Top 11 Data Loss Prevention (DLP) Software Vendors in 2026
Top 11 Data Loss Prevention (DLP) Software Vendors in 2026 (Comparison)
When companies search for DLP software vendors, they are not looking for another long comparison chart. They are trying to figure out one thing: Who will actually protect our data without slowing us down?
The problem is the market is noisy. Some vendors are heavy, agent-based, and take months to deploy. Others only send alerts but do not fix the issue. Meanwhile, sensitive data is no longer just in email. It is in Slack threads, Salesforce tickets, Google Drive files, Endpoints and AI promts.
At Strac, we built our platform around how data actually moves today. We combine DSPM and DLP in one agentless solution that discovers, classifies, and automatically redacts sensitive data in real time across SaaS, cloud, endpoints, and AI tools.
In this guide, we break down the leading types of DLP software vendors, what truly separates them, and how to evaluate them based on deployment speed, remediation depth, AI coverage, and overall practicality. If you are comparing vendors, this will help you cut through the noise and make a decision that holds up in production.
Data Loss Prevention (DLP) software detects, monitors, and protects sensitive data from unauthorized access, sharing, or exfiltration. DLP solutions identify sensitive information — such as personally identifiable information (PII), payment card data (PCI), protected health information (PHI), intellectual property, and credentials — and enforce policies to prevent data leaks.
Modern DLP solutions operate across multiple channels:

The best DLP platforms combine multiple approaches for comprehensive coverage across the entire data lifecycle.
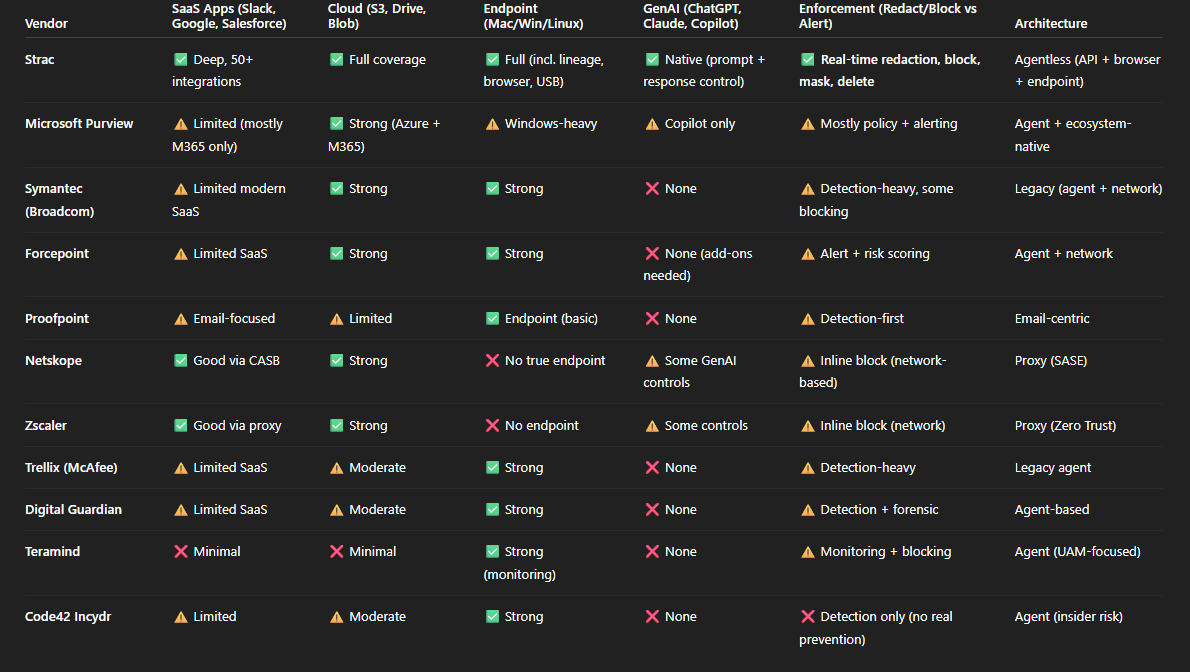
When you’re evaluating DLP software vendors, it’s easy to get distracted by feature lists and bold claims. What really matters is simple: will this tool protect your data in the way your business actually operates?
Look beyond basic detection. Does the vendor only send alerts, or can it automatically redact, block, or fix the issue? Is deployment going to take months and heavy agents, or can you get up and running quickly? And does it protect just email and endpoints, or the full SaaS stack where your data actually lives today; Slack, Salesforce, Google Drive, cloud storage, even AI tools?
The right DLP vendor should reduce risk without creating friction. In the next section, we break down exactly what to look for before making your decision.
Here are the most important elements you need to search for:
Effective DLP starts with knowing where sensitive data exists. Look for solutions that:

DLP policies define what actions are allowed or blocked. Evaluate:
DLP must act in real time to prevent breaches:
Strac Intercom DLP
Consider how the solution fits your environment:
DLP shouldn’t create friction:
Best for: Organizations needing unified DLP across SaaS, Cloud, Endpoint, and GenAI
Overview:
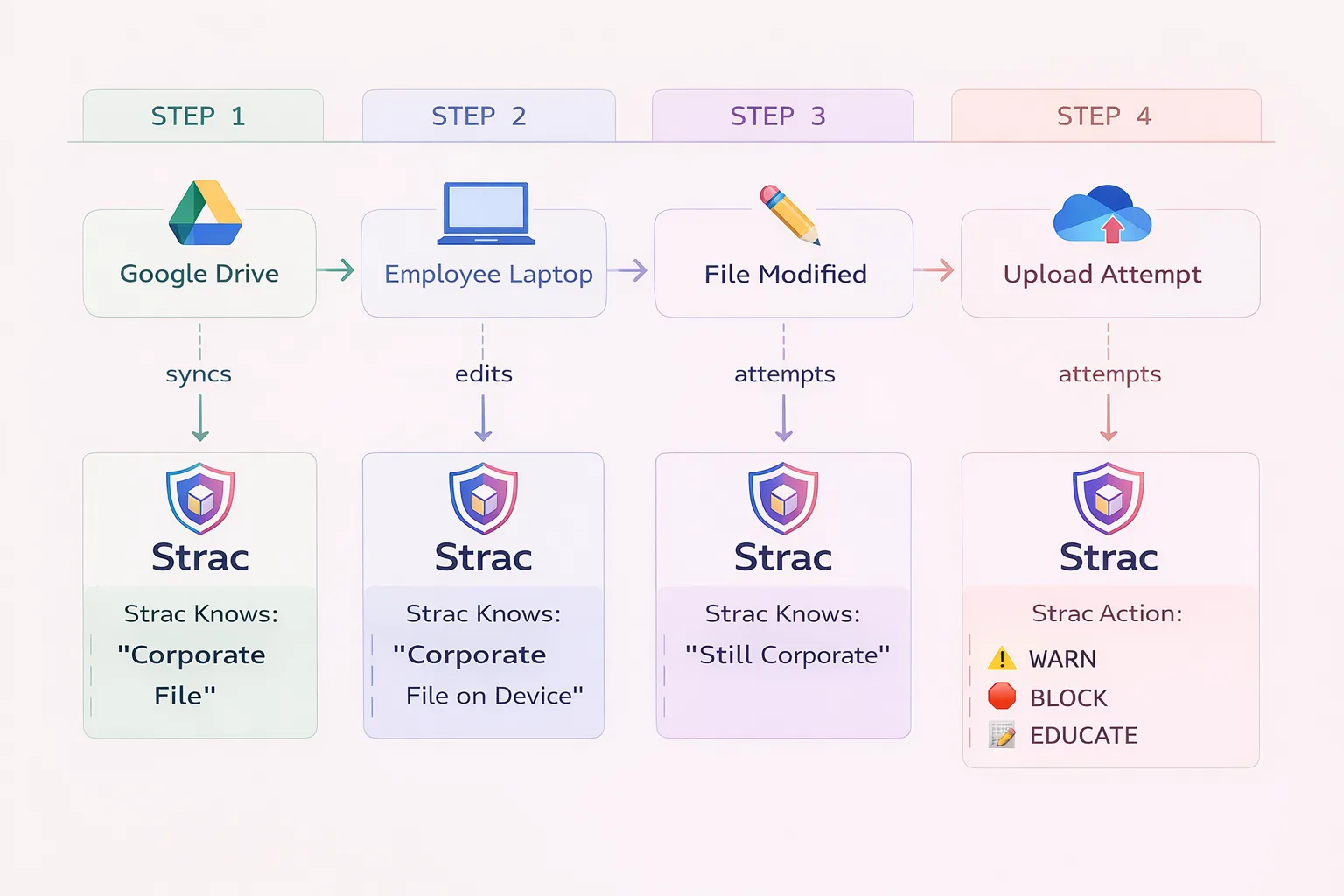
Strac is a modern, AI-native DLP platform that protects sensitive data across SaaS applications (Slack, Google Workspace, Salesforce, Zendesk), cloud storage (Google Drive, OneDrive, Box), endpoints (Mac, Windows, Linux), and GenAI tools (ChatGPT, Claude, Gemini). Unlike legacy DLP vendors that focus primarily on network or endpoint, Strac provides agentless SaaS protection with real-time detection and remediation.
Key Features:
Strac provides redaction as remediation in addition to dozen other remediation actions
Strac GenAI DLP

Pros:
Cons:
Best Use Cases:
Compliance: SOC 2 Type II, HIPAA, PCI-DSS, GDPR, ISO 27001
Best for: Large enterprises with established on-premise infrastructure
Overview:
Symantec DLP, now owned by Broadcom, is one of the oldest and most established DLP platforms. It offers comprehensive coverage across endpoint, network, storage, and cloud. Symantec is particularly strong in regulated industries that require on-premise deployment options and have dedicated security teams to manage complex policies.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: Organizations heavily invested in Microsoft 365
Overview:
Microsoft Purview (formerly Microsoft Information Protection and Compliance) provides native DLP capabilities for Microsoft 365 applications including Exchange, SharePoint, OneDrive, and Teams. For organizations already using Microsoft E5 licenses, Purview offers integrated DLP without additional vendor costs.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: Organizations prioritizing user behavior analytics
Overview:
Forcepoint DLP combines traditional content-aware DLP with user and entity behavior analytics (UEBA). This approach helps identify risky user behavior patterns, not just sensitive content. Forcepoint is strong in environments where insider threat detection is a primary concern.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: Email-centric data protection
Overview:
Proofpoint DLP evolved from the company's email security heritage, making it particularly strong at protecting data in email communications. Proofpoint offers endpoint and cloud DLP, but its differentiation is deep email content analysis and user-centric security based on attack likelihood.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: Cloud-first organizations with SASE architecture
Overview:
Netskope is a Security Service Edge (SSE) and SASE leader that includes cloud DLP as part of its platform. Netskope excels at protecting data in cloud applications through its inline proxy architecture. It's particularly strong for organizations adopting zero trust network access.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: Zero trust architecture with integrated DLP
Overview:
Zscaler provides cloud DLP as part of its Zero Trust Exchange platform. Like Netskope, Zscaler takes a network-centric approach, inspecting traffic inline to detect sensitive data moving to cloud applications and the internet. Zscaler is strong for organizations pursuing zero trust initiatives.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: Organizations with legacy McAfee DLP deployments
Overview:
Trellix DLP (formerly McAfee DLP) provides endpoint, network, and cloud data protection. After the McAfee Enterprise spin-off and merger with FireEye, Trellix has been modernizing the platform while maintaining backward compatibility for existing customers.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: Intellectual property protection
Overview:
Digital Guardian, now part of Fortra, focuses on protecting intellectual property and sensitive data from insider threats and external attacks. The platform offers both agent-based and agentless approaches, with particular strength in manufacturing, technology, and pharmaceutical industries where IP protection is critical.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: User activity monitoring with DLP
Overview:
Teramind combines user activity monitoring (UAM) with DLP capabilities. The platform records user actions, detects policy violations, and can block data exfiltration. Teramind is particularly strong for insider threat programs where understanding user behavior is as important as protecting data.
Key Features:
Pros:
Cons:
Best Use Cases:
Best for: Insider risk management
Overview:
Code42 Incydr focuses specifically on insider risk detection and response. Rather than traditional content-based DLP, Incydr monitors file movements and user behavior to detect data exfiltration. The platform is designed to identify risky data exposure without blocking productivity.
Key Features:
Pros:
Cons:
Best Use Cases:
The rise of ChatGPT, Claude, Gemini, and Copilot has created new data leak vectors that traditional DLP doesn't address. Employees paste sensitive data into AI prompts, upload documents to AI assistants, and use AI-powered coding tools that may expose source code. Modern DLP must include GenAI protection.
Organizations are abandoning complex on-premise DLP deployments in favor of cloud-native solutions that deploy in hours, not months. SaaS-first DLP platforms that protect where data actually lives — in cloud applications — are gaining market share from legacy network DLP vendors.
Security teams don't want separate tools for endpoint DLP, email DLP, cloud DLP, and GenAI protection. Platforms that provide unified visibility and policy management across all vectors are becoming the preferred choice.
Pure content-based DLP generates too many false positives. Leading solutions combine content analysis with user behavior to understand context — is this a departing employee? An unusual data access pattern? Risk-based approaches reduce alert fatigue.
Heavy-handed DLP that blocks legitimate work creates friction and workarounds. Modern DLP emphasizes user education, just-in-time notifications, and contextual blocking that protects data without destroying productivity.

Before evaluating vendors, understand where your sensitive data exists:
Different DLP products excel at different scenarios:
List the applications and infrastructure the DLP must integrate with:
Ask vendors about typical deployment timelines:
Cloud-native solutions typically deploy in days; legacy platforms may take months.
Never buy DLP without a POC that tests:
DLP pricing varies significantly:
Consider the vendor's market position:
The best DLP software depends on your environment and requirements. For SaaS and GenAI protection, Strac offers the broadest coverage. For Microsoft-centric organizations, Microsoft Purview provides native integration. For network-based zero trust, Netskope or Zscaler are strong choices. Enterprises with legacy infrastructure often choose Symantec or Forcepoint.
The three main types of DLP are:
Modern platforms often combine all three types for comprehensive coverage.
DLP pricing varies widely:
Total cost of ownership should include deployment, management, and training.
Traditional DLP solutions do not protect against GenAI data leaks. Employees can paste sensitive information into ChatGPT prompts or upload documents to AI tools without detection. Modern DLP platforms like Strac, Netskope, and Zscaler now include GenAI application controls. If GenAI protection is important, verify the vendor specifically supports ChatGPT, Claude, Gemini, and similar tools.
DLP (Data Loss Prevention) focuses on identifying and protecting sensitive data content — detecting SSNs, credit cards, and confidential documents regardless of where they exist.
CASB (Cloud Access Security Broker) focuses on visibility and control over cloud application usage — who is using which apps, with what permissions, and from where.
Many modern platforms combine DLP and CASB capabilities. DLP provides the content inspection; CASB provides the application context.
Deployment time varies dramatically:
Start with monitoring mode to understand data flows before enabling blocking.
While no regulation explicitly mandates "DLP," many require data protection controls that DLP helps achieve:
DLP provides technical controls and audit evidence for these requirements.
DLP is one component of insider threat prevention, but not a complete solution. DLP can:
For comprehensive insider threat programs, combine DLP with user activity monitoring (UAM), identity analytics, and security awareness training.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

