PII, PHI, and PCI Redaction: How to Protect Sensitive Data Across SaaS, Cloud, and GenAI
Redact PII, PHI, and PCI across SaaS, cloud, endpoints, and AI tools. Learn how modern redaction and real-time data protection actually works.
Sensitive data is moving constantly. Names, emails, health records, payment details; they’re being shared across tools your team uses every day.
PII, PHI, and PCI aren’t just compliance terms. They represent real people and real risk.
When this data gets exposed, the impact is immediate:
Regulations like GDPR, HIPAA, and PCI DSS exist for a reason. But in practice, most companies are still reacting after something goes wrong.
Redaction helps reduce that risk. But on its own, it’s not enough anymore.
Most companies think of redaction as a final step. In reality, it is only one part of a much larger problem.
Sensitive data today is:
If you only redact after exposure, you are already too late.
Modern data protection requires a full lifecycle approach:


This is where traditional tools fall short; and where modern platforms like Strac redefine the approach.
Unstructured data is the biggest blind spot in most organizations.
This includes:
Sensitive data appears here constantly; often unintentionally.
Strac enables real-time redaction in unstructured text, automatically detecting and removing:
Instead of relying on manual processes or alerts, sensitive data is redacted instantly as it appears.
This ensures compliance and eliminates exposure at the source.
Sensitive data does not just live in text; it lives inside files.
Common formats include:
These are especially risky because they are:
Strac uses ML + OCR-based detection to scan and redact sensitive data inside files; even if it is embedded in images or screenshots.
This allows organizations to:
Most data leaks today do not happen in databases.
They happen in:
These environments move fast; and sensitive data moves with them.
Traditional DLP tools were not built for this. They:
Strac is built specifically for SaaS.
It integrates directly with over 40+ applications.
And applies real-time redaction and remediation directly inside those workflows.
No delays. No manual cleanup. No blind spots.
Generative AI has introduced a completely new data risk layer.
Employees now regularly paste:
into tools like ChatGPT,Claude, Copilot, Gemini, and other AI systems.
This creates a new category of exposure:
Sensitive data leaving your environment instantly.
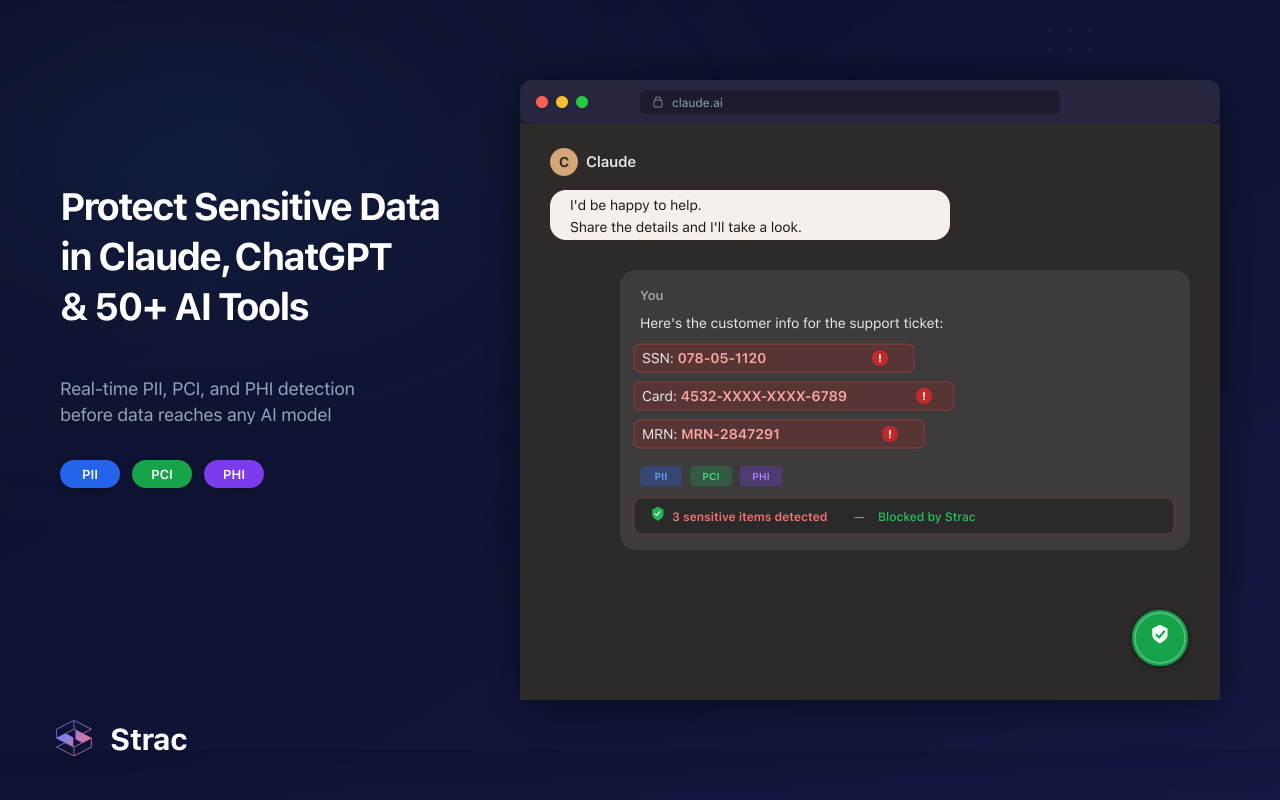
Even if providers have safeguards, risks remain:
Strac extends DLP into GenAI workflows.
It can:
This ensures that PII, PHI, and PCI never leave your environment through AI tools.
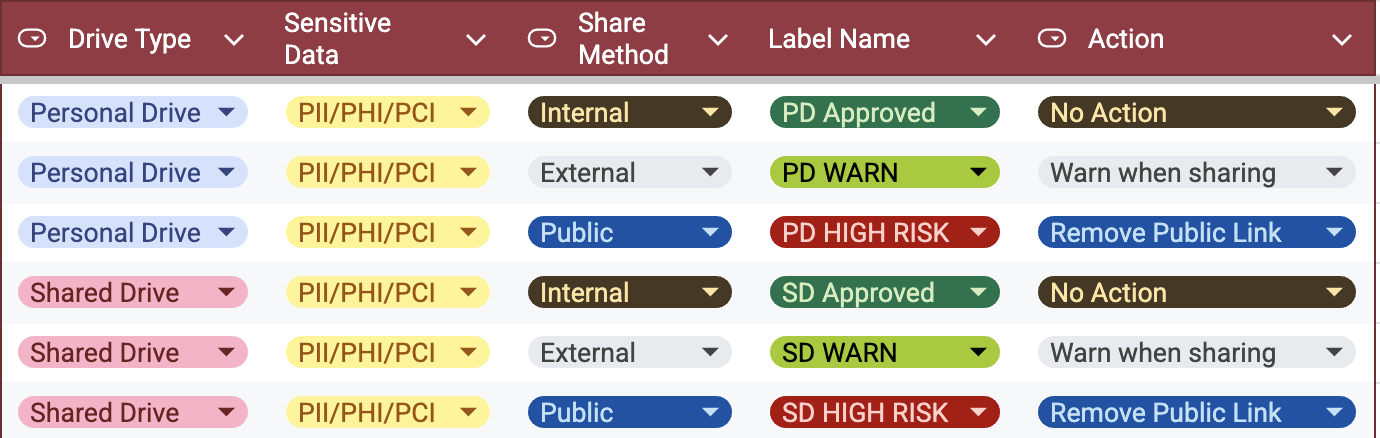
Cloud storage is where a lot of sensitive data quietly accumulates.
Think about tools like Azure, Snowflake , AWS S3 buckets. Files get uploaded, shared, downloaded, duplicated. Over time, access spreads far beyond the original intent.
What starts as a simple file can end up:
And inside those files? Customer data, health records, payment details.
The tricky part is that cloud environments don’t stay static. Permissions change. Files move. New data gets added constantly.
Manually managing this just doesn’t work.
To actually reduce risk, you need to continuously scan cloud storage and take action when something sensitive shows up. That means:
That fix might look like redacting the file, removing public access, or limiting who can view it.
The key is speed. The longer sensitive data sits exposed in the cloud, the higher the risk.
Endpoints are where data actually gets handled.
Laptops, desktops, local files; this is where people download, copy, paste, upload, and move sensitive data around all day.
It’s also one of the hardest areas to control.
Data on endpoints can:
And once it leaves your managed environment, it’s almost impossible to track. Strac has Endpoint DLP for Mac, Windows and Linux.
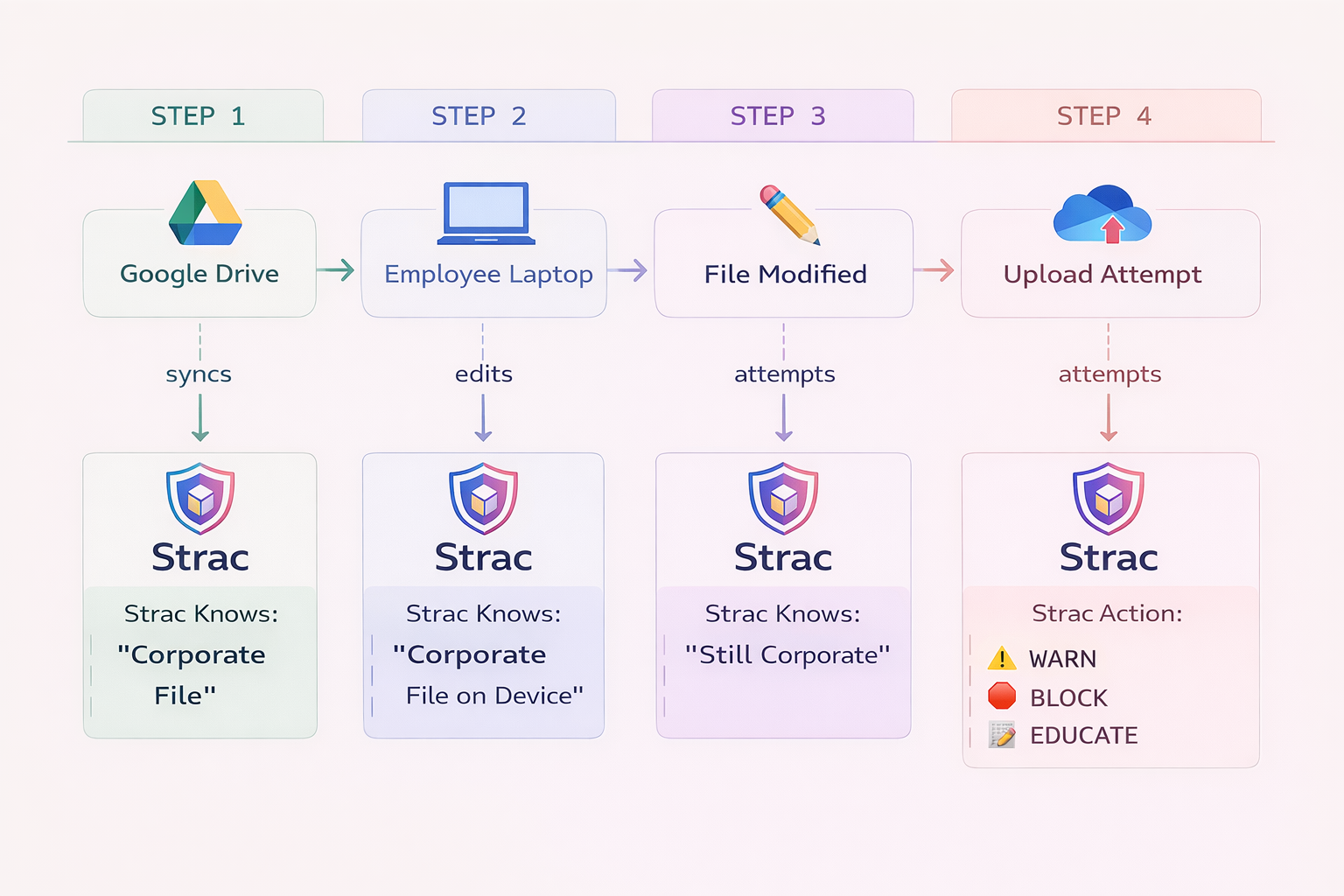
That’s why endpoint protection isn’t just about blocking actions; it’s about understanding what data is being handled in the first place.
To properly protect PII, PHI, and PCI on endpoints, you need to:
That action could be:
The goal isn’t to lock everything down. It’s to reduce risk without slowing people down.
Because at the end of the day, endpoints are where most real-world data movement actually happens.
Modern data protection requires more than isolated tools. It requires a unified system.
Strac delivers this through a full lifecycle approach:
Discover
Continuously scans SaaS apps, cloud storage, endpoints, and GenAI tools to find sensitive data
Classify
Uses ML and OCR to accurately identify PII, PHI, PCI, and custom sensitive data types
Remediate
Takes real-time action:
Monitor
Provides ongoing visibility into where data lives, who has access, and how it moves


Redacting PII, PHI, and PCI data is no longer optional; it is foundational.
But redaction alone is not enough.
Sensitive data is moving faster than ever across SaaS tools, cloud environments, and AI systems. Organizations that rely on outdated, reactive approaches will continue to face exposure and compliance risk.
The shift is clear:
From detection → to real-time remediation
From isolated tools → to unified data protection
Strac represents this shift; giving organizations the ability to not just find sensitive data, but to control it.

PII, PHI, and PCI redaction is the process of removing or masking sensitive data like personal details, health records, and payment information before it gets exposed. It matters because most data leaks don’t come from hacks; they come from everyday sharing inside tools like email, Slack, and cloud storage.
Most sensitive data is exposed inside SaaS tools like Google Drive, Slack, Salesforce, and email, not traditional databases. Cloud storage and endpoints are also major risk areas because files get shared, copied, and downloaded constantly without visibility.
To protect PII, PHI, and PCI in cloud environments, you need continuous scanning of files, visibility into who has access, and the ability to take action instantly. This includes redacting sensitive data, removing public access, and limiting external sharing before exposure spreads.
AI tools become a risk when employees paste real customer or company data into them. Once that data leaves your environment, you lose control over it. That’s why many teams now treat GenAI as a new data leakage surface and prevent sensitive data from being shared in the first place.
The most effective approach is simple: continuously discover where sensitive data lives, classify it correctly, and fix issues in real time. Tools that only alert are not enough; you need systems that can automatically redact, block, or secure data as it moves.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

