Top 10 SaaS Security Companies for Data Protection
Discover the top SaaS security companies in 2026. Compare DSPM, DLP, AI protection, and real-time remediation to choose the right platform for your business.
As SaaS adoption explodes across collaboration tools, cloud apps, and generative AI platforms, choosing from the top SaaS security companies is no longer optional; it’s a board-level decision. Modern security leaders aren’t just looking for alerting tools; they need real-time data protection, posture visibility, and automated remediation across Slack, Google Workspace, Salesforce, cloud storage, and AI workflows.
In 2026, the top SaaS security companies are defined by one thing: how effectively they reduce real data exposure risk without slowing teams down. The leaders in this space go beyond detection; they unify DSPM and DLP, provide agentless deployment, and deliver inline redaction and remediation across the entire SaaS stack.
SaaS security is about protecting sensitive data inside the apps your team uses every day. Not the network. Not the firewall. The actual tools; Slack, Microsoft 365, Salesforce, Google Drive, Zendesk, AI platforms.
Once your business runs in SaaS, your risk lives there too. Files get overshared. Support tickets collect PII. Employees paste customer data into AI tools. Permissions drift. External collaborators stay longer than they should.
SaaS security means knowing where sensitive data exists, who can access it, and fixing exposures fast; without slowing down the business.

A serious SaaS security platform does more than send alerts. It gives you visibility and lets you act.
Here’s what actually matters:
1. Posture Visibility
See misconfigurations, risky permissions, and public links; and fix them.
2. Data Protection (DLP)
Detect and redact sensitive data in chats, emails, tickets, and files; in real time.
3. Access Control Insight
Know who has access to what; including third-party apps and external users.
4. Shadow SaaS & AI Monitoring
Spot unsanctioned tools and risky AI usage before data spreads.
5. Threat Detection with Action
Catch abnormal behavior; block, redact, or contain automatically.
6. Compliance Support
Stay aligned with SOC 2, HIPAA, PCI, GDPR; without manual chaos.
That’s what modern SaaS security looks like; clear visibility, immediate remediation, less noise.
SaaS applications are at the heart of modern business, driving efficiency, scalability, and innovation. However, the widespread adoption of these cloud-based services comes with increased security vulnerabilities. The importance of SaaS security cannot be overstated; it serves as a bulwark against the myriad of cyber threats that contemporary businesses encounter.
From data breaches and ransomware attacks to phishing schemes and insider threats, the scope of potential security incidents in the cloud is extensive. Effective SaaS security strategies are essential to ensure that sensitive data remains protected, compliance with regulations is achieved, and customer trust is preserved.
Here is a curated list of the top SaaS security vendors, each bringing its unique strengths.
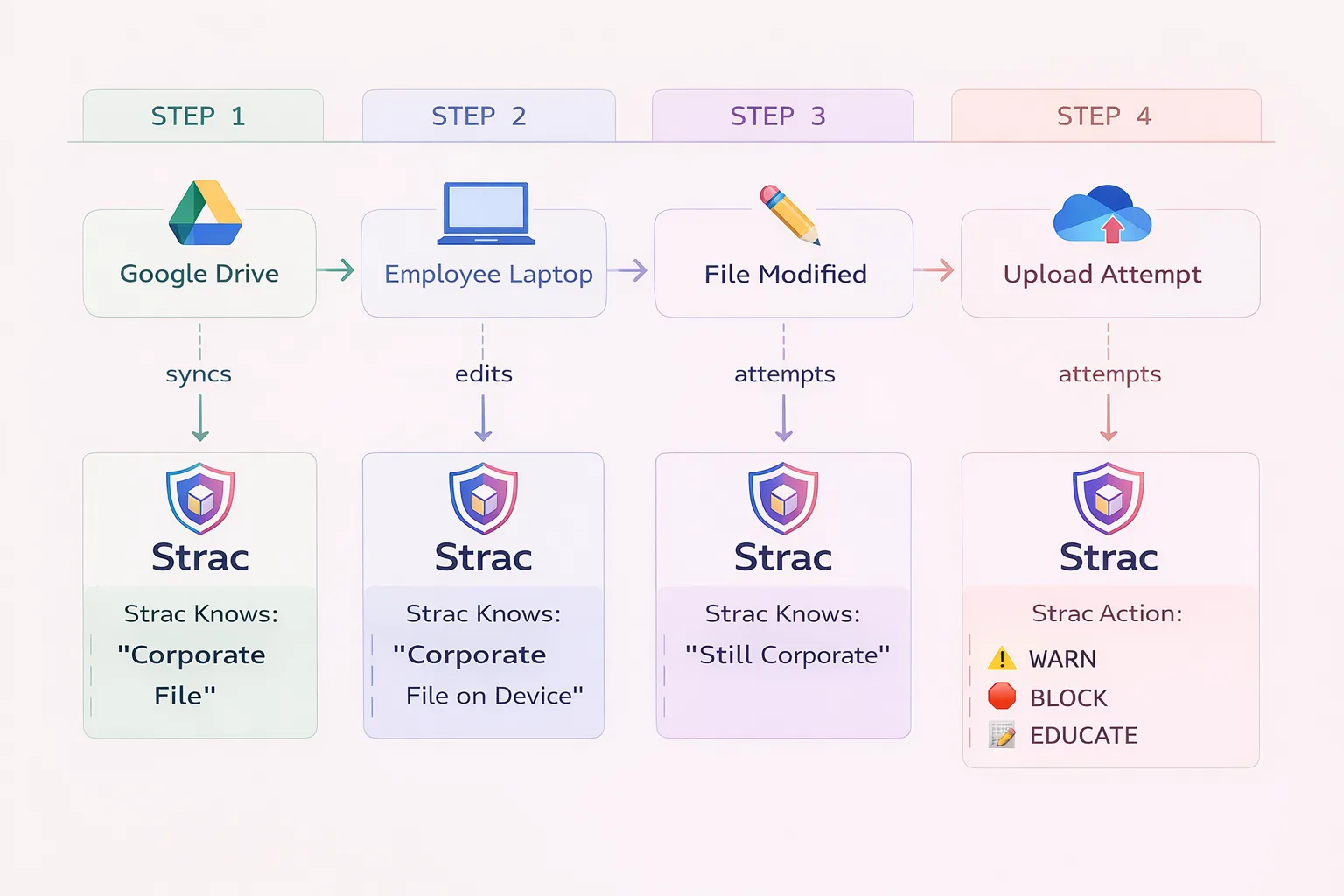
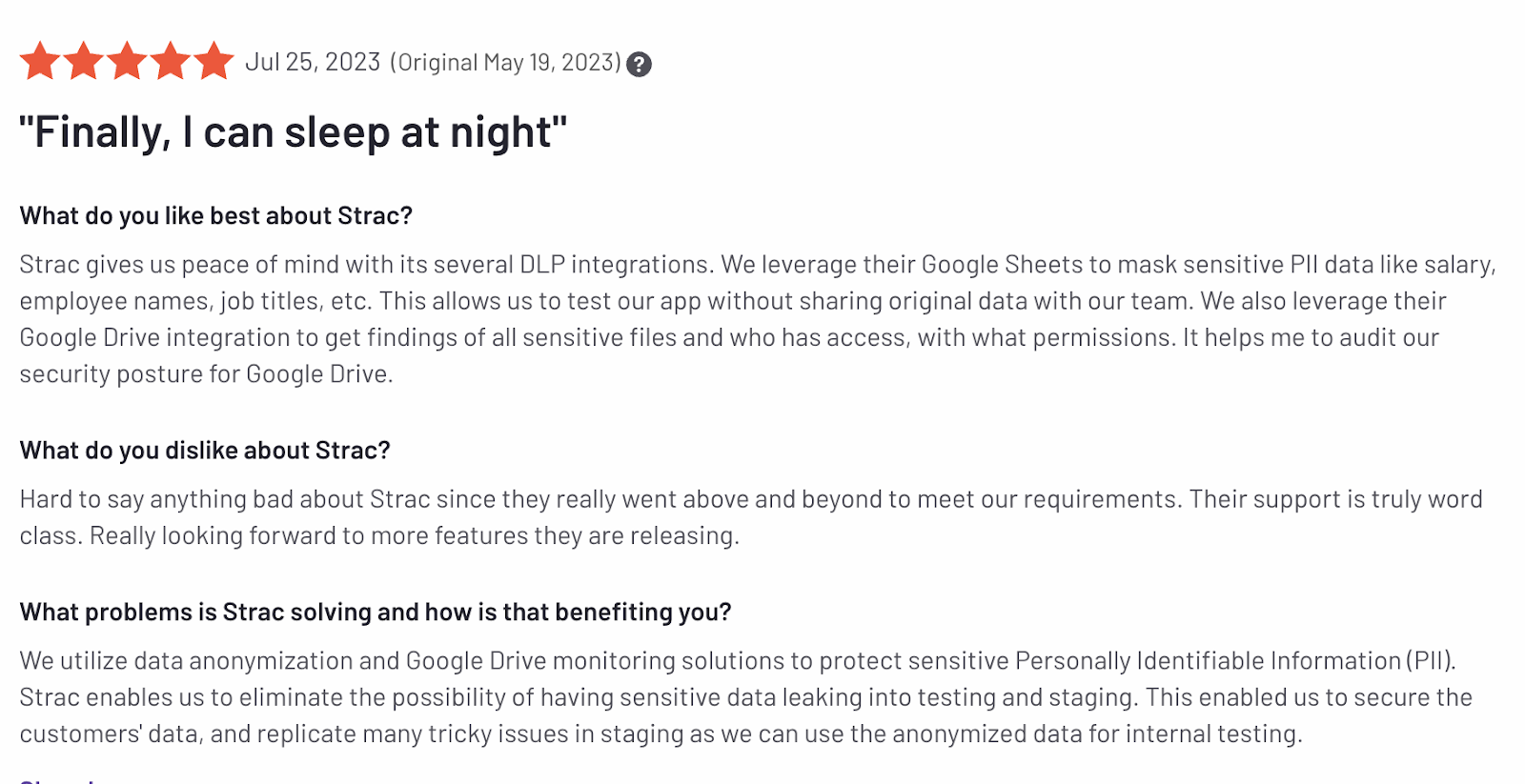
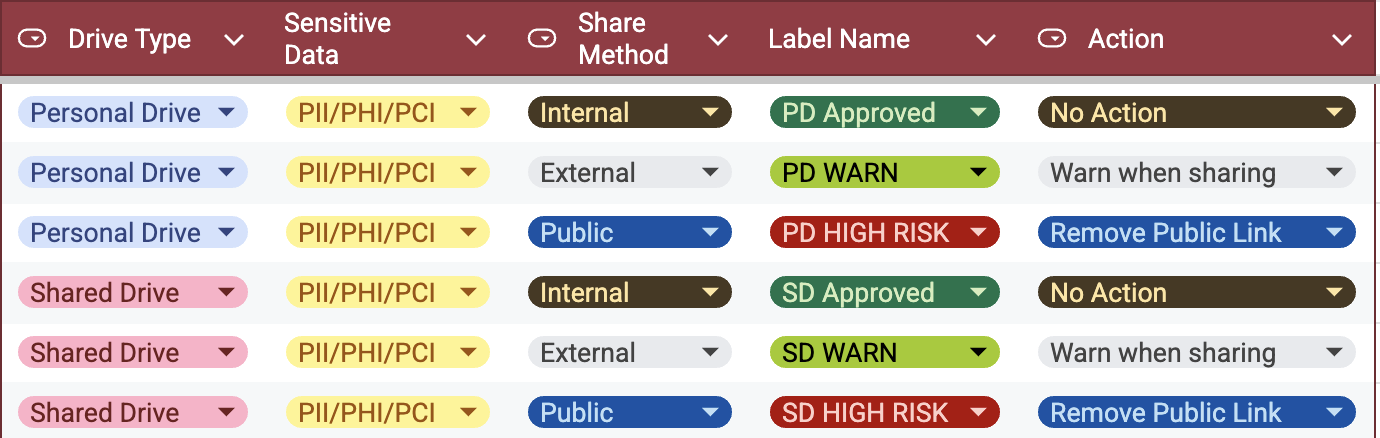
Strac is a Data Discovery, DSPM (Data Security Posture Management) and DLP platform focused on SaaS, Cloud, Gen AI and Endpoints. It is adept at securing sensitive PII across various applications, including Slack, Zendesk, Salesforce, Google Workspace, and Microsoft 365. What sets Strac apart is its ability to scan, classify, and remediate sensitive data such as PHI, PCI, and intellectual property. This ensures compliance with stringent regulatory and compliance standards like PCI, HIPAA, SOC 2, ISO 27001, and GDPR.
The underlying technology accurately detects sensitive data across unstructured text and various document formats. It ensures businesses can share sensitive data securely without exposure. Moreover, Strac supports all kinds of sensitive data elements, making it a versatile choice for protecting financial data. The platform's detect and redact API allows the redaction of sensitive data in text, documents, and even Large Language Model (LLM) prompts in real time.

Key Features




Microsoft Defender for Cloud Apps represents a major advancement in SaaS security. It provides a suite of features designed to secure cloud applications against cyber threats. Its standout capability lies in advanced threat protection, using app signals and analytics to pinpoint and neutralize unusual activities and potential vulnerabilities in real time.
It monitors data interactions and controls the flow of sensitive information within cloud applications to prevent unauthorized access. This ensures adherence to standards such as GDPR and HIPAA.
Key Features
Zscaler Internet Access is a leading SaaS security platform, offering a cloud-native security service. It stands for the transformation from traditional firewall-centric architectures to a modern, zero-trust framework. What sets Zscaler apart is its proxy architecture built on the principle of least privilege. It enables comprehensive TLS/SSL inspection at scale and securing connections based on identity, context, and business policies.
It is integrated seamlessly into the Zscaler Zero Trust Exchange to replace legacy network security solutions. This comprehensive zero-trust approach and Zscaler's integration with SaaS, endpoints, and cloud apps distinguish it from its competitors.
Key Features
Forcepoint ONE stands at the forefront among the SaaS security vendors for its cloud-native services. It is designed to protect data everywhere and secure access anywhere. This data-first Secure Access Service Edge (SASE) solution is engineered to simplify security for the hybrid workforce. It empowers productivity while ensuring continuous control over data.
Forcepoint Alternative: Forcepoint Vs Strac
Its unique selling proposition lies in its ability to modernize access for the hybrid world. It adopts Zero Trust principles with ease and secure data everywhere it goes. Its capabilities are not just about securing the present but are built with the flexibility to adapt to the future.
Key Features
Cipher distinguishes itself in the SaaS security domain through its comprehensive cloud security solution. It addresses the challenges faced by modern enterprises. Cipher is dedicated to enhancing the safety of businesses in the digital environment through its global presence.
Its dynamic xMDR platform provides a customizable and agile defense mechanism to counter evolving threats. This platform is integral to Cipher's mission of improving visibility and security posture for businesses. It ensures comprehensive protection across various digital platforms, including cloud services and IoT.
Key Features
Netskope Security Cloud is a leading security company in the SASE (Secure Access Service Edge) and Zero Trust landscape. It offers a cloud-native platform that merges security and networking services. Netskope Security Cloud commits to protecting people and data regardless of their location or devices.
Netskope Alternative: Netskope Vs Strac
Utilizing its patented Zero Trust Engine, Intelligent SSE components, and the NewEdge network, Netskope One streamlines business operations defense. It focuses on secure and accelerated web and cloud access to simplify data protection and modernize enterprise networking.
Key Features

Cisco Umbrella is a recognized leader in cloud cybersecurity and provides comprehensive SASE (Secure Access Service Edge) solutions. It protects users on and off the network. Cisco Umbrella simplifies, streamlines, and scales cybersecurity efforts by combining multiple security functions into one solution. This integration allows businesses to extend protection to devices, remote users, and distributed locations.
Its DNS-layer security is a powerful approach to blocking malicious domains, IP addresses, and cloud applications before establishing a connection. Furthermore, it embraces the evolution of cybersecurity with its SSE architecture, which uses SaaS security tools like secure web gateway, DLP, CASB, and DNS security.
Key Features

Intruder is a sophisticated yet straightforward SaaS security platform for vulnerability management. It simplifies the task of continuous vulnerability assessment by providing automated scans across cloud infrastructure, web applications, and APIs. The platform intelligently prioritizes issues based on their severity and context.
It tracks your exposed assets, scanning for vulnerabilities as soon as they're detected. It also aids compliance efforts by generating clear, actionable reports demonstrating adherence to various cybersecurity standards. This helps businesses prove their security posture to auditors, stakeholders, and customers.
Key Features
PCASB offers an advanced, integrated solution to secure cloud users, applications, and data from threats, loss, and compliance risks. Its expertise in cloud security helps protect sensitive data and provide immediate context for cloud security incidents.
The platform offers advanced DLP, protection against cloud account takeovers, management of shadow IT, and reduction of attack surfaces. It excels in protecting against account takeovers by correlating threat intelligence across various vectors. It also enhances incident response with insights into threats, users, and behaviors across email and cloud services.
Key Features

Fidelis Security positions itself as a leading provider of proactive cyber defense solutions. It provides a multi-layered defense strategy, encompassing everything from network security to data loss prevention and threat detection. It detects post-breach activities significantly faster than its competitors. This rapid response capability is critical for minimizing the impact of security incidents.
The platform enhances its defensive capabilities with advanced deception technology to create decoys and traps within the network. It also offers highly flexible and automated policy management to enable organizations to adapt their security posture.
Key Features
As we conclude our exploration of the best SaaS security companies, it's clear that the digital age demands innovative solutions. Choosing the right SaaS security provider is crucial for businesses aiming to protect their data and ensure regulatory compliance. Whether through advanced threat protection, seamless integrations, or user-centric security measures, each platform offers something valuable.
By partnering with Strac, you can empower your organization to succeed in the modern age. Feel confident knowing that your data, applications, and networks are protected by the most sophisticated security solutions available today.
Book a demo today to find out more about Strac's offerings.
The top SaaS security companies don’t just monitor activity; they reduce exposure. That means discovering sensitive data across SaaS apps, understanding who can access it, and automatically remediating risk. Platforms that unify DSPM and DLP with real-time redaction and AI coverage lead the market.
Traditional security focused on firewalls and endpoints. SaaS security focuses on data inside cloud apps like Slack, Microsoft 365, Salesforce, and AI tools. The risk isn’t just external attackers; it’s oversharing, misconfigurations, shadow apps, and sensitive data flowing through everyday workflows.
Yes. DSPM gives you visibility; where sensitive data lives and who has access. DLP allows you to act; detect, redact, block, or remediate exposures. The strongest SaaS security platforms combine both instead of forcing you to stitch tools together.
Modern platforms monitor and redact sensitive data in AI prompts, responses, attachments, and APIs. As employees increasingly paste customer data into tools like ChatGPT or Copilot, protecting AI workflows is now a baseline requirement; not an advanced feature.
The best SaaS security solutions are agentless and deploy in minutes; not months. Long rollouts slow security teams and delay risk reduction. Fast deployment means faster visibility and immediate remediation.
Highly regulated industries such as fintech, healthcare, SaaS, and e-commerce benefit the most. Any organization handling PII, PHI, PCI, or confidential business data inside cloud apps needs continuous SaaS security.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

