PHI Redaction: Protecting Sensitive Health Information for Compliance and Security
Redact PHI (Patient Data)
TL;DR:
Protecting Protected Health Information (PHI) is critical for ensuring compliance and preventing data breaches. With the proliferation of communication and collaboration platforms like Zendesk, Slack, Teams, Google workspace, O365, AWS, Azure, Salesforce, Jira/Confluence and email systems, PHI is often inadvertently shared in various channels. To address this challenge, automated redaction tools such as Strac ensure that sensitive information is detected, redacted, and securely managed.
In this blog, we focus on how PHI redaction applies to cloud storages, customer support platforms, communication tools, and email systems, providing real-world examples and solutions
PHI redaction refers to the process of identifying and removing or obscuring sensitive information in a document to ensure it cannot be used to identify an individual. Redaction ensures that sensitive data remains secure when shared, stored, or archived.
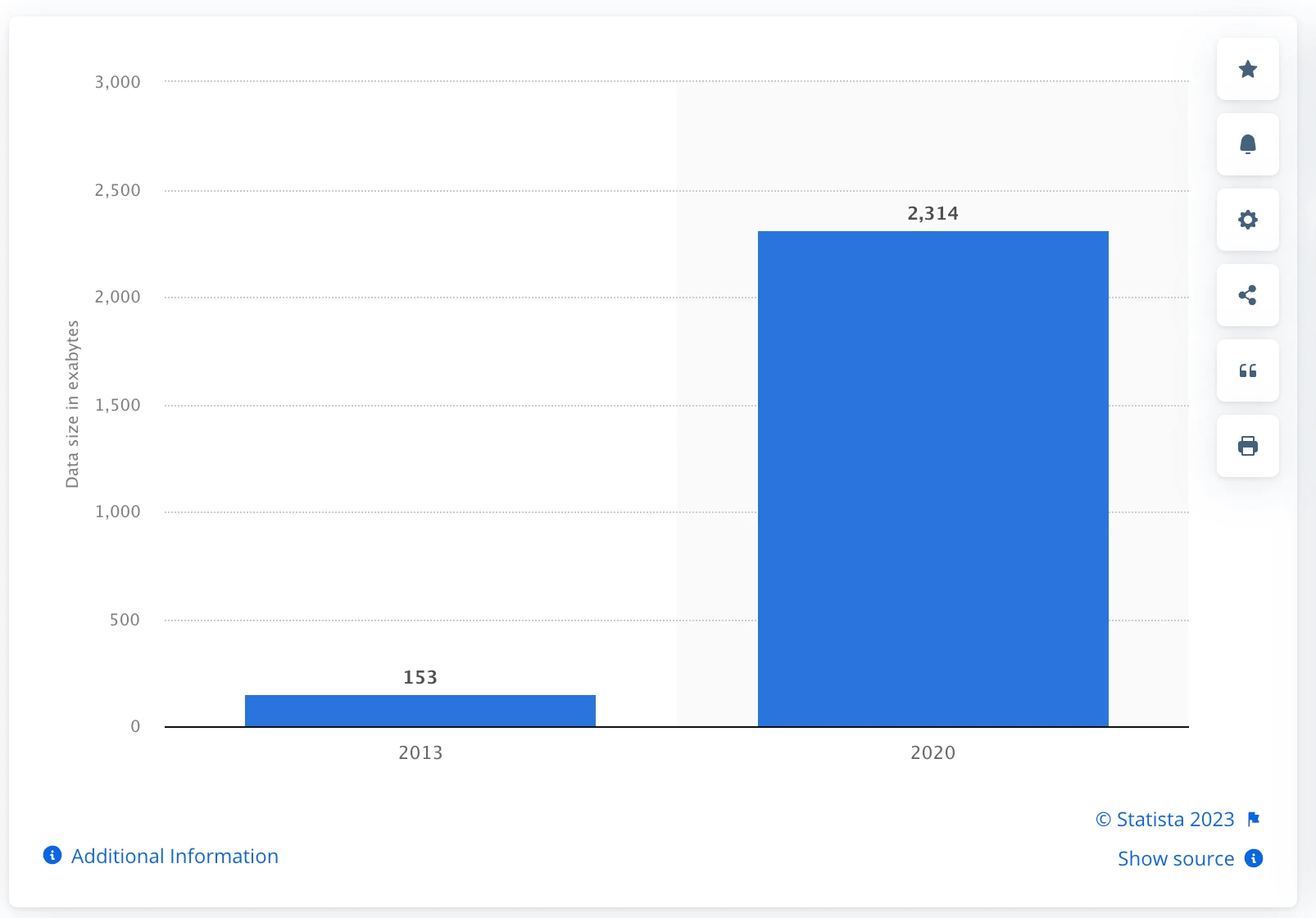
The challenge with PHI lies in the need to balance privacy and utility. While it is critical to protect patient privacy by deidentifying their health information, the deidentified data must still retain enough utility for essential tasks such as health research, quality assurance, and clinical studies. This challenge is amplified by the increasing volume and complexity of health data being collected, and the growing number of services that touch this data.
Scenario:
A patient submits a support ticket containing PHI, such as their name, medical record number, or treatment details.
Challenges:
Solution:
Strac integrates with customer support tools to automatically scan support tickets for PHI and redact it before agents access the ticket. Sensitive information such as patient names and medical record numbers is replaced with placeholders (e.g., "Patient [REDACTED]").
Result:

Scenario:
A healthcare provider's team discusses patient cases in Slack channels, where PHI like diagnosis details or appointment dates may be shared.
Challenges:
Solution:
Strac integrates with Slack to detect and redact PHI in real-time. If a message contains sensitive information, it is immediately flagged and redacted. For example, a message like:
"John Doe's MRI results show a positive diagnosis"
is automatically transformed into:
"Patient [REDACTED]'s MRI results show a positive diagnosis."
Result:
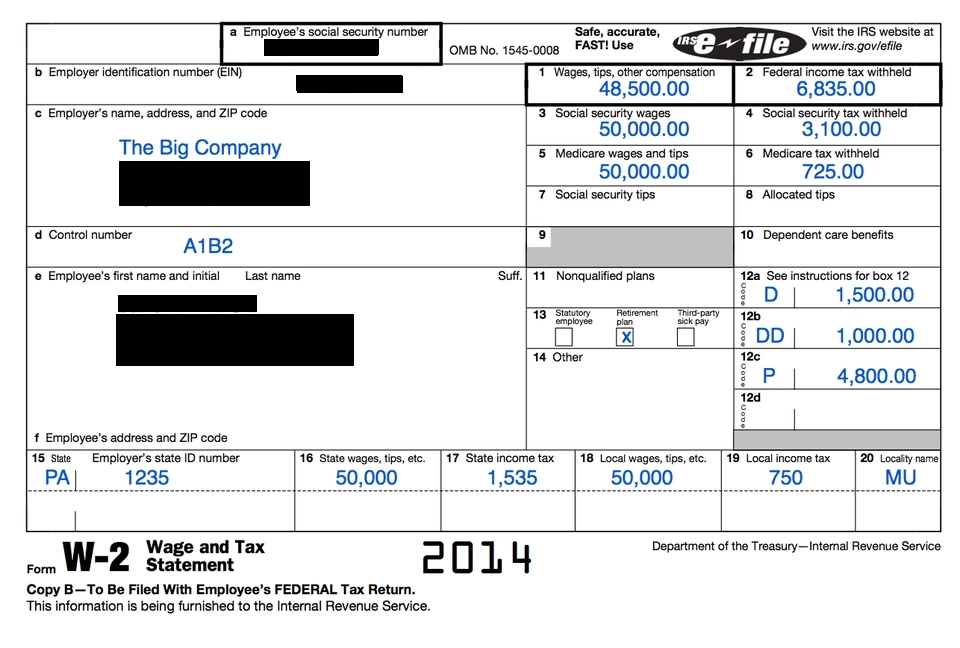
Scenario:
A doctor emails a lab report containing PHI to a colleague or external partner.
Challenges:
Solution:
Strac integrates with email systems like Office 365 and Gmail to scan both email content and attachments. PHI is detected and redacted automatically before the email is sent. For example:
Result:

Scenario:
A healthcare organization stores thousands of files in SharePoint and Google Drive containing sensitive patient data, including scanned medical records, test results, and discharge summaries. These files are often shared externally for collaboration or internally for team access.
Challenges:
Solution:
Strac integrates with SharePoint and Google Drive to perform real-time and historical scanning of all files for PHI. Detected PHI is automatically redacted or flagged for admin review.
For example:
Result:
Scenario:
Healthcare teams document projects, tasks, and patient-related workflows in Jira, Confluence, and Notion, where PHI such as patient names, medical histories, or diagnoses might be logged.
Challenges:
Solution:
Strac integrates with Jira, Confluence, and Notion to scan tasks, tickets, and pages for PHI. Redaction occurs in real-time to ensure compliance without interrupting workflows.
For example:
Result:

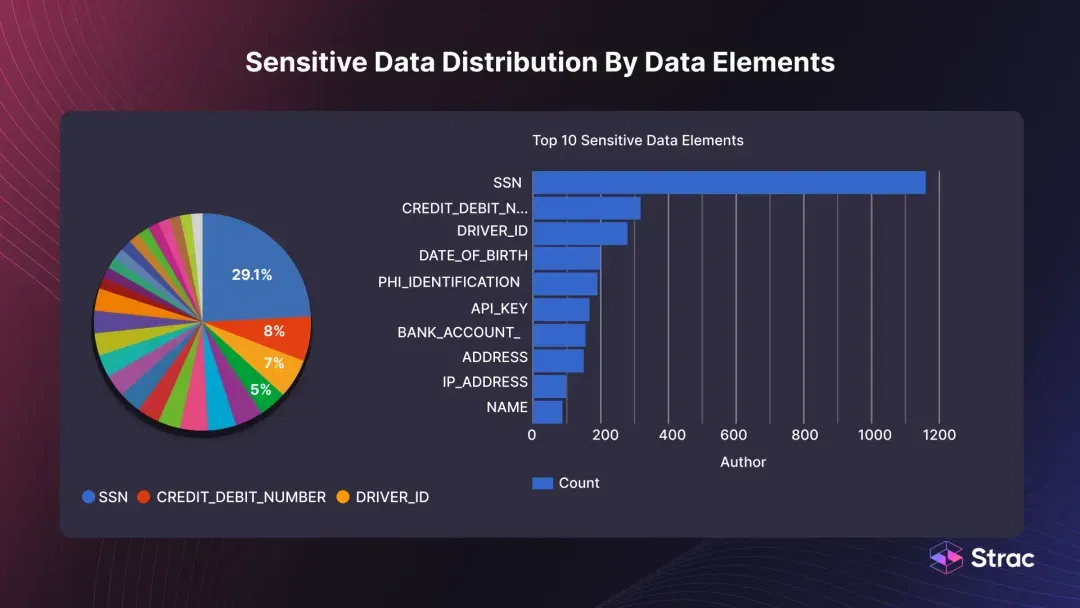
Automated redaction tools like Strac work seamlessly across various platforms to detect and redact PHI. Here’s how:
Using machine learning (ML), natural language processing (NLP), and contextual analysis, Strac identifies PHI within text, images, and metadata.
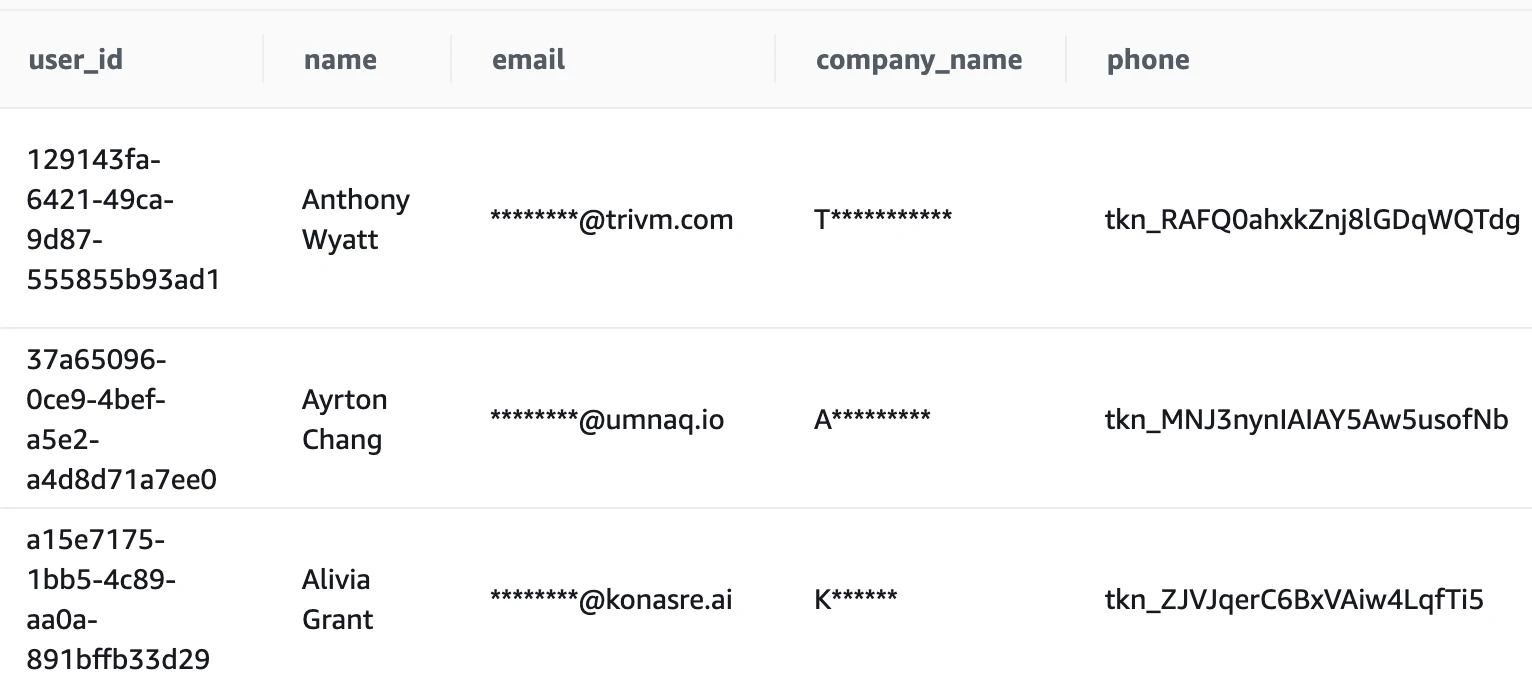
Sensitive information is automatically redacted from the platform’s content. This can include:
PHI Redaction: Strac powered Document Redaction
Strac will work with any database (Relational database or NoSQL Database) and can mask, tokenize or redact sensitive data in databases. Learn more about here: https://www.strac.io/integrations/postgres-data-masking
Checkout our API Docs at https://docs.strac.io to learn how you can protect sensitive PHI data.

To learn more about Strac's tokenization, redaction, and masking solutions, book a demo.
PHI redaction is vital for securing sensitive health information in today’s multi-channel environment. Platforms like Zendesk, Slack, and email systems are integral to healthcare operations, but they require robust redaction tools to protect patient privacy and maintain compliance. With Strac, organizations can automate PHI redaction across platforms, enabling secure and efficient data handling while reducing the risk of compliance violations.
.avif)
.avif)
.avif)
.avif)
.avif)






.gif)

