What Is Data Loss Prevention for Email?
Learn about email data loss prevention, common threats, and best practices to protect your communication with robust solutions. Ensure your email security in today's digital age.
Email is the #1 tool for business communication—and also one of the biggest sources of accidental and malicious data leaks. Whether it’s sensitive customer information, healthcare data, or intellectual property, email-based breaches can result in legal, financial, and reputational fallout. This guide explores what Data Loss Prevention (DLP) for email is, how to implement it in Microsoft 365, and how tools like Strac offer advanced, AI-powered protection.
Email Data Loss Prevention (DLP) is a cybersecurity strategy that prevents unauthorized exposure of sensitive data via email. It ensures that confidential information such as Personally Identifiable Information (PII), Protected Health Information (PHI), Payment Card Industry (PCI) data, and other critical business information is not accidentally or maliciously leaked.
As email remains the most widely used communication tool in organizations, it is also one of the biggest channels for data breaches. Implementing a robust Email DLP solution helps businesses comply with regulatory requirements and protect their sensitive data from being leaked.
Email DLP solutions are designed to monitor, detect, and remediate potential data leaks via email. These solutions enforce security policies that prevent employees from sending sensitive data to unauthorized recipients. They use advanced techniques like content inspection, keyword matching, contextual analysis, and machine learning to identify sensitive information before it leaves the organization’s email infrastructure.
Organizations implement Email DLP solutions to:
Email data loss occurs through various scenarios, including:
Email DLP plays a central role in modern data protection because email remains the most common channel for accidental leaks of PII, PCI, PHI, secrets, tokens, and internal business information. Organizations rely heavily on email for employee communication, customer support, and partner collaboration; without automated protection, sensitive data can leave the environment in seconds. Strong email DLP ensures continuous visibility, proactive prevention, and consistent compliance with frameworks such as GDPR, HIPAA, SOC 2, and PCI DSS.
Effective email DLP does not stop at detection; it applies real-time remediation to redact, mask, block, or quarantine sensitive content before it reaches the wrong recipient. This protects regulated data, reduces legal exposure, and prevents human errors from escalating into compliance incidents. By securing email as part of a unified DSPM + DLP strategy, companies create a complete protective layer across all communication channels.
A powerful email DLP solution must deliver the accuracy, automation, and breadth needed to protect sensitive data without slowing down teams. Since email is a fast-moving and high-volume communication channel, the right capabilities ensure both security and seamless user experience. The following features define a modern, enterprise-ready Email DLP foundation.

These capabilities help organizations prevent data exposure, streamline compliance operations, and gain unified visibility across all communication surfaces. With a strong Email DLP foundation, companies can reduce risk dramatically while maintaining efficiency.
Understanding the types of data loss helps organizations better protect their information. Some common types include:
Email DLP solutions operate by implementing various security mechanisms to detect and prevent data loss. The key functionalities include:
Email data loss exposes organizations to serious security, financial, and compliance risks. Because email is often used to share documents, customer information, and internal updates, a single misdirected message can trigger a high-impact incident. Many teams underestimate the scale of exposure until an audit or breach reveals how much sensitive data travels through email each day.
These risks make email one of the highest-priority vectors to secure. By automating detection and remediation, companies can stop leaks before they leave the environment and maintain strong compliance across the entire communication workflow.
Microsoft 365 DLP is a native feature that monitors and controls the flow of sensitive information across Exchange Online, OneDrive, SharePoint, and Teams. It applies rules and policies to detect sensitive content and trigger actions such as:
For broader protection, Strac enhances these controls with AI, OCR scanning, redaction, labeling, and automated remediation.
Yes—and especially for email. Threats include:
Without DLP, organizations risk regulatory fines, IP theft, and reputation loss. Strac’s Email DLP covers these use cases and integrates seamlessly with Microsoft 365 and Gmail.
Use Microsoft’s sensitivity labels or leverage Strac’s built-in and custom data detectors, which support GDPR, PCI, HIPAA, and more.
Understand workflows and data usage patterns to avoid creating overly restrictive rules.
Configure policies based on templates or create custom policies for your unique data types and compliance goals.
Define conditions, exceptions, and actions (e.g., block, encrypt, warn, redact).
Use test mode to analyze how policies perform without disrupting daily operations.
Use Microsoft Compliance Center or Strac’s centralized dashboard to monitor DLP activity and alerts.
Refine policies based on violation trends, user feedback, and business growth.
Paired with Strac, you also get powerful features like image/text redaction, automated encryption, and data classification across platforms.
Use Strac for extended DLP across cloud, email, endpoints, and AI tools like ChatGPT, Copilot, and Google Gemini.See how this works for Gen AI
Microsoft 365 DLP operates by inspecting:
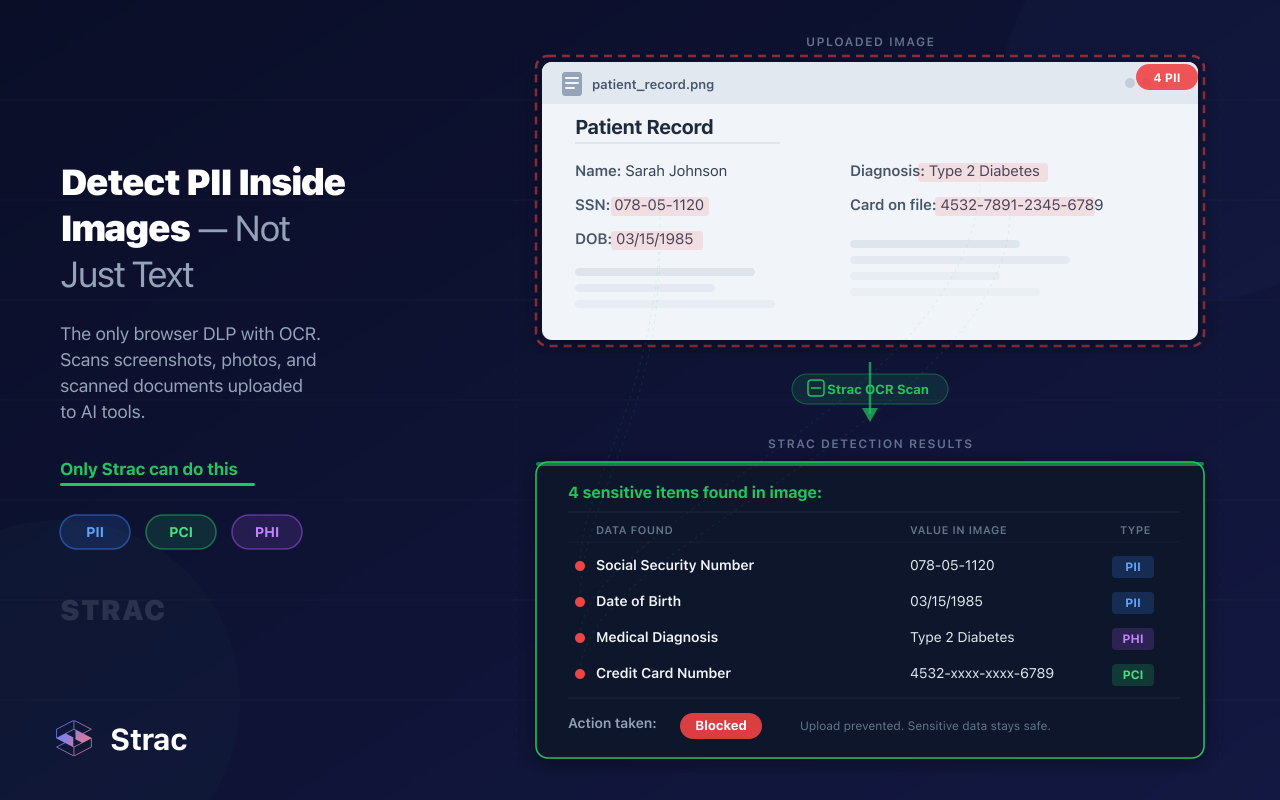
Strac builds on this with AI-based contextual analysis, structured + unstructured data scanning, and OCR-based image inspection.
Label content using Microsoft or Strac’s classification engine. Strac supports automated classification via OCR and ML.
Apply role-based access controls (RBAC) and the principle of least privilege.
Scan files in SharePoint, OneDrive, and Teams for PII, PCI, PHI.
Delete or archive unused sensitive files that could pose risk.
Audit shared links, email forwards, and AI tool interactions for risky exposure.
Microsoft DLP policies define:
Strac augments these with custom rule creation, multi-platform enforcement, and compliance dashboards for HIPAA, PCI, SOC 2, ISO 27001, and CCPA.
Strac integrates directly with Microsoft 365 to provide:
Explore full integration details: Strac Office 365 DLP
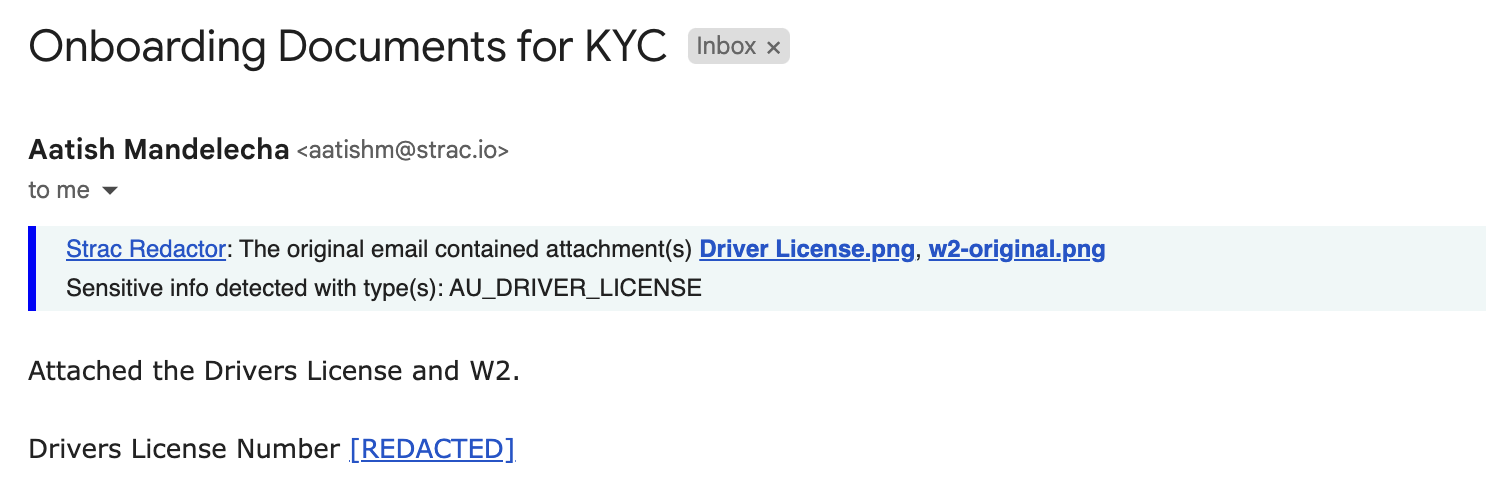
Strac also protects inbound email communication, detecting:
This prevents compromise from both directions—incoming and outgoing.
Strac uses ML, pattern recognition, and contextual rules to identify sensitive data across the message body, metadata, and attachments.
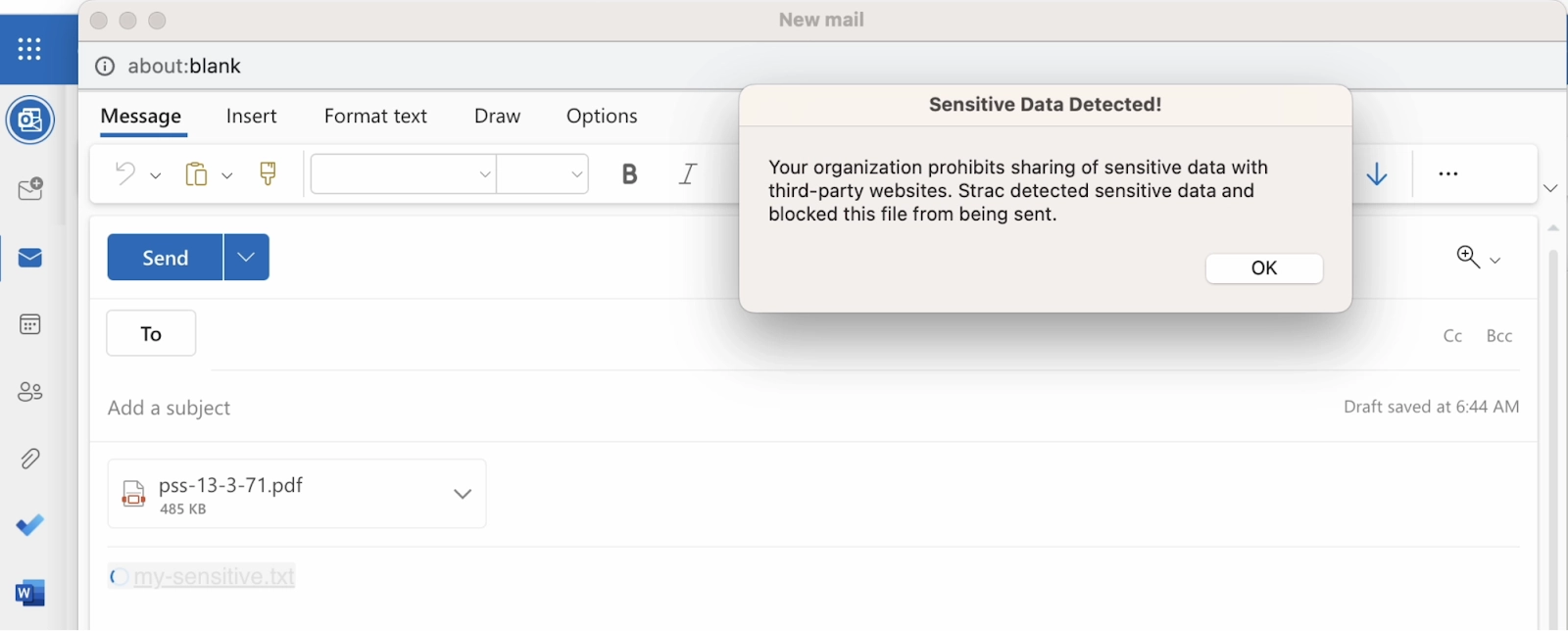
Automatically applies redaction, encryption, or blocking actions in real time, ensuring data doesn’t leave your environment unprotected.
Employees receive alerts and suggested next steps when they attempt to send restricted data. Security teams are notified instantly.
Strac provides detailed dashboards and audit logs to ensure full compliance with internal policies and external regulations.
Here are common data types that DLP solutions like Strac and Microsoft 365 help protect:
Strac supports custom classification and deep discovery using OCR, AI, and cloud connectors.
Apart from Email DLP, organizations can implement other DLP solutions, including:
Email remains one of the fastest and most common pathways for sensitive data to leak, making Email DLP a non-negotiable layer in any modern security stack. With the right capabilities in place; content-aware detection, real-time remediation, agentless deployment, and unified SaaS coverage; organizations can prevent human errors, meet regulatory standards, and protect sensitive information before it escapes the environment. A strong Email DLP program not only safeguards compliance but also reinforces customer trust, operational resilience, and long-term data security across the entire communication ecosystem.

Email data loss usually happens because employees move fast, rely heavily on email for daily communication, and often underestimate how much sensitive information gets shared across inboxes. Human error is the number one factor; people paste the wrong data, attach the wrong file, or type the wrong recipient. At the same time, misconfigurations, lack of automated controls, and data stored inside attachments all contribute to consistent exposure.
The most common causes include:
These risks are why modern organizations rely on automated Email DLP to identify and remediate sensitive content before it escapes the environment.
Email DLP in Office 365 works by monitoring messages and attachments in real time to detect sensitive information before it is sent, stored, or shared. Office 365 uses predefined and custom policies to identify data patterns like credit cards, SSNs, health data, or other sensitive content. When a policy is triggered, the system can alert the sender, block the message, or apply encryption depending on how the rule is configured.
However, native Office 365 DLP has limitations compared to modern content-aware systems.
For full coverage, many companies layer Office 365 with advanced Email DLP that applies real-time redaction, broader SaaS visibility, and agentless protection across the entire communication stack.
A strong Email DLP solution must combine accuracy, automation, and broad coverage to stop leaks before they occur. Because email remains a high-risk vector for regulated data, the right capabilities ensure both security and seamless user experience. Organizations evaluating DLP should look for features that prevent exposure while maintaining speed for day-to-day communication.
Key features include:
These features ensure that Email DLP functions as a proactive security layer rather than a reactive alerting tool.
No security solution is 100% foolproof. While Email DLP significantly reduces risk, sophisticated phishing attacks, insider threats, or shadow IT activities may still bypass controls. Regular audits and security awareness training are crucial.
Not if implemented correctly. A well-configured Email DLP solution like Strac provides alerts and education instead of outright blocking legitimate work, ensuring a balance between security and productivity.
SEGs filter incoming threats like phishing and malware, whereas Email DLP focuses on preventing outbound data loss. They complement each other rather than replace one another.
Yes! Even small businesses handle sensitive customer and financial data. Data leaks can be just as devastating for small firms, leading to legal, financial, and reputational damage.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

