Is AWS HIPAA Compliant? A Detailed Guide
Find out how AWS supports HIPAA compliance. Understand key AWS services, shared responsibilities, and how Strac DLP enhances cloud data security and HIPAA compliance efforts.
Amazon Web Services (AWS) is widely used by healthcare organizations to store, process, and manage protected health information (PHI). However, using AWS in healthcare requires strict AWS HIPAA compliance to ensure PHI is protected according to the Health Insurance Portability and Accountability Act (HIPAA).
AWS supports HIPAA-eligible services and allows organizations to sign a Business Associate Agreement (BAA), but achieving AWS HIPAA compliance ultimately depends on how the infrastructure is configured and monitored. Healthcare providers, payers, and SaaS companies must implement strong security controls, encryption, access management, and continuous monitoring to protect PHI stored in AWS environments.
In this guide, we explain AWS HIPAA compliance requirements, which AWS services support HIPAA, best practices for securing PHI in AWS, and how DLP solutions like Strac help detect, classify, and prevent sensitive healthcare data from being exposed across cloud, SaaS, endpoints, and AI tools.
The Health Insurance Portability and Accountability Act (HIPAA), enacted in 1996, sets the standard for protecting sensitive patient data. Any organization that deals with protected health information (PHI) must ensure that all required physical, network, and process security measures are in place and followed.
HIPAA is particularly relevant to cloud services as it regulates how electronic PHI (e-PHI) is stored, accessed, and transmitted. Cloud service providers that host, process, or transmit e-PHI on behalf of healthcare organizations are considered business associates and must comply with HIPAA regulations to ensure the confidentiality, integrity, and availability of the data.

For cloud service providers to be HIPAA compliant, they must adhere to several key components of the act:
By adhering to these components, cloud service providers can ensure they meet HIPAA standards and help protect sensitive health information from unauthorized access and breaches.
Amazon Web Services (AWS) offers a range of services that are eligible for HIPAA compliance. These include, but are not limited to, Amazon S3 (Simple Storage Service), Amazon EC2 (Elastic Compute Cloud), Amazon RDS (Relational Database Service), AWS Lambda, and Amazon Redshift. These services provide the infrastructure needed to build and deploy applications that handle protected health information (PHI) securely. AWS provides a comprehensive list of HIPAA-eligible services on its official website, ensuring that businesses can select the appropriate tools to meet their compliance needs.
A critical step in achieving HIPAA compliance with AWS is signing a Business Associate Agreement (BAA). The BAA is a legally binding document that specifies each party's responsibilities in protecting PHI. It ensures that AWS, as a business associate, adheres to HIPAA regulations by implementing necessary safeguards and reporting any breaches of unsecured PHI. Without a BAA, using AWS services to store or process PHI would be non-compliant with HIPAA regulations. Signing a BAA with AWS is a fundamental requirement for any healthcare organization or SaaS company that handles sensitive health information.
AWS has a robust compliance program that includes a variety of certifications and frameworks relevant to HIPAA. Key programs and certifications include:
By adhering to these compliance programs and maintaining rigorous security standards, AWS helps organizations meet HIPAA requirements and protect sensitive health information. This robust compliance framework ensures that AWS can support the demanding security and privacy needs of healthcare organizations and their applications.
Ensuring HIPAA compliance when using AWS requires careful configuration and ongoing management of your cloud environment. Here are the steps to configure AWS services for HIPAA compliance:
Before using AWS services to store or process protected health information (PHI), you must sign a Business Associate Agreement (BAA) with AWS. This legally binding agreement outlines the responsibilities of both parties in protecting PHI and ensures AWS's commitment to HIPAA compliance.
AWS provides a list of HIPAA-eligible services that meet the required security and privacy standards. Ensure you are only using services from this list to store, process, or transmit PHI. Examples include Amazon S3, Amazon RDS, and Amazon EC2. Regularly check AWS documentation for updates to the list of eligible services.
Encrypt PHI both at rest and in transit to protect it from unauthorized access. AWS provides several encryption options, including server-side encryption for S3, AWS Key Management Service (KMS) for managing encryption keys, and enabling SSL/TLS for data in transit. Ensure that all PHI stored in AWS is encrypted using strong encryption methods such as AES-256.
Use AWS Identity and Access Management (IAM) to control access to your AWS resources. Implement the principle of least privilege by granting users and applications the minimum permissions necessary to perform their tasks. Multi-factor authentication (MFA) adds an extra layer of security for accessing sensitive data.
Regularly audit your AWS environment to ensure compliance with HIPAA requirements. Use AWS CloudTrail to log and monitor all API activity, and AWS Config to assess your configurations against best practices and compliance guidelines continuously. Regularly review these logs and configurations to identify and address any security issues.
Ensure that you have regular backups of your data and a comprehensive disaster recovery plan in place. Use AWS services such as AWS Backup and Amazon S3 for reliable and secure backup solutions. Test your disaster recovery plan periodically to ensure that you can recover PHI in case of data loss or system failures.
Ensure that all employees handling PHI are trained on HIPAA regulations and AWS security best practices. Regular training sessions help keep staff updated on the latest security protocols and compliance requirements. Emphasize the importance of data privacy and security in their daily tasks.
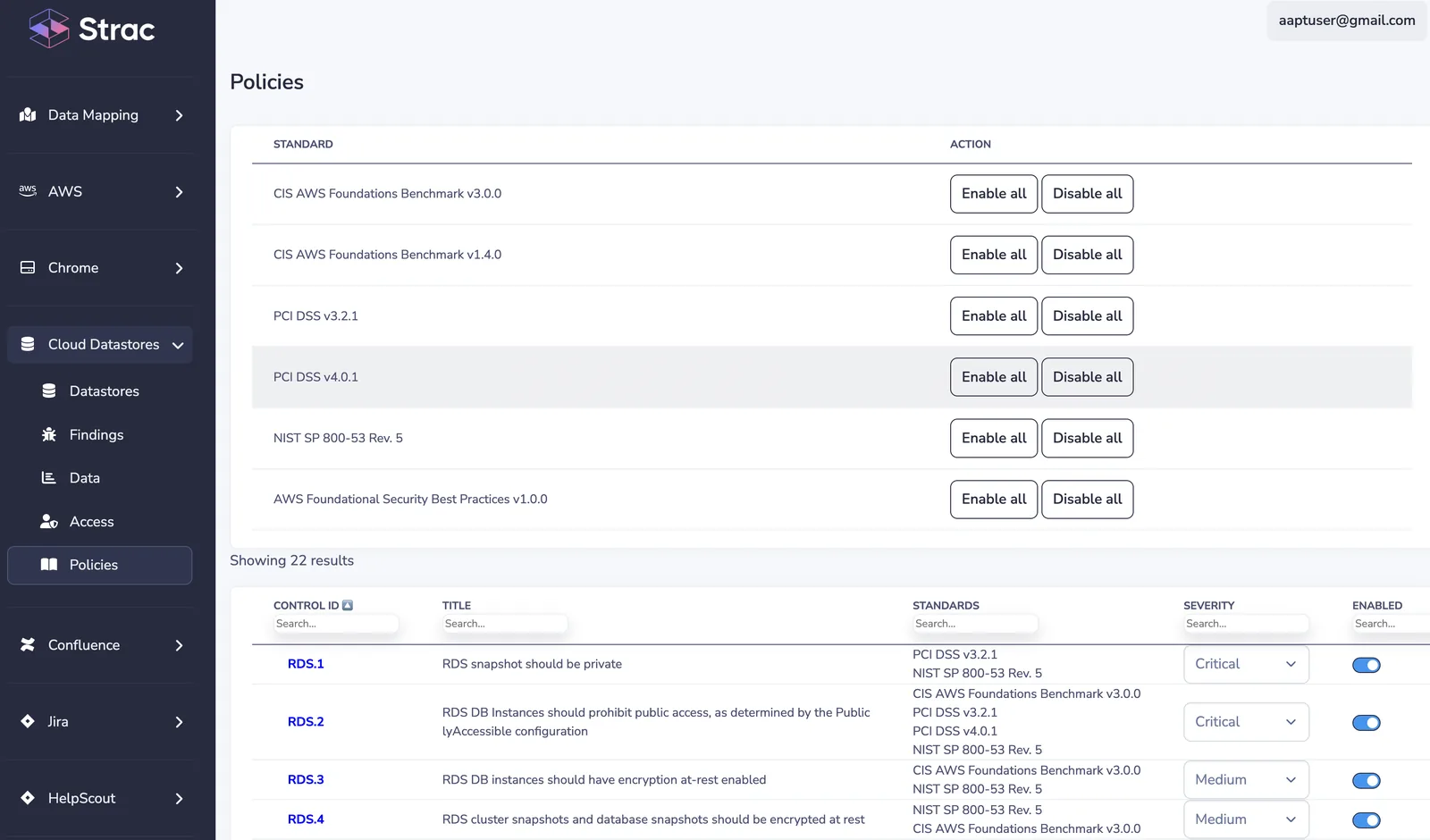
For comprehensive security and compliance, implement Data Loss Prevention (DLP) solutions. DLP tools help monitor and protect sensitive data by identifying and preventing data breaches. Solutions like Strac DLP integrate seamlessly with AWS, providing advanced data protection features such as automated data discovery, classification, real-time monitoring, and encryption. Using DLP solutions ensures that PHI is continuously protected against unauthorized access and potential breaches.
By following these best practices, you can configure AWS services to meet HIPAA compliance requirements, protect sensitive health information, and ensure the security and privacy of your cloud environment.
Strac’s Data Loss Prevention (DLP) solutions are designed to seamlessly integrate with AWS, providing robust protection for sensitive health information. Strac offers advanced features such as automated data discovery and classification, which continuously scans your AWS environment to identify and categorize e-PHI. This ensures that all sensitive data is accurately tracked and protected.
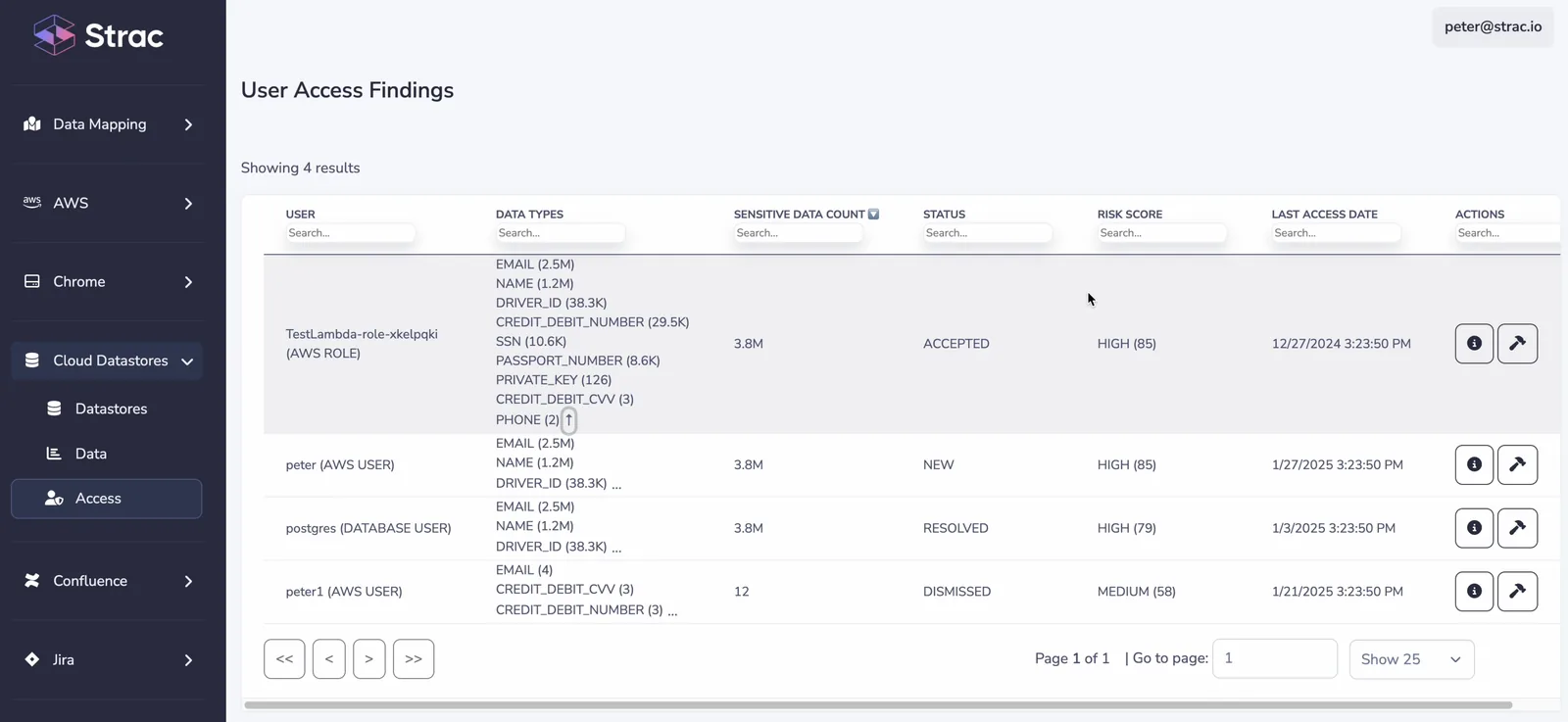
Strac’s encryption capabilities ensure that data is securely encrypted both at rest and in transit. By leveraging AWS Key Management Service (KMS), Strac provides secure encryption key management, ensuring that only authorized personnel can access sensitive information. Additionally, Strac’s real-time monitoring and alerting capabilities enable continuous oversight of data access and usage, allowing for immediate response to potential security threats.
Integrating Strac’s DLP solutions with AWS significantly enhances your security, monitoring, and compliance efforts, providing several key benefits:
Using Strac’s DLP solutions in conjunction with AWS allows SaaS companies to enhance their data protection measures, ensuring HIPAA compliance and safeguarding sensitive health information.
Ensuring HIPAA compliance when using AWS involves selecting HIPAA-eligible services, signing a Business Associate Agreement (BAA), implementing robust security measures such as encryption and access controls, and conducting regular audits. Leveraging Strac’s DLP solutions enhances these efforts by providing advanced data protection, comprehensive monitoring, and automated compliance tools.
Due diligence and continuous compliance are essential in maintaining HIPAA standards and protecting sensitive health information. By following best practices and utilizing tools like Strac, businesses can achieve a robust security posture and avoid the severe repercussions of non-compliance.
Take proactive steps to ensure HIPAA compliance with AWS today. Schedule a demo with Strac to see how their solutions can enhance your data security and compliance efforts.

Not automatically. AWS provides HIPAA-eligible services and allows organizations to sign a Business Associate Agreement (BAA), but AWS HIPAA compliance depends on how you configure and secure your environment. Misconfigured storage, weak access controls, or exposed APIs can still lead to PHI exposure.
Many commonly used services are HIPAA-eligible, including Amazon S3, EC2, RDS, Lambda, CloudTrail, and CloudWatch. However, organizations must still configure encryption, identity controls, logging, and monitoring correctly to maintain AWS HIPAA compliance.
Yes. PHI can be stored in AWS if a BAA is signed and security controls are implemented. This includes encryption at rest and in transit, strict access management through IAM, logging, and continuous monitoring of data access and movement.
The biggest risks usually come from misconfiguration rather than the platform itself, including:
Traditional cloud security tools protect infrastructure, but DLP protects the data itself. A modern DLP solution can:
Solutions like Strac extend AWS HIPAA compliance by protecting sensitive healthcare data not only in AWS infrastructure, but also across SaaS apps, cloud storage, endpoints, and GenAI tools where PHI often moves after leaving the cloud environment.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

