In the digital-centric business world, data transfer is a necessity and MOVEit, a renowned managed file transfer service, plays a key role in the operational efficiency and data management strategies of numerous companies. However, the 2023 breach within MOVEit's system has brought to light a significant challenge in the cybersecurity domain.
The breach, which involved the exploitation of a zero-day vulnerability, resulted in unauthorized access to a vast amount of sensitive data.
In this article, we provide a teardown of the breach, examining its impact and implications for organizational data management.
We’ll explore how this breach occurred, its consequences on the affected parties, and the broader lessons it teaches about the importance of cybersecurity measures.
The Initial Stage of the MOVEit Hack
The MOVEit attack began unfolding on May 27, 2023. It was first identified due to unusual activities within the MOVEit system. The initial signs were subtle, making early detection challenging. However, once identified, it conducted a series of investigations to understand the scope and impact.
What Led to the MOVEit Breach?
The MOVEit attack hinged on a critical zero-day vulnerability within the MOVEit managed file transfer service. This flaw allowed attackers to bypass normal authentication processes, allowing them to inject SQL commands directly into the system. This type of vulnerability is particularly dangerous as it was previously unknown, leaving the system without any specific defenses against it.
The attackers exploited this vulnerability to access the databases of MOVEit customers. By injecting SQL commands, they could retrieve, alter, or delete sensitive data stored within these databases. This method of attack is sophisticated and requires a deep understanding of both the software's architecture and SQL programming.
The Cl0p Ransomware Gang's Involvement
The Cl0p ransomware group, also known as TA505, has been active since 2019. They are known for their sophisticated ransomware attacks and extortion schemes, often targeting large organizations and demanding hefty ransoms.
They operate as an initial access broker and have developed three zero-day exploits. They use custom webshells and malware toolkits in their attacks, setting them apart from other their counterparts who rely on open-source tools.
In addition to the initial data breach, Cl0p's involvement extended to the post-breach extortion phase. They threatened to leak the stolen data publicly if no agreement was reached within seven days, adding an additional layer of urgency and threat to the breach's aftermath.
To effectively counter the threats from such cybercriminal groups, adopting DLP platforms such as Strac is crucial.
Impact of the MOVEit Ransomware Attack
The scale of the breach was significant. Thousands of highly sensitive information, such as staff data, national insurance numbers, and bank details, were compromised across companies such as BBC, British Airways, Boots, and Aer Lingus.
Following the MOVEit breach, legal actions have significantly escalated. IBM now confronts class action lawsuits. The lawsuits charge IBM with a data breach stemming from the company's oversight and its controversial use of the MOVEit application.
Response From Progress Software
In response to the MOVEit breach, Progress Software, the vendor behind MOVEit, took immediate and decisive action to address the vulnerability and mitigate the breach's impact. The company's response included a thorough investigation to understand the breach's scope and to identify any additional potential vulnerabilities in their systems.
- Progress Software released a critical security update to patch the zero-day vulnerability exploited in the breach. This update was essential in closing the security gap and preventing further exploitation.
- Customers were alerted to apply the security update as soon as possible.
- Progress Software reviewed and strengthened their overall cybersecurity posture to prevent similar incidents in the future.
How Can Strac Help Prevent MOVEit Similar Cyber Attacks?
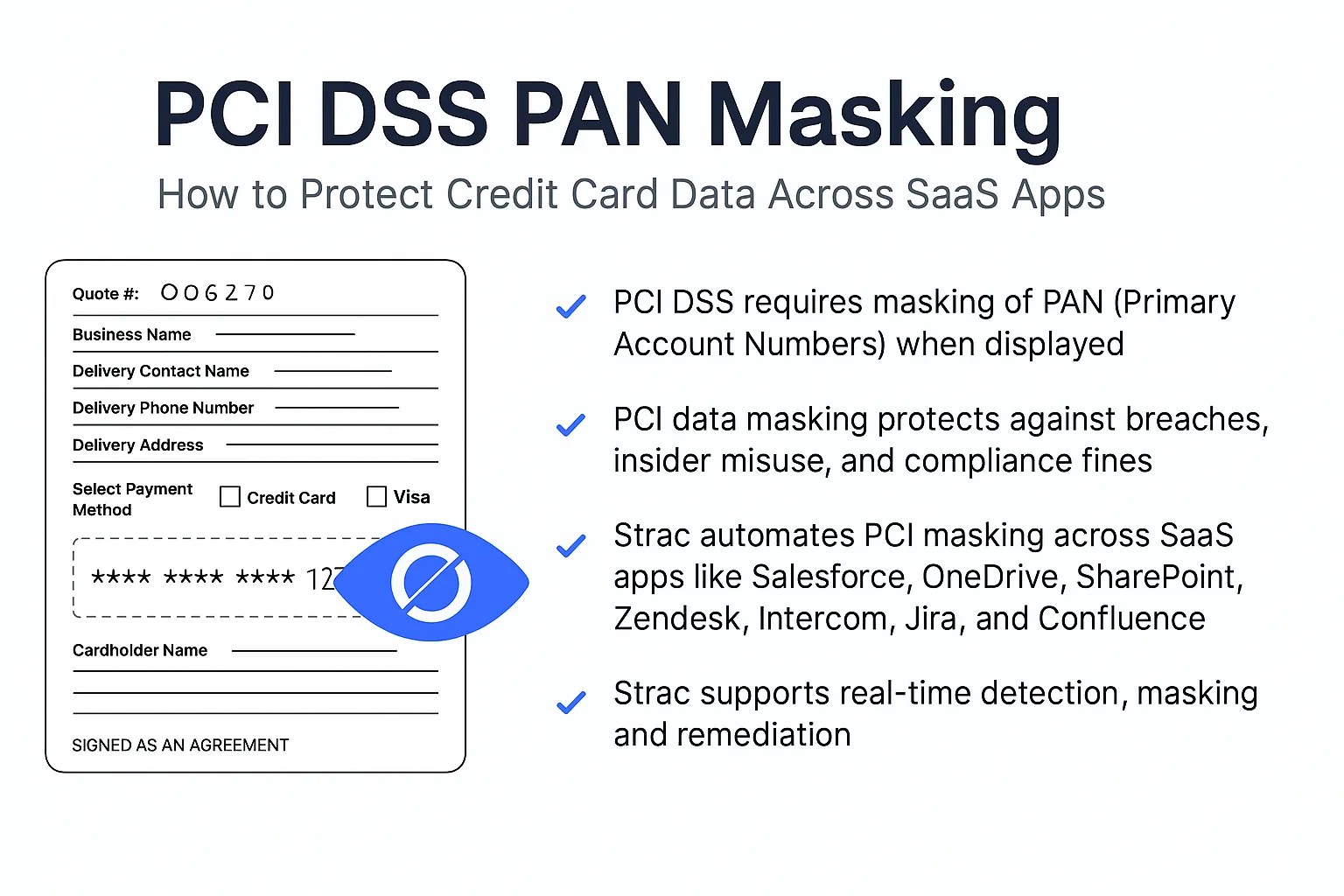
Strac is a modern DLP solution designed to help organizations protect sensitive data from unauthorized access, leaks, or breaches. Here's how Strac can be helpful in preventing data breaches like MOVEit:

- Real-Time Detection and Encryption: Strac employs real-time detection and encryption mechanisms, crucial for identifying and securing sensitive data as it is being transferred or accessed.
- Redaction of Sensitive Data: Strac's automatic redaction feature ensures that sensitive data, such as personal and financial information, is masked or removed from documents and communications.
- Tokenization and Proxy APIs: By leveraging a Zero Data architecture, Strac ensures that sensitive data is tokenized and does not need to be directly handled by backend servers.
- Continuous Scanning of Sensitive Data: Strac continuously scans for sensitive data, maintaining compliance with stringent regulatory and compliance standards.
- Multi-Factor Authentication: Strac enhances security by requiring multiple verification factors for access, preventing unauthorized entry even if a password is compromised.











.webp)














.webp)