Lark DLP (Data Loss Prevention)
Lark DLP (Data Loss Prevention) helps organizations monitor, detect, and remediate sensitive data shared across Lark chats, docs, sheets, files, and external collaborators — in real time and historically.
As teams use Lark for messaging, document collaboration, and file sharing, sensitive data like PII, PCI, PHI, API keys, financial reports, and confidential contracts can easily spread across chats and shared workspaces.
Strac Lark DLP provides:
- 🔎 Real-time and historical Data Discovery & Classification
- 🚨 Instant alerts on sensitive data exposure
- 🛑 Blocking or nudging users before exfiltration
- 🧹 Redaction, masking, deletion, and access revocation
- 📊 Visibility into who has access to sensitive data
- 🔐 Control over external sharing and public links
✨ Why Lark DLP (Data Loss Prevention) Matters

Lark combines chat, docs, cloud storage, meetings, and collaboration into one ecosystem. That means:
- Sensitive data moves quickly across chats and docs
- Files get shared externally with partners and vendors
- Public links may expose confidential information
- Gen AI copy-paste from Lark to ChatGPT or other tools increases risk
- Admins often lack deep visibility into data-level exposure
Without Lark DLP, you may only see that a file was shared — not whether it contains SSNs, credit card numbers, PHI, customer data, or proprietary information.
✨ What Strac Lark DLP Protects
Strac scans and protects:
1️⃣ Lark Chat Messages
- One-to-one messages
- Group chats
- File attachments
- Screenshots and PDFs (via OCR)
Detects:
- SSNs, passport numbers
- Credit cards (PCI)
- Medical records (PHI)
- API keys, secrets
- Custom data elements (MRN, Subscriber ID, etc.)
2️⃣ Lark Drive & File Storage

- Uploaded files
- Shared files
- Public links
- External collaborator access
You can:
- Revoke public access
- Remove external members
- Delete or redact sensitive content
- Apply classification labels
Real-Time Lark DLP (Data Loss Prevention) Controls
Strac enables multiple remediation modes:
🟢 Monitor Mode
- Alert only
- Send notifications to end user or admin
- Log event for audit
🟡 Nudge Mode
- Nudges user
- Create employee awareness
🔴 Redact Mode
- Redact message in real time or historical scan
- Delete the underlying message or file
✨ Historical Scanning (DSPM for Lark)

Lark DLP isn’t just about forward-looking protection.
Strac also performs historical scanning to:
- Discover existing sensitive data in chats and docs
- Identify publicly exposed files
- Detect excessive access permissions
- Show who has access to what
This gives security teams:
- A full data inventory
- Access visibility
- Compliance reporting
- Risk prioritization
Sensitive Data Types Supported
Strac Lark DLP supports:
- PII (SSN, passport, driver’s license, etc.)
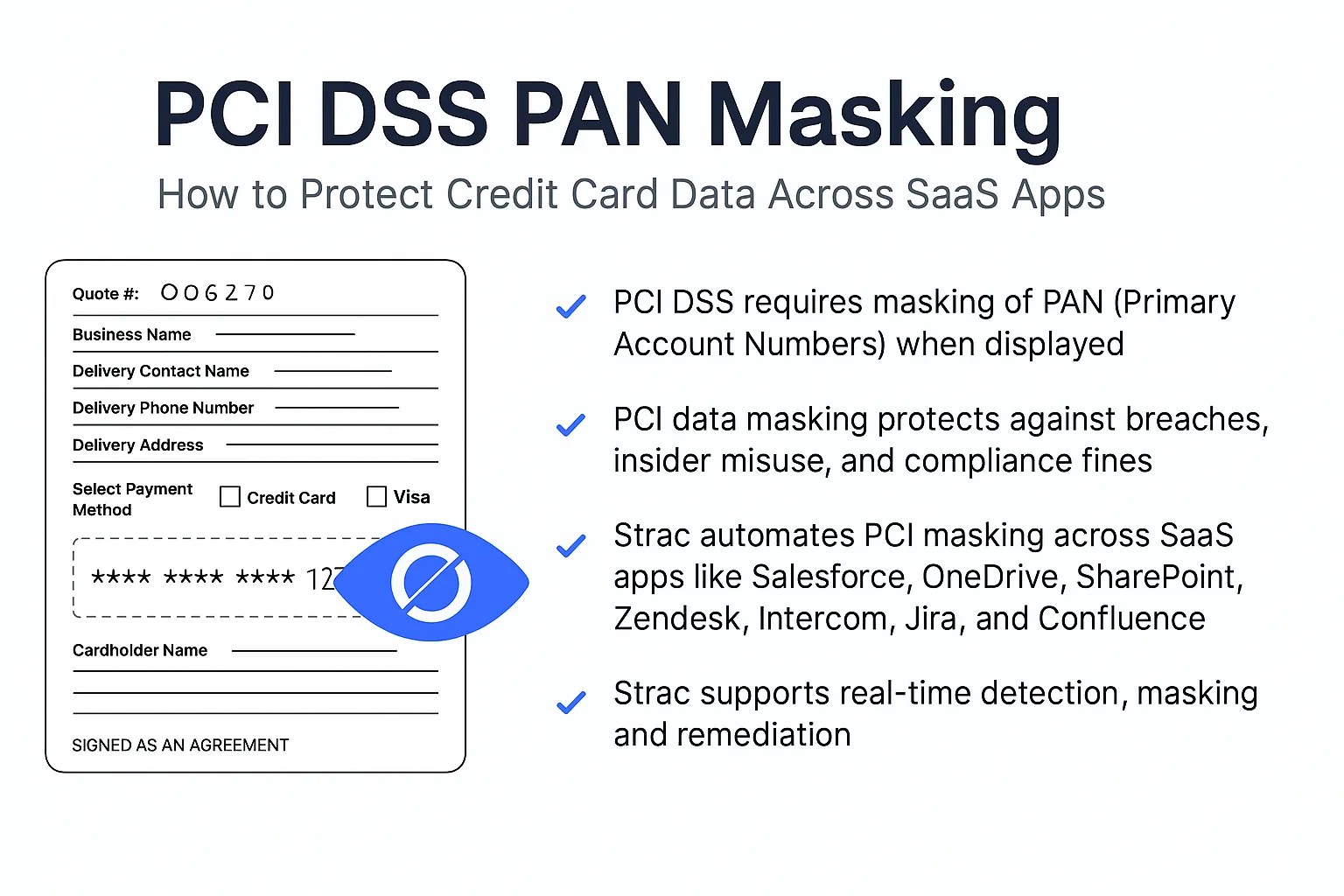
- PCI (credit cards)
- PHI (medical info)
- Financial data
- API keys & secrets
- Source code secrets
- Custom regex + contextual keyword detection
- ML + LLM-based classification
- OCR for images and screenshots
Checkout entire catalog of sensitive data elements we support
Lark + Gen AI Risk Control
Employees often copy content from Lark chats or docs and paste it into:
- ChatGPT
- Gemini
- Claude
- Copilot
Strac integrates with:
So even if data leaves Lark and is uploaded into external tools, your policies still apply.
Compliance Use Cases
Lark DLP helps with:
- SOC 2
- HIPAA
- PCI DSS
- GDPR
- ISO 27001
By providing:
- Continuous monitoring
- Evidence collection
- Automated remediation
- Data access reports
Deployment Options
You can deploy Strac Lark DLP in multiple ways:
- SaaS (Cloud Processing)
- ML/OCR in Strac cloud
- Vault visibility
- Configurable data retention
- SaaS (Local Regex Mode)
- Processing happens locally
- No content sent to cloud
- Risk metadata only stored
- Self-Hosted (Customer AWS)
- Scanner deployed in your cloud
- Data never leaves environment
- Full control over processing
🎥 Why Choose Strac for Lark DLP?
Unlike traditional DLP tools that only alert, Strac:
- Actually remediates risks
- Covers SaaS + Cloud + Endpoint + Browser
- Supports real-time and historical scanning
- Provides granular data-level visibility
- Enables practical bulk remediation
- Supports contextual + ML detection
- Tracks file lineage across environments
You don’t just get alerts — you reduce risk.

Frequently Asked Questions
Does Lark have built-in DLP?
Lark provides basic administrative controls, but it does not provide deep content inspection, advanced classification, OCR scanning, ML-based detection, or automated remediation like redaction and bulk access revocation.
Can Strac block sensitive messages in Lark chats?
Yes. In Redact Mode, Strac can redact sensitive messages or file uploads; essentially blocking messages
Can Strac scan historical Lark data?
Yes. Strac performs full historical scans across chats, docs, and files to discover existing sensitive data and exposure risks.
Does this work with Gen AI tools?
Yes. Strac extends protection beyond Lark via Browser and Endpoint DLP, preventing sensitive data from being uploaded into AI tools.











.webp)














.webp)







.avif)


