The Essential Role of Data Scanning in Ensuring Security and Compliance
Learn why Data Scanning is needed to protect your SaaS, Cloud, Endpoint devices and Generative AI Apps & what to do about it
In the digital era, where data breaches are a constant threat and compliance with data protection regulations is more critical than ever, businesses face the daunting challenge of managing and securing their sensitive data. This challenge is compounded by the proliferation of data across various platforms—SaaS applications, cloud storage, and endpoint devices. Enter Strac, a cutting-edge solution designed to revolutionize the way businesses approach the scanning of sensitive data, ensuring comprehensive protection and compliance with ease.
Data scanning involves the systematic examination of digital environments to identify and categorize data, with a particular focus on sensitive information that could pose a risk if exposed or mishandled. This process is crucial for businesses that handle personal data, financial information, intellectual property, or any data subject to regulatory compliance requirements.

At its core, data scanning employs sophisticated software tools to meticulously sift through files and databases, pinpointing sensitive or specific data stored in an array of formats. This methodical process is aimed at fortifying sensitive data against vulnerabilities, ensuring its security from potential breaches, and maintaining compliance with stringent data protection regulations. By systematically identifying sensitive data, including personally identifiable information (PII), financial details, and health records, data scanning serves as a foundational pillar in the architecture of data security.
With the expansion of digital workspaces, sensitive data now resides in a multitude of locations, from emails and documents in cloud storage like AWS S3 and Google Drive/One Drive/Dropbox/Box, to conversations in collaboration tools like Slack and Microsoft Teams, to AI websites like ChatGPT, Google Bard/Gemini and even in SaaS platforms such as Salesforce, Zendesk, and Jira. This dispersion creates a complex environment where traditional data management practices are no longer sufficient.
Data Scanning is the first step in DLP. In order to know what is the sensitive data, an organization MUST know where is the sensitive data. Data Scanning and DLP tools both do Data Discovery. Once the sensitive data is scanned, Data Scanning and DLP tools will provide alerts and visibility of the sensitive data. DLP goes one step further in providing the necessary remediation actions like redaction, masking, encryption, deletion, etc.
Strac.io stands out by offering a comprehensive solution that goes beyond the surface level, enabling businesses to delve deep into their digital environments to locate and secure sensitive data across SaaS applications, cloud storage, and endpoint devices. Strac's technology is engineered to perform historical scans, allowing organizations to audit and clean up legacy data that could pose a risk if left unmanaged.
Strac’s data scanning solution is distinguished by its depth, flexibility, and comprehensiveness. Here are key features that make Strac an indispensable tool for businesses:
Employing Strac for your data scanning needs offers several strategic advantages:
Data scanning involves using specialized software to analyze files on systems to identify sensitive or specific data. This process helps locate files containing personal or confidential information and pinpoint the sensitive content they hold.
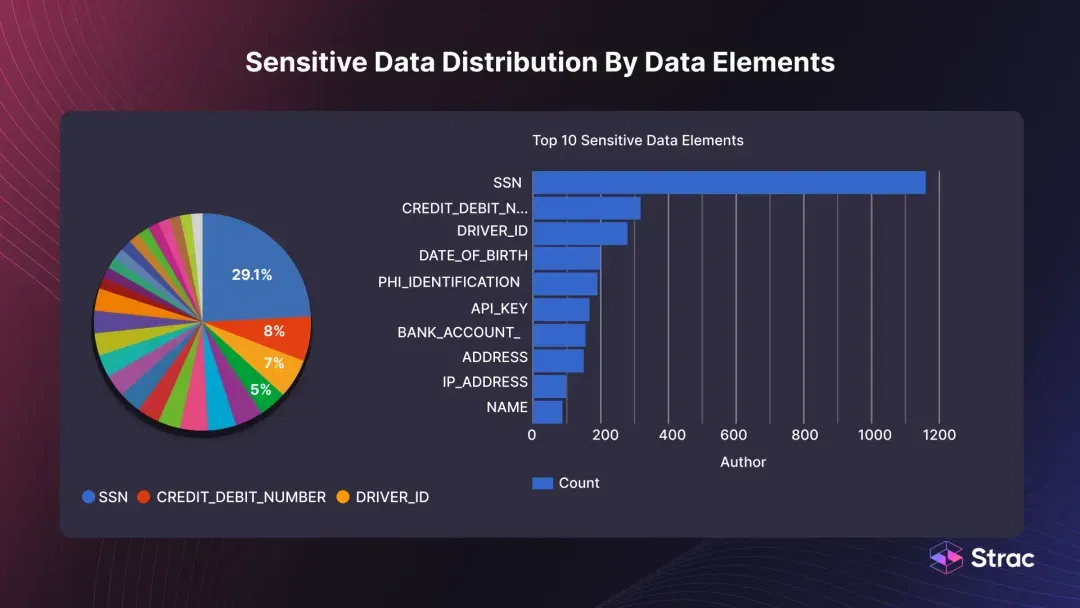
Sensitive data scanning is a process where a software tool is used to locate sensitive information within an organization. This tool can be configured to identify specific patterns, such as Social Security or credit card numbers (PCI data), and can be automated to search through various file types to ensure comprehensive coverage.
When scanning data, it is essential to look for security risks related to unstructured data and ensure compliance with data regulations. Ensure it is thorough in terms of document formats and data elements. Ensure it is accurate in its detection. Ensure it is easy to use and provide reports.
Yes, for PCI. There are 2 requirements that cover Data Scanning:

Yes. Strac is a Data Scanning solution where it automatically discovers sensitive data across SaaS, Cloud, Endpoint devices and Generative AI Apps. Checkout this section for more details:
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

