Web DLP: What It Is, How It Works & Best Practices
Explore the role of Web DLP in protecting sensitive data across web channels. Learn the steps for implementing it, overcoming challenges, and best practices.
Digital technology offers many opportunities but also several threats that attack the foundation of business integrity. From sensitive customer information to business strategies, the data that companies possess are invaluable assets. However, the risk of data breaches has skyrocketed with the rise of remote work, cloud computing, and bring-your-own-device (BYOD) policies. Reports indicate that data breaches continue to be widespread, with organizations experiencing an average of 15 incidents a year.
This backdrop sets the stage for Web Data Loss Prevention (DLP). It shields the data from both accidental slips and deliberate theft, especially as it moves across HTTP and HTTPS channels. Through the implementation of sophisticated DLP policies and technologies, including a well-defined web DLP policy, businesses can take a proactive stance. Here, we’ll explore everything about crafting and enforcing Web DLP protocols, the challenges, and the advantages they bring.
Web Data Loss Prevention (Web DLP) refers to a set of technologies and practices designed to monitor, detect, and prevent the unauthorized transmission of sensitive data over web channels. Web DLP solutions focus on securing data as it moves across the internet, particularly through web browsers, cloud applications, and web-based email services. These solutions aim to safeguard information such as personally identifiable information (PII), financial data, intellectual property, and other sensitive content from being exposed through web activities.
Web DLP solutions provide extensive visibility into data movement across web channels, ensuring that sensitive information is protected during online interactions.
As organizations increasingly adopt cloud services, Web DLP becomes essential in securing data stored and processed in cloud environments, preventing unauthorized access or sharing.
Web DLP solutions can analyze web traffic in real-time, enabling immediate detection and response to potential data breaches or policy violations.

Organizations can enforce data protection policies and compliance requirements, ensuring that data is handled according to internal and regulatory standards.
Web DLP tools often include user behavior analytics to identify suspicious activities and potential insider threats.
Web DLP is designed to monitor how sensitive data moves through everyday web activity. It focuses on user actions inside browsers and web-based tools where data is most likely to be shared, uploaded, or exposed.
By monitoring these interactions in real time, Web DLP helps prevent sensitive data from leaving the organization through common web workflows — not just through traditional file transfers.
An effective Web DLP strategy involves a series of steps designed to protect sensitive data from unauthorized access and leaks. Here’s a structured approach to crafting and enforcing Web DLP protocols.
Understanding the specific types of sensitive data your organization handles is the foundation of any Web DLP strategy. This could include personally identifiable information (PII), financial records, intellectual property, and any data governed by compliance requirements. Conducting a comprehensive data audit helps determine the scope of protection needed and forms the basis for your Web DLP policies.
With a clear inventory of sensitive data, the next step is to create detailed Web DLP policies. These policies must clearly outline what is considered sensitive data. They should specify which web channels and protocols are under surveillance, such as HTTP, HTTPS, and FTP. Additionally, these policies need to define the actions to be taken if a policy is violated.
Actions might include blocking, quarantining the data, or sending alerts. The policies should also note any exceptions or activities that are whitelisted.
Look for a solution that offers content inspection and data fingerprinting for accurately detecting sensitive data, SSL/TLS inspection for scanning encrypted web traffic, and integration options with your existing web gateways or CASBs. The technology should align with your defined policies to offer the flexibility and functionality needed to protect your data effectively.
Once your Web DLP solution is in place, configure it to enforce your established policies. This includes setting up mechanisms to block or quarantine unauthorized data transfers and encrypt sensitive data in motion. Proper configuration ensures that your DLP policies actively prevent data leaks and exposures.

Continuously monitoring policy violations, false positives, and overall system performance is essential. Use the insights gained from monitoring to refine your policies and enforcement rules. It will improve accuracy and reduce operational disruptions. Regularly reviewing your Web DLP strategy helps maintain its effectiveness over time.
Implement security awareness programs to educate your staff about the importance of data security and their responsibilities in preventing data loss. An informed and vigilant workforce is a key line of defense in protecting your organization's sensitive data.
While Web DLP focuses on securing data transmitted over the internet, Endpoint DLP targets the protection of data on individual devices, such as laptops, desktops, and mobile devices. Here's a comparison of the two approaches:
Yes, Strac Web DLP Works seamlessly work with Chrome, Firefox, Edge and Safari. You can see them here:
Strac is at the forefront of the Data Loss Prevention (DLP) industry with unparalleled solutions. It leverages advanced technology and a user-centric approach to ensure sensitive data protection. Here's how Strac distinguishes itself as a leader in the DLP space:

Strac Slack DLP
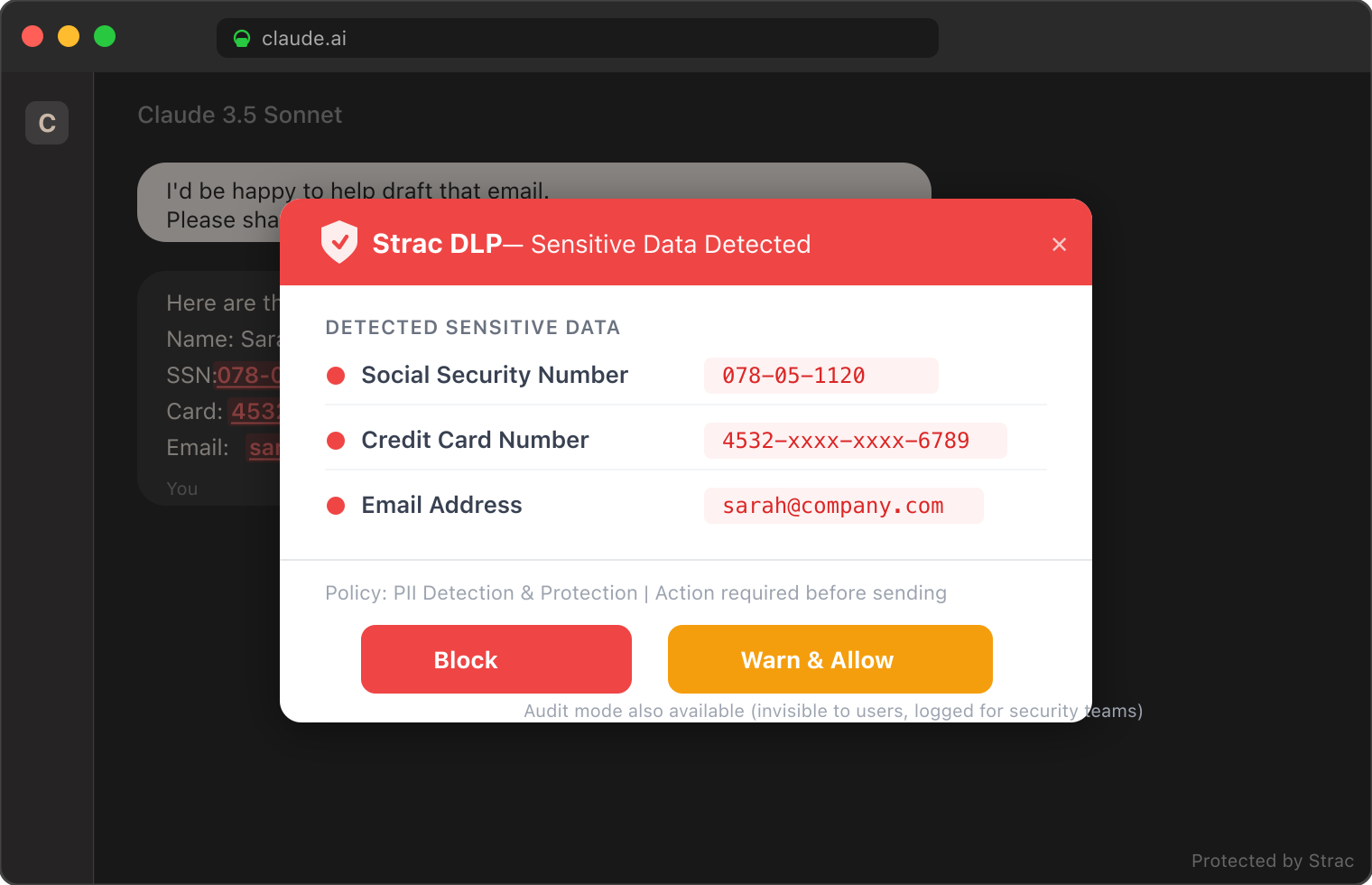
Strac GenAI DLP

Book a demo today to explore more about Strac’s web DLP features.

A web DLP policy defines how sensitive data is detected, monitored, and controlled as it moves through web channels like browsers, SaaS apps, and web-based email. It specifies what data types are sensitive (e.g., PII, PCI, PHI), where they can be shared, and what actions to take when violations occur — such as blocking, redacting, or alerting. In practice, strong policies focus on real-time enforcement, not just detection.
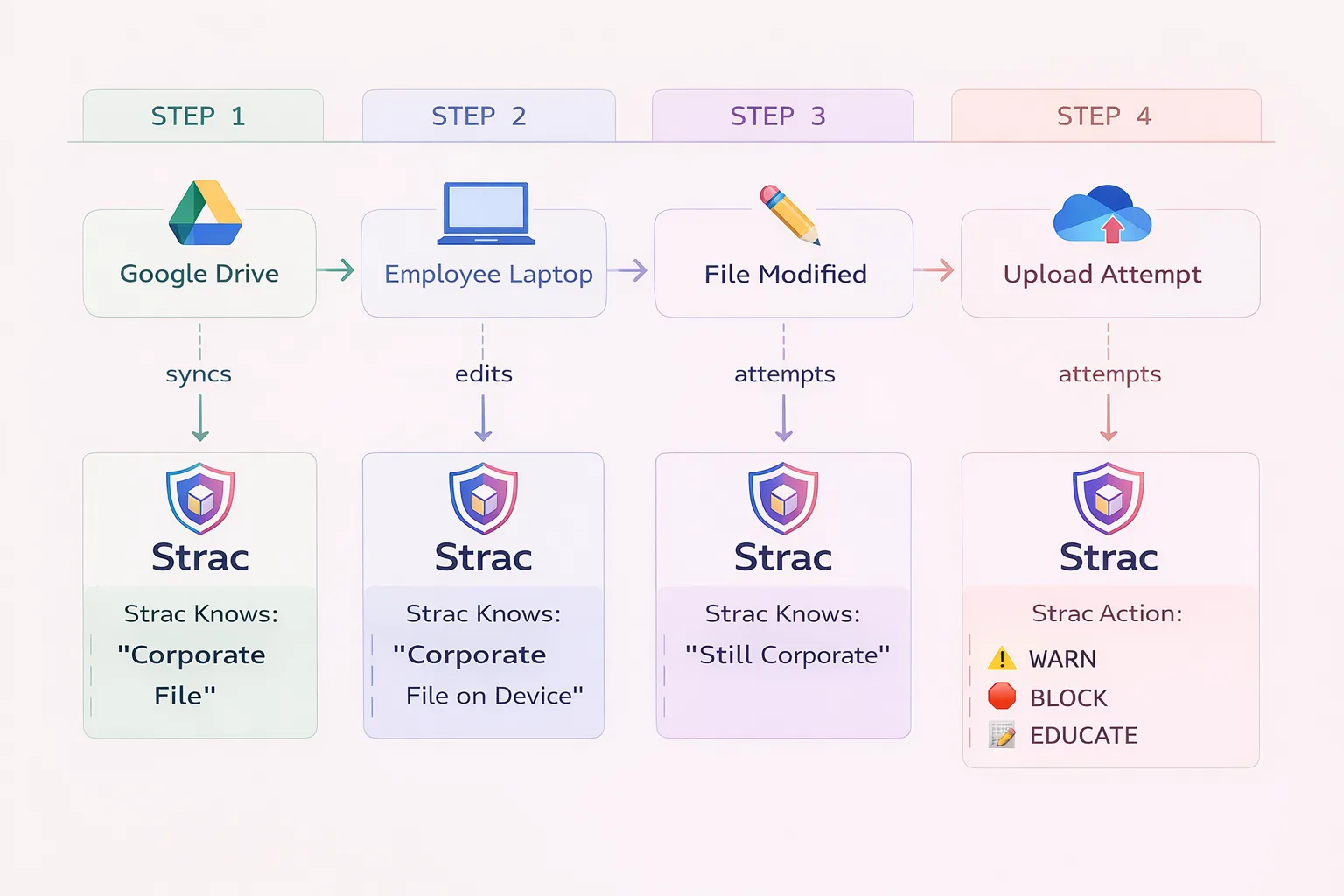
The difference between web DLP and endpoint DLP comes down to where data is protected and how it moves.
Modern environments blur this line — sensitive data often moves from endpoints → browser → SaaS → GenAI tools. That’s why relying on just one approach creates gaps; effective security requires visibility across both.
Web DLP prevents data loss in SaaS apps by monitoring and controlling data interactions at the browser and API level. It inspects actions like file uploads, copy-paste, form submissions, and message sending in real time.
When sensitive data is detected, the system can:
More advanced solutions go further by covering GenAI tools and tracking data lineage, ensuring sensitive data isn’t just stopped — but also not re-exposed across other apps or workflows.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

