PII Compliance: Requirements & Checklist
Ensure your organization's data security with PII compliance. Meet regulatory requirements and protect sensitive information.
PII compliance isn’t just about protecting names and Social Security numbers; it’s about controlling every piece of data that can identify a person across your SaaS apps, cloud storage, databases, and AI tools. In a world where data moves instantly between platforms and teams, personal information is constantly exposed to risk.
Regulators worldwide now require organizations to know exactly where PII lives, who has access to it, and how it’s protected. Failing to meet PII compliance standards doesn’t just lead to fines; it damages trust, reputation, and long-term growth.
In this guide, we’ll break down what PII compliance really means in 2026, what laws apply globally, and how modern organizations can build a scalable, audit-ready data protection strategy.
92% of Americans are concerned about privacy when using the internet. This highlights the need for laws in favor of data protection that can make people feel safer when sharing information.
PII (Personal Identifiable Information) is any piece of data that someone could use to figure out who you are. Some of them are easier to identify, such as your name or social security number, yet others can emerge to be more subtle and reveal details only when combined with others.
This article discusses everything about PII compliance - compliance standards, checklists, and more.
For strong PII compliance, you need to know exactly what qualifies as personal data; and how risky it becomes in context. Not all PII is equal, but all of it requires protection.
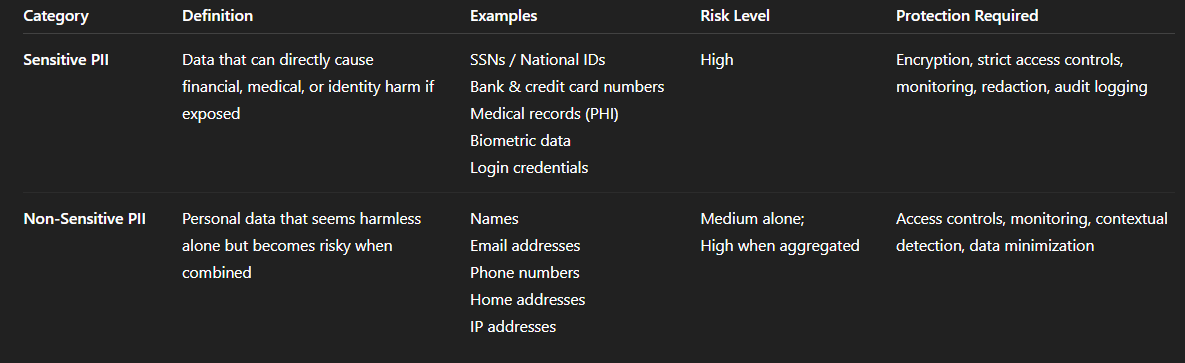
Sensitive PII can cause serious harm if exposed; identity theft, fraud, or medical exploitation.
Examples include:
This data requires strict controls; encryption, access limits, monitoring, and redaction.
Non-sensitive PII may seem harmless on its own; but becomes dangerous when combined with other data.
Examples include:
A name + date of birth + address can be enough for identity fraud. That’s why modern PII compliance looks at context; not just individual data points.
PIIs differ on a wide range of subjects. Hence, every other geography has a different set of rules. Here are some of them.

In the European Union, Directive 95/46/EC defines “personal data” as information to identify a person via an ID number or factors specific to mental, physical, cultural, and other forms of identity.
In Australia, the Privacy Act 1988 describes “personal information” as information or an opinion that may be true or false, that is related to an individual, is apparent, or can be reasonably ascertained. This goes much broader than in most other countries.
In New Zealand, the Privacy Act defines “personal information” as any information related to a living, identifiable human being, including contact information, names, purchase records, and financial information.
From a legal standpoint, the responsibility for protecting PII isn’t entirely attributed to organizations; individual owners also share responsibility.
If we go by the numbers, a study by Experian found that 42% of consumers believe it is the company’s responsibility to protect their personal data. Due to this universal perception, organizations consider themselves responsible for PII and ensure maximum safety. The most common and effective way to protect PII is by establishing a Data Privacy Framework.
The short answer to this is yes.
Almost all regulatory bodies enforce measures for organizations to undertake adequate measures to protect data collected from users online. In some cases, the steps are laid out in detail, and since data leaks and breaches are on the rise, it makes sense for organizations to invest in protecting user data.
Apart from regulations, PII compliance can be helpful to companies in several other ways too. Here’s how:
PII data can be classified into two major types - sensitive and non-sensitive PII. The following distinction helps one prioritize security tools and processes that ensure PII compliance requirements are rightly met.
Sensitive PII refers to any information with ‘legal, contractual, or ethical requirements for restricted disclosure.’ Some examples of sensitive PII are social security numbers, bank details, passport information, or credit card details, along with medical records under HIPAA.
.png)
➡️Learn more about sensitive data elements here - Strac’s catalog of sensitive data elements.
Non-sensitive PII, on the other hand, is any information that can be found in public records, such as a phone book or an online platform such as LinkedIn. Some of the common categories that make up the non-sensitive PII list are address, contact, date of birth, and so on.
No wonder PII compliance requires protecting both types of PII data. Sensitive data should be encrypted because of the potential damage it can cause if information is compromised. Alternatively, though non-sensitive data is less of a risk, with sensitive data, PII can be used to commit fraud or identity theft.
Data privacy regulations in the United States are complex at the very least. The country first observed its data privacy law in 1974 with the introduction of the Privacy Act of 1974. The law first cleared the air about what federal agencies could collect, manage, and use personal information.
The bill was well-received but critics claimed that the US lacks an all-encompassing federal law to govern data privacy.
Then, the Federal Trade Commission Act (FTC Act) enabled a broad jurisdiction over commercial entities to allow government agency to prevent deceptive trade. However, it plays a role in enforcing privacy laws. It can impose sanctions on companies for violating consumer data and not maintaining appropriate data security measures.
Apart from the two above-mentioned laws, some of the other privacy laws in the US are:
PII compliance differs from one nation to another, and hence a defined structure is often avoidable. However, one can formulate a step-by-step framework to achieve the principal objectives.
Here’s the PII compliance checklist that covers them all.
The road to PII compliance begins with first establishing what PII your organization collects and where it is stored. This basic step is repeated periodically to ensure the standards are met.
Next, determine what definition of PII applies to your geography or industry. For instance, if you live in California, make sure you meet all the requirements of the CCPA.
Once you finish the basics, it's time to find out what data is stored and how to gain visibility over others.
This particular step can be seamlessly achieved using smart AI tools like Strac. With Strac DLP, you can instantly detect and redact PII and PHI data.
Once you have classified the data in the first step, it’s time to create a PII compliance policy that governs working with personal data. One such framework is GDPR, a data processing framework. Experts suggest that even if the GDPR regulation doesn't govern you, these principles lay the perfect foundation for building your own PII policy.
Going a step further, the PII compliance policy should have these essential features:
Achieving PII data compliance involves a layered approach to security. At this stage, your data security tools should prioritize reducing the risk of data leaks and unauthorized individuals accessing non-sensitive and sensitive PII. Concerning data safety at this stage, the data is encrypted and made accessible with endpoint security, and cloud data loss protection (DLP).
IAM refers to Identity and Access Management. It defines and manages user roles and access for individuals in an organization, ensuring that only the right people can access the resources. IAM requires creating and proactively managing role-based access controls.
Lastly, monitor your PII. Keep your recovery options ready to ensure a timely response to a data breach.
Protecting PII is not just about knowing where sensitive data exists; it’s about continuously controlling how it moves, who can access it, and eliminating risk the moment it appears. Most tools stop at visibility. Strac goes further by combining discovery, classification, and real-time remediation into a single workflow, so PII is not just identified, but actively protected across your entire environment.
Here’s how Strac helps you protect PII end-to-end:
Strac continuously scans your data across SaaS apps, cloud storage, endpoints, and GenAI tools to identify where sensitive information lives. Whether it’s emails, documents, chat messages, screenshots, or databases, Strac ensures no PII goes unnoticed.
Not all data carries the same level of risk. Strac uses ML-powered, content-aware detection (not just regex) to accurately classify PII, PHI, PCI, and custom data types. This reduces false positives and gives security teams clear context on what truly matters.

Unlike traditional tools that only notify you after exposure, Strac takes action instantly. It can automatically:
This ensures PII is protected the moment it appears; not after it’s already leaked.
PII doesn’t stay in one place. It moves across tools like Google Workspace, Slack, Salesforce, and even AI platforms like ChatGPT. Strac provides unified protection across all these surfaces, eliminating gaps where data typically leaks.

Strac helps you understand who has access to sensitive data and where it’s overexposed. It can remove public links, revoke external collaborators, and enforce least-privilege access; reducing unnecessary risk across your organization.
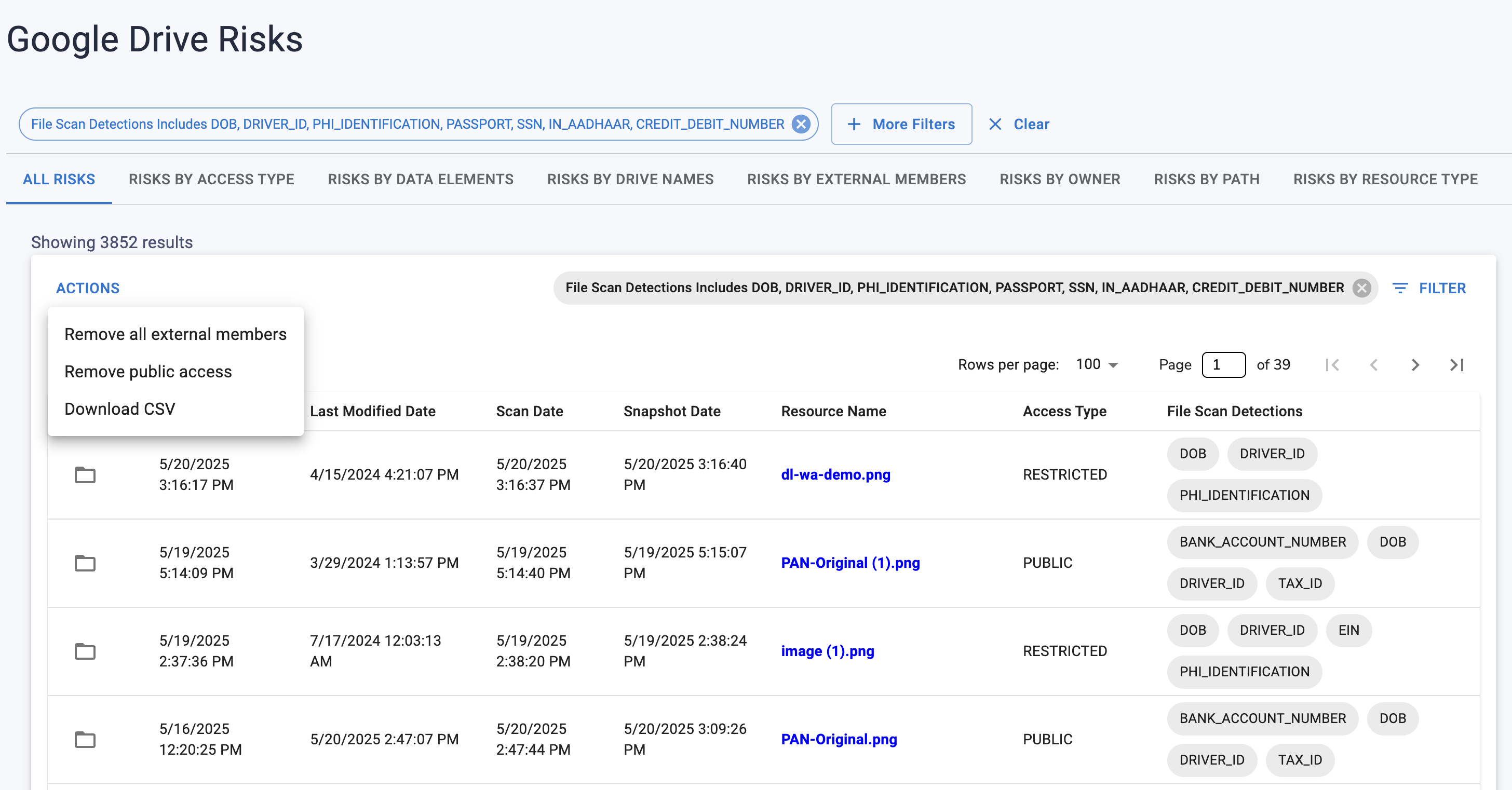
With built-in support for frameworks like GDPR, HIPAA, PCI DSS, SOC 2, and ISO 27001, Strac helps you meet compliance requirements while keeping workflows fast and frictionless. Policies can be applied consistently across all systems without disrupting productivity.
PII risk is not static. As data moves, gets copied, or shared, new vulnerabilities emerge. Strac continuously monitors your environment and adapts in real time; ensuring your protection evolves with your data.

Further, Strac’s Bubble plugin collects and stores critical, sensitive information. The original product is a no-code leader and is loved by organizations all across the globe. However, it fails to achieve the highest security standards alone. This is where Strac and its plugin step in to protect sensitive information.
Read our other Compliance and Data Loss Prevention resources:
Bottom line: Strac doesn’t just help you find PII; it ensures that wherever it appears, it is immediately secured, controlled, and compliant without adding operational overhead.
PII protection today is not a visibility problem; it’s an execution problem. Most organizations already have tools that tell them where sensitive data might exist, but they lack the ability to act on it fast enough to prevent exposure. That gap is exactly where breaches happen.
Strac closes that gap by turning detection into immediate enforcement. Instead of dashboards and alerts piling up, you get real-time control over how PII is handled across SaaS, cloud, endpoints, and AI tools. The result is simple: less manual work, fewer blind spots, and significantly lower risk.
If you cannot detect, classify, and remediate PII in one continuous loop, you are not truly protecting it; you are just observing it.
It’s absolutely enforceable; and increasingly strict. Regulations like GDPR, CCPA, and HIPAA come with real financial penalties, audits, and legal consequences. Treating PII compliance as a “best practice” instead of a requirement is one of the fastest ways companies get fined.
Yes; size does not exempt you. If you collect, process, or store personal data, you are responsible for protecting it. In fact, smaller companies are often targeted more because they lack strong compliance controls.
No. Encryption is just one layer. PII compliance also requires visibility, access control, audit trails, breach response plans, and ongoing monitoring. If you can’t see where your PII is or who is accessing it, you are not compliant.
No; and this is where most companies fail. You cannot protect or govern what you cannot see. Continuous data discovery and classification are foundational to any real PII compliance strategy.
Not on their own. They provide basic controls, but they lack deep content inspection, cross-platform visibility, and automated remediation. PII often leaks through connected apps, exports, screenshots, and AI tools.
You may still be liable. Many regulations require breach disclosure within strict timelines; even if the issue is resolved. The impact depends on how fast you detect, respond, and prove control over the data.
No. Humans are the biggest risk vector. Policies and training help, but without automated enforcement and monitoring, mistakes will happen and PII will leak.
Continuously; not annually. Data moves every second across SaaS, cloud, endpoints, and AI tools. A yearly audit is not enough to keep up with real-world risk.
Both; but mostly increases risk if unmanaged. AI tools accelerate productivity, but they also create new data leakage paths. Without controls, employees can unintentionally expose sensitive data in prompts and outputs.
Start with three things:
If you’re missing any of these, your compliance posture is incomplete.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

