintentional loss of sensitive data. It combines technology and processes to prevent data from leaving your organization without authorization. This helps to ensure that only approved users can access confidential information.
Check Point DLP utilizes Check Point Infinity Architecture for easy deployment and management. Additionally, it educates users on proper data handling policies. They handle information securely and remediate real-time incidents whenever unauthorized access is detected.
Contact the CheckPoint team for further information on pricing.

⭐Rated 4.4 / 5 on g2
Endpoint Protector is a Data Loss Prevention (DLP) solution that provides businesses of all sizes and industries with Intellectual Property Protection, Personal Identifiable Information Protection, and Insider Threat Protection.
With its advanced cross-platform capabilities for macOS, Windows, and Linux computers, as well as enforced encryption for USB storage devices, Endpoint Protector can help organizations achieve compliance while meeting data protection regulations like GDPR, HIPAA, PCI-DSS, CCPA, LGPD, TISAX, and KRITIS.

Contact the Endpoint team for further information on pricing.

⭐Rated 4.5/5 on G2
Microsoft Purview Data Loss Prevention is part of the broader Microsoft security and compliance ecosystem. It helps organizations identify, monitor, and protect sensitive information across Microsoft 365 services such as Exchange, SharePoint, OneDrive, and Teams.
Microsoft Purview DLP is particularly popular among enterprises already deeply embedded in the Microsoft stack. It provides built-in compliance templates and policy controls designed to help meet regulatory requirements.
Pricing varies based on Microsoft 365 licensing tiers. Contact Microsoft for detailed enterprise pricing.
⭐Rated 4.4 / 5 on g2
Netskope is a cloud security platform offering businesses comprehensive digital environment protection. As the leading provider of cloud-native solutions, Netskope provides visibility, real-time data and threat protection, and granular control across SaaS, IaaS, and web traffic. Our suite of features includes Cloud Access Security Broker (CASB), Data Loss Prevention (DLP), and Advanced Threat Protection (ATP) so that you can safely navigate the modern digital landscape.

Contact the Netskope team for further information on pricing.

⭐Rated 4.8/5 on Gartner peer
Cyberhaven is a cutting-edge data loss prevention (DLP) solution that takes an innovative approach to identifying and categorizing sensitive data. It helps prevent insider threats and account takeovers, tracing every aspect of a company's data access, usage, and movement. Cyberhaven also makes it easy to define security policies with its visual policy editor, allowing users to test their policies on historical data before enforcing them.

Contact the Cyberhaven team for further information on pricing.

Source: Gartner Peer
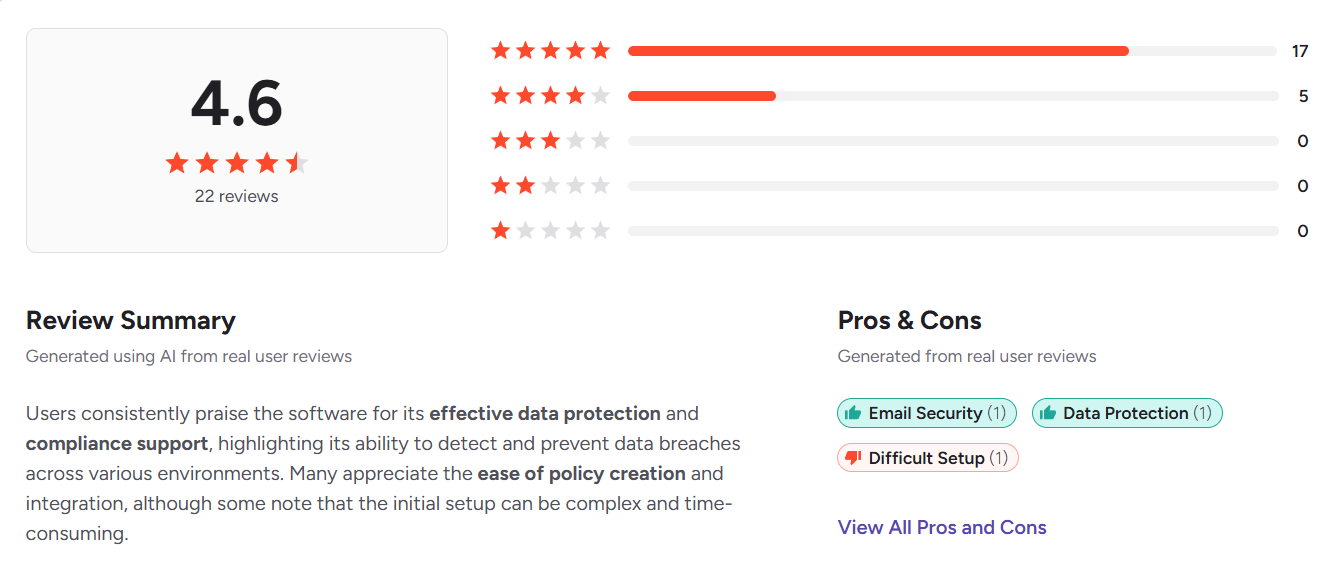
⭐Rated 4.3 / 5 on g2
Digital Guardian is a SaaS solution for Enterprise Data Loss Prevention (DLP). It offers quick deployment and on-demand scalability to protect your data.
With broader endpoint OS coverage, persistent data protection, optimized policy creation, and 24/7 customer support for rapid response, Digital Guardian provides great security. You can also easily migrate your existing policies to Digital Guardian and track the movement of sensitive data to develop better policies for enhanced security.
Contact the Digital Guardian team for further information on pricing.

⭐Rated 4.5/5 on g2
Teramind's Data Loss Prevention (DLP) solution effectively protects against data breaches, data leaks, and IP theft. This solution provides data visibility and control, auto-discovery and classification of sensitive data. It also offers flexible deployment options, such as on-premise or in the cloud, and actionable workforce insights that reduce risk and streamline business operations.

Contact the Teramind team for further information on pricing.

⭐Rated 4.6/5 on g2
Trend Micro Cloud One is a comprehensive security services platform for cloud builders designed to secure hybrid and multi-cloud environments. It offers solutions in Hybrid cloud security, network defense, user protection, cloud migration, cloud-native app development, and operational excellence. Its integrated DLP solution provides visibility and control of data to meet compliance standards easily.

Contact the Trend Micro team for further information on pricing.

⭐Rated 4.3/5 on G2

Trellix DLP is a data protection solution designed to prevent unauthorized access, transmission, or sharing of sensitive information. It employs advanced techniques such as content inspection, data fingerprinting, and keyword matching to safeguard various types of sensitive data.
Pricing details for Trellix DLP are generally available upon request from the vendor. It is advisable for organizations to contact Trellix directly for a fitted quote based on their precise requirements.
Trellix DLP has received positive feedback on G2, with users appreciating its comprehensive protection capabilities but noting areas for improvement in monitoring channels and analytics features. Users rate it favorably for its ease of use but highlight the need for more advanced features in certain aspects of data protection.

This table provides a complete overview of the top alternatives to Forcepoint in the data loss prevention space.
| Tool | Rating (G2) | Key Features | Pros | Cons | Pricing |
| Strac | ⭐5/5 | - DLP for SaaS, Cloud & Gen AI
- Automatic sensitive data detection and redaction - Integrations with popular apps |
- Ease of integration
- Accurate detection - Extensive SaaS integrations |
- Manual invoicing initially | Free 30-day trial; contact for details |
| Symantec Endpoint Protection (SEP) | ⭐4.4/5 | - Application security
- Device management - Web threat management |
- Immediate threat blocking
- Comprehensive web protection |
- Multiple push notifications
- High resource utilization |
Contact for pricing |
| Check Point DLP | ⭐4.8/5 | - Centralized management
- Incident response - Granular policy setting |
- Complete visibility over sensitive data
- Multi-layered protection |
- Focus on network layer can slow server performance
- Limited third-party compatibility |
Contact for pricing |
| Endpoint Protector | ⭐4.4/5 | - Cross-platform collaboration
- Data blocking - Enforced encryption |
- Data safety in transit and at rest
- Professional sales and support |
- High licensing cost for smaller organizations
- Steep learning curve |
Contact for pricing |
| Nightfall | ⭐4.6/5 | - Integration with cloud tools
- Proactive alerts - Automatic remediation |
- Effective onboarding
- Ease of installation |
- Can produce false positives
- Limited support for IM applications |
Contact for pricing |
| Netskope | ⭐4.4/5 | - Advanced threat protection
- Granular visibility & control - Zero Trust Network Access |
- Strong product functionality
- Comprehensive services expertise |
- Difficult integration with security tools
- Complex setup |
Contact for pricing |
| Cyberhaven | ⭐4.8/5 | - Real-time data tracking
- Visual data mapping - Policy editor |
- User-friendly interface
- Extensive customization options |
- Limited support for Linux
- Minimal integrations available |
Contact for pricing |
| Digital Guardian | ⭐4.3/5 | - Reliable data protection
- Analytics tools - Customized policy setups |
- Intuitive design
- Compatible with Windows and Mac |
- Complex initial setup
- Resource-intensive |
Contact for pricing |
| Teramind | ⭐4.5/5 | - User activity tracking
- Insider threat identification - Flexible deployment options |
- Intuitive user experience
- Real-time team activity insights |
- Does not support Linux
- High cost |
Contact for pricing |
| Trend Micro | ⭐4.6/5 | - Visibility into cloud environments
- Integrated DLP solution - Simple online interface |
- Real-time dashboard alerts
- In-depth reporting capabilities |
- GUI improvements needed | Contact for pricing |
| Trellix DLP | ⭐4.3/5 | - Centralized monitoring
- Incident management - Multi-channel protection |
- Comprehensive protection
- User-friendly interface |
- Limited monitoring channels
- No geolocation tracking - Absence of dedicated UEBA |
Contact for tailored quote |
Consider the below questions when evaluating DLP solutions:
In conclusion, the above questions can help you choose the ideal DLP solution for your organization.
With powerful platforms like Strac, you can ensure a secure digital environment and protect against data breaches, unauthorized access, and compliance issues. Ready to get started?
Schedule a demo with Strac now.
Many teams start with Forcepoint DLP and only realize they have outgrown it when daily work begins to feel slowed down by the tool itself. When you are exploring Forcepoint alternatives, you are usually feeling pain around agents, rule complexity, and gaps across modern SaaS tools. The most obvious signals show up in deployment time, noise levels, and limited visibility into where data really lives.
Key red flags that you have outgrown Forcepoint DLP:
If these patterns feel familiar, it is usually the moment to seriously evaluate modern Forcepoint alternatives that are SaaS native, agentless, and focused on real time remediation instead of rule firefighting. Moving to a lighter platform frees your team from maintenance work and lets them focus on real risk reduction instead of wrestling the tool.
Modern AI driven DLP tools are built for a world of SaaS, APIs, and GenAI; legacy platforms like Forcepoint DLP were designed for a world of LANs, VPNs, and file servers. When you compare them side by side, the biggest differences appear in how they detect sensitive data and how they act on it in real time. AI powered platforms shift from rule heavy detection to content aware, context rich decisions that match how people actually work.
Key differences between AI-driven DLP and legacy Forcepoint style DLP:
The result is that AI driven DLP tools feel lighter, more accurate, and more aligned with how modern teams communicate and collaborate. For organizations evaluating Forcepoint alternatives, this jump in usability and intelligence is often the deciding factor.
When security teams compare Forcepoint with SaaS focused DLP solutions, they are really comparing two generations of technology. One is built around endpoints and networks; the other is built around SaaS, APIs, and AI usage. To choose the right Forcepoint alternative, you need to evaluate how each platform performs across deployment, coverage, accuracy, and day to day operations.
Key evaluation criteria to compare Forcepoint vs modern SaaS DLP:
If a SaaS focused, agentless DLP solution scores better on these dimensions than Forcepoint, it is usually a strong signal that the newer architecture is a better long term fit. The right Forcepoint alternative will make security stronger and operations lighter at the same time.
SaaS and GenAI data protection are no longer nice to have features; they are at the center of modern DLP requirements. Most sensitive data now flows through collaboration apps, cloud drives, ticketing systems, and AI assistants rather than just email or local drives. When you select a Forcepoint alternative, your ability to see and control these flows is often the difference between a checkbox solution and real risk reduction.
Why SaaS and GenAI protection are critical today:
Ignoring SaaS and GenAI coverage when picking a Forcepoint alternative means protecting the old perimeter while leaving the real data layer exposed. The next DLP platform you choose should treat SaaS and AI as first class citizens, not afterthoughts.
Automated data discovery and classification change DLP from a reactive rule engine into a proactive, context aware system. Instead of guessing where sensitive data might be, the platform continuously maps where it actually is and what type it is. When you pair that map with DLP enforcement, especially in a Forcepoint alternative, you gain precision, lower noise, and more meaningful alerts.
Ways automated discovery and classification improve DLP:
When automated discovery and classification are built into your DLP platform, every policy becomes more targeted and every alert more meaningful. For organizations moving away from Forcepoint DLP, this is one of the most impactful upgrades; it lets you protect more data with fewer manual rules and dramatically less noise.
Read our other resources:
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

