How to Secure Sensitive Data in SaaS, Cloud, and AI Platforms?
Explore the essentials and types of sensitive data management in SaaS, Cloud, and AI environments. Learn actionable strategies for effective data protection.
The rapid adoption of SaaS, Cloud, and AI technologies has revolutionized business operations and introduced new challenges and risks in data security. As these digital platforms become integral to our daily activities, securing sensitive data such as Personal Identifiable Information (PII) and financial records has never been more critical.
The main challenges in securing sensitive data in SaaS, Cloud, and AI environments revolve around unauthorized access, data breaches, and compliance issues. The complexity of these environments often makes it difficult to have a centralized security protocol, leading to potential vulnerabilities.
The consequences of data breaches can lead to financial losses, lawsuits, and reputational damage. In fact, research indicates that nearly 65% of consumers lose faith in a company following a data breach, and a staggering 85% would cease interactions with the organization altogether.
This blog analyzes how to secure sensitive data effectively in SaaS, Cloud, and AI environments. Let’s begin.
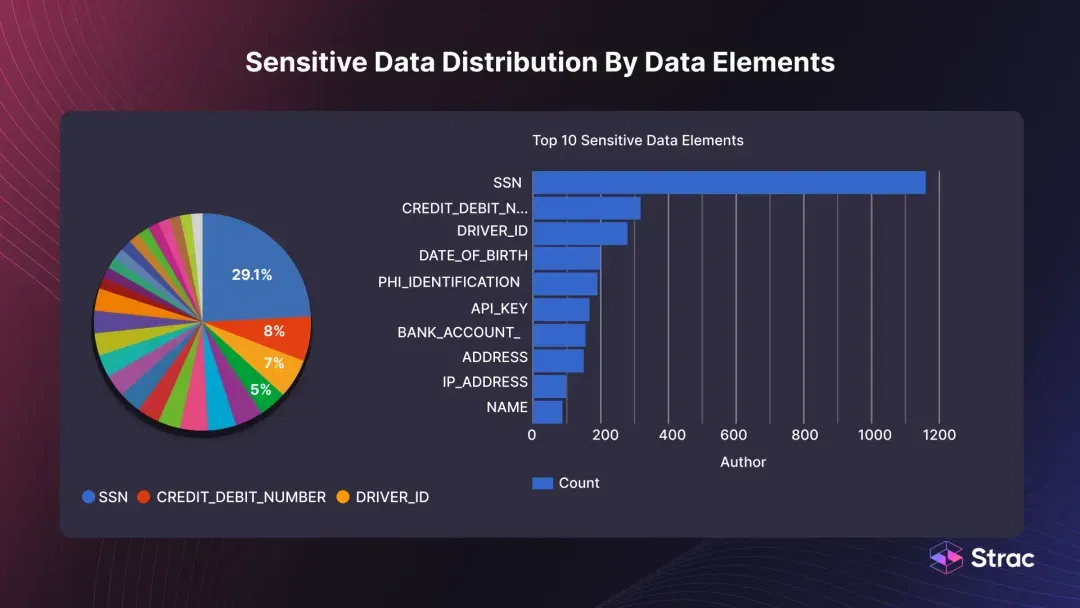
Sensitive data refers to any information that, if exposed, could harm an individual or organization. Sensitive data examples include Personal Identifiable Information (PII) like social security numbers and email addresses, Protected Health Information (PHI) such as medical records, as well as financial information and intellectual property.
Essentially, it's data that is private, confidential, and crucial to the integrity and success of a business or individual. The importance of protecting sensitive data is crucial in SaaS, Cloud, and AI environments for several reasons:
Understanding the types of sensitive data is crucial for implementing effective security measures. Here are some of the most common categories:
PII is any data used for the identification of an individual. This encompasses a wide range of information, such as names, social security numbers, addresses, phone numbers, and email addresses. PII can be customer data, employee records, or vendor information in business.
.webp)
PHI is data related to an individual's health status, healthcare provision, or transactions. This can include medical records, lab results, and insurance information. PHI is highly regulated, especially under laws like the Health Insurance Portability and Accountability Act (HIPAA) in the United States.

Intellectual property refers to inventions, such as gadgets, literary work, symbols, names, and images used in commerce. This can include proprietary software, patents, trade secrets, and copyrighted materials in a business setting. Unauthorized access to intellectual property can lead to significant financial loss and competitive disadvantage.
This category includes data related to an individual's or organization's financial status or activities. Examples include bank account numbers, credit card details, transaction histories, and tax records. Financial information is often targeted for fraud and identity theft.
Software as a Service (SaaS) platforms have become indispensable tools for businesses, offering a range of functionalities from data storage to real-time collaboration. However, the convenience comes with its own set of security vulnerabilities that can lead to sensitive data exposure. Here are some key areas of data security concern in SaaS ecosystems:
One of the most common vulnerabilities is poorly implemented access controls. Unauthorized users can easily access sensitive data without proper authentication and authorization mechanisms.
Data is often most vulnerable when in transit. Inadequate encryption or the use of outdated security protocols can make it easier for cybercriminals to intercept and access sensitive data.
SaaS platforms often integrate with other services and applications. Each integration point is a potential vulnerability, especially if the third-party services do not adhere to stringent security measures.
Improperly configured settings can inadvertently expose sensitive data. For example, a misconfigured database could allow public access to what should be restricted information.
Like any software, SaaS platforms can have exploitable bugs. Cybercriminals are always on the lookout for such vulnerabilities to gain unauthorized system and data access.
Effective data protection is a compliance necessity and a cornerstone of modern business integrity. Here’s how to ensure effective sensitive data management:
Before protecting sensitive data, you must know what and where it is. Start by identifying the different types of data your organization handles. This could range from public data to highly confidential information.
Once identified, start sensitive data classification based on its sensitivity level—public, internal, confidential, or restricted. Create and maintain an inventory that tracks where each data type is stored. This will help you apply appropriate security measures to each data set.
Strong authentication mechanisms ensure that only authorized individuals can access sensitive data. Implement multi-factor authentication across all systems that house sensitive data for additional security.
Enforce strong password policies that require a mix of characters, numbers, and symbols. Moreover, keep up with advancements in authentication technologies and update your methods accordingly.
Encryption is essential for protecting data from unauthorized access, both when it's stored and when it's transferred over a network. Utilize strong encryption algorithms such as AES-256 (a symmetric block cipher selected by the U.S. government to protect classified data) for encrypting data at rest.
Make sure that SSL/TLS encryption is enabled for all data in transit. It is best to periodically update your encryption keys and conduct security assessments to ensure the encryption remains robust.
Regular security audits identify system vulnerabilities, allowing you to address them before they can be exploited. This should include penetration testing and code reviews to ensure no loopholes lead to data exposure.
RBAC minimizes the risk of internal data breaches by ensuring employees can only access the data they need for their jobs. Implement role-based access control to ensure employees can only access the data necessary for their job functions. You must use these role definitions to set up access controls in your data management systems.
Data masking and tokenization obscure the actual data, making it useless even if it falls into the wrong hands. Use data masking and tokenization techniques to obscure specific data within a database, making it inaccessible to unauthorized users. This is particularly useful for protecting financial information and PII.
.webp)
Strac's real-time masking algorithms can be embedded in customer-critical use-cases, offering immediate data protection. Its AI-powered analytics are highly accurate in detecting sensitive data across unstructured text and documents, allowing for effective masking and tokenization.
Secure backups are essential for data recovery in case of accidental deletion or a cyberattack. Ensure that backups of sensitive data are also encrypted and stored in a secure location. Conduct monthly tests to ensure that data can be restored successfully from these backups.
Monitoring and logging are crucial for detecting any unauthorized or suspicious activity early. Keep detailed logs of who is accessing what data and when. Use monitoring tools to detect unusual access patterns or behaviors indicating a security breach.
Training sessions help employees become the first line of defense against cyberattacks. Educate employees about data security and the risks of sensitive data exposure. Regular training sessions can help them recognize phishing attempts and other security threats.
A DLP solution monitors and controls data transfers, preventing sensitive data from leaving the secure corporate environment. Use a DLP solution to monitor and control data transfers. This can help prevent sensitive data from being sent or accessed in an unauthorized manner. Don't just stop at implementing a DLP solution; choose the best by opting for Strac. With its cutting-edge features and seamless integrations, Strac offers a comprehensive approach to data loss prevention.
Check out Strac’s API Docs for more information.
A contingency plan in place mitigates the impact of data exposure incidents. To get started, you'll need:
Immediate Response Protocols: Immediate response protocols help to contain the incident and manage its immediate impact, setting the stage for a more detailed investigation.
How to do it?
Forensic Analysis and Statutory Reporting: Forensic analysis identifies the incident's root cause, helping to prevent future breaches. Statutory reporting ensures legal compliance and can also aid in the investigation. For instance, India's national identification database Aadhaar breach exposed over 1.1 billion records, emphasizing the need for robust contingency plans.
How to Do It?
Longitudinal Security Enhancements: Long-term security enhancements are essential for preventing future incidents and restoring stakeholder trust.
How to Do It?
Strac specializes in Data Loss Prevention (DLP), offering a comprehensive suite of features tailored for SaaS, Cloud, and AI environments. With its advanced AI algorithms, Strac provides highly accurate sensitive data detection.

Read our other resources:
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

