Top 7 Endpoint Monitoring Tools for IT Security in 2026
Discover the top 7 endpoint monitoring tools for IT security in 2026. Enhance protection, detect threats, and ensure compliance with these advanced solutions.
Endpoints are one of the most common entry points for cyberattacks, which makes endpoint monitoring tools essential for modern IT security. Without proper monitoring, organizations risk data breaches, unauthorized access, and compliance violations. As remote work, cloud apps, and mobile devices expand the attack surface, businesses need solutions that provide continuous endpoint visibility, threat detection, and real-time alerts.
In this guide, we explore the top endpoint monitoring tools that help organizations strengthen security, monitor device activity, and protect sensitive data.
These tools will help enhance cybersecurity measures, streamline IT operations, and ensure compliance with modern IT standards.
Strac is a modern endpoint monitoring and Data Loss Prevention (DLP) platform designed for today’s cloud-first and AI-driven workplaces. Unlike traditional endpoint monitoring tools that only track device activity, Strac protects sensitive data directly at the source; across employee laptops, browsers, SaaS applications, Cloud, and generative AI tools.
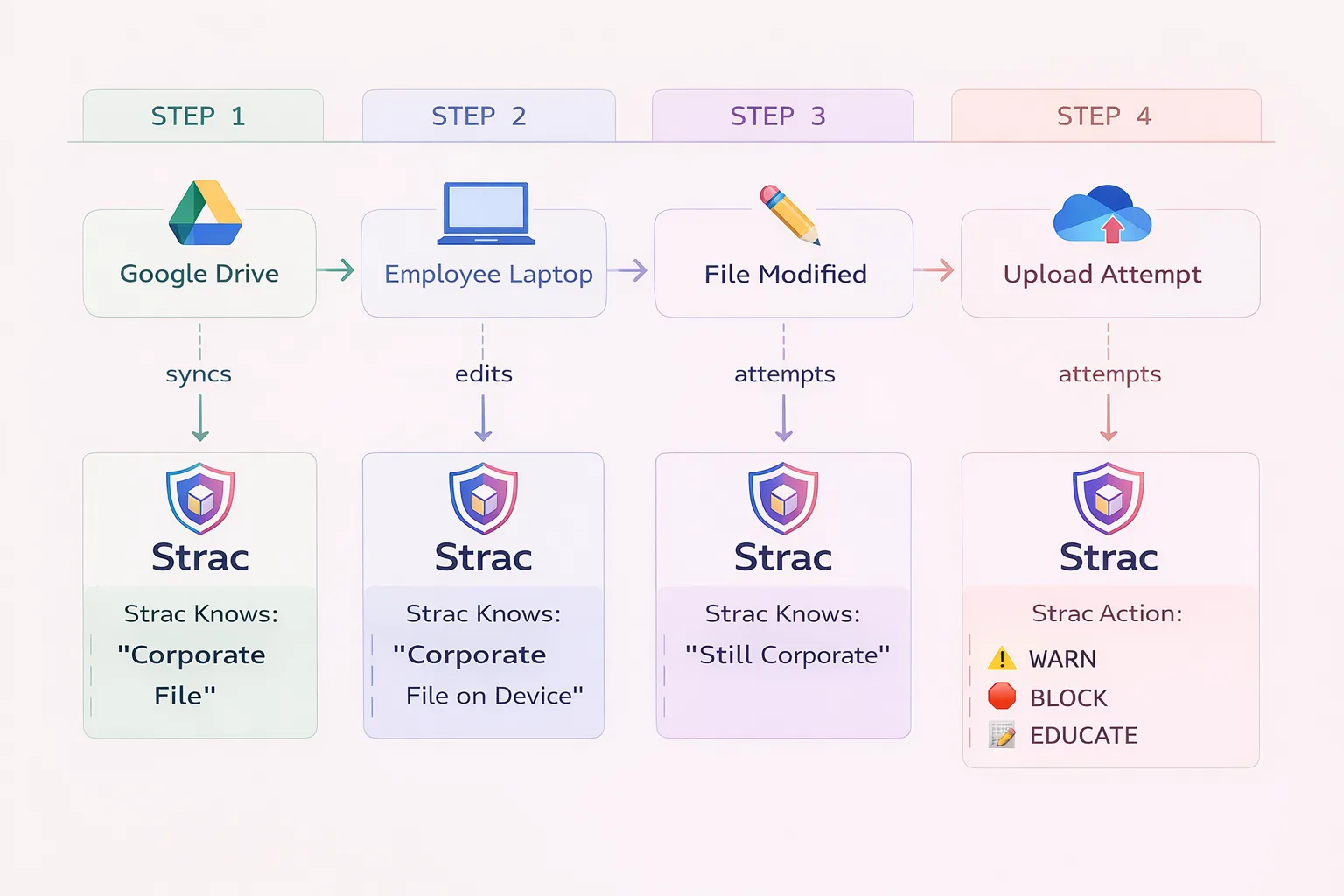
As organizations adopt remote work and AI tools like ChatGPT, sensitive data increasingly moves from endpoints into cloud apps and browser-based workflows. Strac closes this gap by combining endpoint visibility, browser monitoring, SaaS protection, and AI data governance in a single platform.
👉 Learn More about Strac Endpoint Data Lineage
👉 Learn more about DLP Agents

Strac is ideal for organizations that need modern endpoint monitoring combined with advanced data protection, especially those working with remote teams, SaaS platforms, and AI tools. It is particularly valuable for SaaS companies, fintech firms, healthcare organizations, and AI-driven businesses where sensitive data frequently moves between endpoints, browsers, and cloud applications.
What are Customers Saying about Strac
NinjaOne is an all-in-one endpoint management and monitoring solution designed to enhance IT security and efficiency. It integrates endpoint performance monitoring, task automation, remote access, software management, and automated patching. This platform especially benefits organizations with remote or hybrid workforces, offering user-friendly interfaces and comprehensive features to streamline endpoint management.
Key Features
Miradore is cloud-based Unified Endpoint Management (UEM) software that manages various devices, including smartphones, tablets, laptops, and desktops. It also tracks other IT assets such as monitors, VR headsets, printers, and wearables, providing a centralized platform for Android, iOS, iPadOS, Windows, and macOS devices.
Key Features
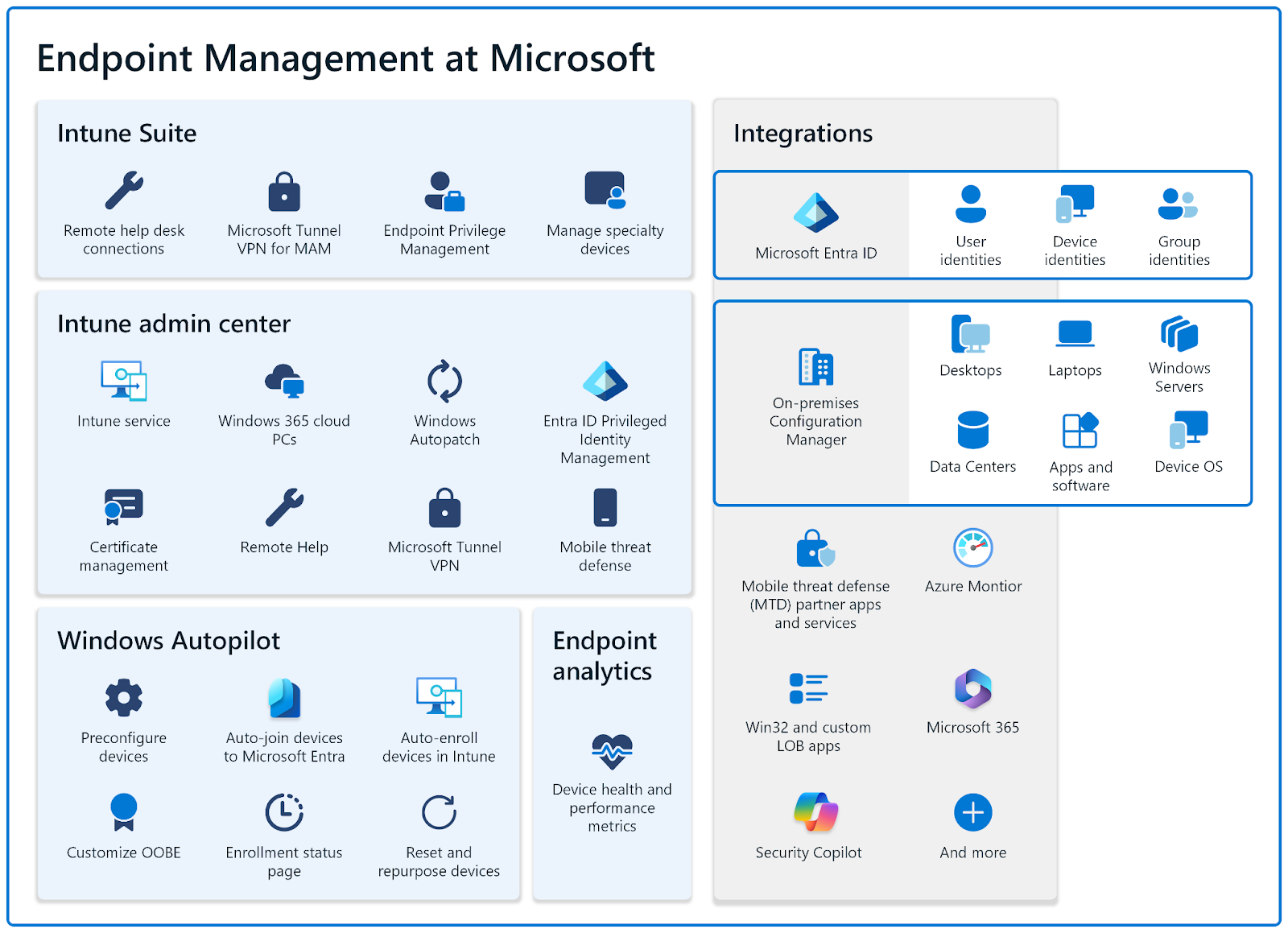
Microsoft Endpoint Manager (MEM) is designed to empower organizations by enabling secure access to resources from any device, anywhere. It integrates application-level controls and intent-based policies to ensure users only access necessary resources.
MEM provides centralized management for all networked devices, including on-premises, remote, and personal devices. It enhances cloud security across virtual endpoints to protect users' remote devices from threats.
Key Features
Hexnode is a comprehensive Unified Endpoint Management (UEM) software designed to streamline the management of various devices from a single, centralized console. It is ideal for organizations implementing bring-your-own-device (BYOD) policies to enhance both security and user experience. Hexnode empowers IT teams to remotely secure, encrypt, lock, and wipe data, thus significantly strengthening the security framework of the organization.
Key Features
Teramind ranks highly among endpoint monitoring tools for its extensive visibility and control over IT infrastructure and workforce. It enhances data security, mitigates risks, and optimizes employee productivity.
Teramind's robust feature set includes advanced monitoring capabilities such as user activity tracking, website monitoring, file transfer tracking, and session recording. These features enable organizations to gain detailed insights into employee behavior, identify potential security risks, and ensure compliance with data security standards.
Key Features
Atera is a powerful unified endpoint management solution tailored for IT teams and managed service providers (MSPs). It offers comprehensive remote monitoring and management capabilities, enabling users to maintain a real-time, holistic view of multiple networks.
This allows IT professionals to efficiently oversee various aspects of their IT infrastructure, promptly address issues, and enhance support capabilities. Atera's proactive design, featuring real-time alerts, ensures that potential problems are detected and resolved before they escalate.
Key Features
Selecting the right endpoint monitoring software is crucial for maintaining a secure and efficient IT infrastructure. To make an informed decision, consider the following key factors:
Your organization must ensure the endpoint monitoring software is compatible with its existing hardware, operating systems, and software applications. The tool should seamlessly integrate with your current IT environment without requiring extensive modifications. Additionally, the software should support an increasing number of endpoints and adapt to business changes.
Look for tools that offer advanced threat detection, antivirus protection, firewall capabilities, and encryption. These features help safeguard against malware, vulnerabilities, and unauthorized access. Additionally, patch management capabilities are critical to ensure that all devices are up-to-date with the latest security patches.
Effective endpoint monitoring software should allow IT administrators to access, configure, and troubleshoot devices remotely. Features such as remote desktop control, software deployment, and real-time alerts can significantly enhance the efficiency and responsiveness of IT support teams. It will reduce the downtime and improve overall productivity.
Automation features can streamline endpoint management tasks, reducing the burden on IT staff. Look for software that can automate routine tasks such as software updates, configuration management, and compliance checks. Additionally, integration with other IT management tools and systems, such as IT service management (ITSM) and network monitoring solutions, can provide an efficient IT management environment.
Reliable vendor support is a critical factor in the successful implementation and ongoing operation of endpoint monitoring software. Evaluate the vendor's reputation, customer reviews, and the quality of their support services. Consider factors such as availability of technical support, documentation, training resources, and responsiveness to issues.
Endpoint monitoring tools are essential for maintaining the security and efficiency of modern IT infrastructures. They provide critical oversight and management capability to help organizations protect against cyber threats and ensure regulatory compliance.
With Strac, you can choose one of the industry's most effective endpoint monitoring tools. Its advanced security features, including threat detection and policy enforcement, are designed to protect all devices from cyber threats.

Endpoint monitoring software is a tool used to continuously oversee and manage the various devices connected to a network. The devices could be desktops, laptops, smartphones, and tablets. It helps detect and mitigate potential security threats, enforce policies, manage configurations, and maintain data integrity across all connected devices.
Organizations often rely on industry-leading tools such as Strac for their centralized control, robust security measures, and DLP capabilities. Several leading software solutions, such as NinjaOne, Miradore, Zluri, etc., are widely recognized and used in the industry.
Endpoint activity monitoring refers to tracking and analyzing the activities performed on endpoint devices within a network. This includes monitoring user actions, application usage, file access, and network connections. It is intended to detect and prevent malicious activities and ensure compliance with security policies.
EDR (Endpoint Detection and Response) tools are specialized cybersecurity solutions designed to detect, investigate, and respond to advanced threats targeting endpoint devices. These tools provide continuous monitoring and comprehensive visibility into endpoint activities to detect suspicious behavior and potential security incidents.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

